In the rapidly evolving landscape of technological advancement, particularly within sectors that rely heavily on data collection and interpretation, understanding the nuances of information management is paramount. While much attention is paid to the tangible datasets we actively collect and analyze, a significant and often overlooked category exists: Shadow Data. This refers to the vast ocean of information that is generated, collected, and stored by organizations but is not readily accessible, governed, or utilized for primary business purposes. It’s the data that lurks in the background, often created as a byproduct of other processes, existing in silos, or simply forgotten.
The concept of shadow data is not exclusive to any single industry, but it holds particular relevance and implications for fields like Tech & Innovation, where the continuous generation and processing of data are fundamental to progress. From AI development and autonomous systems to remote sensing and intricate mapping operations, the sheer volume of data is overwhelming. Unlocking the potential of shadow data within these domains can lead to significant breakthroughs, enhanced efficiencies, and a more comprehensive understanding of the systems and environments they aim to represent.
The Genesis of Shadow Data: Unseen Streams of Information
Shadow data isn’t born in a vacuum; it emerges organically from the very fabric of our digital operations. Understanding its origins is the first step in appreciating its pervasive nature and potential impact. These unseen streams are often the collateral output of intended processes, creating a complex web of information that goes beyond the explicitly managed databases.
Byproducts of System Operations
Many operational systems within technology and innovation environments generate data as a secondary outcome of their primary functions. For instance, the logs generated by servers, network devices, and application software are essential for system monitoring and troubleshooting. However, these logs often contain rich details about user interactions, system performance anomalies, and environmental conditions that are not actively extracted or analyzed for strategic insights. Similarly, internal communication platforms, while designed for collaboration, generate a wealth of textual and metadata that can reveal patterns in team dynamics, project progress, and knowledge sharing – data that often remains uncatalogued.
Unstructured and Semi-Structured Information
A significant portion of shadow data resides in unstructured or semi-structured formats. This includes documents, emails, presentations, chat logs, and media files. While these formats are intuitively understood by humans, they pose challenges for traditional data management systems that are optimized for structured databases. Consequently, valuable information contained within these files, such as research notes, design specifications, customer feedback scattered across emails, or even visual data embedded in reports, often remains hidden, inaccessible for systematic analysis.
Legacy Systems and Data Silos
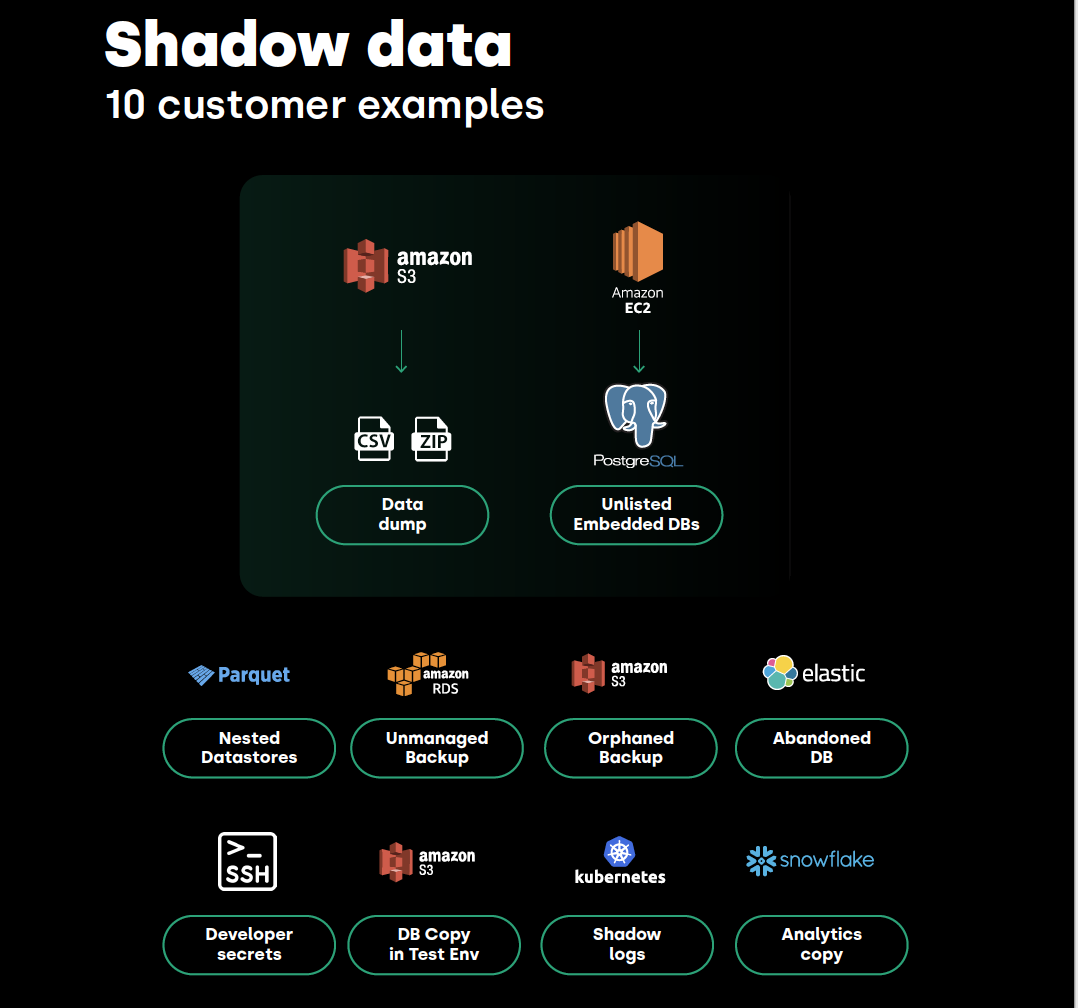
As organizations grow and evolve, they often accumulate legacy systems that continue to operate but are not fully integrated with newer platforms. These older systems may house valuable historical data that is difficult to extract or migrate. Furthermore, different departments or teams within an organization may develop their own bespoke data storage solutions or platforms, creating data silos. Information within these silos is often isolated, making it challenging to gain a holistic view of operations or to cross-reference with data from other parts of the organization. This fragmentation is a fertile ground for the proliferation of shadow data.
The Pervasive Impact of Shadow Data: Missed Opportunities and Hidden Risks
The existence of shadow data is not merely an academic curiosity; it has tangible implications for technological innovation and operational efficiency. Its presence, or rather the lack of awareness and control over it, can lead to both missed opportunities for advancement and significant unforeseen risks.
Unlocking Innovation Potential
In the realm of Tech & Innovation, data is the lifeblood of progress. Shadow data represents a vast untapped resource that could fuel groundbreaking advancements. For example, in the development of AI and machine learning models, historical operational logs, previously considered mere system artifacts, could provide invaluable training data, revealing edge cases, rare events, or subtle patterns that are crucial for building more robust and intelligent systems. Similarly, the unanalyzed communication logs from research teams might contain nascent ideas, early-stage problem-solving approaches, or overlooked experimental results that could accelerate future research and development efforts. Remote sensing technologies generate enormous amounts of raw data; if not properly cataloged and analyzed, crucial insights into environmental changes, geological formations, or infrastructure health could be lost.
Operational Inefficiencies and Redundancy
The existence of shadow data often leads to a lack of clear data ownership and governance, fostering operational inefficiencies. When data is not centralized or properly managed, multiple versions of the same information can proliferate across different systems, leading to confusion and wasted effort in data reconciliation. This redundancy can manifest in various ways, from duplicated research efforts due to lack of awareness of existing findings to conflicting operational metrics derived from disparate data sources. The inability to quickly access and verify information due to its hidden nature also slows down decision-making processes, hindering agile development and rapid iteration cycles that are crucial in fast-paced tech environments.
Security Vulnerabilities and Compliance Challenges
Perhaps the most critical impact of shadow data lies in its inherent security vulnerabilities and compliance challenges. Data that is not actively managed or governed is often not subjected to the same rigorous security protocols as actively used datasets. This can make it an attractive target for cyberattacks, leading to data breaches that expose sensitive intellectual property, confidential research findings, or personal information. Furthermore, regulatory compliance, such as GDPR or CCPA, requires organizations to have a comprehensive understanding of the data they hold and to manage it according to specific privacy and retention policies. Shadow data, by its very nature, eludes such governance, creating significant compliance risks and potential legal repercussions. The inability to locate and delete specific data upon request, for example, is a direct violation of data privacy regulations.
Harnessing the Power of Shadow Data: Strategies for Discovery and Utilization
The challenge of shadow data is not to eliminate it entirely, but rather to bring it into the light, understand its composition, and strategically leverage its value while mitigating its risks. This requires a proactive and systematic approach to data discovery, classification, and governance.
Data Discovery and Inventory
The foundational step in managing shadow data is to identify its existence and scope. This involves undertaking comprehensive data discovery initiatives. Automated tools can be employed to scan systems, storage devices, and cloud environments for various data types and formats. These tools can identify file shares, databases, cloud storage buckets, and even unstructured content within applications. Creating a centralized data inventory or catalog is crucial. This inventory should go beyond simple file listings, aiming to capture metadata such as data origin, creation date, potential owner, and even preliminary classifications based on content analysis. Techniques like data profiling and data lineage mapping can further enhance this understanding, revealing how data flows and transforms within the organization.
Data Classification and Governance Frameworks
Once discovered, shadow data needs to be classified to understand its nature, sensitivity, and potential value. This classification can range from identifying personal identifiable information (PII) and intellectual property to categorizing data based on its relevance to specific business functions or research areas. Establishing robust data governance frameworks is paramount. These frameworks should define clear policies and procedures for data ownership, access control, retention, and disposal. For shadow data, this means extending governance to cover previously unmanaged datasets. This might involve implementing automated data retention policies, establishing processes for regular data audits, and defining clear roles and responsibilities for data stewards. The goal is to move from an environment of uncontrolled data sprawl to one of managed, understood, and valuable information assets.

Strategic Utilization and Risk Mitigation
The ultimate goal is to transform shadow data from a liability into an asset. This involves identifying opportunities for its strategic utilization while simultaneously implementing robust risk mitigation strategies. For instance, anonymized or aggregated shadow data from system logs could be used to train AI models for predictive maintenance or to optimize system performance. Unstructured research notes, when properly cataloged and made searchable, could become a treasure trove for future innovation. Simultaneously, risk mitigation strategies are essential. This includes implementing advanced security measures for all discovered data, particularly sensitive information. Data masking, encryption, and strict access controls are crucial. For data deemed non-essential or redundant, secure disposal processes should be implemented in accordance with legal and organizational policies. By actively managing shadow data, organizations can unlock hidden value, drive innovation, and ensure a more secure and compliant data environment.
In conclusion, shadow data is an ever-present reality in our data-driven world. For those operating at the forefront of Tech & Innovation, understanding and addressing shadow data is not just a matter of good practice; it’s a strategic imperative. By embracing systematic discovery, robust governance, and intelligent utilization, organizations can transform the unseen streams of data into powerful catalysts for progress and a secure foundation for future endeavors.
