In the vast and ever-expanding landscape of digital technology, where data traverses global networks at lightning speed and complex systems operate with increasing autonomy, one often-unseen guardian plays a crucial role in maintaining order, integrity, and trust: cryptographic hash functions. Among these, SHA-2 stands as a cornerstone, a testament to robust security engineering that underpins countless innovations from secure web browsing to blockchain technology, and from autonomous vehicle systems to advanced remote sensing. To truly appreciate the marvels of modern tech and innovation, one must first grasp the foundational elements that make them possible, and SHA-2 is undoubtedly one such element.
SHA-2, an acronym for Secure Hash Algorithm 2, is not a product or an application you interact with directly. Instead, it’s a family of cryptographic hash functions designed by the United States National Security Agency (NSA) and first published in 2001. Its purpose is deceptively simple yet profoundly powerful: to take an input (or ‘message’) of any size and produce a fixed-size string of characters, known as a ‘hash value’ or ‘message digest.’ This unique digital fingerprint possesses properties that make it indispensable for verifying data integrity, authenticating information, and securing digital communications in an increasingly interconnected world.

The Cryptographic Cornerstone: Understanding Hash Functions
At its core, SHA-2 belongs to a class of mathematical operations known as cryptographic hash functions. Unlike encryption, which is a two-way process (encrypting and decrypting data), hashing is a one-way function. You can easily generate a hash from data, but it’s computationally infeasible to reverse the process and reconstruct the original data from the hash alone. This characteristic is fundamental to its utility in securing information and validating trust across diverse technological applications.
What is a Cryptographic Hash Function?
A cryptographic hash function is an algorithm that maps data of arbitrary size to a bit array of a fixed size. The output, often referred to as a “hash,” “digest,” or “fingerprint,” serves as a concise representation of the input data. Imagine you have a massive dataset or even a simple text file. A hash function takes that entire file and boils it down to a short, fixed-length string of letters and numbers. If even a single bit of the original file is changed, the resulting hash will be completely different, making it an excellent tool for detecting tampering or corruption.
The “cryptographic” aspect of these functions refers to a set of stringent properties that make them suitable for security applications. Without these properties, a simple checksum would suffice for basic error detection, but it wouldn’t stand up to malicious attacks.
Key Properties of SHA-2
For SHA-2 to be effective as a cryptographic tool, it must possess several crucial properties:
- Deterministic: The same input will always produce the same output hash. This consistency is essential for verification. If you hash a document today, and then hash it again tomorrow, the hashes must match perfectly to confirm the document hasn’t changed.
- Pre-image Resistance (One-Way): Given a hash value, it should be computationally infeasible to determine the original input data that produced it. This is why it’s considered a “one-way” function, preventing attackers from reversing the hash to expose sensitive information.
- Second Pre-image Resistance (Weak Collision Resistance): Given an input and its hash, it should be computationally infeasible to find another different input that produces the same hash output. This property prevents an attacker from replacing an original message with a fraudulent one that generates the same digest.
- Collision Resistance (Strong Collision Resistance): It should be computationally infeasible to find any two different inputs that produce the same hash output. This is the strongest property and the most challenging to maintain for any hash function. If collisions can be found easily, an attacker could potentially substitute one piece of data for another, both yielding the same hash, thereby undermining authenticity. SHA-2 is designed to make finding such collisions practically impossible with current computational power.
- Avalanche Effect: A tiny change in the input data (even a single bit) should result in a drastically different hash output. This makes it impossible to infer relationships between input changes and hash changes, further bolstering security.
These properties collectively ensure that SHA-2 can reliably verify data integrity and authenticate information in a trustworthy manner, making it a bedrock for countless innovative applications.
The Evolution of Secure Hashing: From SHA-1 to SHA-2 and Beyond
The development of SHA-2 was not an isolated event but rather a critical step in the ongoing arms race between cryptographers and adversaries. As computational power grows and new attack vectors emerge, cryptographic algorithms must evolve to maintain their strength.
The Limitations of Earlier Algorithms (e.g., MD5, SHA-1)
Before SHA-2, other hashing algorithms were widely used. MD5 (Message-Digest Algorithm 5), for instance, was prevalent in the 1990s. However, by the early 2000s, significant weaknesses, particularly the ability to find collisions relatively easily, rendered MD5 unsuitable for security-critical applications.
SHA-1, part of the original Secure Hash Algorithm family developed by the NSA, was seen as a successor to MD5. For a long time, it was the standard for digital signatures and integrity checks. However, theoretical weaknesses in SHA-1 were identified, and by the mid-2000s, practical collision attacks became feasible. The cryptographic community, led by organizations like NIST, began a concerted effort to deprecate SHA-1, urging a migration to stronger alternatives like SHA-2. The final nail in SHA-1’s coffin came in 2017 when Google announced the first successful practical SHA-1 collision attack, definitively demonstrating its insecurity.
The Genesis and Variants of SHA-2 (SHA-256, SHA-512, etc.)
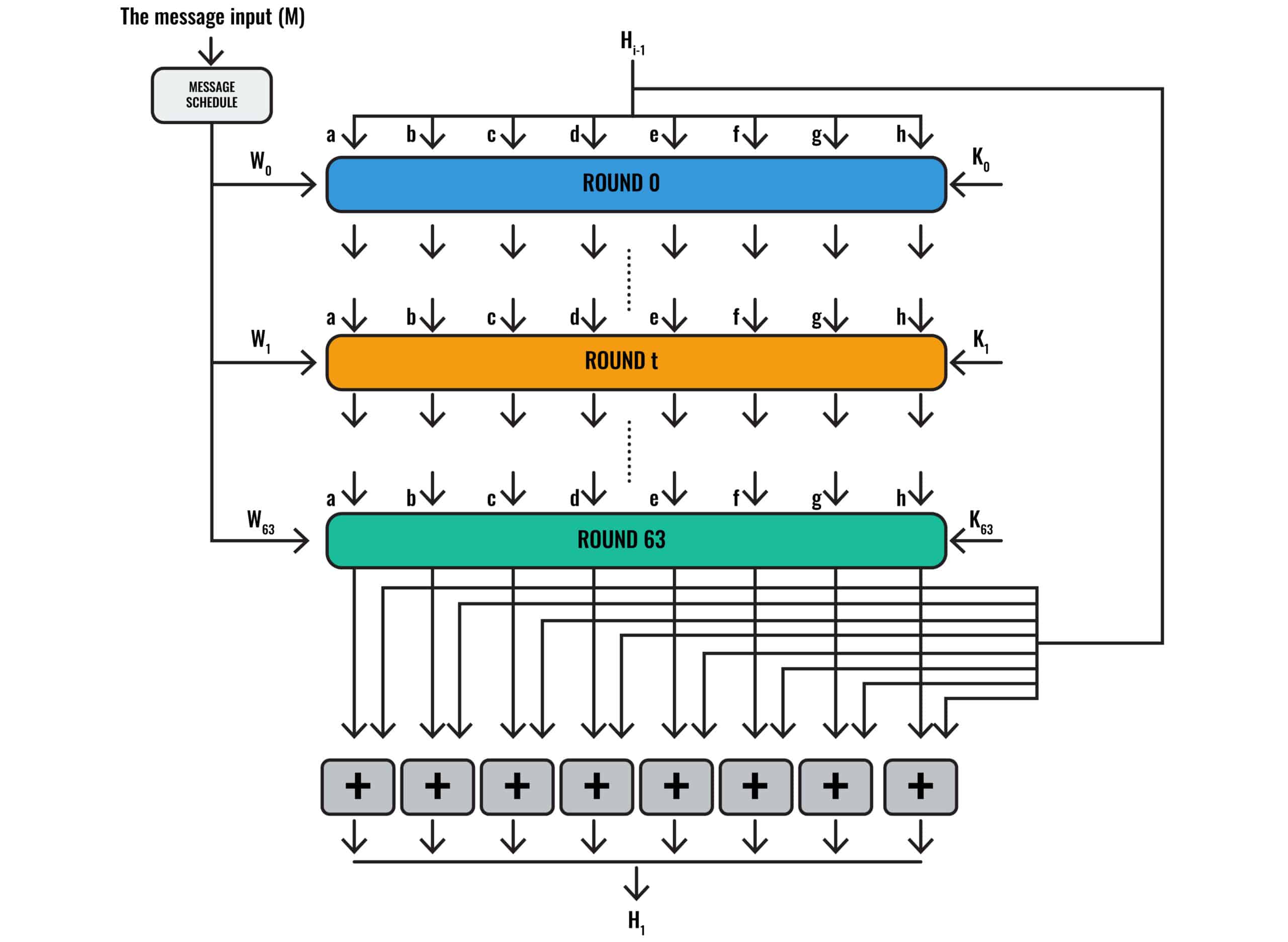
It was against this backdrop of evolving threats and the imperative for stronger security that SHA-2 emerged. The SHA-2 family comprises several functions, each differing primarily in the length of the hash value they produce, and in some cases, the mathematical operations involved. The most commonly used variants include:
- SHA-256: Produces a 256-bit (32-byte) hash value. This is one of the most widely adopted variants due to its robust security and widespread support.
- SHA-512: Produces a 512-bit (64-byte) hash value. Generally considered stronger than SHA-256 and often used in environments where even greater security is paramount, such as high-value data storage or complex digital signature schemes.
- SHA-224 and SHA-384: Truncated versions of SHA-256 and SHA-512, respectively, producing shorter hash outputs while still leveraging the underlying SHA-2 architecture. They are used in specific applications where shorter hash lengths are acceptable or required.
The different hash lengths offer varying levels of collision resistance and security. A longer hash output means a significantly larger number of possible hash values, making it exponentially more difficult for an attacker to find collisions through brute-force methods. SHA-2, particularly SHA-256 and SHA-512, remains unbroken regarding collision resistance, meaning no practical attacks have been demonstrated that violate its core security properties. This resilience has solidified its position as a go-to cryptographic primitive for modern technology and innovation.
SHA-2 in Action: Powering Modern Tech & Innovation
The practical applications of SHA-2 are ubiquitous, often working silently in the background to ensure the integrity and authenticity of our digital interactions. Its role is particularly critical in the realms of advanced technology and cutting-edge innovation, where trust, data veracity, and security are non-negotiable.
Securing Data Integrity and Authentication
One of the most fundamental applications of SHA-2 is verifying the integrity of data. When you download software, an operating system update, or even a large dataset, providers often supply a SHA-2 hash alongside the file. You can then compute the hash of the downloaded file yourself and compare it to the provided one. If they match, you can be reasonably confident that the file has not been altered or corrupted during transit. This is vital for distributing critical software and updates, protecting users from malicious injections or accidental data damage.
Beyond integrity, SHA-2 is also central to authentication. Digital signatures, which rely on cryptographic hashing, allow individuals or organizations to “sign” digital documents, proving authorship and non-repudiation. When you visit a secure website (HTTPS), your browser uses digital certificates that are signed using algorithms like SHA-2, ensuring that you are indeed communicating with the legitimate website and not an impostor.
Ensuring Trust in Autonomous Systems and IoT
The proliferation of autonomous systems – from self-driving cars and drones to smart factories and robotic surgical assistants – hinges entirely on the integrity and security of the data they process and the commands they execute. In an IoT (Internet of Things) ecosystem, where billions of devices communicate and exchange information, SHA-2 plays a pivotal role.
- Firmware Updates: Autonomous systems and IoT devices frequently receive firmware updates. SHA-2 ensures these updates are authentic and untampered with, preventing malicious actors from injecting compromised code that could hijack devices, introduce vulnerabilities, or cause catastrophic failures.
- Secure Boot: Many advanced embedded systems utilize secure boot processes, where each stage of the boot-up sequence is cryptographically verified using SHA-2 hashes. This guarantees that only authorized and unaltered software components are loaded, creating a trusted computing base from the moment the device powers on.
- Secure Communication: While SHA-2 itself isn’t an encryption algorithm, it’s often used in conjunction with encryption protocols (like TLS/SSL, which secures HTTPS traffic) to ensure the integrity of transmitted data. This is crucial for autonomous drones transmitting telemetry, sensor data, or control commands, or for IoT devices exchanging sensitive readings with cloud platforms.
Protecting Remote Sensing and Mapping Data
Innovations in remote sensing and mapping rely heavily on the collection, processing, and distribution of vast quantities of geospatial data, often from sources like satellites, aerial photography, and drones. The authenticity and integrity of this data are paramount, especially when it’s used for critical infrastructure planning, environmental monitoring, or military applications.
SHA-2 can be employed to:
- Verify Data Provenance: Ensure that remote sensing data originates from an authenticated source and has not been tampered with since its collection.
- Maintain Data Integrity: Guarantee that mapping datasets, once generated, remain consistent and free from unauthorized alterations, which could lead to critical errors in navigation, land use, or resource management.
- Secure Data Pipelines: Protect the integrity of data as it moves through various processing stages, from raw sensor readings to refined geospatial products.
Role in Blockchain and Digital Signatures
Perhaps one of the most revolutionary applications of SHA-2 is its foundational role in blockchain technology. Cryptocurrencies like Bitcoin leverage SHA-256 extensively. Each block in the blockchain contains a hash of the previous block, creating an immutable and tamper-evident chain of transactions. The process of “mining” involves repeatedly hashing transaction data until a specific target hash (with a certain number of leading zeros) is found, which is a computationally intensive task. This reliance on SHA-256 provides the security and decentralization that define blockchain systems.
Furthermore, SHA-2 is integral to creating and verifying digital signatures, which are critical for non-repudiation in digital transactions and legal documents. It ensures that a signed document has not been altered since it was signed and confirms the identity of the signer.
Implementing SHA-2: Best Practices and Future Considerations
While SHA-2 is a robust algorithm, its effective deployment requires adherence to best practices and an awareness of future challenges.
Choosing the Right Variant
For most modern applications, SHA-256 is the recommended choice, offering an excellent balance of security and performance. For applications requiring an even higher level of cryptographic strength or processing large volumes of data where output size is not a constraint, SHA-512 is often preferred. It’s crucial to select the appropriate variant based on the specific security requirements and performance characteristics of the system in question. Older, weaker hash functions like MD5 and SHA-1 should be entirely avoided in new implementations and phased out in existing ones.
The Post-Quantum Hashing Horizon
Despite SHA-2’s current strength, the advent of quantum computing presents a long-term challenge to many existing cryptographic algorithms, including those used for digital signatures and key exchange. While SHA-2 itself (as a collision-resistant hash function) is generally considered more resistant to quantum attacks than public-key cryptography (like RSA or ECC), the larger cryptographic ecosystem will need to adapt. Researchers are actively developing “post-quantum cryptography” algorithms, including new hash functions (like those in the SHA-3 family) that are designed to withstand attacks from future quantum computers. Organizations and developers should stay abreast of these developments and plan for future migrations to quantum-resistant standards, ensuring the longevity of security in their innovative solutions.
Conclusion: The Unseen Guardian of Our Digital World
SHA-2 is more than just a cryptographic algorithm; it is a fundamental building block of trust and integrity in our increasingly digital and interconnected world. From securing financial transactions and verifying software updates to ensuring the reliability of autonomous systems and the authenticity of scientific data, its silent operation underpins countless innovations that drive progress in technology. Its robust design, coupled with diligent implementation and a forward-looking perspective on emerging threats like quantum computing, will continue to make SHA-2 an indispensable guardian, allowing us to build, innovate, and connect with confidence in the digital frontier. Understanding “what is SHA-2” is to understand a vital piece of the intricate puzzle that makes modern technology both powerful and secure.
