Secrecy, at its core, is the state of being hidden or kept private, a deliberate act of withholding information or knowledge. While this definition holds true across all facets of human existence, its meaning, implications, and practical challenges undergo profound transformations when viewed through the lens of technology and innovation. In an era defined by pervasive connectivity, artificial intelligence, autonomous systems, and unprecedented data generation, the concept of secrecy is not merely a philosophical construct but a critical, dynamic challenge shaping economies, geopolitics, individual rights, and the very future of technological advancement.
This exploration delves into the multifaceted nature of secrecy within the domain of Tech & Innovation, examining how emerging technologies both threaten and enhance our ability to keep things hidden, and how the pursuit or breach of secrecy drives the relentless march of progress. From the algorithms that govern our digital lives to the classified projects pushing the boundaries of human capability, secrecy remains a potent force—a double-edged sword that can protect innovation, ensure privacy, or enable surveillance and control.
The Digital Enigma: Secrecy in the Age of Information
The digital revolution has fundamentally altered our relationship with information, making it simultaneously easier to share and more challenging to keep private. In a world where data is the new currency, understanding and managing secrecy has become paramount, intertwining deeply with concepts of personal autonomy, corporate responsibility, and national security.
Data Privacy vs. Pervasive Connectivity
The internet, once heralded as an equalizer and liberator of information, has also become an unprecedented engine for data collection. Every click, search, purchase, and interaction generates digital breadcrumbs, constructing an increasingly detailed mosaic of individual lives. This pervasive connectivity, while facilitating immense convenience and fostering global communication, presents an existential challenge to the traditional notion of personal secrecy. Social media platforms, e-commerce sites, and even seemingly innocuous apps collect vast quantities of personally identifiable information (PII), often with implicit or explicit consent that few users truly comprehend.
The tension lies in the delicate balance between the benefits of data sharing—personalized experiences, targeted services, and collaborative innovation—and the inherent human desire for privacy. Regulatory frameworks like GDPR and CCPA represent global attempts to reassert individual control over personal data, aiming to institutionalize a form of digital secrecy by requiring explicit consent, granting rights to data access and deletion, and imposing strict penalties for breaches. However, the sheer volume and velocity of data mean that maintaining true personal secrecy in a hyper-connected world requires constant vigilance and sophisticated technological tools. For many, the expectation of secrecy has shifted from an absolute right to a negotiated compromise, where some level of personal information must be surrendered for access to digital services.
The Cybersecurity Imperative: Protecting Digital Secrets
Beyond individual data, the digital landscape is rife with organizational and governmental secrets—proprietary algorithms, strategic plans, sensitive communications, and critical infrastructure blueprints. Cybersecurity, therefore, emerges as the primary technological battleground for maintaining secrecy in the digital realm. The evolution of cyber threats, from state-sponsored attacks and industrial espionage to ransomware gangs and individual hackers, necessitates a continuous arms race in defensive technologies.
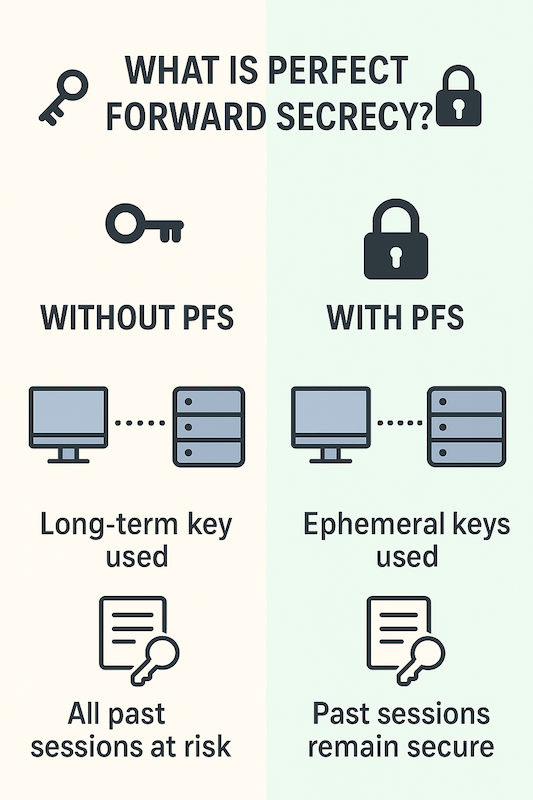
Encryption, a cornerstone of digital secrecy, employs complex mathematical algorithms to scramble information, rendering it unintelligible to unauthorized parties. From end-to-end encrypted messaging services to secure financial transactions, encryption is the invisible shield protecting countless digital secrets. Beyond encryption, advanced cybersecurity measures include intrusion detection systems, firewalls, artificial intelligence-driven threat intelligence, and secure authentication protocols. These technologies are constantly evolving to counter ever more sophisticated methods of digital intrusion and data exfiltration. The imperative to protect digital secrets drives massive investment in cybersecurity research and development, fostering innovation in areas like quantum cryptography, behavioral analytics for anomaly detection, and zero-trust architectures. The failure to maintain digital secrecy, whether through negligence or successful cyber-attacks, can lead to devastating financial losses, reputational damage, and even national security crises, underscoring the critical role of technology in preserving the integrity of hidden information.

Innovation and the Veil of Proprietary Information
In the hyper-competitive world of technology and innovation, secrecy is not just about protection; it’s a strategic asset, a competitive advantage, and a catalyst for future breakthroughs. Companies and research institutions invest billions in R&D, often with the express purpose of creating proprietary knowledge that can be kept secret from rivals.
Guarding Intellectual Property: Trade Secrets in Tech
For technology companies, intellectual property (IP) is often their most valuable asset. While patents protect inventions and copyrights cover creative works, trade secrets provide a mechanism to keep certain crucial information hidden, indefinitely. A trade secret can be any practice, process, design, instrument, pattern, commercial method, or compilation of information not generally known or ascertainable, by which a business can obtain an economic advantage over competitors or customers. Examples abound in the tech industry: Google’s search algorithm, Coca-Cola’s formula (though not tech-specific, it’s a classic example), or the specific manufacturing processes used by semiconductor giants.
The decision to protect an innovation as a trade secret rather than seeking a patent often hinges on the desire for indefinite protection and the nature of the information. Patents require public disclosure of the invention, granting protection for a limited time (typically 20 years). Trade secrets, however, can theoretically last forever, as long as reasonable efforts are made to keep them secret. Technologies play a crucial role in safeguarding trade secrets, from robust access controls and data loss prevention (DLP) systems to secure development environments and non-disclosure agreements enforced through digital means. The constant threat of industrial espionage, often facilitated by cyber means, pushes companies to continually innovate in their IP protection strategies, integrating AI for anomaly detection in data usage and blockchain for secure record-keeping of confidential exchanges.
Competitive Advantage: The Strategic Role of Secrecy in R&D
Secrecy in research and development (R&D) is a critical component of maintaining competitive advantage. Companies developing cutting-edge technologies—be it in AI, quantum computing, biotechnology, or advanced materials—often operate under layers of confidentiality. This strategic secrecy allows them to cultivate unique capabilities, refine products, and prepare for market entry without prematurely revealing their hand to competitors. The element of surprise, derived from successfully kept secrets, can be a game-changer, enabling a company to capture significant market share or establish a new industry standard.
The process of R&D itself often involves a cascade of secrets, from initial exploratory concepts to refined prototypes. Internal project management tools, secure communication channels, and segregated development environments are all technological solutions designed to maintain this secrecy. Furthermore, the hiring of top talent often comes with strict non-compete clauses and confidentiality agreements, bolstered by digital monitoring tools to prevent unauthorized information transfer. This strategic use of secrecy fuels innovation by providing a protected space for experimentation and development, allowing ideas to mature away from competitive pressure and potential infringement. However, this also raises ethical questions about transparency, especially when groundbreaking technologies could have widespread societal implications.
Autonomous Systems and the “Black Box” of AI
As technology advances towards greater autonomy and intelligence, a new dimension of secrecy emerges: the inherent opacity of complex AI systems. This “black box” phenomenon poses unique challenges to accountability, trust, and even our understanding of how these powerful technologies operate.
The Opacity of Algorithmic Decision-Making
Modern AI, particularly deep learning models, often functions as a black box. Given an input, it produces an output, but the intricate sequence of computations and transformations that led to that output remains largely opaque, even to the developers who built the system. This inherent secrecy in algorithmic decision-making arises from the complex, non-linear interactions within neural networks, which can have millions or billions of parameters. While these systems excel at tasks like image recognition, natural language processing, and predictive analytics, their internal workings are not easily interpretable by human logic.
This algorithmic secrecy presents significant challenges, especially when AI is deployed in critical applications such as medical diagnostics, financial trading, criminal justice, or autonomous vehicles. If an AI makes a discriminatory decision, causes an accident, or generates an incorrect diagnosis, understanding “why” it did so is crucial for debugging, improving, and ensuring ethical deployment. The lack of transparency can erode public trust, hinder regulatory oversight, and make it difficult to assign responsibility. The “secret” of the algorithm’s decision process is not intentionally hidden by a human agent but is rather an emergent property of its complexity, posing a new kind of secrecy that technology itself must address.
Explainable AI (XAI): Bridging the Secrecy Gap
In response to the challenges posed by AI’s black box nature, the field of Explainable AI (XAI) has emerged as a crucial area of innovation. XAI aims to develop methods and techniques that allow humans to understand, interpret, and trust the outputs of AI systems. Instead of simply providing an answer, XAI seeks to shed light on the reasoning process, making the AI’s “secrets” more accessible.
XAI approaches include techniques like saliency maps (highlighting relevant parts of an input that influenced a decision), LIME (Local Interpretable Model-agnostic Explanations), SHAP (SHapley Additive exPlanations), and attention mechanisms in neural networks. These technologies are designed to generate human-understandable explanations for AI decisions, either by simplifying the model, providing examples, or visualizing the decision process. Bridging this secrecy gap is vital for ensuring ethical AI development, enabling regulatory compliance, facilitating debugging, and fostering greater adoption of AI in sensitive domains. XAI doesn’t aim to eliminate the inherent complexity of advanced AI but rather to provide a window into its reasoning, transforming algorithmic opacity into interpretable insights and building trust in autonomous systems.
Geopolitical Dimensions: State Secrets and Surveillance Technologies
On a global scale, the concept of secrecy takes on profound geopolitical significance. Nations continually develop and employ advanced technologies to protect state secrets, conduct intelligence operations, and maintain national security, creating an intricate web of hidden capabilities and overt surveillance.
National Security and the Dual-Use Dilemma
State secrets encompass everything from classified military strategies and intelligence capabilities to sensitive diplomatic communications and critical infrastructure vulnerabilities. Protecting these secrets is a paramount function of any sovereign nation, and technology plays an indispensable role. Advanced encryption, secure communication networks, and sophisticated cyber defense systems are continuously developed and deployed to safeguard national classified information from foreign adversaries.
However, many technologies developed for national security have a “dual-use” nature, meaning they can be applied for both defensive and offensive purposes, or for purposes that raise significant ethical concerns. Surveillance technologies, for example, can be used to prevent terrorism or organized crime, but also to suppress dissent or monitor citizens without adequate oversight. The development of sophisticated drones, advanced remote sensing capabilities, and powerful data analytics platforms allows for unprecedented levels of observation and information gathering, blurring the lines between legitimate intelligence gathering and intrusive surveillance. The secrecy surrounding the development and deployment of these technologies often fuels international tension and debates over human rights, highlighting the complex ethical landscape of tech-enabled state secrecy.
The Ethics of Covert Technologies and Data Collection
The ethics surrounding covert technologies and large-scale data collection are increasingly contentious. Governments and intelligence agencies worldwide employ highly secretive technologies to intercept communications, track individuals, and analyze vast datasets to identify threats. While the stated goal is often national security, the secrecy surrounding these operations means they are often conducted without public knowledge or adequate independent oversight. This lack of transparency can lead to abuses of power, infringements on civil liberties, and the erosion of democratic norms.
Innovations in areas like facial recognition, gait analysis, predictive policing algorithms, and persistent surveillance systems raise fundamental questions about privacy in a technologically advanced society. Who has access to this data? How is it stored and secured? What are the limits of governmental data collection? The “secret” operations that leverage these technologies are often justified by the imperative of maintaining national security, but they also highlight a growing tension between collective safety and individual freedom. The ongoing debate demands a balance between the legitimate need for secrecy in certain intelligence operations and the democratic necessity of transparency and accountability for technologies that impact fundamental rights.
Navigating the Future: The Evolving Landscape of Privacy and Transparency
The relentless march of technological progress ensures that the conversation around secrecy will continue to evolve. As AI becomes more integrated into daily life, quantum computing emerges, and digital identities become increasingly complex, our understanding and management of secrecy will require continuous adaptation.
Empowering Individuals in the Data Economy
The future of secrecy in the digital age will increasingly depend on empowering individuals with greater control over their personal data. Innovations in privacy-enhancing technologies (PETs) are crucial here. These include homomorphic encryption, which allows computation on encrypted data without decrypting it; differential privacy, which adds statistical noise to datasets to protect individual identities; and decentralized identity solutions based on blockchain, giving individuals ownership of their digital credentials. These technologies aim to shift the power balance from large corporations and governments back towards the individual, providing tools to truly manage and selectively reveal their digital selves.
Furthermore, educational initiatives are vital to raise awareness about data privacy best practices and the implications of sharing personal information. As the complexity of technology grows, users need to be equipped with the knowledge to make informed decisions about their digital footprint. Empowering individuals is not about creating absolute secrecy, which may be an illusion in the modern world, but about enabling informed choice and conditional secrecy, where individuals decide what to share, with whom, and under what circumstances.
Towards a Balanced Ecosystem of Openness and Protection
Ultimately, the future of secrecy in Tech & Innovation will likely be defined by a continuous negotiation between the desire for openness and transparency, and the necessity of protection and privacy. While some secrets—like trade secrets or personal health data—deserve robust protection, others—like the inner workings of AI algorithms that impact society—demand greater transparency.
Innovation will play a critical role in finding this balance. Technologies that enhance security and privacy will continue to evolve, becoming more user-friendly and robust. Simultaneously, the demand for explainable AI and transparent governance of powerful technologies will drive new research and regulatory frameworks. The goal is not to eliminate secrecy entirely, nor to allow it to become an unchecked force, but to cultivate an ecosystem where the right amount of information is protected or revealed at the right time, by the right parties, for the right reasons. This dynamic equilibrium will shape not only the future of technology but also the fundamental nature of trust, accountability, and freedom in the digital age.
