In the intricate world of computing, where software interacts seamlessly with hardware and user preferences shape digital experiences, there exists a foundational element largely invisible to the casual user: the Windows Registry. This colossal hierarchical database is the central repository for the configuration settings of the operating system, its installed applications, and the hardware connected to it. While most users navigate Windows without ever needing to directly interact with it, power users, IT professionals, and developers often turn to the Registry Editor—a built-in utility—to fine-tune system behavior, troubleshoot issues, or unlock advanced customization options. Understanding the Registry Editor is akin to gaining access to the operating system’s very DNA, offering unparalleled control but demanding extreme caution.
The Digital Backbone of Windows
At its core, the Windows Registry is not just a collection of files; it’s the structured brain that tells Windows how to function, how to recognize devices, how to run programs, and how to present itself to the user. Introduced with Windows 3.1 and becoming central to Windows 95, it replaced the multitude of .INI and .COM files that previously stored configuration data. This consolidation brought about significant improvements in system stability, performance, and management, making it easier for applications to register their settings and for the OS to maintain a consistent state.
A Hierarchical Database
Imagine the Registry as a vast, meticulously organized library. Instead of books, it stores settings. And instead of shelves, it uses a tree-like structure, much like a file system. At the highest level are “hives” (more on these later), which contain “keys.” These keys can, in turn, contain sub-keys, forming branches that extend deep into the system’s configuration. At the end of these branches, within the keys, are “values”—the actual data entries that hold specific settings. For example, a key might represent a particular software application, with sub-keys for its various components, and values defining settings like its default save location, startup preferences, or theme choices. This hierarchical structure allows for efficient storage and retrieval of billions of settings, ensuring that Windows and its applications can quickly access the information they need to operate.
Evolution and Purpose
The introduction of the Registry was a monumental step in the evolution of Windows. Before it, system and application settings were scattered across numerous text-based .INI files. This approach suffered from several drawbacks: slow access times, difficulty in managing permissions, potential for corruption, and a lack of centralized control. The Registry addressed these issues by offering a single, unified database. It provided faster access to settings, allowed for per-user and per-machine configurations, improved security by defining access control lists (ACLs) for specific keys, and offered robust data integrity through transactional logging. Over the decades, as Windows evolved, so too did the Registry, expanding to accommodate new features, hardware standards, and software complexities. Today, it remains an indispensable component, silently orchestrating the myriad operations that define the Windows computing experience. Its purpose extends beyond mere storage; it’s a dynamic system that reflects the current state of the OS, from active user sessions to connected peripherals, making it a powerful tool for those who know how to wield it.
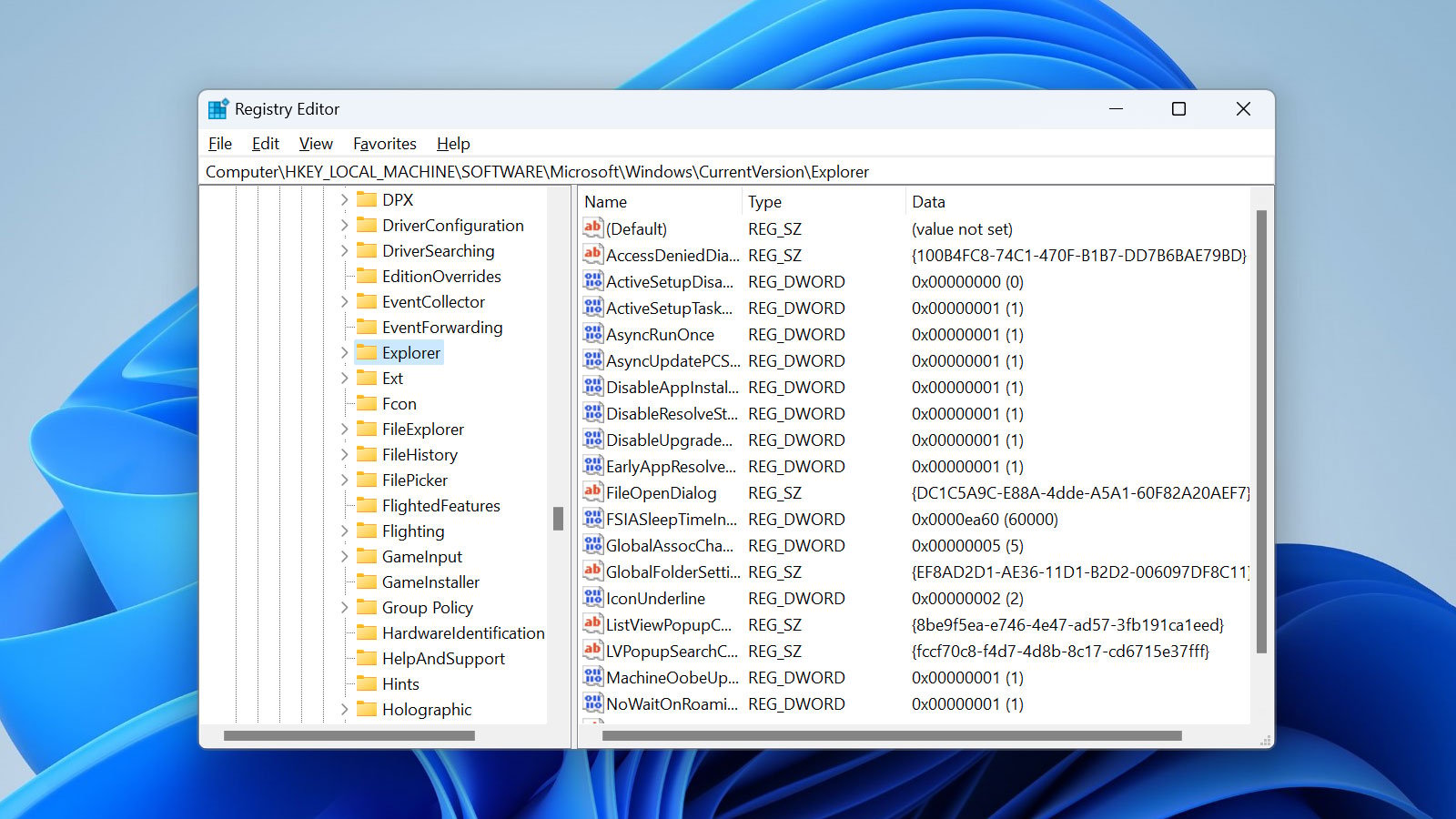
Anatomy of the Registry Editor
To interact with this digital brain, Windows provides a utility called the Registry Editor, often referred to as regedit.exe. This graphical user interface (GUI) tool presents the complex hierarchical structure of the Registry in an easily navigable format, allowing users to view, modify, create, and delete keys and values.
Keys and Values: The Building Blocks
As mentioned, the fundamental components of the Registry are keys and values.
- Keys: These are like folders in a file system. They are organizational containers that can hold other keys (sub-keys) or values. Each key has a unique path, for example,
HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionRun. This path specifies the exact location of a key within the hierarchy. - Values: These are the actual data entries, similar to files within folders. Each value has three components:
- Name: A descriptive label (e.g., “Default,” “Wallpaper”).
- Type: Specifies the format of the data (e.g., string, binary, DWORD).
- Data: The actual information stored (e.g., “C:WindowswebwallpaperWindows.jpg”, “1”).
Understanding the distinction between keys and values is crucial. Keys provide the structure, while values provide the content. Modifying the wrong key or value can have significant, sometimes irreversible, consequences.
Hives: Organizing the Chaos
The Registry is not a single, monolithic file. Instead, it’s logically divided into several distinct sections known as “hives.” Each hive is a top-level key displayed in the Registry Editor and corresponds to a physical file (or set of files) on the hard drive. These hives are:
- HKEYCLASSESROOT (HKCR): Stores information about registered applications, file associations, and OLE (Object Linking and Embedding) data. This tells Windows which program opens which file type.
- HKEYCURRENTUSER (HKCU): Contains the configuration settings specific to the currently logged-on user. This includes desktop settings, network connections, and environmental variables.
- HKEYLOCALMACHINE (HKLM): Holds configuration settings that apply to the entire computer and all users. This includes hardware configuration, security accounts manager (SAM) data, and system-wide software settings.
- HKEYUSERS (HKU): Contains all the user profiles loaded on the computer, including HKEYCURRENT_USER as a sub-key for the active user.
- HKEYCURRENTCONFIG (HKCC): Contains a snapshot of the hardware profile currently being used.
These hives are dynamically loaded and unloaded as needed, enhancing system performance and stability. For instance, user-specific hives are loaded only when a user logs on.
Understanding Data Types
The “type” of a Registry value dictates how the data is interpreted and stored. Common data types include:
- REG_SZ (String Value): A standard text string, often used for paths, names, or descriptive text.
- REGEXPANDSZ (Expandable String Value): A text string that can contain environment variables (e.g.,
%SystemRoot%), which are expanded when read. - REG_BINARY (Binary Value): Raw binary data, often used for hardware component information or complex settings.
- REG_DWORD (DWORD Value): A 32-bit number (integer), typically used for boolean flags (0 for false, 1 for true), counts, or other numerical settings. It can be displayed in decimal or hexadecimal format.
- REG_QWORD (QWORD Value): A 64-bit number, similar to DWORD but for larger numerical values, common in 64-bit Windows.
- REGMULTISZ (Multi-String Value): A list of strings, separated by null characters, often used for lists of files or other multiple entries.
Choosing the correct data type is essential when creating or modifying values, as Windows expects data in a specific format for its operations. Incorrect data types can lead to system instability or application failures.
Common Use Cases and Applications
While the Registry Editor is often depicted as a dangerous tool for the inexperienced, it serves a critical role for those who understand its intricacies. Its applications range from deep system customization to essential troubleshooting.
Customizing System Behavior
For users seeking to personalize their Windows experience beyond the standard Control Panel or Settings app, the Registry Editor offers a gateway to granular control. Examples include:
- Disabling specific features: Turning off Windows Defender components, specific startup items, or context menu entries.
- Changing UI elements: Modifying taskbar behavior, icon spacing, or desktop appearance in ways not exposed through standard settings.
- Optimizing performance: Tweaking memory management settings, disk cache sizes, or network adapter behaviors.
- Altering default actions: Forcing certain programs to open specific file types or changing the behavior of system hotkeys.
These customizations, while powerful, must be approached with caution, as improper modifications can lead to unexpected behavior or system instability.
Troubleshooting and Performance Tweaks
When Windows encounters issues or applications misbehave, the Registry can often provide clues or solutions. Corrupted Registry entries can lead to startup problems, application crashes, or driver conflicts. IT professionals frequently use the Registry Editor to:
- Fix stubborn errors: Removing residual entries from uninstalled software that prevents new installations, or repairing incorrect file associations.
- Resolve driver conflicts: Identifying and modifying entries related to problematic device drivers.
- Diagnose malware issues: Malware often leaves traces or creates auto-start entries in the Registry, which can be identified and removed manually.
- Apply performance tweaks: Adjusting buffer sizes, disabling unnecessary animations, or optimizing boot parameters for specific hardware configurations.
For these reasons, the Registry Editor is an indispensable tool in any advanced troubleshooting toolkit.
Software Configuration Management
Developers and system administrators also rely on the Registry for advanced software configuration. Applications register their settings here, allowing them to persist across sessions and be accessible to different user accounts. This enables:
- Centralized application settings: Programs store user-specific preferences (HKCU) and machine-wide defaults (HKLM).
- Installation and uninstallation management: The Registry tracks installed software, its components, and uninstallation routines.
- Group Policy application: In corporate environments, Group Policy settings—which dictate user and computer configurations—are largely implemented by modifying Registry keys.
This makes the Registry a critical component for managing software lifecycles and enforcing organizational policies.
Security and Privacy Adjustments
The Registry also plays a significant role in controlling Windows security and privacy settings. Many security features, though exposed through the Security Center, can also be directly managed via Registry entries. This includes:
- Disabling telemetry: While Windows provides some privacy settings, advanced users can further restrict data collection by modifying specific Registry keys.
- Enhancing firewall rules: Some intricate firewall configurations or network security policies can be fine-tuned via the Registry.
- Controlling user account privileges: While primarily managed by User Account Control (UAC) and Group Policy, some related security settings can be found and adjusted in the Registry.
- Locking down system features: Preventing users from accessing certain system tools or making specific changes, useful in shared or public computer environments.
However, making incorrect security-related changes without proper understanding can inadvertently open up vulnerabilities or restrict legitimate system functions.
Navigating and Editing with Caution
The power offered by the Registry Editor comes with significant responsibility. Because it underpins the entire operating system, an incorrect modification can render Windows unbootable, cause application failures, or introduce subtle, hard-to-diagnose issues.
Best Practices for Registry Modification
When venturing into the Registry Editor, adherence to best practices is paramount:
- Understand the change: Never modify a Registry entry without fully understanding its purpose and potential impact. Research online resources, official documentation, or trusted tech communities before making any changes.
- Locate the correct path: Ensure you are navigating to the exact key and value intended. A slight deviation can lead to unintended consequences.
- Note original values: Before changing any value, make a note of its original data. This provides a rollback point if the modification causes issues.
- Avoid random deletion: Deleting keys or values arbitrarily is extremely dangerous and almost always leads to system instability. Only delete entries if you are certain they are obsolete, corrupted, or specifically instructed to do so by a reliable source for troubleshooting.
- Reboot if necessary: Some Registry changes require a system restart to take effect. Always test the system after a change to ensure stability.
Backup and Restore Strategies
The single most important safety measure when editing the Registry is to back it up. Windows provides several methods for this:
- System Restore Points: Creating a System Restore Point before making significant Registry changes is highly recommended. This allows you to revert your system to an earlier working state if issues arise.
- Exporting Keys/Hives: Within the Registry Editor, you can export individual keys, branches, or even entire hives to a
.REGfile. This file can later be imported to restore the backed-up settings. For critical changes, it’s often wise to export the specific key you’re about to modify. - Full Registry Backup: Third-party tools or advanced Windows utilities can perform a comprehensive backup of the entire Registry.
Having a robust backup strategy ensures that even if a modification goes wrong, you have a recovery path, mitigating the risk of total system failure.
Tools and Alternatives for Safe Management
For those who need to manage Registry settings but prefer a safer or more automated approach, several alternatives exist:
- Group Policy Editor (gpedit.msc): For Professional, Enterprise, and Education editions of Windows, this tool provides a user-friendly interface for managing many system and security settings that ultimately translate into Registry changes. It’s much safer than direct
regeditmanipulation. - PowerShell/Command Prompt: Advanced users can script Registry changes using PowerShell cmdlets (
Get-ItemProperty,Set-ItemProperty,New-ItemProperty,Remove-ItemProperty) orreg.execommands. This allows for automation and precise control, especially in batch operations or deployment scenarios. - Third-party Registry Cleaners/Optimizers: While some of these tools can be beneficial, many are snake oil or can cause more harm than good. Exercise extreme caution and research thoroughly before using them. It’s generally safer to manually manage the Registry or use official Windows tools.
- Dedicated Configuration Tools: Many applications provide their own GUI settings panels, which are the safest way to modify their respective configurations, as these tools handle the underlying Registry changes correctly.
For most users, relying on these safer alternatives and only resorting to regedit when absolutely necessary and with proper guidance is the recommended approach.
The Future of System Configuration
As technology evolves, so too do the methods by which operating systems and applications are configured. While the Registry has served Windows reliably for decades, the push towards more intuitive, secure, and cloud-integrated experiences is shaping new paradigms for system configuration.
Abstraction and User Interfaces
Modern operating systems, including Windows, are increasingly abstracting away the direct interaction with underlying configuration mechanisms like the Registry. The trend is towards more user-friendly interfaces (like the Settings app in Windows 10/11) that provide clear, categorized options without exposing the user to the complexity of keys and values. This abstraction reduces the learning curve, minimizes the risk of accidental damage, and makes systems more accessible to a broader audience. While the Registry still exists in the background, future innovations will likely continue to build layers of abstraction, allowing users to configure their systems through higher-level policies and preferences rather than raw data entries.
Cloud-Based Settings and Synchronization
The advent of cloud computing and persistent user profiles has introduced the concept of synchronizing settings across multiple devices. Modern operating systems leverage cloud services to store user preferences, application settings, and even device configurations, allowing for a seamless experience whether a user logs into a new PC, a tablet, or a virtual machine. This represents a significant shift from purely local, Registry-bound settings. Future innovations will likely expand on this, enabling more sophisticated synchronization capabilities, version control for settings, and potentially even AI-driven profile management that adapts to a user’s context and device.
AI-Driven Configuration Management
Looking further ahead, artificial intelligence (AI) and machine learning (ML) are poised to revolutionize system configuration. Imagine an operating system that learns your preferences, usage patterns, and hardware capabilities, then autonomously optimizes system settings for performance, battery life, or security, without any manual intervention. AI could identify and fix corrupted configuration entries, predict potential conflicts before they occur, or even suggest optimal settings for new software installations. While the Registry might still exist as a low-level storage mechanism, AI could provide an intelligent layer that interprets, modifies, and manages these settings dynamically, making manual Registry editing a rare, niche activity reserved for highly specialized tasks. This would represent a true leap in “Tech & Innovation,” transforming system configuration from a static database management task into an adaptive, intelligent process.
In conclusion, the Windows Registry Editor remains a powerful, if somewhat arcane, tool. It is the deep control panel of the operating system, offering unparalleled insight and control for those who dare to venture into its labyrinthine structure. While its direct interaction may diminish for the average user with the rise of abstraction and AI-driven systems, its foundational role in how Windows operates ensures its continued relevance in the realm of Tech & Innovation for power users and system administrators for years to come.