Wi-Fi Protected Access (WPA) and its subsequent iterations represent the dominant security protocols for wireless local area networks (WLANs). Among these, Pre-Shared Key (PSK) authentication stands as a foundational and widely adopted method, particularly in home and small office environments. Understanding PSK is crucial for anyone looking to secure their wireless network against unauthorized access. This article delves into the intricacies of PSK, exploring its operational mechanisms, various implementations, and its role in safeguarding our increasingly connected lives.
The Fundamentals of Pre-Shared Key (PSK) Authentication
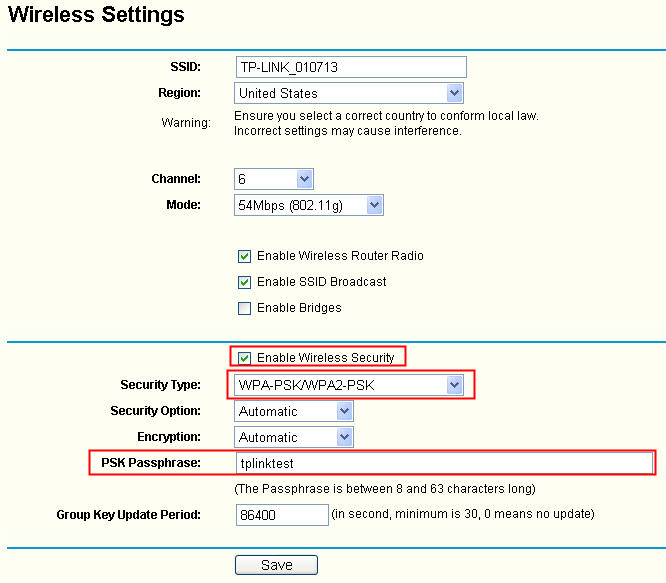
At its core, PSK authentication relies on a shared secret – the pre-shared key – that is known to both the wireless access point (AP) and all authorized client devices. This key, often referred to as the Wi-Fi password, is the primary mechanism for verifying the identity of devices attempting to connect to the network.
How PSK Works: The Handshake Process
When a client device, such as a laptop or smartphone, seeks to connect to a WPA/WPA2/WPA3-PSK enabled network, a process known as the four-way handshake takes place. This handshake is designed to ensure that both the client and the AP possess the correct PSK without ever explicitly transmitting the key over the air.
- Authenticator (AP) sends an Authenticator Nonce (ANonce): The AP generates a random number called an ANonce and sends it to the client.
- Supplicant (Client) sends a Supplicant Nonce (SNonce): The client, upon receiving the ANonce, generates its own random number, the SNonce, and sends it back to the AP.
- AP Computes Keys and Sends Authenticator Message: The AP combines the PSK, the ANonce, and the SNonce (along with other network-specific information like the SSID) and uses cryptographic functions to derive a Pairwise Transient Key (PTK) and a Group Temporal Key (GTK). The PTK is unique to the client-AP session and is used for encrypting unicast traffic (data sent from one device to another). The GTK is used for encrypting multicast and broadcast traffic. The AP then sends an Authenticator message to the client, which includes these derived keys.
- Client Computes Keys and Sends Supplicant Message: The client performs the same cryptographic operations using its received ANonce, its own SNonce, and the shared PSK. If the calculated keys match those derived by the AP, the client sends a Supplicant message back. This message is encrypted using the PTK, proving that the client knows the PSK.
If the handshake is successful, the client is authenticated and can begin transmitting and receiving encrypted data. This handshake is critical because it establishes unique encryption keys for each session, providing a layer of security even if the PSK itself is compromised.
The Role of the PSK (Wi-Fi Password)
The PSK is the cornerstone of this authentication method. Its strength and secrecy are paramount to the overall security of the network. A strong PSK should be:
- Long: Generally, more characters offer greater security.
- Complex: A mix of uppercase and lowercase letters, numbers, and symbols makes it harder to guess.
- Unique: Avoid using common words, personal information, or easily guessable patterns.
- Kept Secret: This is the most crucial aspect. Sharing the PSK with unauthorized individuals negates its security purpose.
Evolution of PSK: WPA, WPA2, and WPA3
PSK has evolved alongside the Wi-Fi security standards to address evolving threats and improve security.
WPA-PSK (Wi-Fi Protected Access)
WPA was developed as an interim solution to address the significant vulnerabilities found in the original WEP (Wired Equivalent Privacy) protocol. WPA-PSK uses the Temporal Key Integrity Protocol (TKIP) for encryption, which, while an improvement over WEP, has known weaknesses and is now considered deprecated. Despite its age, WPA-PSK might still be encountered on older devices or networks for compatibility reasons.
WPA2-PSK (Wi-Fi Protected Access II)
WPA2-PSK is the most prevalent and widely supported PSK implementation. It mandates the use of the Advanced Encryption Standard (AES) encryption algorithm, specifically AES-CCMP (Counter Mode with Cipher Block Chaining Message Authentication Code Protocol). AES is a much more robust and secure encryption standard than TKIP. WPA2-PSK offers a significant leap in security over WPA-PSK, making it the recommended standard for most home and small business networks for many years.
Key advantages of WPA2-PSK:
- Stronger Encryption: AES provides superior protection against brute-force attacks and cryptographic weaknesses.
- Widespread Compatibility: Almost all modern Wi-Fi devices support WPA2.
However, even WPA2-PSK is not entirely immune to attacks. The primary vulnerability lies in the initial handshake. If an attacker can capture the four-way handshake, they can then attempt to crack the PSK offline using dictionary attacks or brute-force methods, especially if the PSK is weak.
WPA3-PSK (Wi-Fi Protected Access 3)
WPA3 represents the latest generation of Wi-Fi security, building upon the strengths of WPA2 and introducing enhanced protection mechanisms, especially for PSK networks. WPA3-PSK brings several critical improvements:

- Simultaneous Authentication of Equals (SAE): This is perhaps the most significant advancement for PSK. SAE replaces the four-way handshake with a Diffie-Hellman key exchange variant. This provides “forward secrecy,” meaning that even if the PSK is compromised later, past communications cannot be decrypted because each session uses unique, ephemeral encryption keys that are not derived directly from the PSK itself in a way that can be easily reversed. SAE also makes offline dictionary attacks significantly more difficult.
- Enhanced Open Network Security: For public Wi-Fi networks where PSK is not practical (as there’s no shared secret), WPA3 introduces Wi-Fi Enhanced Open™, which provides individualized data encryption between the user and the network, preventing passive eavesdropping.
- Stronger Encryption for Enterprise Networks: While not directly related to PSK, WPA3 also offers 192-bit encryption for enterprise networks, further enhancing security for sensitive environments.
Adoption of WPA3-PSK:
While WPA3 offers superior security, its adoption is still ongoing. It requires both the access point and the client devices to support WPA3. Older devices may not be compatible, necessitating a rollback to WPA2 or a mixed mode (WPA2/WPA3) for backward compatibility, which can sometimes reduce the overall security benefit.
Security Considerations and Best Practices for PSK Networks
Implementing PSK authentication is a critical step in securing a Wi-Fi network, but it’s not a foolproof solution on its own. Adhering to best practices can significantly bolster your network’s defenses.
Choosing a Strong PSK
As mentioned earlier, the strength of your PSK is paramount. Avoid:
- Dictionary words or common phrases.
- Personal information like names, birthdays, or addresses.
- Sequential or repetitive characters (e.g., “12345678,” “abcdefgh,” “aaaaaaaa”).
- Simple modifications of common passwords.
Instead, opt for a long (15+ characters), random, and complex password that combines uppercase and lowercase letters, numbers, and special characters. Consider using a password manager to generate and store strong, unique passwords for all your devices and networks.
Regularly Changing Your PSK
While not strictly necessary if your PSK is robust and never compromised, periodically changing your PSK can add an extra layer of security. This is especially important if you suspect unauthorized access or if you have recently had guests connected to your network.
Network Segmentation and Guest Networks
For home and small businesses, consider creating a separate guest network. This allows visitors to access the internet without giving them access to your primary network and its connected devices. Guest networks typically use a different PSK and are often isolated from the main network.
Firmware Updates
Ensure that your router and access point firmware are always up-to-date. Manufacturers regularly release firmware updates that patch security vulnerabilities discovered in their devices. Outdated firmware can leave your network exposed to known exploits.
MAC Address Filtering (Limited Benefit)
While MAC address filtering (allowing only devices with specific hardware addresses to connect) can be configured, it offers minimal real security. MAC addresses can be easily spoofed, making this feature more of a deterrent for casual attackers than a robust security measure.
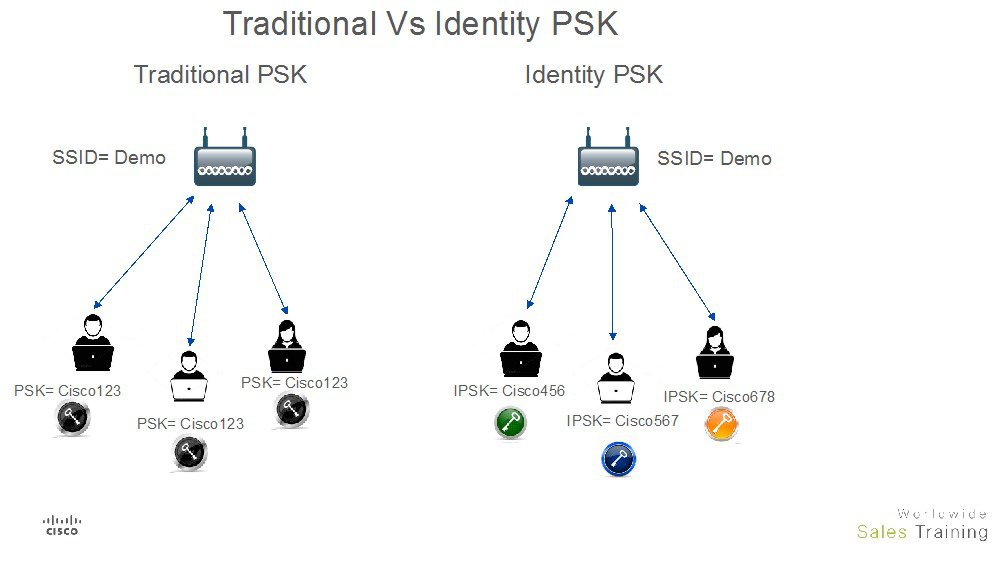
Understanding the Limits of PSK
It’s important to recognize that PSK authentication is primarily designed for trusted environments. In public or untrusted networks, where multiple users share the same PSK, the security of individual users’ data can be compromised. This is where WPA3’s SAE and Enhanced Open™ features offer significant improvements.
Conclusion: PSK’s Enduring Role in Wireless Security
Pre-Shared Key authentication, in its various forms, remains a cornerstone of wireless network security. From its early implementation in WPA to the robust protections offered by WPA3-PSK, the principle of a shared secret to authenticate devices has proven to be an effective and widely adopted solution. While WPA2-PSK has served the majority of users reliably for years, the advancements in WPA3, particularly SAE, are crucial for addressing the evolving landscape of cyber threats.
Understanding how PSK works, the differences between its implementations, and adopting strong security practices are essential for safeguarding your wireless network. As our reliance on Wi-Fi continues to grow, ensuring its security through protocols like WPA3-PSK is not just a technical consideration but a fundamental aspect of digital privacy and protection. The journey of PSK mirrors the continuous innovation in cybersecurity, striving to keep our connected world safe and secure.
