In the rapidly evolving landscape of drone technology, innovation often stems not just from cutting-edge hardware, but also from the robust, secure, and flexible software infrastructure that underpins it. At the heart of managing and interacting with many advanced drone systems – from on-board companion computers to sophisticated ground control stations and cloud-based data processing hubs – lies the Secure Shell (SSH) protocol. SSH provides a cryptographic network protocol for operating network services securely over an unsecured network, and on Linux systems, it is the de facto standard for remote command-line access.

Understanding “options” in SSH is not merely a technicality for system administrators; it is a critical skill for drone developers, researchers, and operators. These options are the configurable parameters that allow users to fine-tune SSH connections, enhancing security, improving automation, optimizing performance, and enabling complex functionalities essential for deploying and maintaining innovative drone solutions. This article delves into what SSH options are, why they are indispensable in the drone ecosystem, and how their judicious use fuels the next generation of aerial technology.
The Foundational Role of SSH in Drone Ecosystems
The conventional image of drone operation often involves a pilot with a remote controller. However, the true innovation in modern drone technology extends far beyond manual flight. Autonomous missions, data analytics at the edge, real-time telemetry processing, and sophisticated swarm intelligence all rely on interconnected computing systems, many of which run Linux. SSH serves as the secure backbone for interacting with these critical components.
Beyond the Controller: Accessing Onboard Linux Systems
Many high-end drones, particularly those used for research, industrial inspections, or complex autonomous tasks, incorporate powerful companion computers (e.g., Raspberry Pi, NVIDIA Jetson, Intel NUC) running Linux distributions. These onboard systems process sensor data, execute flight control algorithms, manage payloads, and handle communication. Accessing these systems for development, debugging, or mission configuration while the drone is on the ground (or even in flight via a secure wireless link) is paramount. SSH provides this secure conduit, allowing developers to upload code, inspect logs, modify parameters, and troubleshoot issues directly on the drone’s brain. Without SSH, direct physical access to these tiny, often embedded, computers would be cumbersome and impractical, significantly slowing down the innovation cycle.
Ground Control and Data Hubs: The Server-Side Perspective
Beyond the drone itself, ground control stations (GCS) and backend data processing servers frequently run Linux. These systems might host mission planning software, store flight logs, process imagery and LiDAR data, or manage fleets of drones. SSH enables secure remote access for administrators and data scientists to these critical infrastructure components. For instance, a drone operator might use SSH to securely transfer gigabytes of high-resolution aerial imagery from a GCS to a cloud-based processing server, or a developer might SSH into a remote server to deploy updates to the fleet management software. The security and versatility offered by SSH are indispensable for maintaining the integrity and efficiency of these operations.
Security Imperatives for Autonomous and Connected Drones
As drones become more autonomous and interconnected, the security of their communication channels is non-negotiable. Malicious actors attempting to hijack a drone, steal sensitive data, or disrupt critical missions pose significant threats. SSH, with its robust encryption and authentication mechanisms, is a cornerstone of this security. By ensuring that all remote interactions with Linux-based drone components are encrypted and authenticated, SSH helps protect against eavesdropping, data tampering, and unauthorized access, fostering trust and reliability in advanced drone operations. The ability to configure SSH connections with specific security options becomes a powerful tool in mitigating these risks.
Demystifying SSH Options: Customizing Connectivity for Drone Applications
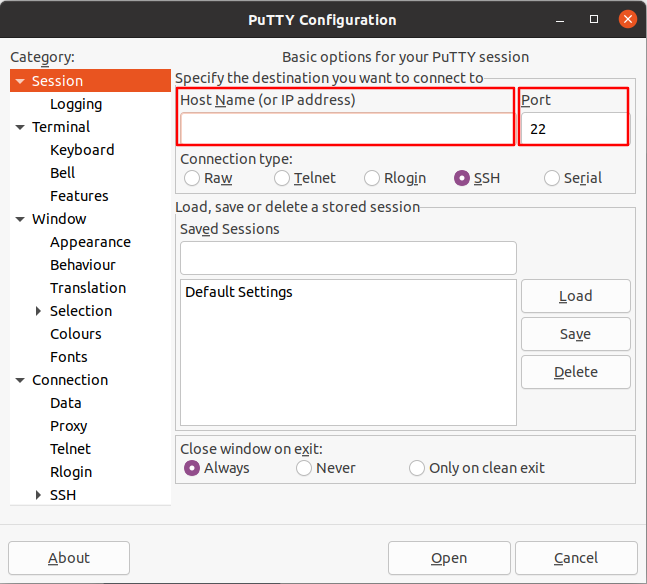
At its core, an “option” in SSH refers to a parameter that modifies the behavior of the SSH client or server. These options can be specified on the command line, within user-specific configuration files (~/.ssh/config), or system-wide configuration files (/etc/ssh/ssh_config for clients, /etc/ssh/sshd_config for servers). For drone applications, leveraging these options is key to tailoring SSH connections to specific operational requirements.
Authentication Methods: Key-Based Security for Drone Networks
One of the most critical sets of SSH options relates to authentication. While password-based authentication is common, it’s generally considered less secure and cumbersome for automated or frequent access. For drone systems, key-based authentication is often preferred.
IdentityFile: This option specifies the path to a private key file used for public key authentication. Instead of typing a password, the SSH client uses this private key to prove its identity to the server, which holds the corresponding public key. For drones, this means a developer can securely connect to an onboard companion computer without ever exposing a password, ideal for automated scripts or situations where human intervention is minimized.IdentitiesOnly: When set toyes, this option ensures that the SSH client only attempts authentication using the identity files explicitly configured or specified on the command line, preventing it from trying other potentially insecure or unnecessary identity files.PasswordAuthentication: This server-side option (insshd_config) can be set tonoto disable password authentication entirely, forcing clients to use more secure methods like public key authentication. This is a common security hardening step for drone ground stations and onboard systems.
Port Forwarding and Tunnels: Bridging Gaps for Telemetry and Services
SSH’s ability to create secure tunnels and forward ports is invaluable for drone operations, allowing access to services that might otherwise be blocked by firewalls or simply not exposed directly.
LocalForward(or-Lon command line): This option forwards a port on the local machine to a port on a remote machine through the SSH connection. For instance, a drone might run a web-based diagnostics interface on its companion computer (port 8000). Usingssh -L 8888:localhost:8000 user@drone_ip, a developer can access that interface by navigating tohttp://localhost:8888in their browser, with all traffic securely tunneled over SSH. This is crucial for accessing internal services without exposing them directly to the open network.RemoteForward(or-Ron command line): This option does the reverse, forwarding a port on the remote machine to a port on the local machine. Imagine a drone in the field needs to send specific telemetry data to a local service running on a developer’s laptop behind a firewall. A reverse tunnel initiated from the drone can make this possible, securely pushing data back to the developer.DynamicForward(or-Don command line): This creates a SOCKS proxy server on the local machine. Any application configured to use this SOCKS proxy can then securely route its traffic through the SSH server. This can be useful for general secure browsing or accessing multiple services on a remote drone network.
Configuration Management: Streamlining Drone Fleet Deployment
For managing multiple drones or complex ground infrastructure, SSH configuration files (e.g., ~/.ssh/config) are powerful tools. They allow users to define aliases and apply specific options for different hosts, streamlining workflow and reducing errors.

-
Host: This keyword defines a block of configuration options that apply only when connecting to a specific host or group of hosts. For example:Host drone_alpha Hostname 192.168.1.101 User pi IdentityFile ~/.ssh/id_drone_alpha Port 2222 # If SSHD is on a non-standard port LocalForward 8888 localhost:8000 Host gcs_server Hostname gcs.mydronecorp.com User admin IdentityFile ~/.ssh/id_gcs RemoteForward 9999 localhost:9999With this configuration, connecting to
ssh drone_alphaautomatically uses the specified IP, user, private key, and sets up the port forwarding, saving time and ensuring consistency.
Essential SSH Options for Drone Developers and Operators
Beyond the fundamental options, several others prove incredibly useful for practical drone management.
Port: Specifies the port number to connect on the remote host. While 22 is default, changing it to a non-standard port (e.g., 2222) on drone companion computers can slightly reduce automated scanning attempts.ServerAliveInterval/ServerAliveCountMax: These options help maintain SSH connections over unstable networks, common in field drone operations.ServerAliveIntervalsends a null packet after a specified number of seconds if no data has been received from the server, preventing firewalls from closing idle connections.ServerAliveCountMaxdefines how many such packets can be sent without response before the client disconnects.ConnectTimeout: Useful for scripting, this option specifies the timeout (in seconds) for connecting to the SSH server. It helps prevent scripts from hanging indefinitely if a drone is unreachable.StrictHostKeyChecking: When set toyes(the default), SSH will refuse to connect if the host key changes, protecting against man-in-the-middle attacks. While crucial for security, it can be cumbersome in dynamic drone development environments where IP addresses or configurations change frequently. Setting it tonooraccept-new(with caution) might be used temporarily during testing phases, butyesis highly recommended for production systems.
Advanced SSH Techniques for Cutting-Edge Drone Innovation
As drone systems grow in complexity, advanced SSH options facilitate more intricate network architectures and automation.
SSH ProxyJump: Securely Traversing Complex Drone Networks
For large-scale drone operations or segregated networks, direct SSH access to every drone or component might not be possible or desired. Instead, a “jump host” or “bastion host” might be used as an intermediary. ProxyJump (or -J on the command line) allows an SSH client to connect to a target host by first connecting to a jump host. This is invaluable for securely accessing drones in isolated network segments without exposing them directly to the internet.
Host target_drone
Hostname 10.0.0.50
ProxyJump jump_host
Host jump_host
Hostname jump.mydronecorp.com
User bastion_user
IdentityFile ~/.ssh/id_bastion
Now, ssh target_drone will automatically route the connection through jump_host, providing a secure pathway.
SSH for Automation: Scripting Drone Management Tasks
Many SSH options are designed to facilitate non-interactive use, which is fundamental for automating drone maintenance, data collection, and software deployment. By combining key-based authentication with non-interactive command execution, scripts can perform tasks like:
- Automatically fetching telemetry logs from a fleet of drones.
- Pushing software updates to onboard companion computers.
- Triggering diagnostic routines on ground control servers.
BatchMode yesensures that the client will never ask for a password or passphrase, making it suitable for scripts where user interaction is not possible.
Securing Data in Transit: Integrating SSH with Drone Data Pipelines
Beyond remote command execution, SSH can be integrated into broader data pipelines. scp (Secure Copy Protocol) and rsync over SSH are widely used for secure, efficient file transfers of large datasets, such as high-resolution imagery or sensor readings collected by drones. Options like -C for compression can significantly speed up transfers over bandwidth-limited connections, a common scenario in drone field operations. By leveraging SSH’s robust encryption, drone data remains protected from interception during transit, from the drone’s edge computer to a ground station, and then to cloud analytics platforms.
Best Practices for SSH Security in Drone Operations
While SSH options provide immense flexibility, security remains paramount, especially given the sensitive nature of drone operations.
- Always Use Key-Based Authentication: Disable password authentication on all public-facing SSH servers related to drone systems (e.g., ground stations, cloud servers). Use strong, unique private keys for each user/service and protect them with strong passphrases.
- Principle of Least Privilege: Create specific users with minimal necessary permissions for drone-related SSH access. Avoid using
rootfor direct SSH logins. - Harden SSH Server Configurations: Regularly review and secure
sshd_config. Disable features not in use, limit user access, and consider tools likefail2banto thwart brute-force attacks. - Regular Audits and Updates: Keep SSH clients and servers updated to patch known vulnerabilities. Regularly audit access logs (
/var/log/auth.logon Linux) for suspicious activity. - Restrict
StrictHostKeyChecking: For production drone systems, ensureStrictHostKeyChecking yesis in effect to prevent man-in-the-middle attacks.
Conclusion
The humble “option” in SSH on Linux is anything but trivial; it is a powerful lever for innovation in the drone industry. By mastering these configurable parameters, developers and operators can build more secure, efficient, and robust systems for managing and interacting with complex drone hardware and software. From securing onboard companion computers and streamlining ground control operations to enabling automated data pipelines and intricate network architectures, SSH options are an indispensable part of the “Tech & Innovation” driving the future of unmanned aerial systems. Understanding and applying these options effectively is not just good practice; it’s a strategic imperative for anyone serious about pushing the boundaries of drone technology.
