In the rapidly evolving landscape of modern technology, particularly within the context of interconnected systems, the concept of network segregation has emerged as a critical pillar of robust security and efficient operation. Far from being a mere technical buzzword, network segregation is a fundamental strategy that involves dividing a computer network into smaller, isolated segments. This division is not arbitrary; it’s a deliberate architectural choice designed to enhance security, improve performance, and simplify management. Understanding network segregation is paramount for anyone involved in designing, implementing, or securing any networked environment, from small businesses to large enterprises, and increasingly, in specialized fields like drone operations.

The core principle behind network segregation is to create boundaries. These boundaries act as digital fences, controlling the flow of traffic and information between different parts of the network. Without segregation, a network can be viewed as a single, sprawling entity where a breach in one area could potentially compromise the entire system. By segmenting the network, the impact of a security incident can be contained, limiting lateral movement for attackers and reducing the blast radius of any potential exploit. This is analogous to how modern buildings are designed with fire-resistant walls and separate ventilation systems to prevent the spread of a fire.
The benefits of network segregation extend beyond mere security. It can also lead to significant performance improvements. By isolating different types of traffic or user groups, network administrators can prioritize critical data flows and prevent less important traffic from consuming valuable bandwidth. This is especially relevant in environments that handle diverse workloads, such as real-time data processing, high-definition video streaming, or mission-critical communications. Furthermore, a segregated network is often easier to manage and troubleshoot. With clearly defined segments, it becomes simpler to monitor traffic, identify bottlenecks, and diagnose issues without impacting the entire network. This article will delve into the intricacies of network segregation, exploring its various forms, implementation methods, and its profound implications for cybersecurity and operational efficiency.
The Foundational Principles of Network Segregation
Network segregation is built upon a series of core principles that dictate how networks are divided and how traffic is managed between these divisions. At its heart, it’s about implementing a layered security approach and controlling access based on defined policies.
Isolating Critical Assets
One of the primary drivers for network segregation is the need to protect sensitive or critical assets. This could include financial data, intellectual property, customer personal information, or control systems for industrial processes. By placing these assets on a separate, highly restricted network segment, administrators can implement stringent access controls and monitoring. This makes it significantly harder for unauthorized users or malicious actors to gain access, even if they manage to compromise less sensitive parts of the network. The isolation ensures that even if a breach occurs in a more vulnerable segment, the critical assets remain protected behind additional layers of security.
Minimizing the Attack Surface
A single, flat network presents a much larger target for attackers. If a vulnerability is exploited on one device, it can potentially lead to widespread compromise as attackers can move freely between systems. Network segregation effectively reduces this “attack surface” by breaking down the network into smaller, more manageable zones. Each zone can have its own security policies, firewalls, and intrusion detection systems. This means that even if an attacker gains a foothold in one segment, their ability to move laterally to other segments is severely hindered, as they would need to bypass multiple security controls. This principle is akin to a ship with multiple watertight compartments; if one compartment floods, the others can remain sealed, preventing the entire vessel from sinking.
Enhancing Performance and Reliability
Beyond security, network segregation plays a crucial role in optimizing network performance and reliability. By segmenting traffic based on its type, origin, or destination, administrators can implement Quality of Service (QoS) policies. This allows them to prioritize critical applications and services, ensuring they receive the necessary bandwidth and low latency, even during peak usage times. For example, voice and video traffic, which are sensitive to delays, can be placed on a separate segment with higher priority, ensuring clear communication. Similarly, segregating high-bandwidth activities like large file transfers or backups can prevent them from impacting real-time applications. This also contributes to reliability, as a problem or overload in one segment is less likely to cascade and affect the entire network.
Facilitating Compliance and Auditing
Many regulatory frameworks and industry standards, such as PCI DSS (Payment Card Industry Data Security Standard) or HIPAA (Health Insurance Portability and Accountability Act), mandate specific security controls for handling sensitive data. Network segregation is a key enabler for achieving compliance with these regulations. By isolating systems that process or store regulated data, organizations can apply targeted security measures and simplify the auditing process. It becomes easier to demonstrate that only authorized personnel and systems have access to sensitive information and that appropriate controls are in place. This focused approach makes it more efficient to prove adherence to compliance requirements.
Methods of Implementing Network Segregation
The implementation of network segregation can be achieved through various technological and architectural approaches, each with its own strengths and use cases. The choice of method often depends on the scale of the network, budget, existing infrastructure, and the specific security objectives.
Virtual Local Area Networks (VLANs)
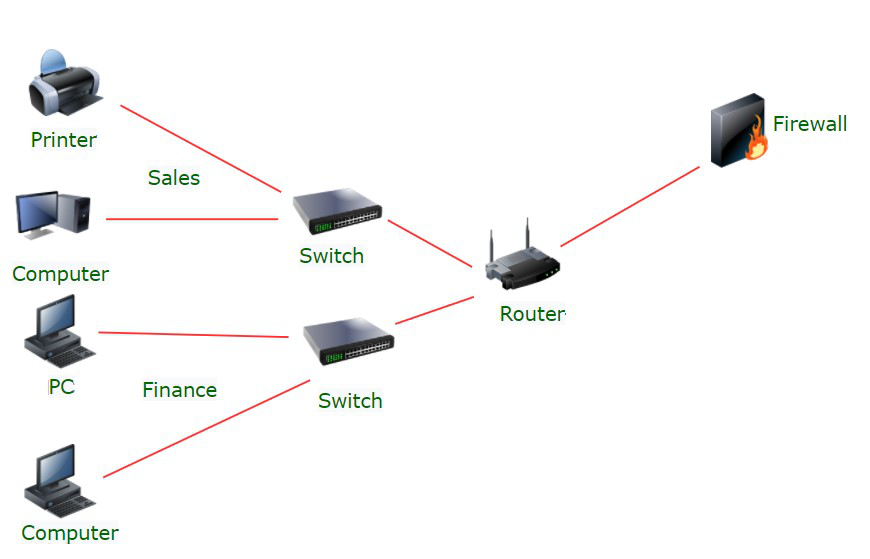
Virtual Local Area Networks (VLANs) are a widely adopted and cost-effective method for segmenting a network at the data link layer (Layer 2) of the OSI model. VLANs allow administrators to logically group devices together, regardless of their physical location. Devices within the same VLAN can communicate with each other as if they were on the same physical network segment, but traffic between different VLANs must pass through a Layer 3 device, typically a router or a Layer 3 switch, which can then enforce access control policies. This provides a fundamental level of isolation and allows for the creation of multiple broadcast domains within a single physical network. For example, an organization might create separate VLANs for departments like finance, HR, and IT, or for different types of devices such as servers, workstations, and VoIP phones.
Benefits of VLANs:
- Cost-Effective: VLANs leverage existing switch infrastructure, reducing the need for extensive rewiring or additional hardware.
- Flexibility: Network administrators can easily reconfigure VLAN membership to accommodate changes in user roles or device placement without physical network modifications.
- Reduced Broadcast Traffic: By creating smaller broadcast domains, VLANs limit the amount of unnecessary traffic that is sent to all devices on a segment, improving overall network efficiency.
- Basic Security: While not a complete security solution on its own, VLANs provide an initial layer of separation, preventing direct communication between devices in different VLANs without routing.
Subnetting and IP Addressing
Subnetting is the process of dividing a larger IP network into smaller subnetworks, known as subnets. This is performed at the network layer (Layer 3) of the OSI model. Each subnet is assigned its own unique network address and subnet mask. Devices within the same subnet can communicate directly, but communication between different subnets requires a router. Routers are essential for enforcing security policies between subnets, as they can implement Access Control Lists (ACLs) to permit or deny traffic based on source IP addresses, destination IP addresses, protocols, and ports. Subnetting is a fundamental networking practice that naturally supports network segregation and is often used in conjunction with other methods.
Key Aspects of Subnetting for Segregation:
- Hierarchical Structure: Subnetting creates a hierarchical addressing scheme, making network management and routing more efficient.
- Granular Control: By assigning different subnets to different functions or security zones, administrators gain granular control over traffic flow and access.
- Router-Based Enforcement: Routers act as the gateways between subnets, providing a centralized point for implementing security policies and traffic filtering.
- Scalability: Subnetting allows networks to scale effectively by breaking them down into manageable segments.
Firewalls and Access Control Lists (ACLs)
Firewalls are dedicated network security devices or software that monitor and control incoming and outgoing network traffic based on predetermined security rules. They act as a barrier between trusted and untrusted networks, or between different segments of a trusted network. Firewalls can inspect traffic at various layers of the OSI model and make decisions about whether to allow, deny, or log network packets. Access Control Lists (ACLs) are a core component of firewall functionality. ACLs are sets of rules configured on routers and firewalls that specify which types of traffic are permitted or denied between network interfaces or segments.
Firewall and ACL Functionality:
- Traffic Filtering: Firewalls and ACLs enable administrators to define precise rules about what traffic can pass between network segments, effectively enforcing the segregation.
- Stateful Inspection: More advanced firewalls can perform stateful inspection, tracking the state of active network connections and making decisions based on the context of the traffic.
- Network Address Translation (NAT): Firewalls often employ NAT to mask internal IP addresses, providing an additional layer of security by hiding the internal network structure.
- Intrusion Prevention/Detection: Many modern firewalls incorporate Intrusion Prevention Systems (IPS) and Intrusion Detection Systems (IDS) to actively monitor for and block malicious activity.
Micro-segmentation
Micro-segmentation represents a more advanced and granular approach to network segregation. Instead of segmenting the network into broad zones, micro-segmentation aims to isolate individual workloads or applications. This means that even within a single subnet or VLAN, specific applications or services can have their own security policies and be isolated from each other. This is often achieved through software-defined networking (SDN) technologies, host-based firewalls, or network virtualization. The goal is to create a highly dynamic and secure environment where the principle of least privilege is strictly enforced at the application level.
Characteristics of Micro-segmentation:
- Workload-Centric Security: Policies are applied directly to individual workloads (e.g., virtual machines, containers, or even individual processes), providing a highly granular security posture.
- Dynamic and Agile: Micro-segmentation can adapt to changes in application deployment and infrastructure, making it ideal for cloud-native and DevOps environments.
- Zero Trust Architecture: It aligns perfectly with Zero Trust security models, where trust is never implicitly granted and verification is always required.
- Application Isolation: Prevents lateral movement of threats between applications, even if they reside on the same server or in the same subnet.
Advanced Concepts and Applications of Network Segregation
As networks become more complex and the threat landscape evolves, network segregation continues to evolve, incorporating advanced concepts and finding applications in specialized domains. These advancements go beyond basic segmentation, offering more sophisticated control and enhanced security.
Software-Defined Networking (SDN) and Network Virtualization
Software-Defined Networking (SDN) and network virtualization have revolutionized the way networks are designed and managed, offering powerful new tools for implementing network segregation. SDN decouples the network control plane from the data plane, allowing for centralized management and programmatic control of network resources. Network virtualization creates virtual networks that run on top of physical infrastructure, enabling the creation of highly customized and isolated network environments. Together, these technologies allow for the dynamic creation and modification of network segments and security policies.
Impact of SDN and Virtualization:
- Programmatic Control: Network segmentation policies can be defined and enforced through software, enabling automation and rapid deployment.
- Agility and Flexibility: Virtual networks can be spun up and torn down on demand, allowing for quick adaptation to changing business needs and security requirements.
- Micro-segmentation Enablement: SDN and network virtualization are key enablers of micro-segmentation, allowing for fine-grained control over traffic flow between individual virtual machines or containers.
- Centralized Policy Management: Security policies can be managed from a central console, simplifying administration and ensuring consistency across the network.
Segmentation for IoT and Operational Technology (OT) Environments
The proliferation of Internet of Things (IoT) devices and the increasing connectivity of Operational Technology (OT) systems in industrial settings present unique challenges for network security. These devices often have limited processing power, may not support traditional security agents, and can introduce significant vulnerabilities if not properly managed. Network segregation is a critical strategy for securing these environments. By isolating IoT and OT devices onto dedicated network segments, organizations can limit their exposure to the broader corporate network and the internet, reducing the risk of compromise.
Specifics for IoT/OT:
- Containment of Vulnerabilities: If an IoT device is compromised, the segregation prevents the threat from spreading to critical IT systems.
- Traffic Monitoring: Dedicated segments allow for specialized monitoring of IoT/OT traffic, enabling the detection of unusual or malicious activity.
- Protocol-Specific Security: Some OT protocols may require specific security measures that can be more easily implemented and managed within a segregated environment.
- Safety and Reliability: In industrial settings, network segregation can contribute to the safety and reliability of critical processes by preventing interference or disruption.
The Role of Network Segregation in Cloud Computing
In cloud computing environments, network segregation takes on a new dimension, with virtual private clouds (VPCs), security groups, and network access control lists (NACLs) playing crucial roles. Cloud providers offer robust tools for logically isolating resources within their infrastructure, allowing organizations to create secure and segmented environments for their applications and data. This enables businesses to leverage the scalability and flexibility of the cloud while maintaining a strong security posture.

Cloud-Specific Segregation Strategies:
- VPCs: Provide a logically isolated private network within a public cloud, offering complete control over the network environment.
- Security Groups: Act as virtual firewalls for cloud instances, controlling inbound and outbound traffic at the instance level.
- NACLs: Operate at the subnet level, providing an additional layer of stateless traffic filtering for VPCs.
- Hybrid Cloud Considerations: Segregating resources in hybrid cloud environments, where on-premises and cloud infrastructure are interconnected, is essential for maintaining consistent security.
In conclusion, network segregation is not a one-time setup but an ongoing process of defining, implementing, and refining boundaries within a network. As technology advances and threats become more sophisticated, the importance of robust network segregation strategies will only continue to grow. It remains a cornerstone of modern cybersecurity, ensuring the confidentiality, integrity, and availability of critical information and systems across a wide range of applications and environments.
