Network penetration testing, often abbreviated as pen testing or ethical hacking, is a simulated cyberattack against a computer system, network, or web application to identify security vulnerabilities that an attacker could exploit. In essence, it’s a proactive approach to cybersecurity, where authorized security professionals attempt to breach an organization’s defenses in a controlled environment to uncover weaknesses before malicious actors can. The primary goal is not to cause damage but to provide actionable insights that allow organizations to strengthen their security posture.
The digital landscape is constantly evolving, with new threats emerging daily. Organizations invest heavily in security measures, but without a robust testing methodology, they can remain unaware of exploitable flaws. Penetration testing acts as a critical stress test, revealing how well existing security controls perform under simulated adversarial conditions. It moves beyond theoretical security assessments to practical, hands-on validation of an organization’s defenses. This rigorous process is crucial for compliance with various industry regulations and standards, which often mandate regular security testing.
The Core Objectives of Penetration Testing
At its heart, network penetration testing aims to achieve several key objectives, all centered around enhancing an organization’s security resilience. Understanding these objectives is fundamental to appreciating the value and methodology of pen testing.
Identifying Vulnerabilities
The most immediate and evident objective of pen testing is the discovery of security flaws. These can range from simple misconfigurations and weak passwords to more complex software vulnerabilities like SQL injection or cross-site scripting (XSS) flaws. Testers use a variety of tools and techniques, mirroring those of real attackers, to probe for these weaknesses across different layers of the network.
Assessing Security Control Effectiveness
Beyond simply finding vulnerabilities, pen testing evaluates how well an organization’s existing security measures, such as firewalls, intrusion detection systems (IDS), antivirus software, and access control policies, are performing. It reveals whether these controls are adequately configured, up-to-date, and effective in preventing or detecting simulated attacks. A successful penetration test might demonstrate that a firewall rule is too permissive or that an IDS is not flagging known malicious traffic patterns.
Quantifying Risk and Impact
Penetration testing provides a tangible understanding of the potential damage an attacker could inflict. By successfully exploiting vulnerabilities, testers can demonstrate the real-world impact, such as data exfiltration, system downtime, or unauthorized access to sensitive information. This quantification helps organizations prioritize remediation efforts, allocating resources to address the most critical risks first.
Ensuring Compliance
Many industries are subject to strict regulatory requirements for data protection and cybersecurity, such as GDPR, HIPAA, PCI DSS, and SOX. Penetration testing is often a mandatory component of these compliance frameworks, providing evidence that an organization is actively working to secure its systems and data. Successful pen tests can demonstrate due diligence and help avoid significant fines and penalties associated with non-compliance.
Improving Incident Response Capabilities
The process of a penetration test also serves to test an organization’s incident response (IR) capabilities. By simulating an attack, it can reveal how effectively the security team detects, analyzes, and responds to security incidents. This can highlight gaps in the IR plan, communication protocols, or the tools and training available to the response team.
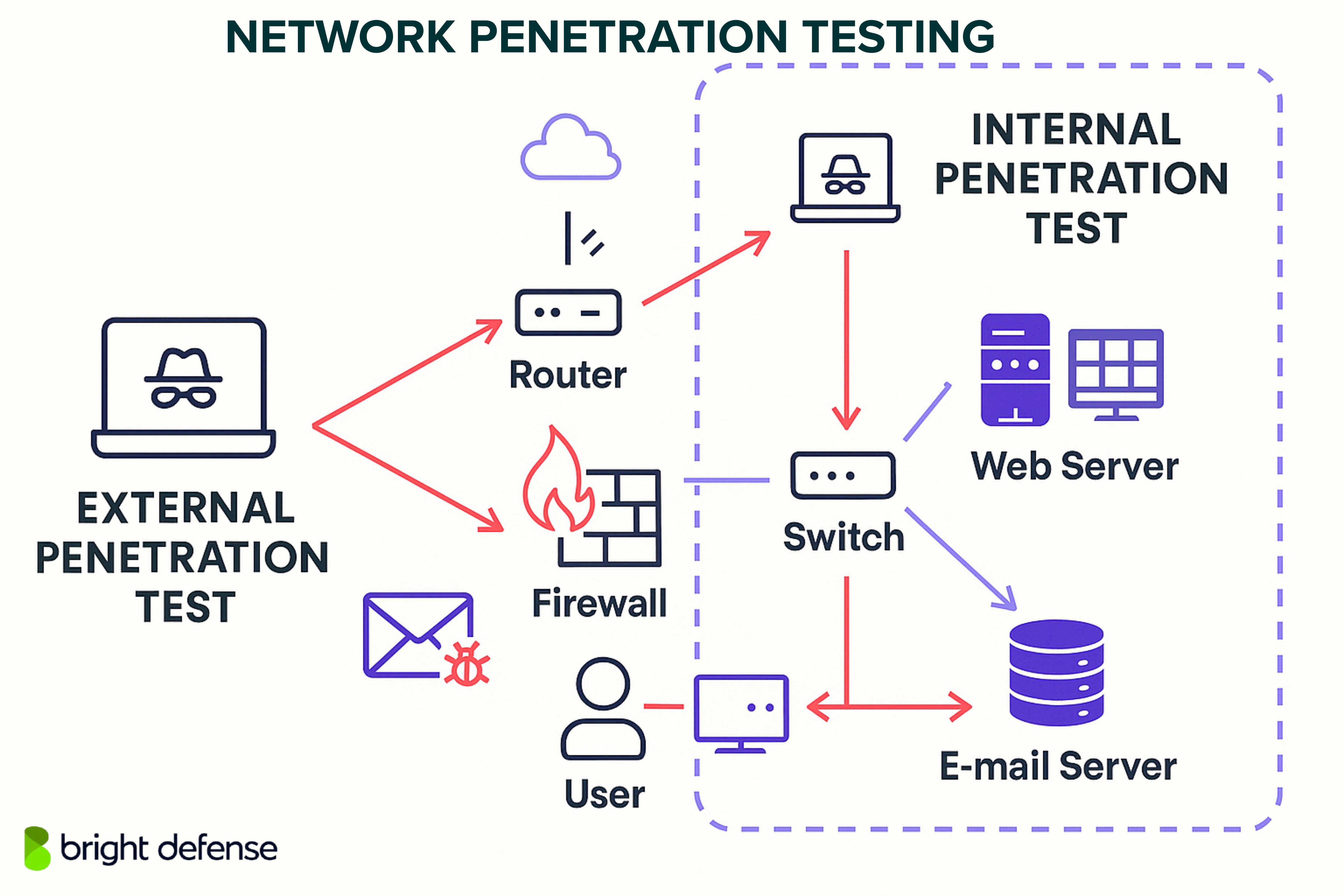
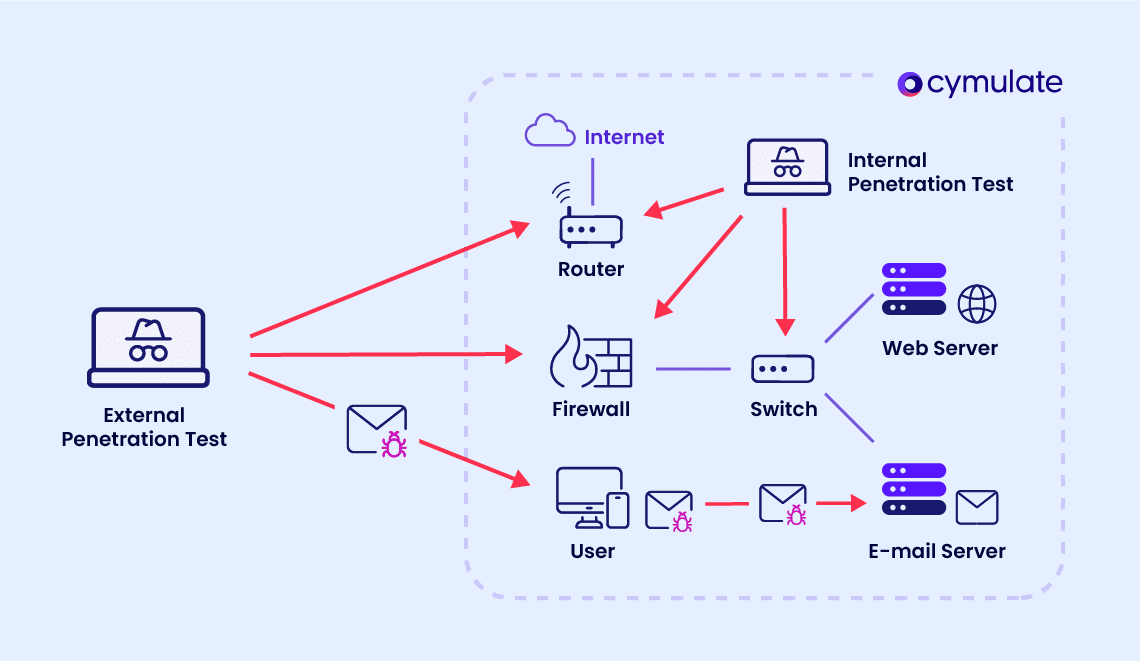
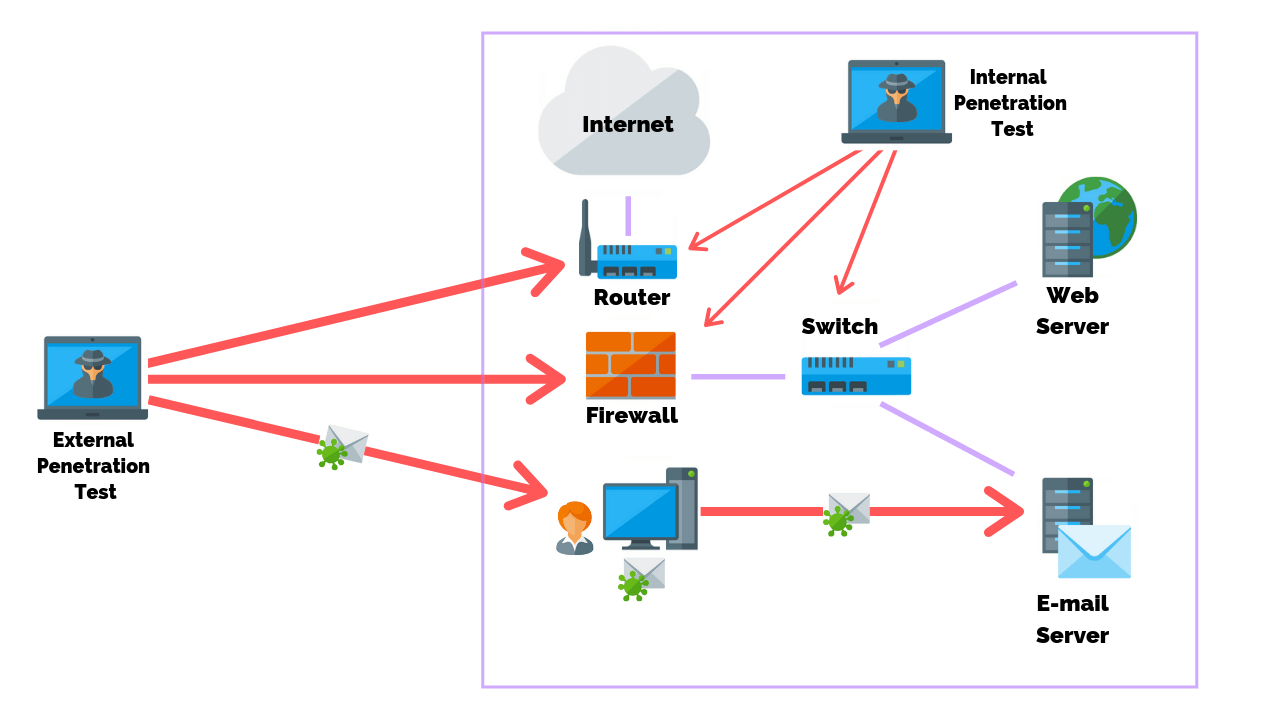
Types of Network Penetration Testing
Penetration testing methodologies can be broadly categorized based on the level of information provided to the testing team before the engagement begins. This distinction significantly influences the approach and scope of the test.
Black Box Testing
In a black box penetration test, the testers have virtually no prior knowledge of the target network’s internal structure, systems, or security measures. They are given only the target’s name or IP address, mimicking the scenario of an external attacker with no inside information. This approach is valuable for understanding how well an organization’s perimeter defenses hold up against unknown threats. The testers must first perform reconnaissance to gather information, discover potential entry points, and then attempt to exploit them.
White Box Testing
Conversely, white box testing, also known as clear box or glass box testing, provides the testers with complete knowledge of the target environment. This includes network diagrams, source code, IP addresses, server configurations, and security policies. This comprehensive understanding allows testers to conduct a more thorough and efficient assessment, delving deep into specific applications and systems to uncover complex or subtle vulnerabilities. White box testing is often used for internal audits or when a highly detailed analysis of specific systems is required.
Grey Box Testing
Grey box testing falls between black box and white box testing. The testers are given partial information about the target system, such as user credentials or a general understanding of the network architecture. This approach simulates an attacker who may have some insider knowledge or has already gained a limited foothold within the network. Grey box testing can be particularly effective for testing the security of applications from the perspective of a privileged user or an attacker who has already breached the perimeter.
The Penetration Testing Lifecycle
A well-executed penetration test follows a structured lifecycle, ensuring a methodical and comprehensive approach to identifying and reporting vulnerabilities. While specific methodologies may vary, the general phases remain consistent.
Planning and Reconnaissance
This initial phase involves defining the scope and objectives of the test, obtaining proper authorization, and gathering as much information as possible about the target. Reconnaissance can be passive (e.g., using public sources like WHOIS records, DNS lookups, and social media) or active (e.g., port scanning, network mapping, and banner grabbing). The aim is to build a comprehensive picture of the target’s attack surface.
Scanning and Vulnerability Analysis
Once reconnaissance is complete, testers use specialized tools to scan the target network for open ports, running services, and potential vulnerabilities. This phase often involves automated vulnerability scanners that can identify known weaknesses in software and configurations. However, manual analysis is crucial to interpret scanner results, identify false positives, and discover vulnerabilities that automated tools might miss.
Exploitation
This is the phase where testers actively attempt to exploit the identified vulnerabilities to gain unauthorized access to systems or data. This can involve using pre-built exploit code, crafting custom exploits, or employing social engineering techniques. The goal is to demonstrate the impact of a vulnerability by successfully breaching a system or accessing sensitive information.
Post-Exploitation and Lateral Movement
After gaining initial access, testers aim to determine what further actions can be taken. This might involve escalating privileges, moving laterally across the network to compromise other systems, or exfiltrating data. This phase helps organizations understand the potential reach of an attacker who has successfully breached their defenses.
Reporting
The final and arguably most critical phase is the creation of a detailed report. This report outlines all findings, including identified vulnerabilities, the methods used to exploit them, the impact of these exploits, and specific, actionable recommendations for remediation. A good report should be clear, concise, and tailored to both technical and managerial audiences.
Remediation and Re-testing
While not always part of the initial pen test engagement, the remediation and re-testing phases are crucial for organizational security. Organizations use the pen test report to fix identified vulnerabilities. After remediation efforts are completed, a re-test is often performed to verify that the vulnerabilities have been effectively addressed and that no new ones have been introduced during the fix process.
Methodologies and Tools
Penetration testers employ a wide array of methodologies and tools to conduct their assessments. These tools can range from open-source utilities to sophisticated commercial platforms, and their effective use requires significant expertise.
Common Methodologies
Various methodologies guide penetration testing. The Open Source Security Testing Methodology Manual (OSSTMM) provides a framework for testing information security. The National Institute of Standards and Technology (NIST) Special Publication 800-115, “Technical Guide to Information Security Testing and Assessment,” is another widely adopted standard. OWASP (Open Web Application Security Project) provides extensive guidance specifically for web application security testing.
Essential Tools
A penetration tester’s toolkit is diverse. Network scanners like Nmap are fundamental for discovering hosts and services on a network. Vulnerability scanners such as Nessus and OpenVAS automate the identification of known weaknesses. For web application testing, Burp Suite and OWASP ZAP are indispensable for intercepting and manipulating traffic, identifying injection flaws, and more. Metasploit Framework is a powerful platform for developing and executing exploits. Password cracking tools like John the Ripper and Hashcat are used to test password strength. For wireless network testing, tools like Aircrack-ng are commonly used.
The Importance of Ethical Hacking
Network penetration testing is a cornerstone of a robust cybersecurity strategy. It provides a realistic, proactive assessment of an organization’s security posture, moving beyond theoretical defenses to practical validation. By embracing ethical hacking, organizations can uncover hidden weaknesses, strengthen their defenses, ensure compliance, and ultimately protect their valuable assets and reputation in an increasingly complex threat landscape. It’s not just a technical exercise; it’s a strategic investment in resilience and trustworthiness.
