In today’s digitally interconnected world, the seamless and reliable operation of networks is paramount. From global telecommunications giants to small businesses reliant on their internal IT infrastructure, the ability for data to flow unimpeded is the lifeblood of operations. This is where network monitoring steps in, acting as the vigilant guardian of our digital highways. At its core, network monitoring is the process of continuously observing, analyzing, and managing the performance, availability, and security of a computer network. It’s not just about identifying when something breaks; it’s about proactively understanding the health of the network, predicting potential issues, and ensuring optimal performance for all users and applications. Without robust network monitoring, organizations are essentially flying blind, susceptible to outages, performance degradation, and security breaches that can have catastrophic consequences.

The Pillars of Network Health: Understanding Key Performance Indicators
Network monitoring is not a monolithic concept; it is built upon the meticulous tracking and analysis of a wide array of metrics that collectively paint a picture of the network’s overall health. These metrics, often referred to as Key Performance Indicators (KPIs), provide actionable insights into various aspects of network operation. Understanding these pillars is fundamental to grasping the depth and breadth of network monitoring.
Availability: Is the Network Online and Accessible?
Perhaps the most fundamental aspect of network monitoring is ensuring that network resources are available when needed. This involves tracking the uptime of critical devices and services.
Device Uptime and Downtime
This is the straightforward measurement of how long a device, such as a router, switch, server, or firewall, has been operational and accessible. Conversely, downtime refers to periods when a device is unavailable. Network monitoring tools continuously poll devices to check their status, often using protocols like ICMP (Internet Control Message Protocol) to send “pings” and expecting a response. A failure to receive a response indicates a potential outage.
Service Availability
Beyond just devices, it’s crucial to monitor the availability of the services they provide. This includes applications, databases, web servers, and critical network services like DNS (Domain Name System) and DHCP (Dynamic Host Configuration Protocol). For example, a web server might be running, but if the web service itself is not responding to requests, users cannot access the website. Monitoring tools can simulate user requests to specific services to verify their functional availability.
Performance: How Well is the Network Operating?
While availability ensures that the network is up, performance monitoring focuses on how efficiently and effectively it is operating. This involves measuring the speed, responsiveness, and capacity of the network.
Bandwidth Utilization
Bandwidth refers to the maximum data transfer rate of a network connection. Bandwidth utilization measures how much of that capacity is currently being used. High utilization can indicate congestion, which leads to slower speeds and poor application performance. Monitoring bandwidth allows administrators to identify bottlenecks, forecast future capacity needs, and optimize data flow.
Latency and Jitter
Latency, often referred to as “ping time,” is the delay it takes for a data packet to travel from its source to its destination. High latency can significantly impact the user experience, especially for real-time applications like video conferencing or online gaming. Jitter, on the other hand, is the variation in latency over time. High jitter can cause choppy audio and video, making communication difficult. Monitoring these metrics is crucial for ensuring a smooth and responsive user experience.
Packet Loss
Packet loss occurs when data packets fail to reach their destination. This can happen due to network congestion, faulty hardware, or transmission errors. Even small amounts of packet loss can degrade the quality of data transmission, leading to retransmissions and slower speeds. Network monitoring tools track packet loss rates to identify areas where data is being dropped.
Traffic Analysis: Understanding Data Flow
Beyond simply measuring performance, understanding the nature of the traffic flowing through the network is essential for effective management. This involves analyzing the types of data, their sources and destinations, and their impact on network resources.
Top Talkers and Listeners
This analysis identifies the devices or applications that are sending (talkers) or receiving (listeners) the most data. Understanding these patterns can help administrators pinpoint bandwidth hogs, identify potential security threats (e.g., a compromised device generating excessive traffic), or optimize resource allocation.
Protocol Analysis
Networks use various protocols to facilitate communication. Analyzing the types and volumes of different protocols (e.g., HTTP, FTP, DNS, SMB) can reveal insights into application usage, identify unusual protocol activity, and help diagnose network issues. For instance, a sudden surge in unusual protocol traffic might indicate a malware infection.
Application Performance Monitoring (APM)
APM goes a step further by specifically monitoring the performance of applications that run over the network. This involves tracking metrics like response times, error rates, and transaction times for individual applications. APM is crucial for ensuring that business-critical applications are functioning as expected and providing a good user experience.
Security: Protecting the Network from Threats
Network monitoring plays a vital role in safeguarding the network from a myriad of security threats, both internal and external.
Intrusion Detection and Prevention
Network monitoring tools can analyze network traffic for patterns indicative of malicious activity, such as unauthorized access attempts, malware propagation, or denial-of-service attacks. Intrusion Detection Systems (IDS) alert administrators to suspicious activity, while Intrusion Prevention Systems (IPS) can actively block such threats.
Anomaly Detection
This involves establishing a baseline of normal network behavior and then flagging any deviations from that baseline. Anomalies could include sudden spikes in traffic, unusual login attempts, or unexpected connections to external servers, all of which could signal a security incident.
Log Management and Analysis
Network devices and applications generate a vast amount of log data, which records events and activities. Centralized log management systems collect and analyze these logs, making it easier to identify security incidents, troubleshoot problems, and perform forensic investigations.

The Tools and Technologies of Network Monitoring
The practice of network monitoring relies on a sophisticated ecosystem of tools and technologies designed to collect, process, and present network data in an understandable and actionable format. These tools vary in complexity and scope, catering to different network sizes and requirements.
Protocols and Standards
The foundation of network monitoring lies in the protocols that enable devices to communicate and provide status information.
Simple Network Management Protocol (SNMP)
SNMP is a widely adopted protocol for monitoring and managing network devices. It allows administrators to query devices for information (e.g., CPU usage, memory status, interface traffic) and, in some cases, to remotely configure devices. SNMP agents on network devices collect and store management information, which can then be accessed by SNMP managers.
NetFlow/sFlow
These are flow-based network protocols used to collect IP traffic information as it enters or exits an interface. NetFlow (developed by Cisco) and sFlow (a vendor-neutral standard) provide detailed insights into who is communicating with whom, for how long, and how much data is being transferred. This is invaluable for traffic analysis, security, and capacity planning.
ICMP (Internet Control Message Protocol)
As mentioned earlier, ICMP is primarily used for diagnostic purposes. The “ping” command, a common tool for testing network connectivity, relies on ICMP echo requests and replies. Network monitoring tools use ICMP to determine the reachability and basic response time of network devices.
Software Solutions
A variety of software applications are available to centralize and analyze the data gathered by monitoring protocols.
Network Monitoring Systems (NMS)
NMS are comprehensive platforms that provide a single pane of glass for monitoring various aspects of the network. They often integrate multiple monitoring techniques, offer graphical dashboards, alerting mechanisms, and reporting capabilities. Examples include SolarWinds Network Performance Monitor, PRTG Network Monitor, and Zabbix.
Log Management and SIEM Solutions
Security Information and Event Management (SIEM) systems are designed to aggregate and analyze log data from various sources, including network devices, servers, and applications. They are crucial for detecting security threats, investigating incidents, and ensuring compliance. Examples include Splunk, LogRhythm, and IBM QRadar.
Application Performance Monitoring (APM) Tools
Dedicated APM tools focus on the end-to-end performance of applications. They trace transactions across different tiers of an application, identify performance bottlenecks, and provide insights into user experience. Examples include Dynatrace, New Relic, and AppDynamics.
Hardware Appliances
In some cases, dedicated hardware appliances are used for specialized network monitoring tasks, offering high performance and dedicated processing power for tasks like deep packet inspection or real-time traffic analysis.
The Benefits and Importance of Proactive Network Monitoring
The implementation of a robust network monitoring strategy yields a multitude of benefits that extend across operational efficiency, cost savings, and enhanced security. It transforms IT from a reactive cost center to a proactive enabler of business success.
Minimizing Downtime and Ensuring Business Continuity
The most immediate and tangible benefit of network monitoring is its ability to prevent or quickly resolve network outages. By detecting issues before they escalate into full-blown failures, organizations can significantly reduce downtime, ensuring that critical business operations remain uninterrupted. This directly translates to preventing lost revenue, maintaining customer satisfaction, and preserving brand reputation.
Optimizing Network Performance and User Experience
A well-monitored network operates at peak efficiency. By continuously tracking performance metrics, administrators can identify and address bottlenecks, ensuring that applications run smoothly and users have a positive experience. This leads to increased employee productivity, improved customer engagement, and a more responsive digital environment.
Enhancing Network Security Posture
Network monitoring is a cornerstone of any effective cybersecurity strategy. By providing visibility into network traffic and identifying suspicious activities, monitoring tools empower security teams to detect and respond to threats more rapidly. This proactive approach significantly reduces the risk of data breaches, malware infections, and other costly security incidents.
Informed Capacity Planning and Resource Management
Understanding network traffic patterns and resource utilization through monitoring provides the data necessary for accurate capacity planning. Organizations can forecast future needs, make informed decisions about hardware upgrades or bandwidth expansion, and optimize resource allocation to avoid overspending or underprovisioning.
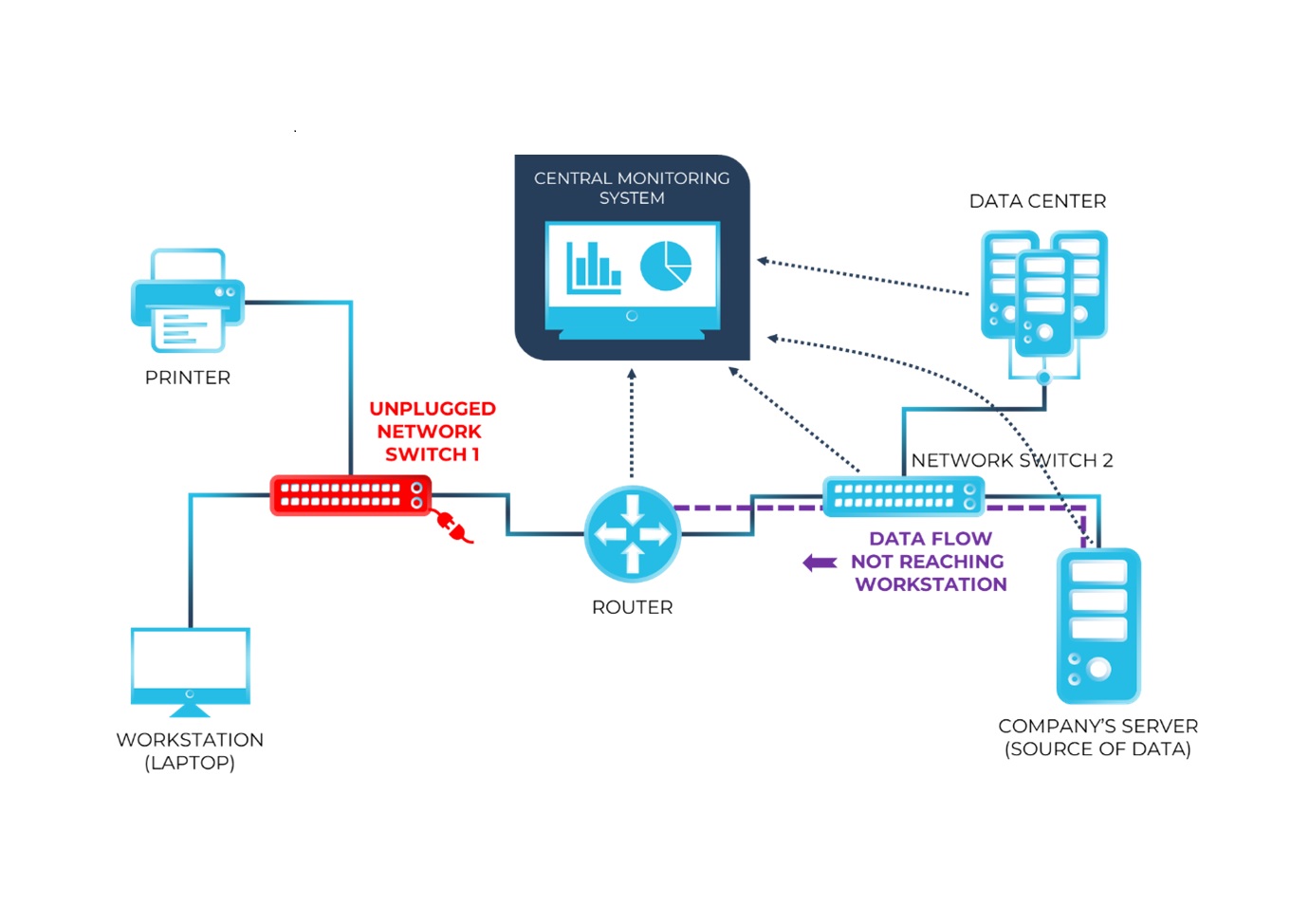
Facilitating Troubleshooting and Root Cause Analysis
When network issues do arise, network monitoring tools provide invaluable data for quick and efficient troubleshooting. Administrators can pinpoint the source of a problem, whether it’s a faulty device, a misconfigured setting, or a performance bottleneck, significantly reducing the time and effort required for resolution. This leads to faster recovery times and minimizes disruption.
Driving Cost Efficiency
By preventing downtime, optimizing resource utilization, and enabling proactive problem-solving, network monitoring ultimately contributes to significant cost savings. Reduced downtime means fewer lost revenue opportunities. Optimized resources mean more efficient spending. Proactive problem-solving avoids costly emergency fixes and extensive downtime.
In conclusion, network monitoring is an indispensable discipline for any organization that relies on digital infrastructure. It is the practice of seeing, understanding, and managing the complex web of connections that power our modern world. By embracing comprehensive network monitoring, businesses can build resilient, performant, and secure networks that serve as a strong foundation for innovation and success.
