In an era increasingly shaped by technological advancements, the concept of “security” itself has evolved, moving far beyond traditional notions of physical barriers and human guards. Nowhere is this transformation more evident than within the burgeoning field of drone technology and innovation. When we ask “what is meant by security” in this context, we are delving into a multi-faceted domain that encompasses the protection of the drones themselves, the data they collect, the systems that control them, and critically, how these intelligent, autonomous flying machines are leveraged to enhance security across various sectors.
At its core, security in drone tech and innovation involves ensuring the integrity, confidentiality, and availability of drone systems and the information they process, while simultaneously exploring their unparalleled potential to fortify physical and cyber defenses. This exploration extends from safeguarding the intricate AI algorithms that govern autonomous flight to protecting the vast datasets generated by sophisticated mapping and remote sensing operations. It’s a dynamic interplay between offensive capabilities (e.g., using drones for surveillance) and defensive measures (e.g., protecting drones from hacking), all underpinned by continuous technological evolution.
The Evolving Landscape of Drone Security
The rapid development of drone technology, particularly in areas like artificial intelligence, machine learning, and advanced sensor integration, has profoundly reshaped the security landscape. Drones are no longer mere remote-controlled toys; they are sophisticated flying robots capable of complex tasks, data acquisition, and autonomous decision-making. This leap in capability inherently broadens the scope of what “security” means for them and for the systems they interact with.
Beyond Physical Protection: A Multi-Layered Approach
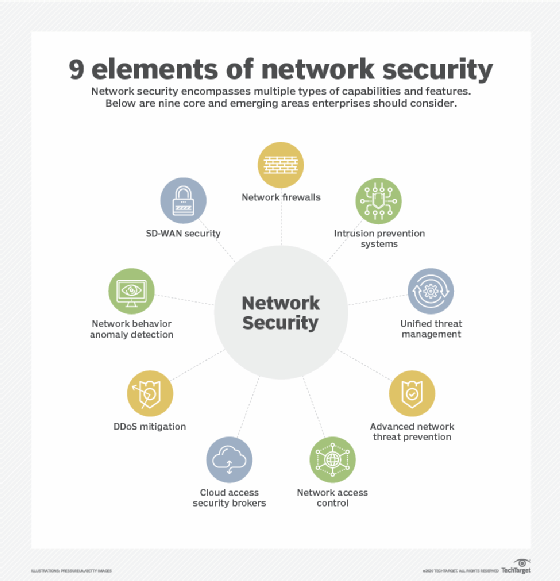
Traditional security often conjures images of robust physical defenses. For drones, however, security extends far beyond preventing a physical breach or theft. A truly secure drone ecosystem demands a multi-layered approach that addresses hardware, software, data, communication, and operational protocols. Physically securing the drone from damage or unauthorized access is a baseline, but the true vulnerabilities often lie in the digital realm.
Consider a drone utilizing AI Follow Mode for industrial inspection or autonomous flight for infrastructure mapping. The security concerns here pivot on protecting the AI algorithms from manipulation, ensuring the integrity of the captured mapping data, and securing the communication links that transmit control commands and telemetry. A compromised AI algorithm could lead to unpredictable drone behavior, while insecure data could expose critical infrastructure vulnerabilities or sensitive personal information. Therefore, security measures must span physical hardening, robust encryption for data and communications, secure coding practices for AI/ML models, and rigorous authentication protocols for operators and systems.
The Dual Nature of Drone Technology
One of the most compelling aspects of drone tech and innovation regarding security is its inherent duality. The very technologies that empower drones to perform invaluable security functions can also be exploited to create new threats. For instance, autonomous flight capabilities, which are revolutionary for long-range patrols or hazardous inspections, could, if compromised, be repurposed for illicit activities, surveillance, or even direct attacks. Similarly, high-resolution mapping and remote sensing, while vital for disaster response and critical infrastructure monitoring, could fall into the wrong hands and be used for reconnaissance by adversaries.
This dual nature necessitates a comprehensive understanding of potential misuse scenarios and the proactive development of counter-measures. Innovation in drone technology, therefore, isn’t just about building more capable drones; it’s equally about building more resilient, trustworthy, and ethically governed systems. The constant push-and-pull between developing new capabilities and safeguarding against their malicious application defines much of the security discourse in this domain.
Securing the Core: Protecting Advanced Drone Systems
The heart of modern drone innovation lies in its advanced systems – the AI that enables intelligence, the algorithms that dictate autonomy, and the sensors that gather vast amounts of data. Securing these core components is paramount to ensuring reliable, safe, and trustworthy drone operations.
Safeguarding Autonomous Flight and AI Algorithms
Autonomous flight, whether for search and rescue, delivery, or surveillance, relies on complex AI algorithms and robust navigation systems. Security here means protecting against a range of sophisticated attacks:
- Cybersecurity for AI/ML: Malicious actors could inject poisoned data into training sets, leading to biased or unsafe AI decisions (data poisoning). They could also craft adversarial examples to trick the AI into misidentifying objects or environments, bypassing obstacle avoidance or target recognition systems. Protecting these models requires secure development lifecycles, continuous monitoring, and robust anomaly detection.
- Anti-Spoofing and Anti-Jamming for Navigation: GPS and other GNSS systems are critical for autonomous navigation. However, they are susceptible to spoofing (transmitting false GPS signals to deceive the drone about its location) and jamming (overpowering GPS signals to deny navigation). Advanced drone security incorporates multi-sensor fusion (using visual, inertial, and other sensors alongside GPS), robust anti-jamming antennas, and cryptographic authentication of navigation signals to ensure the drone always knows its true position.
- Secure Software and Firmware: The underlying code that governs autonomous flight must be secure from vulnerabilities that could be exploited for unauthorized access or control. Regular security audits, penetration testing, and secure update mechanisms are crucial.
Data Integrity and Privacy in Mapping & Remote Sensing
Drones equipped with advanced remote sensing capabilities (LIDAR, hyperspectral, thermal cameras) generate immense volumes of data crucial for applications like precision agriculture, urban planning, and environmental monitoring. The security implications are vast:
- Securing Collected Data: From the moment data is captured, it must be protected against unauthorized access, alteration, or deletion. This involves strong encryption during transmission and storage, secure cloud infrastructure, and strict access controls. Data integrity is vital; corrupted or tampered mapping data could lead to erroneous decisions in critical applications, such as infrastructure development or emergency response.
- Ethical Considerations and Privacy: Mapping and remote sensing, especially in urban environments, raise significant privacy concerns. High-resolution imagery can capture identifiable individuals or sensitive property details. Security in this context means adhering to strict data privacy regulations (e.g., GDPR), implementing anonymization techniques where possible, and establishing clear policies for data retention and usage. Companies developing these innovations must build privacy by design into their systems.
Trust and Authentication in Drone Operations
As drones become more integrated into various systems, establishing trust between the drone, its operator, and control infrastructure becomes paramount.
- Secure Communication Protocols: The communication link between the drone and its ground control station (GCS) is a prime target for interception or manipulation. End-to-end encryption, frequency hopping, and secure handshaking protocols are essential to prevent unauthorized command injection or data exfiltration.
- Operator Verification and Access Control: Ensuring that only authorized and authenticated personnel can control a drone or access its data is fundamental. This involves robust authentication methods, role-based access control, and comprehensive logging of all operational activities. In multi-drone operations, secure fleet management systems are critical.
Drones as Enablers of Next-Generation Security
Beyond merely being secured, drone tech and innovation are fundamentally transforming how security is conceived and implemented across numerous sectors. AI, autonomous flight, mapping, and remote sensing are not just buzzwords; they are powerful tools revolutionizing security paradigms.
Autonomous Surveillance and Patrols
One of the most impactful applications of advanced drone technology in security is autonomous surveillance and patrolling.
- Perimeter Defense: Drones leveraging AI for object detection and classification can autonomously patrol large perimeters, critical infrastructure, or sensitive sites. They can identify intruders, suspicious vehicles, or abnormal activities with greater efficiency and consistency than human patrols, especially in hazardous or expansive environments. AI allows these drones to distinguish between genuine threats and benign occurrences, reducing false positives.
- Persistent Monitoring: Autonomous drones can provide persistent, overhead monitoring for extended periods, feeding real-time video and sensor data to security command centers. This is invaluable for event security, border control, and monitoring remote assets where continuous human presence is impractical or too costly. Their ability to operate without direct human intervention after mission planning signifies a significant leap in operational capability.
Advanced Remote Sensing for Critical Infrastructure Protection
Mapping and remote sensing capabilities allow drones to play a crucial role in protecting vital infrastructure, from energy grids to transportation networks.
- Anomaly Detection: Drones equipped with thermal, multispectral, or LIDAR sensors can perform detailed inspections of pipelines, power lines, bridges, and other infrastructure, identifying subtle anomalies, wear, or damage that might be invisible to the naked eye. AI-powered analytics can process this data to automatically flag potential issues before they escalate into major security risks or operational failures.
- Disaster Assessment: Following natural disasters or security incidents, drones can rapidly map affected areas, assess damage, and identify safe access routes for emergency responders. This situational awareness is critical for effective response and recovery operations, minimizing risks to human personnel.
Rapid Response and Situational Awareness
In emergency situations, whether for law enforcement, search and rescue, or fire services, the ability of drones to provide immediate aerial oversight is revolutionary.
- First Responder Support: Drones can be deployed quickly to provide a live, overhead view of active crime scenes, fires, or accident sites, offering critical situational awareness to first responders. Their ability to autonomously follow targets or conduct area sweeps significantly enhances operational effectiveness and safety.
- Search and Rescue: For missing persons in difficult terrain, thermal camera-equipped drones can cover vast areas much faster and more safely than ground teams, drastically increasing the chances of successful rescues. AI can assist in identifying potential targets in complex visual data, reducing search times.
Addressing Emerging Security Challenges and Future Horizons
As drone tech and innovation continue their upward trajectory, new security challenges will inevitably arise, demanding proactive and adaptive solutions. The future of security in this domain lies in anticipating these challenges and fostering responsible innovation.
Counter-Drone Technologies and Airspace Management
The proliferation of drones, both legitimate and illicit, has created new vulnerabilities in airspace security. Counter-drone technologies are a rapidly developing field focused on:
- Detection and Identification: Systems using radar, acoustic sensors, RF detection, and optical tracking to identify unauthorized drones. AI plays a crucial role in distinguishing drones from birds or other benign airborne objects.
- Mitigation: Techniques ranging from passive (e.g., jamming drone control signals) to kinetic (e.g., net guns, interceptor drones) to safely neutralize threatening drones.
- Airspace Integration: Developing Unmanned Traffic Management (UTM) systems that securely manage drone flights in shared airspace, preventing collisions and identifying rogue operators. This involves secure communication and authentication between drones and UTM systems.
Ethical AI and Responsible Autonomous Systems
The increasing autonomy of drones, powered by advanced AI, brings significant ethical considerations that are intrinsically linked to security.
- Preventing Bias: AI algorithms, if trained on biased data, can perpetuate or even amplify existing societal biases, with serious implications for surveillance and law enforcement applications. Security here means ensuring fairness, transparency, and accountability in AI development.
- Transparency and Explainability: For critical security applications, it’s crucial to understand how an AI system arrived at a particular decision (e.g., identifying a threat). Explainable AI (XAI) is vital for building trust and ensuring that autonomous systems operate within ethical and legal boundaries.
- “Kill Switch” and Human Oversight: Even with advanced autonomy, human oversight remains a critical security layer. Ensuring that humans can intervene or override autonomous systems in emergencies or unforeseen circumstances is a fundamental safety and security requirement.
The Human Element: Training and Policy in a Secure Drone Ecosystem
Ultimately, the most sophisticated drone security technologies are only as effective as the humans who design, operate, and regulate them.
- Operator Training: Comprehensive training for drone pilots and security personnel is essential, covering not just flight operations but also cybersecurity best practices, data handling, privacy protocols, and emergency procedures.
- Regulatory Frameworks: Governments and international bodies play a crucial role in establishing clear, enforceable regulations that govern drone operation, data collection, and security standards. These frameworks must evolve as rapidly as the technology itself to address new threats and ensure responsible innovation.
- Collaboration: A secure drone ecosystem requires collaboration between government agencies, private industry, academic researchers, and end-users to share threat intelligence, develop best practices, and collectively address emerging challenges.
In conclusion, “security” in the realm of drone tech and innovation is a continually expanding concept. It encompasses the rigorous protection of AI, autonomous flight, mapping, and remote sensing systems from diverse threats, while simultaneously leveraging these very innovations to create unparalleled new capabilities for surveillance, protection, and rapid response. As drones become more ubiquitous and sophisticated, the continuous pursuit of robust, ethical, and intelligent security solutions will define the next frontier of this transformative technology.
