In an increasingly digitized world where every online interaction, from shopping to social media, demands authentication, the concept of secure and convenient access has become paramount. The “Keychain iPhone” refers to Apple’s robust password management system, more formally known as iCloud Keychain. Far from being a mere list of stored credentials, iCloud Keychain represents a significant stride in personal digital security and user experience within the broader landscape of tech and innovation. It embodies Apple’s integrated approach to making complex security simple for the end-user, tackling one of the most persistent challenges of the internet age: password fatigue and the inherent risks of weak or reused passwords.

The Evolution of Digital Security and Convenience
The journey towards sophisticated password management tools like iCloud Keychain is rooted in the fundamental shift of our daily lives into the digital realm. Early internet usage often involved users juggling a handful of simple, easily memorized passwords. As the number of online services exploded, so did the necessity for more unique and complex passwords, leading to a critical dilemma.
From Memorized Passwords to Secure Digital Wallets
Historically, users adopted a range of insecure practices to cope with the proliferation of passwords. Writing them down on sticky notes, using simple sequential patterns, or worse, reusing the same weak password across multiple critical accounts, became common. This landscape presented a fertile ground for cybercriminals, with data breaches frequently exploiting these vulnerabilities. The innovation of a “digital wallet” for passwords, where credentials could be securely stored and automatically filled, was a necessary evolution. iCloud Keychain emerged as Apple’s comprehensive answer, providing a highly integrated and encrypted solution that prioritizes both stringent security and unparalleled convenience, thereby elevating the standard for personal digital security.
Addressing the Password Fatigue Crisis
The sheer volume of unique login credentials required for modern online life leads to what is colloquially known as “password fatigue.” This phenomenon drives users towards less secure practices, paradoxically increasing their risk. iCloud Keychain directly addresses this crisis by abstracting away the burden of memorization and manual entry. By intelligently generating strong, unique passwords for new accounts and securely storing existing ones, it mitigates the human tendency to opt for convenience over security. This technological intervention not only enhances individual user security but also contributes to a more secure digital ecosystem by reducing the prevalence of easily guessable or compromised credentials. It represents an innovative solution to a pervasive human-computer interaction challenge, allowing users to engage more securely with the digital world without becoming cybersecurity experts themselves.
iCloud Keychain: A Deep Dive into its Core Technologies
At its heart, iCloud Keychain is an intricate system built upon advanced cryptographic principles and seamless cloud integration, designed to operate transparently and securely across a user’s Apple devices. Its technological prowess lies in its ability to marry robust encryption with a fluid user experience.
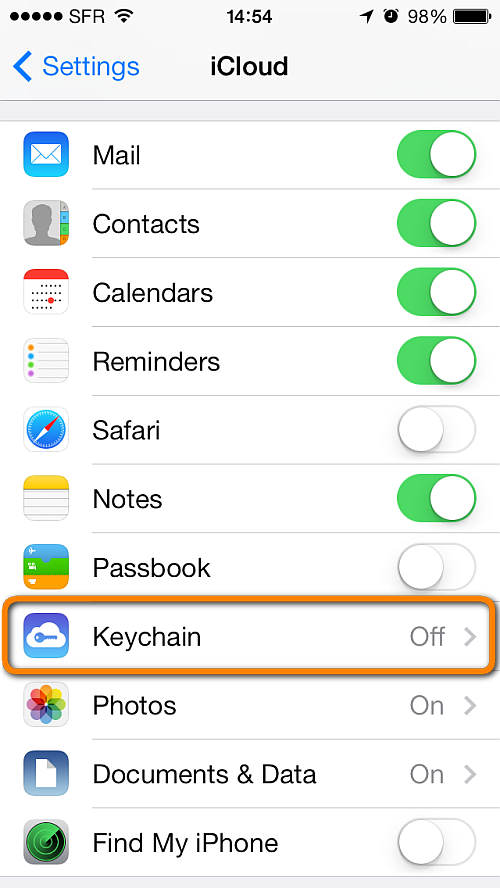
Secure Encryption and Device Synchronization
The foundational technology of iCloud Keychain is end-to-end encryption. When passwords, credit card information, Wi-Fi network details, or other secure notes are saved, they are immediately encrypted using powerful industry-standard algorithms. This encryption happens before data leaves the user’s device, ensuring that even Apple cannot access the plaintext content. The encryption key itself is derived from the user’s device passcode, meaning that without the physical device and its passcode, the data remains inaccessible. This secure environment is then extended through iCloud, where the encrypted data is synchronized across all of a user’s trusted Apple devices. This synchronization is also end-to-end encrypted, meaning data remains protected during transit and at rest on Apple’s servers. The innovation here is making this complex, multi-layered security architecture invisible to the user, who simply experiences their credentials appearing magically on their new iPhone or Mac.
Password Generation and AutoFill Capabilities
One of iCloud Keychain’s most impactful innovations is its integrated strong password generator. When signing up for a new online service, Safari, leveraging iCloud Keychain, automatically suggests a complex, unique password that meets most security requirements (e.g., length, mixture of characters). This significantly reduces the likelihood of users creating weak or predictable passwords. More importantly, once generated, this password is automatically saved to iCloud Keychain. For subsequent logins, the AutoFill feature intelligently recognizes login fields in apps and websites, presenting the correct credentials for a one-tap or Face ID/Touch ID authenticated login. This seamless integration of generation, storage, and retrieval minimizes friction for the user while enforcing strong security practices by default. This automatic suggestion and storage represent a proactive approach to cybersecurity, moving beyond merely managing existing passwords to actively fostering the creation of stronger ones.
Storing More Than Just Passwords
While primarily known for passwords, iCloud Keychain’s utility extends beyond simple login credentials. It also securely stores other sensitive information vital for daily digital interactions. This includes credit card details (card number, expiration date, name, but not the CVV/security code, which must be manually entered for security), Wi-Fi network passwords, and secure notes. This comprehensive approach transforms it into a centralized, encrypted repository for various pieces of critical personal data. This breadth of storage, all under the same robust encryption and synchronization protocols, further enhances convenience and security, eliminating the need for disparate secure storage solutions for different data types.
Seamless Integration Across Apple Ecosystem
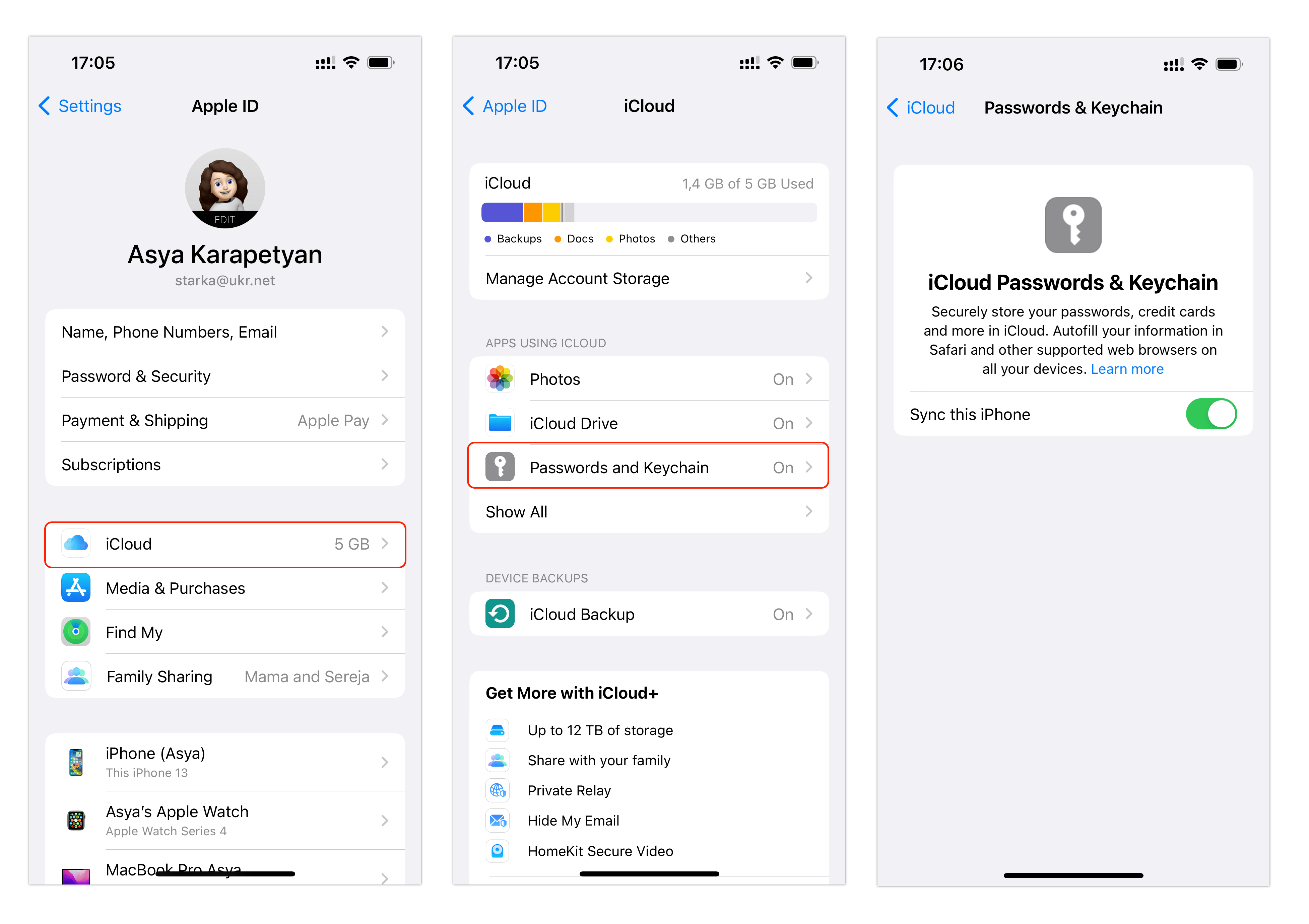
A key innovation driving iCloud Keychain’s effectiveness is its deep integration within the Apple ecosystem. It’s not a standalone app but a fundamental service woven into macOS, iOS, iPadOS, and watchOS. This means that access to stored credentials is not limited to Safari but extends to any app that supports Apple’s AutoFill APIs. This pervasive integration ensures a consistent and secure experience whether browsing on a Mac, shopping on an iPhone, or logging into a new app on an iPad. The ability for credentials to synchronize almost instantaneously across devices, secured by the user’s Apple ID and device passcodes, is a testament to Apple’s engineering prowess in creating a cohesive and user-friendly secure environment. This ecosystem-wide approach amplifies the convenience and security benefits, making it an indispensable tool for Apple users.
Innovations in User Experience and Data Protection
iCloud Keychain isn’t just about underlying security protocols; it’s also a masterclass in designing a user experience that promotes and simplifies strong security practices. Its innovations lie in how it intelligently interacts with the user, making robust protection an effortless default.
Multi-Factor Authentication Integration
While iCloud Keychain primarily manages passwords, its operation is deeply intertwined with Apple’s broader security infrastructure, including Multi-Factor Authentication (MFA). Accessing and managing iCloud Keychain itself often requires an Apple ID secured with two-factor authentication (2FA). This adds a critical layer of defense, ensuring that even if a user’s Apple ID password were compromised, an unauthorized party could not access their iCloud Keychain data without also having access to a trusted device to receive the second factor. Furthermore, for many online services, iCloud Keychain can store the login credentials, while the 2FA codes generated by separate authenticator apps (or SMS codes) provide the second factor. This intelligent division of labor ensures that while credentials are securely managed, the crucial second layer of authentication is still required where applicable, reinforcing a comprehensive security posture.
On-Device Intelligence and Recommendations
A notable innovative aspect of iCloud Keychain is its proactive intelligence. Beyond simply storing passwords, it actively scans and monitors stored credentials for potential weaknesses. For instance, it can alert users to passwords that are reused across multiple sites, passwords that are easily guessable, or credentials that have been compromised in known data breaches (by checking against public databases of breached passwords). This on-device analysis provides actionable security recommendations, prompting users to update vulnerable passwords with stronger, unique alternatives generated by the Keychain itself. This transforms the tool from a passive repository into an active security guardian, empowering users to maintain optimal digital hygiene without requiring deep cybersecurity knowledge. It’s a prime example of leveraging local processing and contextual awareness for enhanced security.
Privacy-Centric Design Principles
Apple’s design philosophy places a strong emphasis on privacy, and iCloud Keychain is no exception. Its end-to-end encryption ensures that user data is inaccessible to Apple, placing control solely in the user’s hands. The system is engineered to minimize the data footprint, only storing what is necessary for seamless login and payment experiences. Furthermore, the intelligent suggestions for password changes and security alerts are processed on the user’s device wherever possible, reducing the need to send sensitive data to cloud servers for analysis. This commitment to privacy-by-design principles differentiates iCloud Keychain, building trust and demonstrating how powerful technological solutions can be deployed without compromising individual data sovereignty.
The Broader Technological Impact on Personal Security and Identity Management
iCloud Keychain’s influence extends beyond individual convenience, subtly shaping the broader landscape of personal cybersecurity and identity management. Its innovations set a benchmark for what users expect from their devices in terms of security and usability.
Reducing Vulnerability to Phishing and Brute-Force Attacks
By enforcing unique, strong passwords and automating their entry, iCloud Keychain significantly diminishes the success rate of common cyber threats like phishing and brute-force attacks. Phishing relies on tricking users into revealing their credentials on fake websites; iCloud Keychain’s AutoFill, by only presenting credentials on legitimate, recognized domains, acts as a crucial defense mechanism against such schemes. Similarly, unique and complex passwords, automatically generated, make brute-force attacks (where attackers systematically try many passwords) impractical. This systemic elevation of security standards for millions of users has a ripple effect, making the digital environment safer for everyone by reducing the attack surface.
Empowering Users with Stronger Security Practices
Perhaps iCloud Keychain’s most profound technological impact is its ability to democratize strong security practices. It effectively makes advanced security accessible to the average user, abstracting away the complexities of cryptography and password hygiene. By making strong passwords the default, by actively identifying weaknesses, and by simplifying the entire authentication process, it empowers users to protect themselves effectively without needing specialized knowledge or diligence. This user empowerment is a critical innovation in the ongoing battle against cybercrime, shifting the paradigm from reactive defense to proactive, integrated protection.
Future Implications for Passwordless Authentication
iCloud Keychain also lays crucial groundwork for future innovations, particularly in the realm of passwordless authentication. Technologies like passkeys, which allow users to log in with Face ID or Touch ID instead of a password, build upon the same underlying principles of secure key generation and synchronization that power iCloud Keychain. As the industry moves towards a passwordless future, the secure infrastructure and user trust built around systems like iCloud Keychain will be instrumental in facilitating this transition. It represents a living example of how integrated technological solutions can evolve to meet emerging security challenges, continuously redefining the boundaries of what’s possible in personal digital security.
