Understanding Interactive Voice Response (IVR) and its Role in Drone Operations
The term “IVR PIN” might initially seem out of place in the context of drones and aerial technology. However, a deeper exploration reveals a surprisingly relevant connection, particularly within the burgeoning field of drone management, operational control, and data security. Interactive Voice Response (IVR) systems, commonplace in customer service and telecommunications, are increasingly finding applications in sophisticated technological domains, including drone fleet management, pilot authentication, and access control for sensitive drone operations. When we discuss “IVR PIN,” we are referring to the Personal Identification Number used within an IVR system specifically designed to interact with or manage aspects of drone technology.
This intersection of voice-based authentication and unmanned aerial vehicle (UAV) operations highlights the evolving landscape of drone technology, moving beyond the purely hardware-centric focus to encompass robust software, communication protocols, and secure human-machine interfaces. Understanding IVR PIN is crucial for anyone involved in the professional deployment, management, or security of drone fleets, especially in industries where stringent access controls and operational integrity are paramount.
The Mechanics of IVR and its Application to Drone Technology
Core Principles of Interactive Voice Response (IVR)
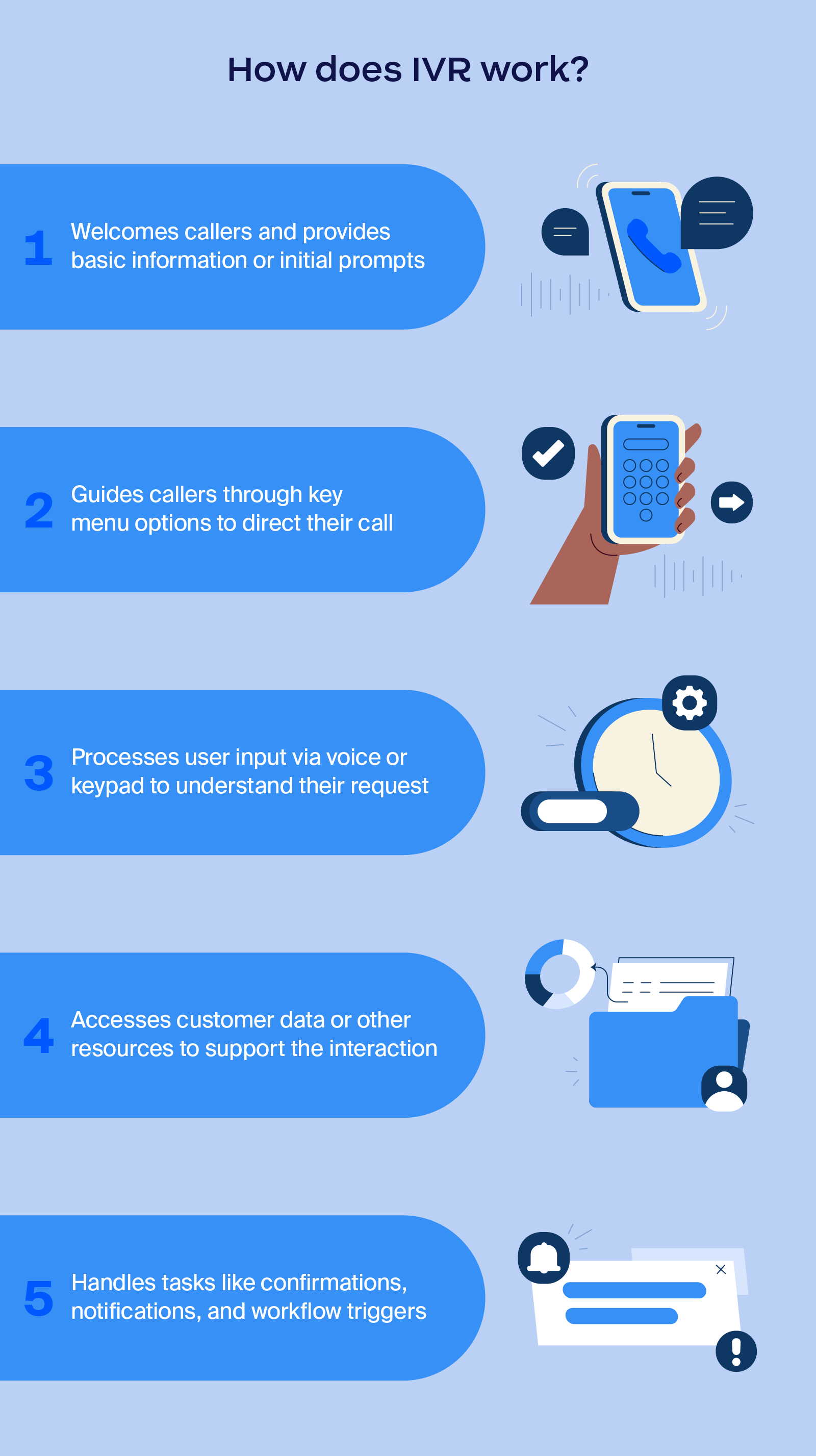
At its core, an IVR system is a technology that allows a computer to conduct a conversation with a human by using spoken language and Dual-tone multi-frequency (DTMF) (touch-tone) signals. When a user calls into an IVR system, they are presented with a series of spoken prompts. They can then respond using their voice or by pressing buttons on their phone keypad. The system analyzes these inputs and routes the call or performs a requested action.
Key components of an IVR system include:
- Telephony Gateway: Connects the IVR system to the public switched telephone network (PSTN) or Voice over IP (VoIP) networks.
- Application Server: Hosts the software that defines the IVR script, logic, and data processing.
- Speech Recognition Engine: Converts spoken words into text for the application server to process.
- Text-to-Speech (TTS) Engine: Converts text data into spoken prompts for the user.
- Database: Stores customer information, account details, and other relevant data.
Bridging IVR to Drone Operations
The application of IVR to drone operations might seem indirect, but it addresses critical needs in a sector that is rapidly professionalizing. Consider scenarios where drone pilots or maintenance personnel need to securely access systems, report flight status, or authorize specific operations. Instead of relying solely on physical keys, complex software logins, or potentially insecure digital authentication methods, an IVR system offers a hands-free, easily accessible, and secure alternative.
The “IVR PIN” is the specific numerical code a user enters into the IVR system to authenticate themselves. This PIN acts as a digital key, verifying the identity of the individual interacting with the drone management system. This is particularly valuable in environments where hands might be occupied with equipment, or when quick, verified access is needed remotely.
Security and Authentication: The Role of the IVR PIN
Enhanced Access Control for Drone Systems
In professional drone operations, security is not merely a feature; it’s a necessity. Whether managing a fleet of delivery drones, surveying drones, or surveillance UAVs, unauthorized access can have severe consequences, including data breaches, equipment theft, or even misuse for malicious purposes. The IVR PIN provides a robust layer of authentication for accessing critical drone systems and data.
For example, a pilot preparing for a flight might need to remotely arm a drone or access its flight plan. By calling a dedicated drone management hotline connected to an IVR system, they would be prompted to enter their unique IVR PIN. Upon successful authentication, the system could then grant them access to specific functionalities, such as:
- Flight Plan Authorization: Confirming and authorizing a pre-programmed flight path.
- System Arming/Disarming: Remotely initiating or deactivating drone systems.
- Status Reporting: Allowing pilots to verbally report mission status or any encountered issues.
- Data Retrieval: Providing secure, voice-verified access to collected drone data logs.
- Maintenance Logs: Enabling technicians to log and retrieve maintenance records.
Protecting Sensitive Data and Operations
Drone operations often involve the collection and transmission of sensitive data, including imagery, sensor readings, and flight telemetry. An IVR PIN helps ensure that only authorized personnel can access or manipulate this information. This is particularly important in regulated industries such as public safety, infrastructure inspection, and logistics.
The security of the IVR PIN itself is paramount. Like any PIN or password, it should be:

- Unique: Not shared with others.
- Complex: A combination of digits that is difficult to guess.
- Regularly Changed: To mitigate the risk of compromise.
- Securely Stored: The IVR system must employ encryption and secure storage mechanisms for PINs.
The system’s ability to integrate with existing enterprise security protocols, such as multi-factor authentication (MFA), further bolsters its security posture. For instance, after entering the IVR PIN, a user might receive a one-time code via SMS to their registered device for an additional layer of verification.
Practical Use Cases of IVR PIN in Drone Deployments
Fleet Management and Dispatch
For organizations managing large fleets of drones, efficient and secure dispatching is critical. An IVR system with PIN authentication can streamline this process. A dispatcher might use the system to:
- Assign Drones to Pilots: Verifying pilot identity via IVR PIN before assigning a specific drone for a mission.
- Monitor Fleet Status: Authorized personnel could call in to get real-time status updates on drone availability, battery levels, or current mission status, authenticated by their PIN.
- Emergency Notifications: The IVR system could be programmed to send automated alerts or receive critical updates from the field, with pilot authentication ensuring the legitimacy of the information.
Pilot and Operator Verification
In regulated airspace, pilot and operator credentials must be meticulously managed and verified. An IVR PIN offers a convenient yet secure method for pilots to confirm their identity before commencing operations. This can be integrated into pre-flight checklists or operational readiness checks.
- Remote Pre-Flight Checks: A pilot, en route to a launch site, can call in and authenticate using their IVR PIN to confirm their readiness and receive final go-ahead instructions.
- Post-Flight Debriefing: Pilots can use the IVR system to initiate a secure debriefing session, where their identity is confirmed via PIN before they provide verbal or touch-tone input on mission outcomes.
Maintenance and Technical Support
Maintaining a drone fleet requires strict protocols for access to maintenance bays, diagnostic tools, and service records. An IVR PIN can facilitate secure access for authorized technicians.
- Accessing Maintenance Schedules: Technicians can call in, authenticate with their PIN, and receive information on upcoming maintenance or pending service orders.
- Logging Maintenance Activities: Upon completion of a task, technicians can use the IVR system to verbally log their actions, ensuring an auditable trail of maintenance performed on specific drone units, linked to their verified identity.
- Remote Troubleshooting Support: During field repairs, a technician might use the IVR system to securely connect with remote technical support, with their PIN verifying their credentials before any sensitive system diagnostics are shared.
The Future of IVR in Advanced Drone Ecosystems
As drone technology continues to evolve, becoming more autonomous, integrated into complex networks, and critical to various industries, the need for robust, secure, and user-friendly management systems will only increase. IVR systems, powered by voice recognition and secure PIN authentication, are poised to play an even more significant role.
Integration with AI and Autonomous Systems
The future could see IVR systems interacting not just with human operators but also with AI-driven drone management platforms. An AI could use voice commands, authenticated by a PIN, to initiate complex autonomous flight sequences or request specific data analysis from drone-captured information.
- AI-Initiated Commands: A mission commander might verbally instruct an AI drone supervisor to deploy a specific drone for an emergency response, with their IVR PIN providing the necessary authorization.
- Secure Data Querying: An AI tasked with analyzing survey data might be programmed to only respond to data queries initiated by an authenticated user via an IVR interface, using their PIN to grant access.

Standardization and Interoperability
As the drone industry matures, there will likely be a push for standardization in how drone systems are accessed and managed. IVR systems, with their potential for secure authentication through PINs, could become a standardized interface for interacting with diverse drone platforms and management software, promoting interoperability across different manufacturers and service providers.
The concept of an “IVR PIN” may seem simple, but it represents a crucial element in the sophisticated ecosystem of drone technology. It is a gateway to secure access, efficient management, and the overall integrity of drone operations, underscoring the blend of traditional telecommunications security with cutting-edge aerial innovation.
