In the vast and ever-evolving landscape of technology, seamless operation and adaptability are paramount. Behind every sophisticated application, every customizable operating system, and countless pieces of hardware, lies a layer of fundamental configuration that dictates behavior and preferences. Among the earliest and most enduring methods for managing these settings is the INI file. Standing for “initialization,” INI files are simple text-based structures that have played a foundational role in defining how software applications and system components behave, particularly within the Microsoft Windows ecosystem, but also in numerous other contexts.
To the uninitiated, an INI file might seem like an arcane relic of computing’s past. However, understanding their structure, purpose, and enduring legacy provides valuable insight into the principles of software design, system configuration, and data persistence that remain relevant in modern tech. They represent a straightforward, human-readable approach to storing settings, one that prioritizes ease of understanding and direct modification. While newer, more complex data formats like XML, JSON, and YAML have emerged to handle more intricate data structures, the INI file continues to serve in niches where simplicity, directness, and readability are prized above all else. This article delves into the core aspects of INI files, exploring their anatomy, historical significance, practical applications, and their place within the broader spectrum of technological innovation.
The Anatomy of an INI File: Structure and Syntax
At its heart, an INI file is a plain text file, easily readable and editable by both humans and machines. Its simple, structured format is what has contributed to its longevity and widespread adoption for configuration purposes. The design philosophy emphasizes clarity and directness, making it straightforward to define, retrieve, and modify settings.
Sections and Keys: Organizing Configuration Data
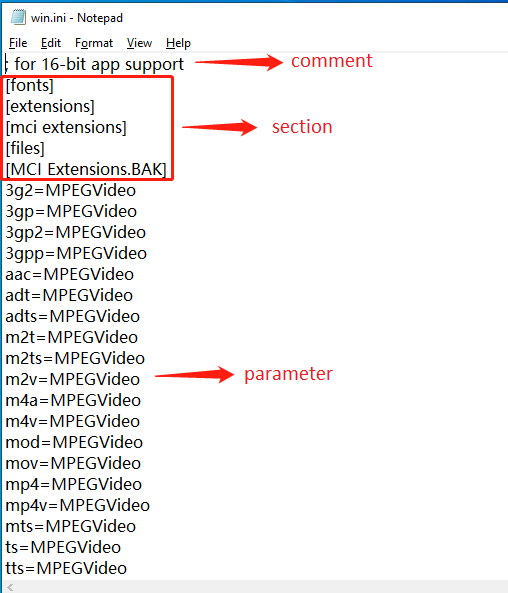
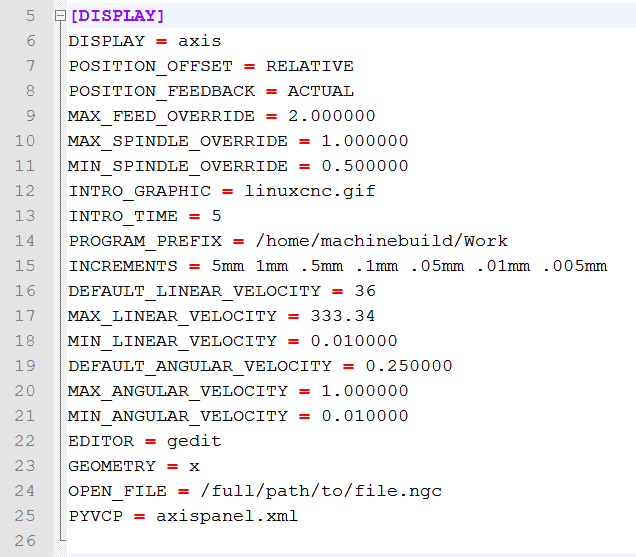
The primary organizational unit within an INI file is the section. Sections are used to group related configuration settings together, improving readability and preventing naming collisions for common settings. A section is declared by enclosing its name in square brackets, like so:
[NetworkSettings]
Underneath each section, specific configuration parameters are defined using key-value pairs. A key is a unique identifier for a particular setting, and its associated value is the data assigned to that setting. The key and value are separated by an equals sign (=):
[NetworkSettings]
IPAddress=192.168.1.100
SubnetMask=255.255.255.0
Gateway=192.168.1.1
In this example, IPAddress, SubnetMask, and Gateway are keys, and their respective numerical sequences are the values. This structure allows applications to easily locate specific settings by first identifying the relevant section and then querying for the desired key within that section.
Values and Data Types: Storing Specific Settings
While INI files are text-based, the values associated with keys are typically interpreted by the reading application according to expected data types. For instance, a value like true or false might be interpreted as a boolean, a sequence of digits as an integer or float, and any other string as, well, a string. There’s no inherent type enforcement within the INI file itself; it’s up to the parsing software to cast or validate the data.
Common value types encountered in INI files include:
- Strings: Textual data, often enclosed in quotes (though not strictly necessary in all parsers, and sometimes handled by escaping special characters).
- Numbers: Integers or floating-point numbers.
- Booleans: Representing true/false states, often
1or0,OnorOff,TrueorFalse. - Paths: File system locations.
The simplicity means there’s no built-in support for complex data structures like arrays or nested objects. While some parsers might implement conventions (e.g., item1=value1,value2,value3 for a comma-separated list), these are not part of the fundamental INI standard.
Comments and Readability: Documenting Your Configurations
Good configuration files are not just functional; they are also understandable. INI files support comments, which are lines of text ignored by the parsing software but invaluable for human readers. Comments typically begin with a semicolon (;) or a hash symbol (#):
; This is a comment about the network settings.
# Another type of comment.
[NetworkSettings]
IPAddress=192.168.1.100 ; Static IP address
SubnetMask=255.255.255.0
Gateway=192.168.1.1
Comments are crucial for explaining the purpose of sections, keys, or specific values, especially in complex configurations or files that might be maintained by multiple individuals over time. They enhance the readability and maintainability of the configuration, aligning with the “Tech & Innovation” focus on creating robust and understandable systems.
Historical Context and Widespread Adoption
The story of INI files is deeply intertwined with the early days of personal computing and the evolution of operating systems. Their rise to prominence speaks volumes about the need for simple, user-editable configuration mechanisms in a rapidly developing technological landscape.
The Windows Legacy: A Standard Bearer for Applications
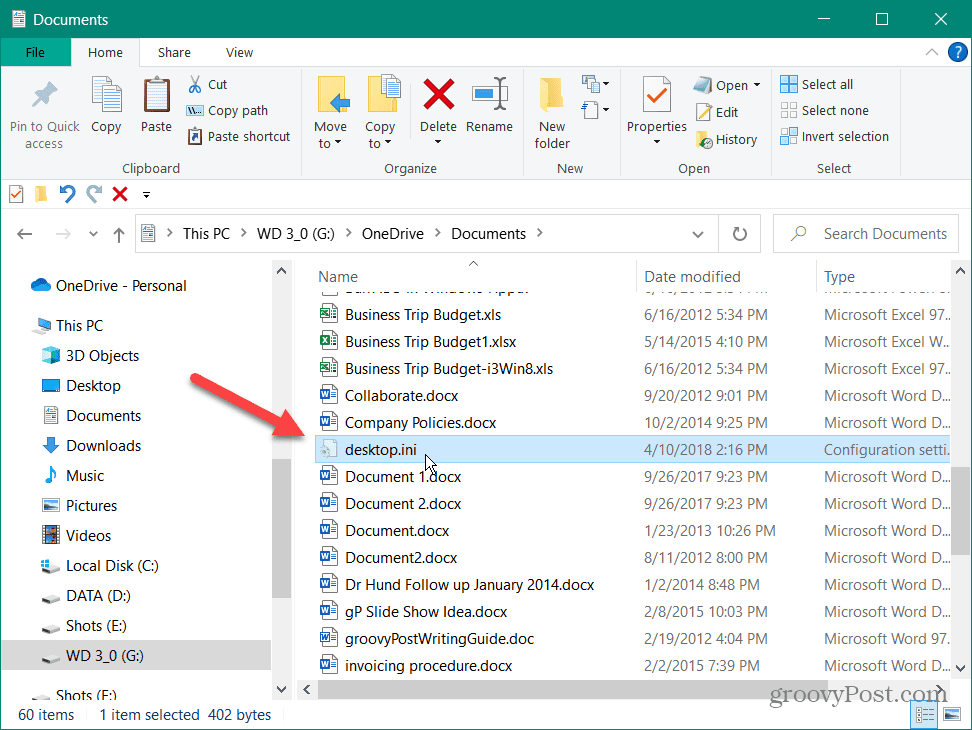
INI files gained significant traction with the advent of Microsoft Windows, particularly Windows 3.1 and earlier versions. Before the introduction of the Windows Registry in Windows 95, INI files were the primary method for applications to store their settings and preferences. Key system files like WIN.INI and SYSTEM.INI were central to how the operating system itself functioned, containing crucial configurations for peripherals, drivers, and user environments.
Every application often came with its own INI file, allowing users to customize various aspects, from interface themes to performance parameters. This decentralized approach meant that configuration was often transparent and directly accessible by users with a simple text editor, fostering a sense of control and customizability. While the Windows Registry eventually superseded INI files for most system-level and application settings due to its centralized, hierarchical structure and performance benefits, the INI format had already left an indelible mark.
Beyond Windows: Versatility in Cross-Platform Environments
Despite their strong association with Windows, the simplicity and portability of INI files ensured their use extended far beyond. They became a popular choice for configuration in various contexts:
- Unix/Linux Applications: While often using dot-files (e.g.,
.myconfig) or other plain text formats, many applications and utilities on Unix-like systems adopted INI-like structures for their configuration due to their ease of parsing and human readability. - Embedded Systems and IoT: For devices with limited resources, parsing complex XML or JSON can be resource-intensive. INI files offer a lightweight alternative for storing device-specific settings, network parameters, or sensor configurations.
- Gaming: Many older, and even some modern, video games utilize INI files for storing game settings, user profiles, key bindings, and graphical preferences, providing an easy way for users to tweak their experience.
- Proprietary Software and Utilities: Numerous niche applications, internal tools, and legacy systems continue to rely on INI files for their configuration, where the overhead of more complex formats is unwarranted.
Why They Persisted: Simplicity and Readability
The enduring appeal of INI files lies in their inherent simplicity and human readability. Anyone with basic text editing skills can open an INI file, understand its contents, and make modifications. This low barrier to entry for configuration management was a significant advantage, especially in an era when graphical user interfaces for advanced settings were less common or robust. The format is also incredibly easy to parse, making it straightforward for developers to write code that reads and writes INI files without relying on complex libraries. This efficiency and transparency ensured their long-term relevance, even as technology advanced.
Practical Applications and Use Cases in Modern Tech
While newer formats dominate for complex data, INI files continue to find purpose in various corners of modern technology, demonstrating their timeless utility where simplicity and direct configuration are priorities.
Customizing Software Behavior: From Games to Productivity Tools
Many applications still use INI files for user-specific settings or application-wide preferences. This allows users to fine-tune the software’s operation without needing to delve into complex internal menus or database entries.
- Gaming Configuration: As mentioned, many games allow players to adjust graphical settings, keybinds, and difficulty through an INI file, providing a direct route to customization not always exposed in-game.
- Tooling and Utilities: Small utility programs, command-line tools, or internal scripts often use INI files to store parameters like input/output paths, default values, or operational flags. This makes them highly configurable without requiring recompilation.
- Legacy System Integration: When working with older systems or applications, INI files often serve as the primary configuration mechanism, requiring developers to understand and interact with them to ensure compatibility and functionality.
Managing System Settings and Device Configurations
Beyond individual applications, INI files can be found managing aspects of system-level configurations, particularly in more constrained or specialized environments.
- Hardware Drivers: Some hardware drivers, particularly for less common or specialized peripherals, might use INI files to store initialization parameters or operational settings.
- Embedded System Configuration: Devices with limited memory or processing power often benefit from the lightweight nature of INI files for storing essential operational settings, network credentials, or sensor calibration data. This is crucial for rapid deployment and easy updates in the field.
- Automated Deployment Scripts: In environments where systems are deployed en masse, INI files can be used as templates to pre-configure various software components or system settings, streamlining the setup process.
Embedded Systems and IoT Devices: Lightweight Configuration
The Internet of Things (IoT) revolution has brought forth a new wave of devices that prioritize small footprints and efficient resource usage. Here, INI files offer a compelling advantage.
- Resource Efficiency: Parsing XML or JSON requires more memory and processing cycles. INI files, being extremely simple, are ideal for microcontrollers and single-board computers that need to load configurations quickly and efficiently.
- Offline Configuration: IoT devices often operate in environments without constant internet connectivity. INI files allow for local, persistent storage of settings that can be easily updated via a file transfer or direct connection, rather than relying on cloud-based configuration services.
- Ease of Maintenance: For technicians in the field, modifying a simple INI file on a device is often much faster and less error-prone than using specialized configuration tools or complex network interfaces.
Legacy Systems and Interoperability
In enterprise environments, maintaining and integrating legacy systems is a common challenge. Many critical applications developed decades ago still rely on INI files for their configuration. Understanding and being able to manipulate these files is essential for:
- System Maintenance: Keeping older applications running often involves tweaking their INI settings to adapt to new hardware, operating system updates, or evolving business requirements.
- Interoperability: When building new systems that need to interact with legacy applications, using INI files as an intermediate configuration format can sometimes simplify the communication layer.
- Migration Planning: When migrating from old to new platforms, understanding the configuration logic embedded in INI files is crucial for successfully transferring settings and ensuring continuity of operations.
Advantages and Limitations of INI Files
Like any technology, INI files offer a distinct set of pros and cons that dictate their suitability for various applications. Understanding these helps in making informed decisions about configuration strategy.
Pros: Simplicity, Human-Readability, Easy Parsing
- Extreme Simplicity: The fundamental structure of sections, keys, and values is exceptionally easy to grasp and implement. This reduces the learning curve for developers and makes direct user interaction feasible.
- Human-Readability: Being plain text, INI files can be opened and understood by anyone with a basic text editor. This transparency is a significant advantage for debugging, auditing, and manual configuration.
- Easy Parsing: The straightforward syntax makes writing parsers for INI files relatively simple, even without specialized libraries. This efficiency is beneficial for resource-constrained environments.
- Platform Independence: While historically tied to Windows, the format itself is text-based and inherently platform-agnostic, making it usable across different operating systems as long as a parser is available.
Cons: Limited Data Structures, Lack of Standardization, Security Concerns
- Limited Data Structures: This is the most significant limitation. INI files do not inherently support complex data types like nested objects, arrays (beyond simple comma-separated lists), or rich hierarchical structures. This restricts their use for applications requiring more sophisticated configurations.
- Lack of Strong Standardization: While there’s a widely accepted de-facto standard, there isn’t an official, rigorously defined specification for INI files that covers all edge cases (e.g., handling of spaces, duplicate keys, case sensitivity). This can lead to minor incompatibilities between different parsers.
- No Schema Validation: Unlike formats like XML (with XSD) or JSON (with JSON Schema), INI files lack an inherent mechanism for schema validation. This means errors in syntax or expected data types might only be caught at runtime by the application.
- Security Concerns: Storing sensitive information (like passwords or API keys) directly in plain-text INI files is a significant security risk. There’s no built-in encryption or access control, making them unsuitable for confidential data without external security measures.
- Scalability Issues: For very large or frequently changing configurations, the flat structure of INI files can become cumbersome to manage compared to more hierarchical or database-driven approaches.
The Rise of Alternatives: XML, JSON, YAML – When to Choose What
The limitations of INI files led to the development and widespread adoption of more powerful configuration and data serialization formats:
- XML (eXtensible Markup Language): Offers robust hierarchical structure, schema validation (XSD), and broad industry support. It’s often used for complex configurations and data exchange but can be verbose.
- JSON (JavaScript Object Notation): A lightweight, human-readable format for data interchange. It supports complex nested structures (arrays and objects) and is extremely popular for web applications and APIs.
- YAML (YAML Ain’t Markup Language): Designed to be even more human-readable than JSON, especially for configuration files. It supports complex data structures and is often used in DevOps, containerization, and configuration management tools.
The choice between these formats and INI files depends entirely on the specific requirements of a project. For simple, flat configurations where human readability and direct editing are paramount, INI files remain a valid and often preferred choice. For complex data, interoperability with web services, or stringent validation needs, the alternatives offer superior capabilities.
Best Practices for Working with INI Files
For developers and system administrators who continue to utilize INI files, adhering to best practices can mitigate their limitations and ensure reliable, maintainable configurations.
Version Control for Configuration Files
Treat INI files like source code. Store them in a version control system (like Git). This practice offers several critical benefits:
- History Tracking: Every change to the configuration is recorded, allowing you to see who made what change and when.
- Rollbacks: If a configuration change introduces a bug or undesirable behavior, you can easily revert to a previous working version.
- Collaboration: Multiple team members can work on configurations without overwriting each other’s changes, and conflicts can be resolved systematically.
- Deployment Consistency: Ensures that the correct version of configuration files is deployed alongside the application, preventing discrepancies between environments (development, staging, production).
Validating and Sanitizing Inputs
Since INI files lack built-in validation, it’s crucial for the application reading the INI file to perform robust validation on the values it retrieves.
- Type Checking: Convert string values from the INI file to the expected data type (e.g.,
int,boolean,float) and handle conversion errors gracefully. - Range Checking: Ensure numerical values fall within acceptable ranges.
- Format Validation: Validate string formats (e.g., email addresses, file paths).
- Default Values: Always provide default values for configuration settings in your application code, so that if a key is missing or invalid in the INI file, the application can still function predictably.
Secure Handling of Sensitive Information
As highlighted under limitations, storing sensitive data directly in an INI file is highly discouraged. If it’s absolutely necessary to store sensitive information (e.g., database connection strings, API keys) in a configuration file, employ robust security measures:
- Encryption: Encrypt the sensitive values within the INI file and decrypt them only when accessed by the application. Ensure the encryption key is not stored alongside the INI file itself.
- Environment Variables: Store sensitive data as environment variables, which can be managed securely by the operating system or deployment platform, rather than in persistent files.
- Separate Secure Stores: Utilize dedicated secure configuration stores or vaults (e.g., HashiCorp Vault, cloud-based key management services) for sensitive data, with the INI file merely referencing the location or ID of the secure item.
- Strict Access Controls: Implement tight operating system-level permissions on INI files containing any sensitive data to restrict read access to only necessary accounts.
Conclusion
The INI file, though often overshadowed by its more feature-rich successors, remains a testament to the enduring power of simplicity in technology. From its origins as the backbone of early Windows application configuration to its continued relevance in embedded systems and niche applications today, the INI format has proven its value as a straightforward, human-readable method for managing software and system settings.
In an era of increasingly complex and interconnected technologies – where AI drives autonomous flight, high-resolution cameras capture every detail, and global navigation systems demand absolute precision – the underlying principle of adaptable configuration remains vital. While modern innovations often leverage more sophisticated data formats for their intricate settings, the INI file offers a foundational understanding of configuration design. It teaches us the importance of clear structure, the value of human readability, and the constant trade-off between simplicity and complexity in technological solutions. As we continue to push the boundaries of innovation, the legacy of the INI file serves as a reminder that sometimes, the most elegant solutions are also the most direct.
