The internet is an indispensable tool in modern life, facilitating communication, commerce, entertainment, and education. However, with its pervasive use comes a significant concern for many: privacy. Every click, every search, every website visited leaves a digital footprint. For those seeking to navigate the web with a greater degree of discretion, the concept of “incognito mode” has emerged as a popular solution. But what exactly is incognito mode, how does it work, and what are its limitations? This exploration delves into the functionalities and implications of private browsing, providing a comprehensive understanding of this ubiquitous feature.
The Fundamentals of Incognito Mode
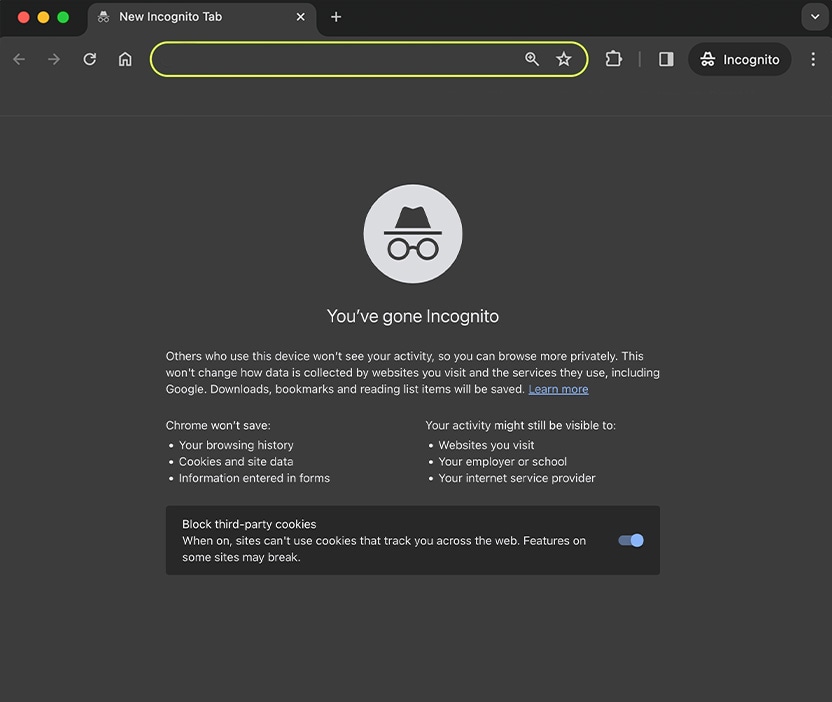
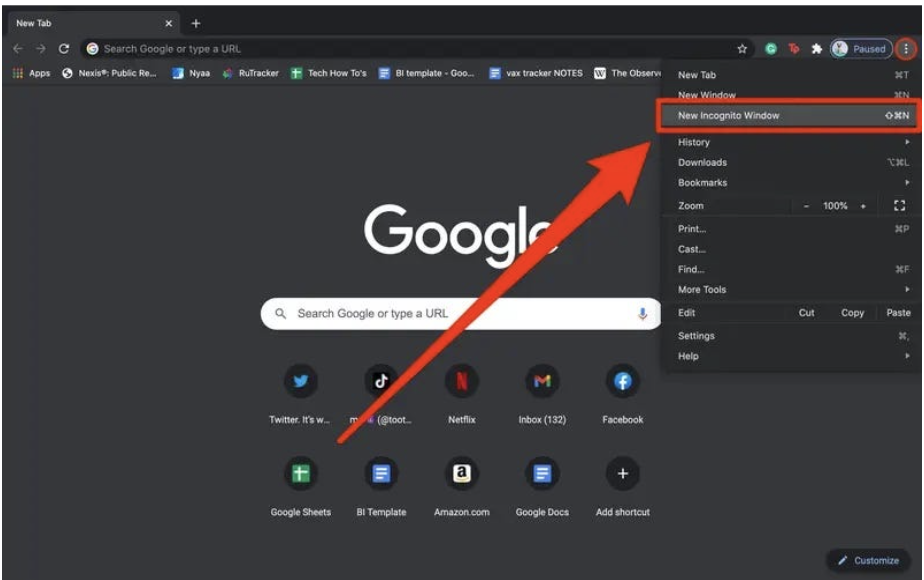
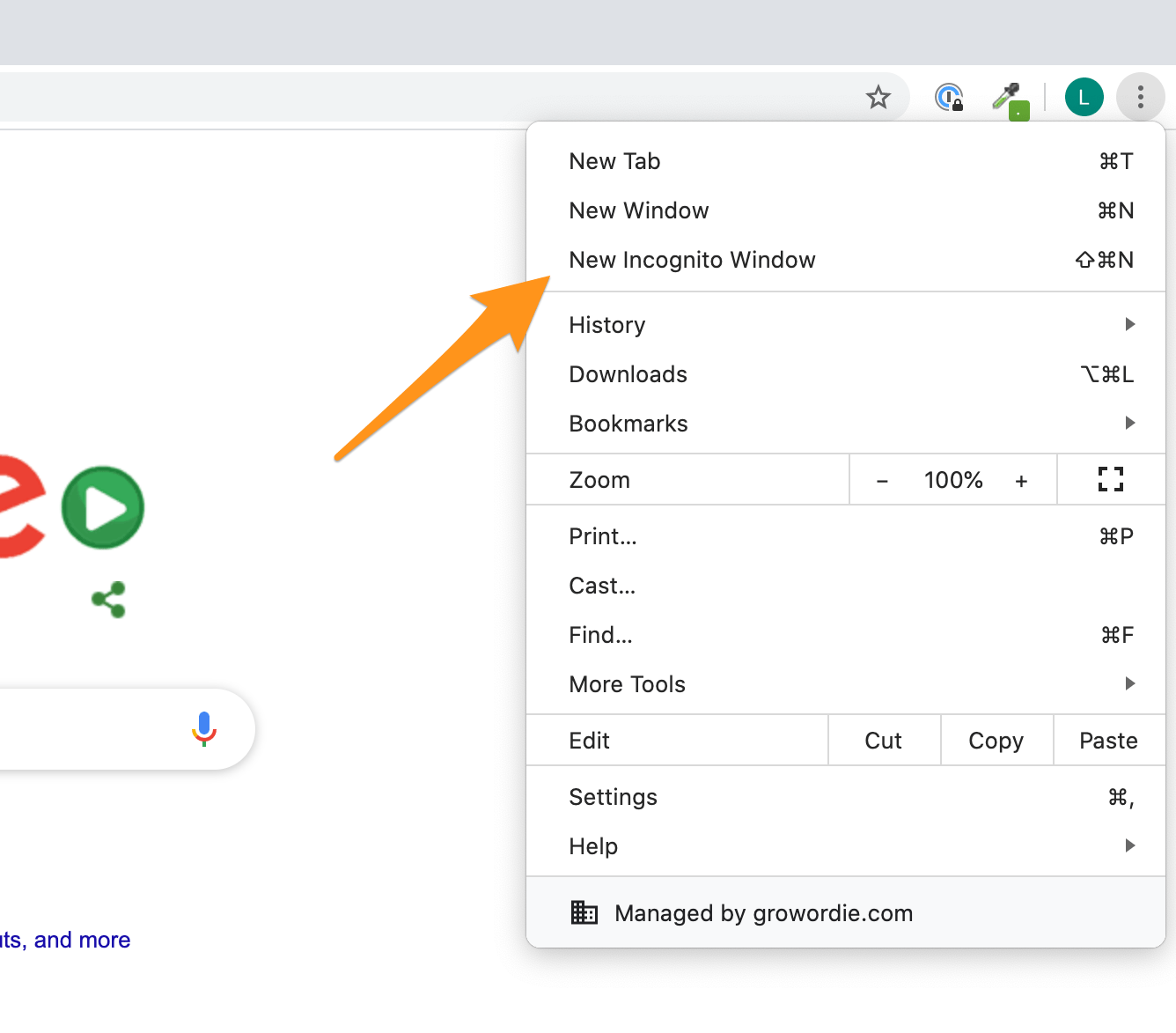
Incognito mode, also known by various names such as private browsing, private window, or in-private browsing, is a feature offered by most modern web browsers that allows users to browse the internet without their activity being saved locally on their device. At its core, it’s a temporary, isolated browsing session.
How Incognito Mode Works: Local Data Management
When you open a standard browser window, your browser diligently records a wealth of information about your online activities. This includes:
- Browsing History: A chronological list of all the websites you’ve visited. This is what appears when you access your browser’s history tab.
- Cookies: Small data files websites store on your computer to remember information about you, such as login credentials, shopping cart contents, or user preferences. These are crucial for website functionality and personalization.
- Site Data: This encompasses various pieces of information websites store locally, including cached images, scripts, and other temporary files that help speed up page loading times on subsequent visits.
- Form Data: Information you’ve entered into web forms, such as names, addresses, and email addresses, which browsers often autofill for convenience.
- Download History: A record of files you’ve downloaded, though not the files themselves.
- Search Queries: The terms you’ve typed into search engines.
Incognito mode fundamentally alters this data-saving process. When you initiate an incognito session, the browser creates a temporary, sandboxed environment. All the data that would typically be stored during a regular browsing session—history, cookies, site data, and form entries—is cleared automatically once you close all incognito windows. This means that after you’re done, there will be no trace of your browsing activity on your device in terms of these specific data types.
The “Privacy” Illusion: What Incognito Mode Doesn’t Hide
It’s crucial to understand that “incognito” is a misnomer in the sense that it doesn’t render you entirely anonymous or invisible online. While it shields your activity from being recorded on your specific device, it does not prevent your online activities from being visible to other entities. This is where much of the confusion and misconception surrounding incognito mode lies.
The primary benefit of incognito mode is preventing local data retention. This is useful for a variety of scenarios, such as:
- Using a shared computer: If you’re using a computer that others also use, incognito mode ensures that your browsing history and login information are not left behind, protecting your personal accounts.
- Shopping for gifts: Want to research a surprise gift without leaving a trace for the recipient to find in the browsing history? Incognito mode is ideal for this.
- Logging into multiple accounts on the same site: Some websites don’t allow you to be logged into multiple accounts simultaneously. Incognito mode can help by providing a fresh cookie environment.
- Avoiding targeted ads based on recent searches: While not foolproof, closing incognito windows clears cookies, which can help reset some ad-tracking mechanisms for that session.
- Researching sensitive topics: For personal or sensitive research, incognito mode can offer a sense of immediate privacy on your device.
However, it’s vital to recognize what incognito mode does not do. It does not:
- Make you anonymous to your Internet Service Provider (ISP): Your ISP can still see all the websites you visit, regardless of whether you are using incognito mode. They have direct access to your network traffic.
- Hide your activity from websites themselves: Websites you visit will still know you accessed them. They can still track your IP address, your browser fingerprint, and any information you voluntarily submit on their forms or through your interactions.
- Protect you from malware or viruses: Incognito mode does not offer any security enhancements against malicious software. If you download a virus or visit a compromised website, your device can still be infected.
- Prevent employer or school network monitoring: If you are using a computer or network provided by your employer or educational institution, they can likely still monitor your internet activity, even in incognito mode. Network administrators have visibility into traffic that passes through their servers.
- Obscure your IP address: Your IP address, which acts as your unique online identifier, is still visible to websites and your ISP. This means your general geographical location can still be determined.
- Bypass government surveillance: For entities with the legal authority and technical means, incognito mode offers no protection against surveillance.
The Technical Nuances of Incognito Mode
Understanding the technical underpinnings of incognito mode reveals why its privacy assurances are limited. Browsers are designed to interact with web servers, and these interactions inherently involve the exchange of data.
The Role of Cookies and Local Storage
Cookies are a cornerstone of how websites personalize user experiences and track activity. They are small text files stored on your computer that contain information about your visit. When you revisit a site, your browser sends these cookies back, allowing the site to recognize you.
In a standard browsing session, cookies persist across sessions, enabling features like “remember me” logins and personalized recommendations. When you use incognito mode, the browser essentially starts with a blank slate for cookies. Any cookies generated during the incognito session are ephemeral and are deleted when the session ends. This means that websites will treat each incognito visit as a new encounter, without prior knowledge of your previous interactions. Similarly, other forms of local storage, like localStorage and sessionStorage used by websites, are also cleared.
IP Addresses and Network Traffic
Your Internet Protocol (IP) address is a numerical label assigned to your device when it connects to the internet. It serves to identify your device and its location, enabling data to be sent and received. While incognito mode does not directly mask your IP address, it prevents the browser from storing information that might link your IP address to specific browsing activities on your device.
However, the IP address itself is still transmitted with every request to a website. This means the website you visit, your ISP, and potentially others can see your IP address. Your ISP, in particular, is aware of which IP addresses are assigned to its customers and can correlate online activity with specific accounts. This is why incognito mode is often referred to as “private browsing” rather than “anonymous browsing.”
Practical Applications and Limitations
The true value of incognito mode lies in its practical applications for everyday users, balanced against a clear understanding of its inherent limitations.
Scenarios Where Incognito Mode Shines
- Shared Devices: As mentioned, this is perhaps the most common and beneficial use case. If you share a computer with family members, roommates, or colleagues, using incognito mode prevents them from seeing your personal browsing history, search queries, or any account information you might have logged into during your session. This maintains a clear separation of personal online activity.
- Research and Exploration: When researching sensitive topics, personal health information, or anything that you might not want readily available in your regular browsing history, incognito mode provides a layer of immediate privacy on your device. It allows for discreet exploration without contributing to the local record of your digital life.
- Testing Website Functionality: For web developers and designers, incognito mode is invaluable for testing how a website appears and functions for a first-time visitor. It ensures that cached data, cookies, and login states do not interfere with the test, providing a clean environment to evaluate the user experience.
- Avoiding Price Discrimination: Some online retailers are known to adjust prices based on your browsing history and perceived demand. By using incognito mode, you can potentially avoid this by appearing as a new visitor, though sophisticated retailers might still employ other tracking methods.
- Logging into Multiple Accounts: If you need to log into different accounts for the same service (e.g., multiple Gmail accounts) on the same browser, incognito mode can be a convenient way to do this without logging out of your primary account in your regular window.
Beyond Local Privacy: What Incognito Mode Cannot Do
It’s imperative to reiterate that incognito mode is not a shield against all forms of online tracking or surveillance.
- Network Monitoring: Your employer, school, or even public Wi-Fi providers can monitor the websites you visit through their network infrastructure. Incognito mode does not prevent this network-level visibility.
- Website Tracking: Websites themselves can employ advanced tracking techniques beyond simple cookies. They can use browser fingerprinting (identifying unique characteristics of your browser configuration), IP address tracking, and the collection of information you provide directly on their pages.
- Account-Based Tracking: If you are logged into an account with a service (like Google, Facebook, etc.), your activity will be tracked and associated with that account, even if you are browsing in incognito mode. This is because the tracking originates from your authenticated presence on the service.
- Download Security: Incognito mode does not magically secure downloaded files. If you download a malicious file, it will still reside on your computer and can cause harm, regardless of how you downloaded it.
- Legal or Governmental Access: Incognito mode offers no protection against lawful requests for information from your ISP or other entities that have the legal authority to obtain your browsing data.
Enhancing Online Privacy Beyond Incognito Mode
For users who require a higher degree of online privacy and security than incognito mode provides, several additional tools and practices can be employed. These methods address the limitations of incognito mode by offering more robust solutions for anonymity and data protection.
Virtual Private Networks (VPNs)
A Virtual Private Network (VPN) is a powerful tool that encrypts your internet traffic and routes it through a server in a location of your choice. This has several key benefits for privacy:
- Masks Your IP Address: Your real IP address is hidden and replaced with the IP address of the VPN server. This makes it much harder for websites and services to track your location and activity back to you.
- Encrypts Your Traffic: All data transmitted between your device and the VPN server is encrypted. This means your ISP, or anyone monitoring your local network, cannot see the content of your online communications. They will only see that you are connected to a VPN server.
- Bypasses Geo-Restrictions: By connecting to a server in a different country, you can access content that may be restricted in your geographical location.
While VPNs significantly enhance privacy, it’s important to choose a reputable VPN provider with a strong no-logging policy. This ensures that the VPN provider itself is not keeping records of your online activities.
The Tor Browser
The Tor (The Onion Router) browser is designed for a much higher level of anonymity than standard browsers or even incognito mode. Tor works by routing your internet traffic through a series of volunteer-operated servers, known as relays. Each relay decrypts only one layer of encryption, revealing the IP address of the next relay. This multilayered encryption and relay system makes it extremely difficult to trace your activity back to its origin.
- Anonymity: Tor is considered one of the most effective tools for achieving online anonymity.
- Circumventing Censorship: It can be used to access websites and information that are blocked or censored in certain regions.
However, using Tor can come with drawbacks. The multiple relay hops can significantly slow down your internet connection, making it less suitable for activities that require high bandwidth, such as streaming video. Additionally, while Tor offers strong anonymity, it is not infallible, and advanced adversaries might still be able to de-anonymize users under certain circumstances.
Secure Search Engines
Traditional search engines like Google log your search queries and use this data to personalize your experience and target advertisements. For a more private search experience, consider using privacy-focused search engines such as:
- DuckDuckGo: This popular search engine does not track your searches, store your personal information, or create user profiles. It aims to provide unbiased search results without personalized manipulation.
- Startpage: Startpage sources its results from Google but anonymizes your searches and does not track you. It acts as a privacy-protecting intermediary.
These search engines ensure that your search history remains private, contributing to a more secure and less trackable online presence.
General Security Best Practices
Beyond specific privacy tools, adopting general cybersecurity best practices is crucial:
- Strong, Unique Passwords and Two-Factor Authentication (2FA): Use a password manager to create and store strong, unique passwords for all your online accounts. Enable 2FA whenever possible to add an extra layer of security.
- Keep Software Updated: Regularly update your operating system, browser, and applications. Updates often include security patches that fix vulnerabilities exploited by malware.
- Be Wary of Phishing Attempts: Be cautious of unsolicited emails, messages, or links that ask for personal information.
- Review App Permissions: On mobile devices, regularly review the permissions granted to applications and revoke unnecessary access.
By combining the judicious use of incognito mode with these advanced privacy tools and security practices, individuals can significantly enhance their online privacy and navigate the digital world with greater confidence and control. Incognito mode serves as a convenient first step, but a comprehensive approach is necessary for robust digital self-protection.
