In the vast and ever-expanding landscape of digital communication, the Hypertext Transfer Protocol (HTTP) serves as a foundational pillar, enabling the seamless exchange of data across the World Wide Web. While often associated with simple browsing and retrieving web pages, HTTP is a versatile protocol that underpins a multitude of complex interactions, from submitting forms to powering sophisticated APIs for autonomous systems. Among its various request methods, POST stands out as a critical mechanism for sending data to a server for processing, an operation that is increasingly vital in the realm of advanced robotics, drone technology, and remote sensing. Understanding HTTP POST is not merely an academic exercise; it’s essential for anyone involved in developing, deploying, or managing interconnected technological systems, including those that propel the advancements in aerial platforms and their applications.

This article delves into the intricacies of HTTP POST, exploring its fundamental principles, its distinct advantages over other HTTP methods, and its profound implications for data management and interaction within the burgeoning drone and UAV ecosystem. From transmitting critical flight telemetry to uploading high-resolution mapping data, HTTP POST plays a silent yet indispensable role in enabling the sophisticated capabilities we now expect from modern aerial technology.
Understanding the HTTP Protocol: The Foundation of Web Communication
At its core, HTTP is a client-server protocol, meaning a client (e.g., a web browser, a drone’s onboard computer, a ground control station) sends a request to a server, and the server responds. This stateless protocol forms the backbone of data exchange on the internet, defining how messages are formatted and transmitted, and what actions web servers and browsers should take in response to various commands. While simple in concept, its flexibility has allowed it to evolve into the ubiquitous standard for web-based interactions.
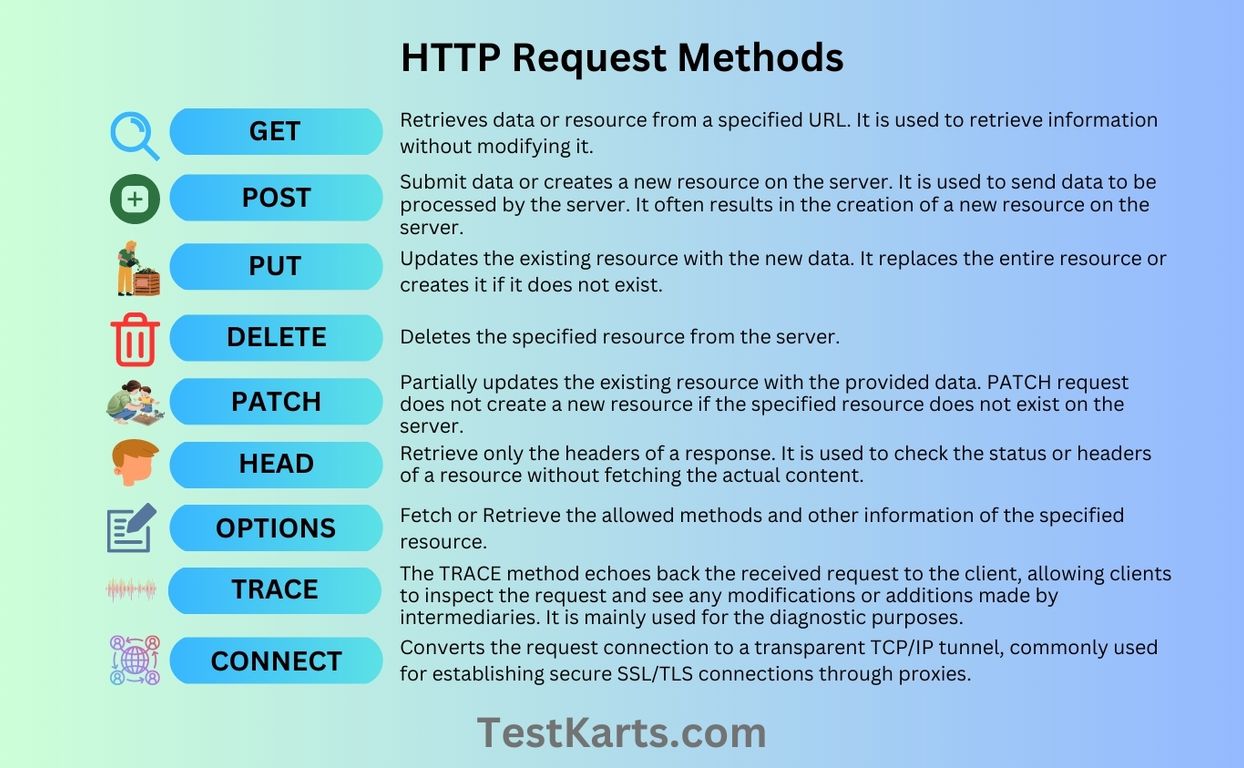
The strength of HTTP lies in its straightforward request-response model, but its true power comes from the variety of “methods” or “verbs” it offers to specify the desired action on the resource identified by the URL. These methods dictate the intent of the client, informing the server whether to retrieve data, create a new resource, update an existing one, or delete it.
Request Methods: GET vs. POST
Among the most commonly used HTTP methods are GET and POST, each serving distinct purposes. GET is designed to retrieve data from a specified resource. When you type a URL into your browser or click a link, your browser typically sends a GET request. The data sent with a GET request is appended to the URL as query parameters, making it visible in the URL bar and in browser history. This characteristic makes GET requests cacheable and idempotent (meaning making the same request multiple times will have the same effect as making it once, without additional side effects).
POST, on the other hand, is used to send data to the server to create or update a resource. Unlike GET, the data sent with a POST request is included in the body of the request, not in the URL. This distinction is crucial for several reasons, including security, data volume, and the nature of the operation being performed. POST requests are generally not cacheable by default and are not considered idempotent, as repeatedly submitting a POST request might lead to the creation of multiple identical resources or repeated updates.
The Role of Request Bodies
The primary differentiator for POST is its utilization of the request body. While GET can include minimal data in the URL query string, POST is specifically designed to transmit larger and more complex data structures within the request’s message body. This body can contain various data formats, such as form data (encoded as application/x-www-form-urlencoded or multipart/form-data), JSON (application/json), XML (application/xml), or even binary data.
The ability to encapsulate data within the request body is fundamental to POST‘s utility. It means that sensitive information, complex payloads, or large files can be sent to the server without being exposed in the URL, providing a layer of privacy and facilitating the transfer of substantial amounts of information necessary for sophisticated applications, including those found in drone operations.
Why HTTP POST is Crucial for Data Submission
The distinct characteristics of HTTP POST make it the preferred method for any operation that involves submitting new information to a server or making changes to an existing resource. Its design addresses several key challenges that other HTTP methods, particularly GET, cannot adequately handle, thereby ensuring data integrity, security, and scalability for modern applications.
Securing Data with POST
One of the most significant advantages of POST over GET is its enhanced capability for handling sensitive data. When data is sent via GET, it is appended to the URL, making it visible in browser history, server logs, and potentially vulnerable to interception or manipulation. For applications involving passwords, personal identifiable information (PII), or confidential operational parameters for autonomous systems, exposing this data is an unacceptable security risk.
POST addresses this by encapsulating data within the request body. While POST requests are not inherently encrypted (that’s the role of HTTPS – HTTP Secure, which encrypts the entire communication channel), the data is not publicly exposed in the URL. This design, combined with HTTPS, provides a robust mechanism for securely transmitting sensitive information, a non-negotiable requirement for commanding drones, sending flight plans, or uploading proprietary sensor data.
Handling Large Data Payloads
The practical limits on URL length imposed by browsers and web servers mean that GET requests are unsuitable for transmitting large amounts of data. These limits can vary but are generally in the kilobytes, making GET impractical for scenarios requiring substantial data transfer. POST, conversely, faces no such inherent limitations on the size of its request body, other than those imposed by server configurations or practical network throughput.
This capacity for large data payloads is incredibly important for various technological applications. Consider a drone collecting high-resolution images or video footage during a mapping mission, or an array of sensors continuously generating telemetry data. To upload this data to a cloud-based processing platform or a central ground control system, POST is the indispensable method. It allows for the efficient and reliable transfer of multi-megabyte or even gigabyte files, enabling the collection and analysis of rich environmental data critical for advanced remote sensing and geographical information systems (GIS).
HTTP POST in the Drone and UAV Ecosystem
The principles of HTTP POST extend far beyond traditional web browsing, finding critical applications within the rapidly evolving domain of drones and Unmanned Aerial Vehicles (UAVs). As these autonomous systems become more sophisticated and integrated into various industries, the need for robust, secure, and efficient data exchange mechanisms grows exponentially. HTTP POST fulfills a pivotal role in enabling seamless communication between drones, ground control systems, cloud platforms, and other networked services.
Telemetry and Real-time Data Reporting
Modern drones are equipped with an array of sensors that constantly collect critical flight data: GPS coordinates, altitude, speed, battery status, motor RPMs, temperature, and more. This telemetry data is vital for monitoring the drone’s health, ensuring mission success, and providing real-time operational insights. While some real-time, low-latency communication might leverage WebSockets or custom UDP protocols, for periodic updates, logging, and aggregation of larger data batches, HTTP POST is often employed.
Ground control stations or cloud-based drone management platforms can receive this telemetry data via POST requests. A drone’s onboard computer or a connected module can periodically package sensor readings into a JSON payload and POST it to a designated API endpoint. This allows for centralized logging, historical analysis, and the triggering of alerts or automated responses based on flight parameters, forming a crucial component of drone fleet management and predictive maintenance strategies.
Mission Planning and Command & Control APIs
The planning and execution of complex drone missions often involve sending detailed instructions from a ground control system to a UAV. These instructions can include flight paths (waypoints), camera settings, payload activation commands, and specific autonomous behaviors. Given the criticality and often proprietary nature of mission plans, HTTP POST is an ideal method for transmitting this data securely.
When a user defines a flight path on a mapping interface and clicks “upload,” the ground control software can serialize this mission plan into a structured format (e.g., JSON) and POST it to the drone’s onboard API or an intermediary cloud service. This ensures that the complete, unalterable mission data is delivered to the drone for execution. Similarly, more advanced command and control operations, such as triggering specific actions or uploading new firmware, can also leverage POST requests to ensure data integrity and proper server-side processing before the command is relayed to the drone.
Uploading Captured Data for Analysis
One of the most valuable contributions of drones to various industries – from agriculture and construction to environmental monitoring and infrastructure inspection – is their ability to collect vast amounts of high-resolution visual and sensor data. After a mapping or inspection flight, the drone typically returns with gigabytes of images, video, thermal data, or LiDAR scans. Uploading this raw data for post-processing and analysis is where HTTP POST truly shines.
Whether the data is offloaded from the drone to a local ground station and then POSTed to a cloud platform, or directly transmitted from a drone with robust network connectivity, POST facilitates the transfer of these large binary files. Specialized POST requests using multipart/form-data encoding allow for the simultaneous upload of multiple files along with metadata (e.g., flight ID, timestamp, mission type). This capability underpins applications like photogrammetry for 3D modeling, multispectral analysis for crop health assessment, and thermal imaging for anomaly detection, transforming raw drone data into actionable intelligence.
Implementing HTTP POST: Practical Considerations
Implementing HTTP POST effectively requires careful consideration of both the client-side (the entity sending the request) and the server-side (the entity receiving and processing the request). Proper implementation ensures data is sent correctly, securely, and handled efficiently, which is particularly vital for the reliability of drone operations and data workflows.
Client-Side Implementation
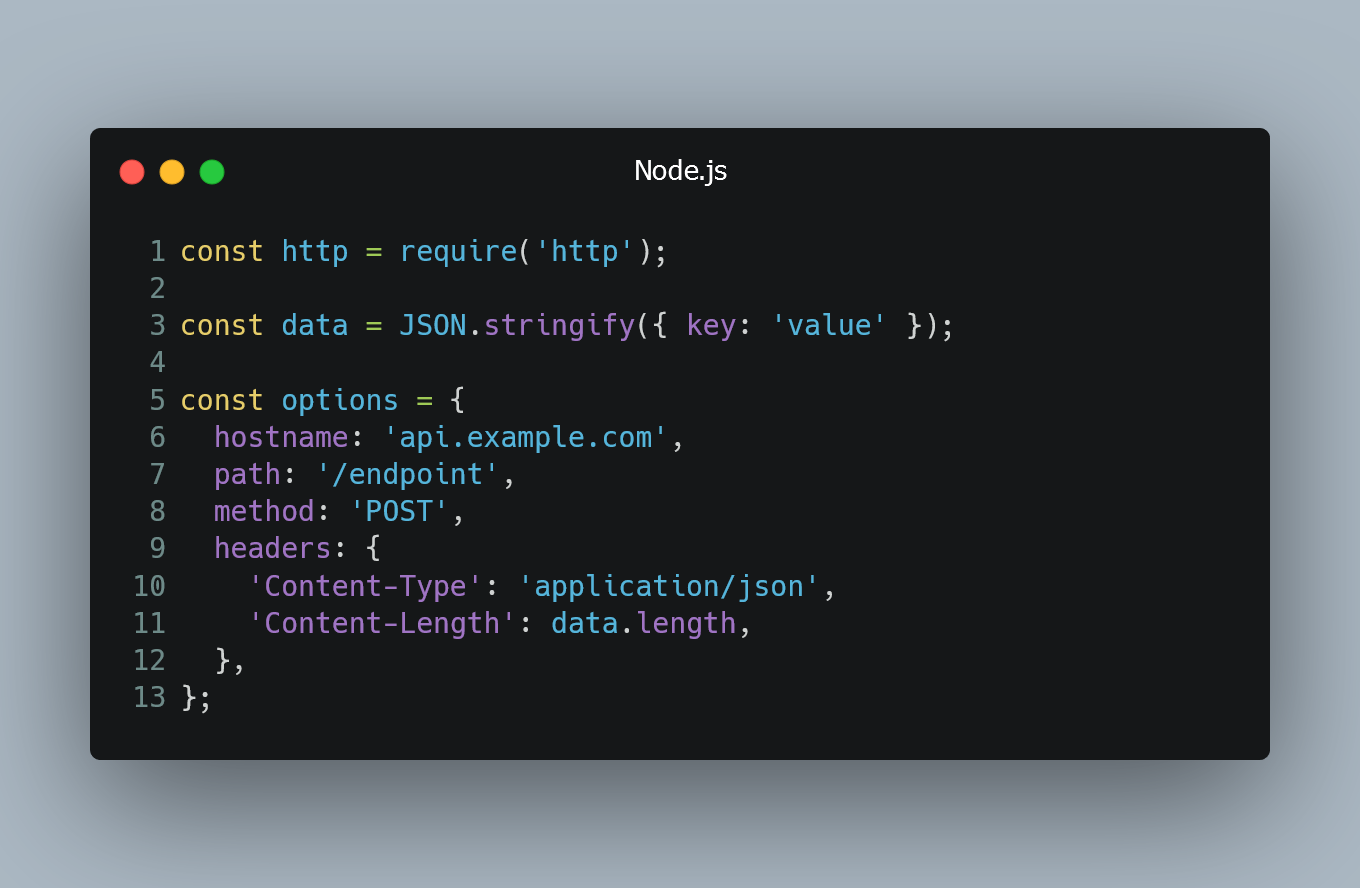
On the client-side, making an HTTP POST request typically involves using a specific library or framework function. In web development, JavaScript’s fetch API or XMLHttpRequest are common. For applications written in Python, the requests library is widely used. For embedded systems or drone onboard computers, C/C++ libraries or custom network stacks might be employed. The key steps involve:
- Defining the Target URL: The endpoint on the server where the data needs to be sent.
- Structuring the Data Payload: Serializing the data into an appropriate format (e.g., JSON, form data, binary). This is often the most critical step, as incorrect formatting will lead to server errors.
- Setting HTTP Headers: Especially the
Content-Typeheader, which tells the server what type of data is in the request body (e.g.,application/json,multipart/form-data). Other headers might includeAuthorizationfor authentication. - Executing the Request: Sending the
POSTrequest with the data payload and headers. - Handling the Response: Processing the server’s response, which typically includes a status code (e.g., 200 OK, 201 Created, 400 Bad Request, 500 Internal Server Error) and often a response body containing confirmation or error messages.
For drone systems, the client might be a compact onboard computer, needing efficient and robust network code to handle potential disconnections or retransmissions, ensuring critical data is delivered even in challenging environments.
Server-Side Processing and Best Practices
On the server-side, an application or API endpoint is configured to listen for POST requests at a specific URL. When a POST request is received, the server’s responsibilities include:
- Parsing the Request Body: Understanding the
Content-Typeheader to correctly parse the incoming data payload. - Validating Data: Ensuring the received data conforms to expected formats and constraints (e.g., checking data types, ranges, required fields). This is crucial for preventing malformed data from corrupting systems.
- Processing the Data: Performing the intended action, such as storing telemetry in a database, updating a mission status, or saving uploaded media files to storage.
- Generating a Response: Sending an appropriate HTTP status code and a response body back to the client, indicating the success or failure of the operation.
- Authentication and Authorization: Verifying the identity of the client and ensuring they have the necessary permissions to perform the requested action. This is paramount for securing drone operations against unauthorized access.
Best practices for server-side POST handling emphasize idempotence where possible (even though POST is not inherently idempotent, the server can implement logic to achieve it for specific operations like creating unique resources), robust error handling, comprehensive logging, and thorough security measures to protect against common web vulnerabilities.
The Future of Data Exchange in Autonomous Systems
As drone technology continues its rapid advancement, the role of efficient and reliable data exchange mechanisms like HTTP POST will only grow in importance. The trend towards increasing autonomy, AI integration, and real-time decision-making necessitates even more sophisticated ways to transmit and process data collected by UAVs.
Edge Computing and Local Processing
While cloud processing remains vital for large-scale data analysis, there is a growing push towards edge computing – processing data closer to the source (i.e., on the drone itself or at a local ground station). This reduces latency, conserves bandwidth, and enables quicker decision-making for critical applications like obstacle avoidance or immediate anomaly detection. HTTP POST could still play a role here, sending processed summaries or critical alerts to the cloud, rather than raw, voluminous data. This involves POSTing smaller, pre-analyzed payloads, optimizing network usage.
Interoperability and Standardized APIs
The drone ecosystem is becoming increasingly diverse, with various hardware manufacturers, software platforms, and service providers. Achieving seamless interoperability requires standardized APIs (Application Programming Interfaces) that define how different components can communicate. HTTP POST will continue to be a cornerstone for these APIs, enabling third-party developers to build applications that interact with drone platforms for mission planning, data ingestion, and fleet management. The adoption of open standards and well-documented RESTful APIs (which heavily rely on HTTP POST for resource creation/update) will be crucial for fostering innovation and expanding the capabilities of autonomous aerial systems.
In conclusion, HTTP POST is far more than a simple web method; it is a fundamental enabler of modern interactive and data-driven applications. Within the dynamic and complex world of drones and UAVs, its ability to securely and efficiently transmit diverse data payloads makes it an indispensable tool for everything from real-time telemetry and mission command to the upload of rich environmental datasets. As technology evolves, HTTP POST will undoubtedly continue to adapt and underpin the sophisticated data exchange requirements of the next generation of autonomous flight.
