In the rapidly evolving landscape of unmanned aerial vehicles (UAVs) and autonomous systems, the definition of an “endpoint” has shifted. Once limited to laptops and desktop workstations, endpoints now include high-altitude mapping drones, remote sensing platforms, and complex ground control stations (GCS). As drone technology moves further into the realm of enterprise operations and critical infrastructure, the necessity for robust, hardware-level protection becomes paramount. This is where the principles of HP Wolf Security enter the conversation.
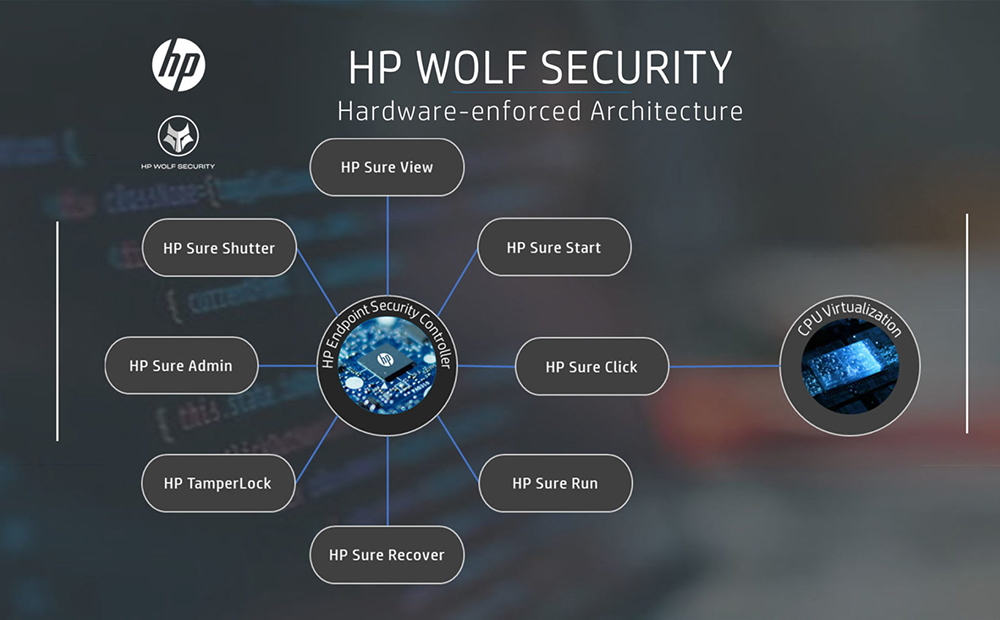
HP Wolf Security is not merely a software suite; it is a comprehensive security architecture designed to protect users from the BIOS level up to the cloud. In the context of “Tech & Innovation” within the drone industry, understanding HP Wolf Security provides a blueprint for how we must secure the next generation of autonomous flight systems, AI-driven data collection, and remote sensing operations.
The Evolution of Cybersecurity in the Drone Ecosystem
The drone industry has undergone a radical transformation over the last decade. What began as a hobbyist market has matured into a sophisticated sector driven by Tech & Innovation, where drones are utilized for everything from precision agriculture to national security. However, as the capabilities of these machines have grown, so too has the complexity of the cyber threats they face.
From Consumer Toys to Enterprise Endpoints
Originally, the primary concern for drone operators was physical flight safety—avoiding crashes and ensuring stable GPS signals. Today, however, drones are essentially flying computers. They run complex operating systems, process massive amounts of sensitive data through AI follow modes, and communicate via encrypted and unencrypted channels with mobile devices and cloud servers.
HP Wolf Security recognizes that modern devices are under constant siege. By applying the same logic to the drone industry, we see that every drone in a fleet is an endpoint that can be compromised. If a drone used for mapping critical infrastructure is “hijacked” at the firmware level, the data it collects could be manipulated or stolen. The shift from “toy” to “tool” necessitates a shift from “basic encryption” to “Wolf-class” endpoint resilience.
The Growing Threat Surface in Autonomous Systems
Innovation in autonomous flight and AI-driven navigation has expanded the “threat surface” of drone operations. When a drone operates autonomously using remote sensing and mapping software, it relies on a chain of trust that starts at the hardware level. HP Wolf Security addresses this by assuming that the perimeter has already been breached.
In the drone world, this means protecting the flight controller, the telemetry links, and the onboard processing units that handle AI tasks. Whether it is a “man-in-the-middle” attack on a telemetry feed or a malicious firmware update, the innovations in drone tech require a security posture that is “always on” and “always watching,” much like the proactive defense mechanisms found in the Wolf Security suite.
Decoding the HP Wolf Security Philosophy for UAV Applications
To understand how HP Wolf Security relates to the technological advancement of drones, we must look at its core pillars: hardware-enforced protection, below-the-OS resilience, and application isolation. These concepts are directly applicable to the development of more secure, more innovative drone flight systems.
Hardware-Enforced Protection: Below-the-OS Security
One of the standout features of HP Wolf Security is its focus on “Below-the-OS” protection. Technologies like HP Sure Start provide a self-healing BIOS that can detect a firmware attack and automatically recover to a known good state.
In the realm of Drone Tech & Innovation, the flight controller’s firmware is the equivalent of a computer’s BIOS. A compromised flight controller can lead to a “flyaway” or a total loss of the asset. By integrating hardware-enforced security—where the hardware itself can verify the integrity of the code before it executes—drone manufacturers can ensure that even if a hacker gains access to the communication link, the core flight systems remain immutable. This “Silicon-to-Cloud” approach is the gold standard for securing autonomous machines that operate in high-risk environments.
Application Isolation and Containerization
HP Wolf Security utilizes micro-virtualization (HP Sure Click) to isolate risky tasks. For example, if a user opens a malicious attachment, it is trapped in a “micro-VM,” preventing it from infecting the rest of the system.

When we apply this innovation to drone technology, we see the potential for “Mission Isolation.” Modern drones often run third-party apps for mapping, thermal imaging, or payload control. If one of these third-party applications is compromised, it should not be able to affect the primary flight systems or the drone’s navigation sensors. By containerizing different aspects of the drone’s “brain,” developers can innovate more freely, knowing that a bug or a breach in a secondary sensor app won’t lead to a catastrophic failure of the entire platform.
Applying Wolf-Class Security to Remote Sensing and Mapping
Remote sensing and mapping are perhaps the most data-intensive areas of drone innovation. These tasks involve capturing gigabytes of high-resolution imagery, LiDAR data, and thermal signatures. Protecting the integrity of this data is a primary function of modern security frameworks.
Protecting Data Integrity in Aerial Surveys
When a drone performs a remote sensing mission—such as inspecting power lines or mapping a construction site—the data collected is the “product.” If that data is altered, the entire mission is compromised. HP Wolf Security’s emphasis on identity protection and credential guarding (HP Sure Sense) is vital here.
In a professional drone workflow, the “identity” of the drone and the “identity” of the pilot must be cryptographically verified. Innovation in this space involves using AI-driven threat detection to ensure that the data being written to the onboard storage hasn’t been tampered with by unauthorized background processes. This ensures that when a surveyor receives a 3D point cloud, they can be 100% certain it reflects the physical reality of the site.
Securing the Ground Control Station (GCS)
We often focus on the drone itself, but the Ground Control Station (GCS)—usually a ruggedized laptop or tablet—is where the pilot interacts with the machine. This is the most vulnerable point in the chain. HP Wolf Security was built precisely for this: protecting the endpoint where human interaction meets machine control.
The GCS often connects to the internet to download maps or upload flight logs to the cloud. This connectivity introduces risk. By utilizing the advanced endpoint protection of a Wolf-enabled device, drone operators can ensure that their flight control software is running in a protected environment, shielded from keyloggers, screen-scraping malware, and unauthorized remote access. In the world of tech and innovation, the security of the pilot’s interface is just as important as the stabilization of the drone in the air.
The Future of Autonomous Flight: AI and Threat Detection
As we look toward the future of drone innovation, the integration of Artificial Intelligence (AI) and Machine Learning (ML) is inevitable. AI is what allows for “Follow Mode,” “Obstacle Avoidance,” and “Autonomous Pathfinding.” However, AI itself must be secured.
Self-Healing Firmware and Resilient Architectures
The next frontier for drone tech is “resilient autonomy.” HP Wolf Security’s “Sure Run” technology monitors critical processes and restarts them if they are killed by malware. Similarly, future autonomous drones will require “Sure Run” for their AI modules.
If a drone’s obstacle avoidance system is disabled by a cyber-attack or a software glitch, the drone should have the internal intelligence to recognize the failure and immediately initiate a safe landing or an automated “return to home” (RTH) protocol. This level of self-healing architecture is the natural evolution of drone technology, moving from simple mechanical machines to intelligent, self-protecting entities.

The Convergence of IT and OT in Drone Operations
Finally, we must recognize that drone technology is the point where Information Technology (IT) and Operational Technology (OT) collide. HP Wolf Security represents the peak of IT security, but its principles are increasingly necessary for OT assets like drones.
Innovation in this space is no longer just about longer flight times or better cameras; it is about “Operational Trust.” As drones become integrated into the “Internet of Things” (IoT) and “Internet of Drones” (IoD), they will need to defend themselves against a wide array of sophisticated digital threats. HP Wolf Security provides a roadmap for this journey, proving that security is not a barrier to innovation, but rather the foundation upon which complex, autonomous, and truly useful technology can be built.
In conclusion, “What is HP Wolf Security?” is a question with an answer that reaches far beyond the office cubicle. In the context of drone tech and innovation, it is a philosophy of resilience. It is the realization that to fly higher, further, and more autonomously, our machines must be protected from the inside out—starting at the silicon and extending to the very edge of the sky. As we continue to push the boundaries of what UAVs can do, the layered, hardware-enforced defense strategies pioneered by HP Wolf will become the standard for every professional flight operation across the globe.
