The digital landscape is a vast and complex ecosystem, often presenting users with both readily accessible information and areas that are intentionally obscured. The term “Hidden Wiki” often surfaces in discussions about the darker corners of the internet, specifically within the context of the deep web and its associated marketplaces. Understanding what the Hidden Wiki represents requires delving into the structure of the internet itself and the mechanisms that govern access to its various layers. While the title might evoke a sense of mystery, its practical function is primarily that of a navigational tool, albeit for a specific and often controversial segment of online content.
Navigating the Deep Web: The Role of Link Directories
To comprehend the Hidden Wiki, one must first understand the distinction between the surface web, the deep web, and the dark web. The surface web is what most users interact with daily – sites indexed by standard search engines like Google, Bing, and DuckDuckGo. This is the tip of the iceberg. Below this lies the deep web, a much larger portion of the internet that is not indexed by conventional search engines. This includes password-protected content, online banking portals, private databases, and cloud storage services. Access to these areas is usually restricted by logins or other authentication methods, but they are not inherently malicious.
The dark web is a subset of the deep web that requires specific software, configurations, or authorization to access. The most common method of accessing the dark web is through the Tor (The Onion Router) network. Tor works by routing internet traffic through a series of volunteer-operated servers, encrypting the data at each step. This anonymizes the user’s IP address and location, making it difficult to trace their online activity. It is within this anonymized environment that the Hidden Wiki finds its primary purpose.
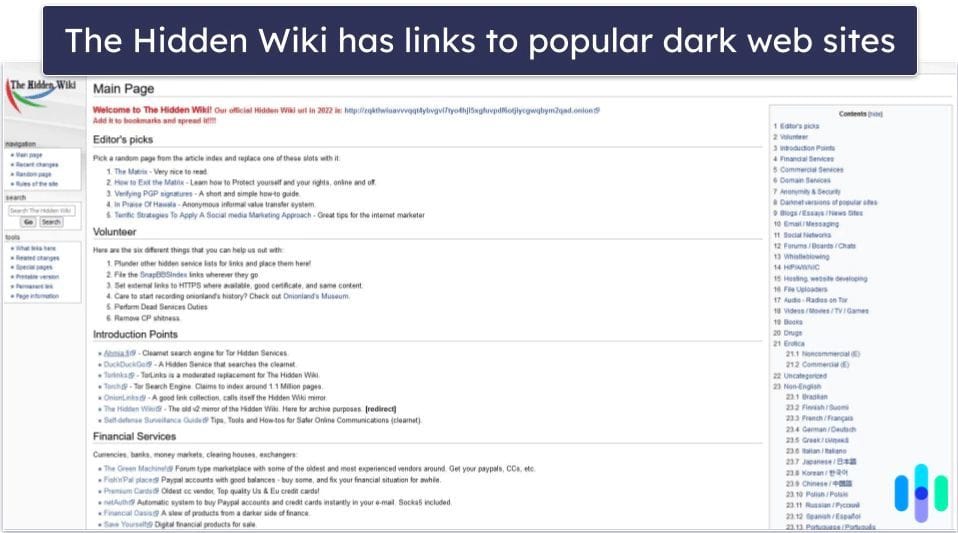
The Hidden Wiki, in essence, is a directory of links. Unlike a traditional wiki which might contain collaborative articles and editable content, the Hidden Wiki primarily serves as a curated list of hyperlinks pointing to .onion websites. These .onion addresses are specific to the Tor network and are not accessible through standard web browsers. The nature of these linked sites varies widely, ranging from forums and communication platforms to marketplaces for goods and services, some of which are entirely legal and legitimate, while others operate in illicit or illegal domains.
The Structure and Evolution of Hidden Wikis
Historically, the concept of a “Hidden Wiki” emerged as a way for users of the Tor network to discover and access .onion sites. Early iterations were often simple text files or basic web pages listing a few known links. As the dark web grew and more .onion sites were established, these directories became more complex. The term “Hidden Wiki” itself is not tied to a single, definitive website. Instead, it has become a generic descriptor for such link aggregation sites that operate on the Tor network. Multiple Hidden Wiki instances exist, often with different link collections, updates, and even competing for user traffic.
The content hosted on these Hidden Wikis is dynamic and subject to constant change. Links can become outdated as sites go offline, new sites emerge, or administrators update their directories. Maintaining an up-to-date and comprehensive Hidden Wiki is a challenge, often requiring active community participation or dedicated administrators who continuously scan for and verify active .onion links. This constant flux contributes to the perception of the Hidden Wiki as an ever-shifting and elusive entity.
Content Spectrum: Legitimate vs. Illicit
It is crucial to differentiate the types of content found through Hidden Wiki directories. While the media often focuses on the illicit marketplaces and criminal activities rumored to exist on the dark web, there are also legitimate uses for Tor and .onion sites. These include:

- Secure Communication: For journalists, whistleblowers, and activists in oppressive regimes, Tor provides a vital tool for secure and anonymous communication. .onion sites can host encrypted messaging services and secure forums for these individuals.
- Privacy-Focused Services: Several organizations and individuals host their websites on the dark web to offer services with enhanced privacy protections, shielding users from surveillance and data collection prevalent on the surface web.
- Bypass Censorship: In countries where internet access is heavily censored, Tor can be used to access information and websites that are otherwise blocked.
- Forums and Communities: Beyond the sensational, there are many forums and communities on the dark web that cater to niche interests, support groups, and discussion of various topics in a relatively anonymous environment.
However, the anonymity and the lack of centralized oversight that Tor provides also make it an attractive platform for illegal activities. Hidden Wikis are frequently used to link to marketplaces that sell drugs, stolen data, counterfeit goods, weapons, and other illicit items. This association has led to the term “Hidden Wiki” becoming almost synonymous with the criminal underbelly of the internet in popular perception.
The Technical Underpinnings of .onion Services
The functionality of a Hidden Wiki and the sites it links to is deeply intertwined with the technology of the Tor network. Unlike standard websites that reside on servers with publicly known IP addresses, .onion services are hosted within the Tor network itself. This means that they do not have a traditional IP address. Instead, they are identified by their .onion address, which is a pseudorandom string of characters.
When a user accesses a .onion address through the Tor Browser, the Tor network handles the connection. This involves a complex process of establishing encrypted circuits through multiple relay nodes. For a .onion service, this also involves a rendezvous point. The service publishes its public key and a descriptor at a distributed hash table (DHT) within the Tor network. When a user requests the service, their Tor client finds this descriptor, which tells it how to connect to the service’s designated introduction points. Then, the client and the service agree on a rendezvous point through which they can communicate anonymously.
This technical architecture ensures that neither the user nor the service provider knows the other’s true IP address. For the operators of a Hidden Wiki, this means they can host their link directory as a .onion service, and the links they provide will point to other .onion services, all within the secure and anonymous framework of the Tor network.
Security Considerations and Risks
While the Hidden Wiki and the dark web offer avenues for privacy and anonymity, they are also rife with significant risks. Users navigating these spaces should be acutely aware of the potential dangers:
- Malware and Scams: Many .onion sites are designed to trick users into downloading malware, phishing for personal information, or participating in fraudulent schemes. Even seemingly legitimate links can lead to compromised sites.
- Illegal Content Exposure: Users can unintentionally stumble upon disturbing or illegal content, which can have psychological impacts or even legal repercussions depending on local laws.
- Law Enforcement Surveillance: While Tor aims for anonymity, it is not foolproof. Law enforcement agencies actively monitor the dark web and have developed sophisticated techniques to track down users involved in illegal activities. The presence of a Hidden Wiki linking to illicit sites makes it a focal point for such investigations.
- Unreliable Information: Link directories like the Hidden Wiki are often not meticulously curated. Links can be outdated, misleading, or lead to dead ends. Information found on these sites should always be treated with extreme skepticism.

The Ongoing Debate and Future of Dark Web Link Directories
The existence of Hidden Wikis and the dark web itself sparks ongoing debates about privacy, security, freedom of speech, and the regulation of online spaces. Proponents argue for the necessity of anonymous communication and access to uncensored information, particularly for those living under authoritarian regimes. Critics, however, point to the facilitation of criminal enterprises and the potential for societal harm.
As technology evolves, so too will the methods of navigating and organizing content within the deep and dark web. While traditional link directories like the Hidden Wiki have served their purpose, newer and more sophisticated methods of discovery and access may emerge. The underlying principles of anonymity and the demand for spaces beyond mainstream oversight, however, are likely to persist. Therefore, understanding the function of tools like the Hidden Wiki remains relevant for comprehending the multifaceted nature of the internet and the continuous efforts to control, secure, or access information across its various layers.
