In an increasingly interconnected world, Global Positioning System (GPS) technology has become an indispensable cornerstone of modern life, particularly within the realm of flight technology. From commercial aviation to sophisticated unmanned aerial vehicles (UAVs) and advanced navigation systems, GPS provides the precise positioning, navigation, and timing (PNT) data that these systems rely upon for safe and efficient operation. However, this critical dependency also exposes inherent vulnerabilities, one of the most insidious being GPS spoofing. Far more sophisticated than simple jamming, GPS spoofing represents a calculated deception, feeding false PNT information to a receiver, potentially leading to catastrophic consequences for flight operations. Understanding this threat is paramount for safeguarding the integrity and reliability of our aerospace infrastructure.
Understanding GPS and its Vulnerabilities
To fully grasp the implications of GPS spoofing, it’s essential to first understand how GPS works and why it possesses certain inherent weaknesses that can be exploited. GPS is a space-based radionavigation system owned by the U.S. government and operated by the U.S. Space Force. It provides users with PNT services globally.
The Fundamentals of GPS Operation
The GPS constellation consists of a network of 31 active satellites orbiting Earth, each continuously transmitting radio signals. A GPS receiver on the ground, or in an aircraft, passively listens to these signals. Each signal contains information about the satellite’s precise orbital position (ephemeris data) and the exact time the signal was transmitted. By receiving signals from at least four satellites, a GPS receiver can calculate its precise three-dimensional position (latitude, longitude, and altitude) and synchronize its internal clock with atomic clock precision. The principle behind this calculation is trilateration: measuring the time difference between signal transmission and reception to determine the distance to each satellite, and then using these distances to pinpoint the receiver’s location. The weak nature of the GPS signals, traveling vast distances from space, is a key characteristic that both enables its widespread use and contributes to its vulnerability.
Why GPS is Crucial for Modern Flight Technology
For modern flight technology, GPS is not merely a convenience; it is a foundational element.
- Navigation: It provides pilots and autonomous flight systems with real-time, highly accurate positional data, enabling precise flight path planning, execution, and air traffic control management.
- Stabilization Systems: Many advanced flight control systems, particularly in UAVs, rely on GPS for maintaining stable flight, especially during hovering or autonomous maneuvers.
- Autonomous Operations: The burgeoning field of autonomous flight, from drone delivery services to unpiloted commercial aircraft concepts, hinges entirely on reliable GPS for self-navigation, obstacle avoidance, and mission execution without human intervention.
- Collision Avoidance: Systems like ADS-B (Automatic Dependent Surveillance–Broadcast) use GPS data to broadcast an aircraft’s position, contributing significantly to air traffic awareness and collision prevention.
- Timing Synchronization: Precise timing information from GPS is crucial for various onboard systems, communication networks, and even the synchronization of radar and other sensors.
Without robust and trustworthy GPS data, the precision, safety, and autonomy of modern flight technologies would be severely compromised, reverting to less efficient and less accurate methods.
Inherent Vulnerabilities of GPS Signals
Despite its technological sophistication, GPS is not without its Achilles’ heel. The primary vulnerability stems from the nature of the signals themselves:
- Weak Signals: GPS signals arrive at Earth with very low power. They are designed to be universally accessible, meaning they don’t require high-power transmitters. This weakness makes them susceptible to interference.
- Line-of-Sight Dependency: GPS signals are microwave signals that travel in a straight line and can be blocked by physical obstructions like buildings, terrain, or even dense foliage, leading to signal loss or multi-path errors.
- Lack of Native Authentication: The original GPS design did not incorporate robust signal authentication mechanisms. A GPS receiver typically assumes that any incoming signal resembling a GPS signal is legitimate. This assumption is what makes spoofing possible. The receiver processes the signal without verifying its source or authenticity, making it difficult to distinguish between genuine satellite signals and maliciously fabricated ones.
These vulnerabilities, particularly the lack of authentication, lay the groundwork for malicious actors to deceive GPS receivers, posing a significant threat to flight technology.
The Mechanics of GPS Spoofing
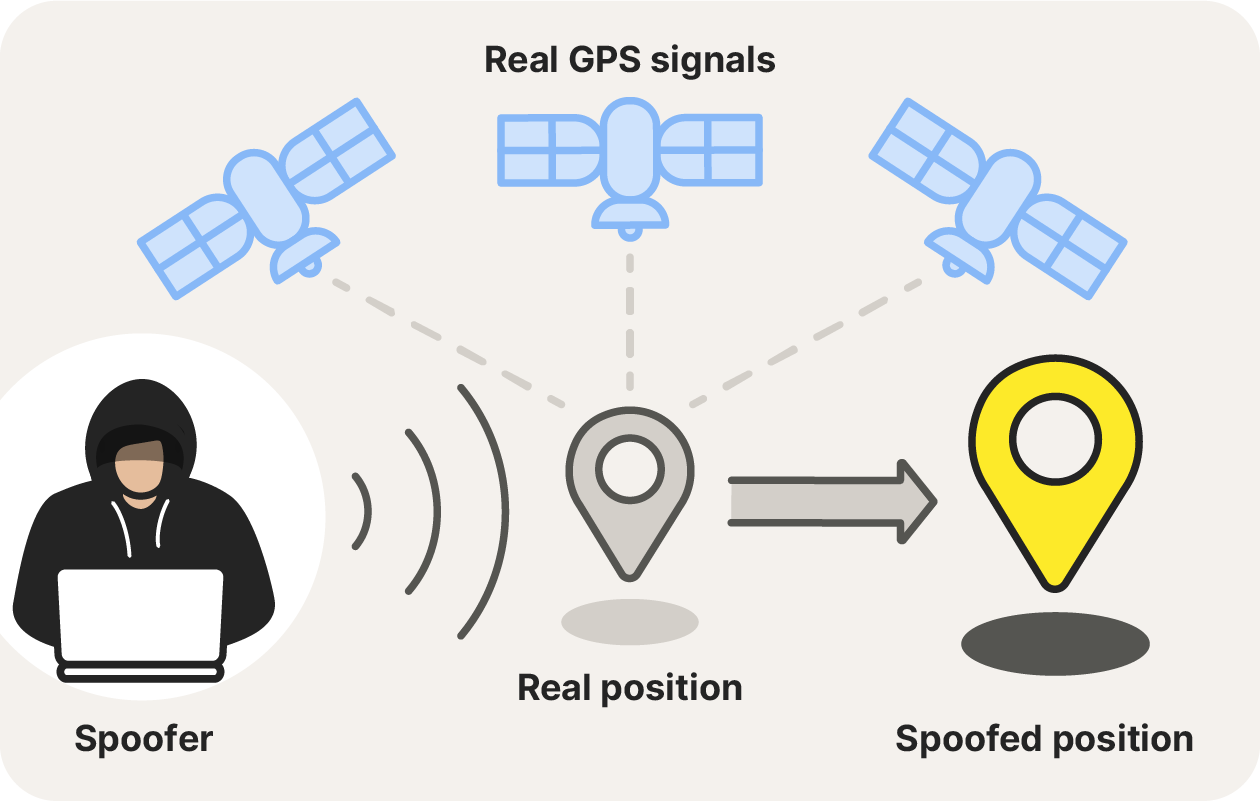
GPS spoofing is a sophisticated form of attack that goes beyond simply disrupting signals. It involves deliberately broadcasting false GPS signals designed to trick a receiver into calculating an incorrect position or time. This distinction is critical when discussing its impact on flight technology.
How Spoofing Differs from Jamming
It is important to differentiate GPS spoofing from GPS jamming, although both are forms of electronic interference.
- GPS Jamming: Jamming involves overwhelming the genuine, weak GPS signals with strong, random radio noise on the same frequencies. The goal of jamming is to deny a GPS receiver access to any GPS signal, causing it to lose its fix entirely. The receiver will typically report “GPS signal lost” or similar errors. While disruptive, a jammed system often fails gracefully, perhaps reverting to inertial navigation or a pre-programmed flight path until signals are restored.
- GPS Spoofing: Spoofing, conversely, does not aim to deny signals but to deceive. A spoofer generates false GPS-like signals that are carefully synchronized and structured to mimic legitimate satellite signals. These fake signals are typically broadcast at a slightly higher power than the genuine ones, allowing them to overpower and replace the real signals within the receiver’s processing. The receiver, unaware of the deception, continues to operate as if it’s receiving legitimate signals, but calculates an incorrect position or time, often subtly shifting from the true location or even causing it to jump to an entirely different, controlled location. This makes spoofing far more insidious, as the flight system may continue operating under false pretenses without immediately recognizing an attack.
The Technical Process of a Spoofing Attack
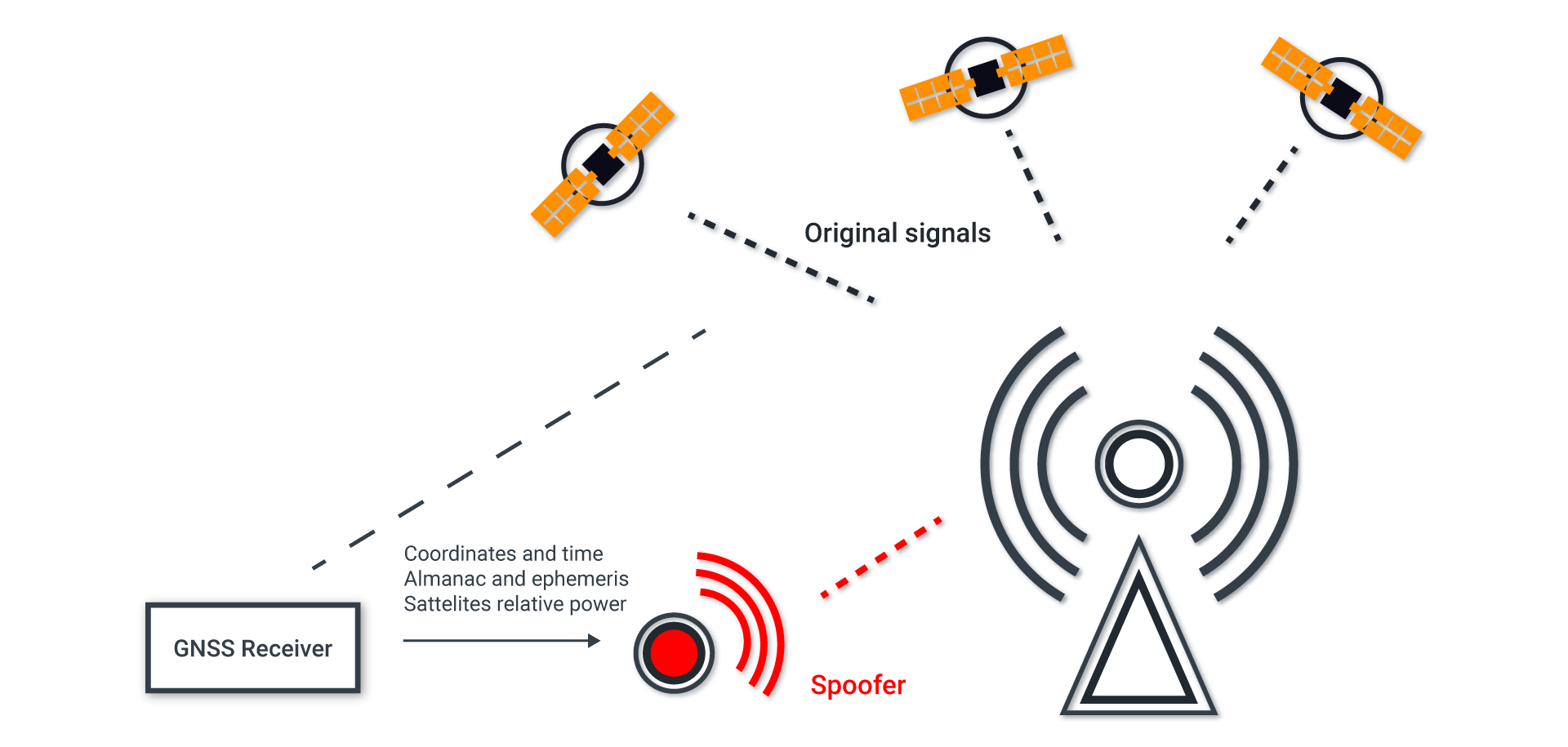
A successful GPS spoofing attack typically follows a sophisticated technical process:
- Signal Acquisition and Analysis: The spoofer first needs to acquire and analyze the real GPS signals in the target area. This is crucial for synchronizing the fake signals with the genuine ones, making the transition seamless for the receiver.
- Fabrication of False Signals: The spoofer then generates its own set of GPS-like signals. These signals contain fabricated PNT data (e.g., a fictitious location, velocity, or time offset) but are carefully crafted to mimic the structure, modulation, and timing characteristics of authentic GPS signals.
- Synchronization and Overpowering: The most challenging part is synchronizing the fake signals with the genuine ones and then gradually increasing their power. The spoofer broadcasts these false signals at a power level slightly higher than the real signals. As the fake signals become dominant, the target receiver’s tracking loops “lock” onto the stronger, fake signals, seamlessly transitioning from tracking real satellites to tracking the malicious spoofer.
- Controlled Drift or Jump: Once the receiver is tracking the spoofed signals, the attacker can manipulate the PNT data within those signals to guide the target system to a desired, incorrect location or to report an incorrect time. This can be a subtle, gradual drift over time, or an abrupt “jump” to a different location, depending on the attacker’s objectives and sophistication.
Types of GPS Spoofing Devices and Methods
GPS spoofing can range from rudimentary to highly advanced:
- Basic Rebroadcast Spoofers (Replay Attacks): These are the simplest, involving recording genuine GPS signals in one location and replaying them in another. While less sophisticated, they can still confuse receivers, making them believe they are at the recorded location.
- Software-Defined Radio (SDR) Spoofers: More advanced spoofers utilize SDR platforms. These allow for highly flexible generation of custom GPS signals with precise control over parameters like signal power, timing, and content. This method enables the creation of dynamic, sophisticated spoofing scenarios.
- Sophisticated Multi-Channel Spoofers: High-end spoofers mimic multiple GPS satellites simultaneously, enabling a more convincing deception. They can simulate a constellation of satellites, allowing for highly accurate control over the target’s reported position and motion.
- Targeted vs. Wide-Area Spoofing: Spoofing can be targeted at a single receiver or broadcast over a wider area, affecting multiple receivers. The latter requires more power and sophistication but can have broader implications.
The increasing availability of powerful and inexpensive SDRs has lowered the barrier to entry for performing GPS spoofing, making it a more accessible threat than ever before.
Ramifications and Real-World Impact on Flight Technology
The implications of successful GPS spoofing attacks on flight technology are profound, ranging from immediate operational disruptions to long-term safety and security concerns. The very systems designed to enhance safety and efficiency become vectors for risk when compromised.
Disruption of Navigation and Autonomous Systems
The most immediate impact of GPS spoofing is the corruption of navigation data. If an aircraft or UAV’s GPS receiver is spoofed:
- Incorrect Position Reporting: The system will believe it is at a location different from its true position. For piloted aircraft, this could lead to disorientation, flying off course, or entering restricted airspace unknowingly. For autonomous systems, this means deviating from pre-programmed flight paths, potentially into hazardous terrain, buildings, or other aircraft.
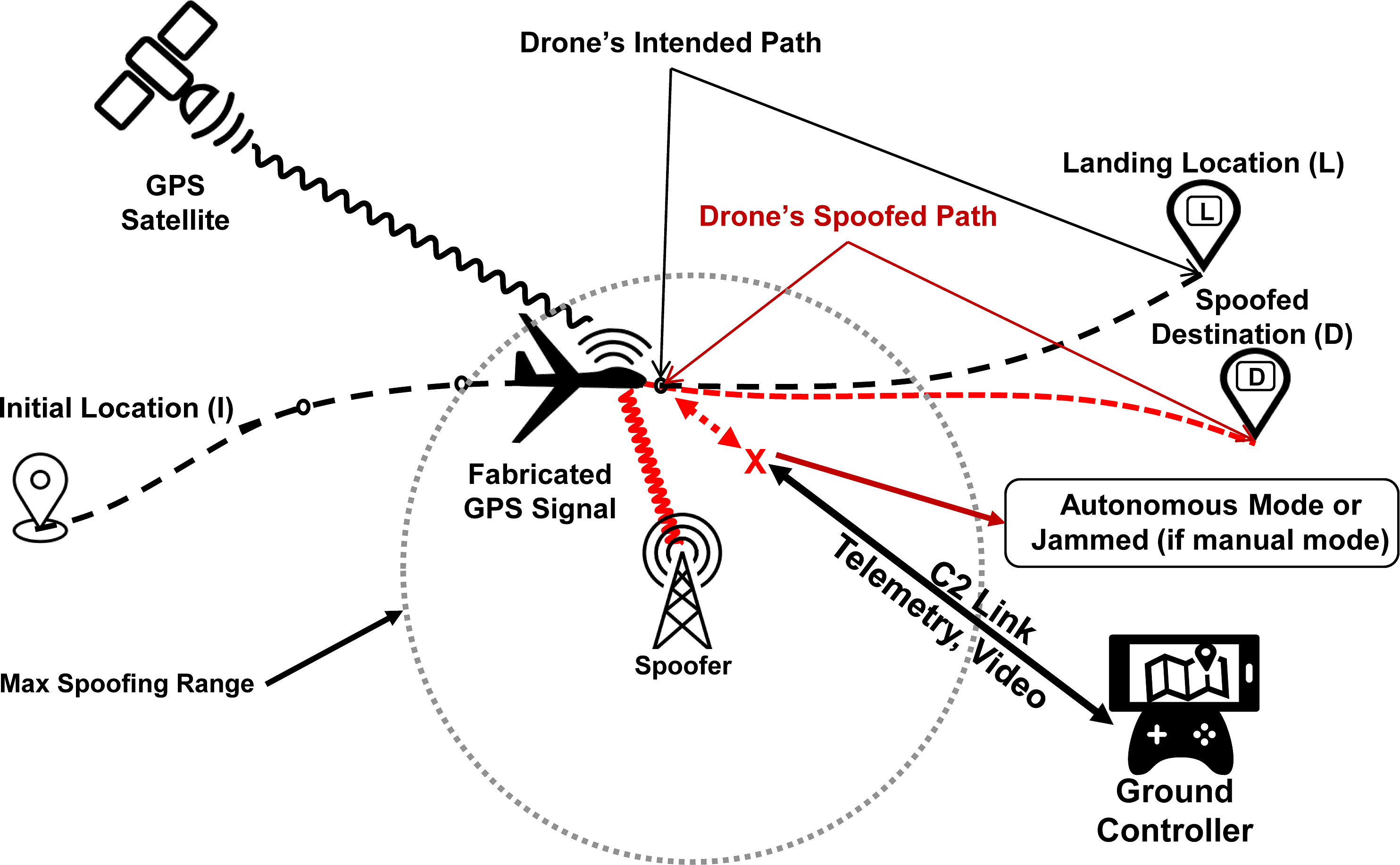
- Loss of Control for Autonomous Vehicles: Many modern UAVs heavily rely on GPS for autonomous flight, including waypoint navigation, “return-to-home” functions, and even stability control. If spoofed, the drone might attempt to fly to a non-existent “home” location, perform erratic maneuvers based on false coordinates, or even crash.
- Misleading Sensor Fusion: Flight systems often integrate GPS data with other sensors (e.g., inertial measurement units, barometric altimeters). If the GPS input is false, it can corrupt the entire sensor fusion process, leading to degraded performance or complete failure of integrated navigation systems.
- Incorrect Timing: Spoofing can also manipulate the timing information provided by GPS, which is critical for synchronized communication and sensor operation, potentially leading to system errors or failures.
Safety and Security Concerns for Aviation
The ramifications extend directly to the safety and security of flight:
- Collision Risk: An aircraft under a spoofing attack could be guided into the path of another aircraft, into terrain, or into obstacles. For example, a commercial airliner receiving false positional data could be instructed by air traffic control to a conflicting altitude or heading, leading to a mid-air collision.
- Controlled Flight Into Terrain (CFIT): By subtly altering altitude data, a spoofer could make an aircraft believe it is at a safe altitude when it is dangerously close to the ground, leading to a CFIT incident.
- Illegal Border Crossings and Restricted Airspace Violations: Spoofing can be used to surreptitiously guide an aircraft or drone across international borders or into highly sensitive, restricted airspace without the pilot’s or operator’s knowledge, creating serious geopolitical and security incidents.
- Weapon System Misguidance: Military flight systems, particularly those involving precision-guided munitions or reconnaissance drones, are highly vulnerable. Spoofing could lead to weapons striking incorrect targets or reconnaissance assets being diverted away from critical areas, with devastating military and political consequences.
- Targeting and Hijacking: In extreme scenarios, an advanced spoofing attack could theoretically be used to “hijack” an autonomous aircraft, rerouting it to a different destination or even causing it to land in an unauthorized location.
Economic and Geopolitical Implications
Beyond immediate operational safety, GPS spoofing carries significant broader consequences:
- Economic Disruption: Large-scale spoofing attacks on civilian air traffic could lead to widespread flight cancellations, air traffic control system overloads, and immense economic losses for airlines and related industries.
- Supply Chain Disruptions: As cargo and logistics increasingly rely on drone delivery and GPS-guided transport, spoofing could cripple supply chains, affecting everything from critical medical supplies to e-commerce.
- Erosion of Trust: Repeated incidents of GPS spoofing would erode public trust in autonomous flight technologies and the overall reliability of air navigation systems, hindering innovation and adoption.
- Geopolitical Instability: State-sponsored spoofing attacks, particularly against military or critical civilian infrastructure, are acts of electronic warfare that can escalate international tensions and contribute to regional instability. Documented incidents in the Black Sea and other conflict zones highlight this growing concern.
The insidious nature of spoofing, where a system appears to function normally while being fed false data, makes it a particularly challenging threat to detect and mitigate, demanding robust countermeasures across all layers of flight technology.
Countermeasures and Future Defenses
Given the critical role of GPS in flight technology and the severe risks posed by spoofing, significant efforts are underway to develop and deploy robust countermeasures. These defenses span technological advancements, architectural changes, and international cooperation.
Enhanced Receiver Design and Signal Authentication
The most direct approach to combating spoofing lies in making GPS receivers smarter and more resilient:
- Anti-Spoofing Algorithms: Modern receivers are being equipped with advanced algorithms designed to detect anomalies in incoming GPS signals. These algorithms can identify inconsistencies in signal power, arrival angles, Doppler shifts, and signal correlations that might indicate a spoofing attack. They can then issue warnings or even disregard suspicious signals.
- Cryptographic Authentication: Future GPS signals, such as the modernized M-code for military use and the upcoming civilian OS-NMA (Open Service Navigation Message Authentication), incorporate cryptographic authentication. This allows receivers to verify the authenticity of the navigation data, ensuring that the signals are indeed coming from legitimate satellites and not a spoofer. This is a crucial long-term solution.
- Multi-Frequency Receivers: Modern receivers often track signals on multiple GPS frequencies (L1, L2, L5). A spoofer attempting to manipulate all these frequencies simultaneously faces a much higher technical hurdle, making multi-frequency tracking a deterrent.
- Signal Power Monitoring: By continuously monitoring the strength of received GPS signals, receivers can detect sudden, unexplained increases in power, which could be indicative of a nearby spoofer attempting to overpower genuine signals.
Multi-Sensor Integration and Redundancy
Relying solely on GPS, even an authenticated one, is no longer considered sufficient for critical flight applications. Integrating data from multiple, diverse sensors provides redundancy and helps to detect and mitigate spoofing:
- Inertial Navigation Systems (INS): INS (utilizing accelerometers and gyroscopes) provides autonomous navigation capability independent of external signals. While INS drifts over time, it can bridge short GPS outages or identify discrepancies when GPS data is suspect. Combining GPS with INS (GPS/INS integration) is a standard practice, where GPS corrects INS drift, and INS smooths GPS data and provides continuity during signal loss or spoofing attempts.
- Barometric Altimeters: Provide altitude information independent of GPS.
- Radar Altimeters: Offer very precise height-above-ground measurements.
- Vision-Based Navigation: For UAVs, cameras can be used for visual odometry or feature tracking to determine position and motion relative to the ground, offering another layer of redundancy.
- Celestial Navigation and Star Trackers: For long-range or high-altitude flight, traditional methods of celestial navigation, modernized with digital star trackers, can provide an independent source of positional data.
- Terrain-Referenced Navigation (TRN): By comparing onboard terrain maps with real-time sensor data (e.g., radar or lidar), an aircraft can determine its position relative to known terrain features, offering an alternative when GPS is compromised.
By fusing data from these diverse sensors, an advanced flight system can identify inconsistencies. If the GPS suddenly reports a position that drastically contradicts the INS, altimeters, and visual data, the system can flag the GPS data as untrustworthy and potentially ignore it or switch to an alternative navigation mode.
Regulatory Frameworks and International Cooperation
Technological solutions must be complemented by legal and regulatory efforts:
- Legislation and Enforcement: Stronger laws against the possession and use of GPS spoofing devices are crucial, alongside robust enforcement mechanisms.
- International Standards: Collaboration among international aviation bodies (e.g., ICAO) and satellite navigation providers is essential to develop common standards for anti-spoofing technologies and threat response protocols.
- Information Sharing: Establishing secure channels for sharing threat intelligence and incident reports among nations and industry stakeholders can help to identify patterns of attack and accelerate the development of effective defenses.
The Role of Alternative Navigation Systems
While GPS remains dominant, exploring and investing in alternative PNT systems provides a crucial hedge against its vulnerabilities:
- eLoran: Enhanced Long-Range Navigation (eLoran) is a ground-based radionavigation system that operates on different frequencies and principles than GPS, making it resistant to GPS jamming and spoofing. It can provide a crucial backup PNT source, particularly for maritime and aviation applications.
- Galileo, GLONASS, BeiDou: Utilizing signals from multiple Global Navigation Satellite Systems (GNSS) – such as Europe’s Galileo, Russia’s GLONASS, and China’s BeiDou – provides greater resilience. A receiver tracking multiple constellations is much harder to spoof comprehensively, as an attacker would need to spoof all systems simultaneously. This multi-GNSS approach significantly enhances the robustness of PNT.
In conclusion, GPS spoofing represents a serious and evolving threat to the precision, safety, and autonomy of modern flight technology. While the problem is complex, a multi-faceted approach combining advanced receiver technology, robust multi-sensor integration, stringent regulatory measures, and investment in alternative navigation systems offers the most promising path forward to safeguarding our skies from this insidious form of electronic warfare. The continuous innovation in these areas is not just about enhancing technology; it’s about ensuring the ongoing safety and reliability of air travel and autonomous flight for decades to come.
