In an increasingly interconnected digital world, where individuals and organizations interact with a multitude of online services, applications, and platforms daily, managing identity and access efficiently and securely has become paramount. The traditional model of creating a unique username and password for every single service is not only cumbersome but also a significant security vulnerability. Enter federated identity – a transformative technological framework designed to streamline and secure access across disparate systems, enhancing user experience while fortifying security postures. At its core, federfederated identity is about establishing a trusted relationship between multiple independent organizations or domains, allowing a user’s identity to be verified and asserted by one system (an Identity Provider) and accepted by another (a Service Provider) without the need for redundant credentials. It represents a paradigm shift from siloed identity management to a distributed, yet cohesive, approach, laying the foundation for seamless digital interactions across the vast landscape of modern technology and innovation.
The Core Concept: Trust and Interoperability
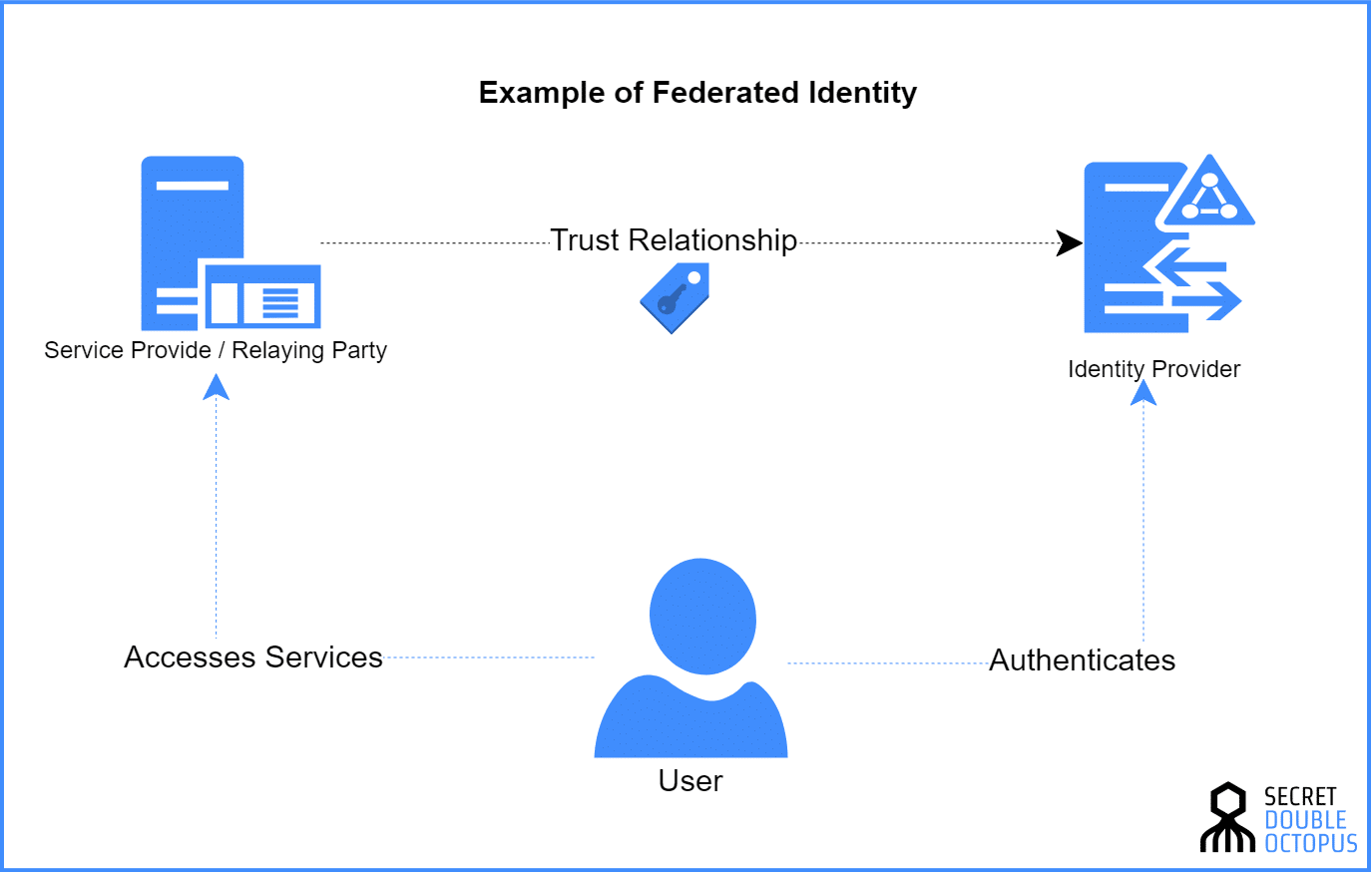
Federated identity systems are built upon a fundamental principle of trust, enabling different entities to confidently exchange identity attributes and authentication decisions. This trust is what allows a user to log in once with a single set of credentials and gain access to multiple services without re-authenticating. The architecture revolves around distinct roles and standardized communication protocols that facilitate this interoperability.
Understanding Identity Providers (IdPs) and Service Providers (SPs)
At the heart of any federated identity system are two primary actors: the Identity Provider (IdP) and the Service Provider (SP). An Identity Provider (IdP) is a system that creates, maintains, and manages identity information for principals (users) and provides authentication services. When a user attempts to access a service, the IdP is responsible for verifying the user’s identity – typically through a username, password, multi-factor authentication, or other methods. Once authenticated, the IdP asserts the user’s identity to other services. Examples include corporate directories like Active Directory Federation Services (AD FS), cloud identity services like Okta or Azure AD, or even consumer identity services like Google or Facebook for social logins.
A Service Provider (SP), on the other hand, is the application or service that a user wishes to access. Instead of managing its own user identities and authentication mechanisms, the SP trusts an IdP to perform these tasks. When a user tries to access an SP, they are redirected to the IdP for authentication. Upon successful verification, the IdP sends an authentication assertion back to the SP, allowing the user access. Websites, SaaS applications, and internal corporate tools frequently act as SPs.
The Trust Relationship
The successful operation of a federated identity system hinges on a meticulously established trust relationship between the IdP and the SP. This trust is typically formed through a pre-agreed-upon exchange of digital certificates and configuration metadata. The SP explicitly trusts the IdP to accurately authenticate users and provide reliable identity attributes. When an IdP asserts that a user is who they claim to be, the SP accepts this assertion as authoritative. This eliminates the need for the SP to store or verify user credentials directly, significantly reducing its security footprint and administrative burden. The establishment of this trust is not merely a handshake; it involves cryptographic assurances and adherence to agreed-upon standards, ensuring that identity information exchanged is both authentic and tamper-proof.
Single Sign-On (SSO) as a Primary Benefit
One of the most immediate and tangible benefits of federated identity is the enablement of Single Sign-On (SSO). SSO allows a user to authenticate once with their identity provider and gain access to multiple federated service providers without having to re-enter their credentials. This dramatically improves the user experience by eliminating password fatigue and the frustration of managing numerous logins. For organizations, SSO streamlines access to internal and external applications, boosting productivity and reducing the number of helpdesk calls related to password resets. It’s a cornerstone feature that underpins the value proposition of federated identity, making complex digital ecosystems feel seamless and intuitive to navigate.
Key Protocols and Standards Driving Federation
The concept of federated identity is brought to life through a suite of standardized protocols that define how identity information is exchanged securely and reliably between IdPs and SPs. These standards ensure interoperability, allowing diverse systems from different vendors to communicate effectively.
Security Assertion Markup Language (SAML)
Security Assertion Markup Language (SAML) is an XML-based open standard for exchanging authentication and authorization data between an IdP and an SP. Developed by the OASIS Security Services Technical Committee, SAML has been a cornerstone of enterprise federated identity for over two decades. It defines three key roles: the principal (user), the IdP, and the SP. The typical SAML flow involves the user attempting to access an SP, being redirected to the IdP for authentication, and upon successful login, the IdP generating a digitally signed SAML assertion (an XML document containing identity and authentication information) which is then sent back to the SP. The SP validates this assertion and grants access. SAML is particularly prevalent in business-to-business (B2B) scenarios and enterprise environments, where strong security and a clear separation of concerns are critical.
OAuth 2.0 and OpenID Connect (OIDC)
While SAML primarily focuses on authentication (who the user is), OAuth 2.0 is an authorization framework that enables an application to obtain limited access to a user’s account on an HTTP service (like Google, Facebook, etc.), without giving the application the user’s password. It defines how a user can grant delegated access to their resources (e.g., photos, contacts) on one service to another service. OAuth 2.0 is widely used in consumer-facing applications, mobile apps, and APIs.
Building on top of OAuth 2.0, OpenID Connect (OIDC) is an identity layer that enables clients to verify the identity of an end-user based on the authentication performed by an authorization server, as well as to obtain basic profile information about the end-user in an interoperable and REST-like manner. Essentially, OIDC adds an authentication layer to OAuth 2.0, providing identity services in addition to authorization. It is often described as “SAML for the modern web” due to its simplicity, RESTful nature, and widespread adoption in web and mobile applications for user authentication.
Lightweight Directory Access Protocol (LDAP) and SCIM
While not strictly federated identity protocols themselves, Lightweight Directory Access Protocol (LDAP) and System for Cross-domain Identity Management (SCIM) play crucial supporting roles in many identity management architectures, including those that incorporate federation. LDAP is an open, vendor-neutral, industry-standard application protocol for accessing and maintaining distributed directory information services. It is commonly used to store user identities within an organization, which an IdP might then leverage for authentication. SCIM, on the other hand, is a RESTful protocol designed to simplify user provisioning and de-provisioning across multiple applications. It automates the creation, updating, and deletion of user accounts and groups, allowing for efficient management of user lifecycles across federated systems. By integrating SCIM, organizations can ensure that user identities and attributes are consistently synchronized between the IdP and various SPs.
Advantages and Benefits of Federated Identity
The adoption of federated identity brings a cascade of benefits, revolutionizing how users access digital services and how organizations manage their digital presence. These advantages span user experience, security, administration, and organizational agility.
Enhanced User Experience and Productivity
Perhaps the most immediately noticeable benefit for end-users is the significant improvement in their digital experience. With Single Sign-On (SSO) enabled by federated identity, users no longer need to remember dozens of complex passwords or repeatedly log in to different applications. This drastically reduces “password fatigue” and the friction associated with accessing multiple services, leading to a smoother, more efficient workflow. Less time spent on authentication means more time focused on productive tasks, directly boosting overall productivity for individuals and teams.
Improved Security Posture
Federated identity inherently strengthens an organization’s security posture. By centralizing authentication to a trusted IdP, organizations can enforce consistent, robust security policies, including strong password requirements, multi-factor authentication (MFA), and adaptive authentication techniques, across all connected applications. This dramatically reduces the attack surface, as credentials are not scattered across numerous SPs. If an IdP is compromised, the impact is contained and can be addressed centrally. Furthermore, federated systems facilitate quicker de-provisioning of access for departing employees, mitigating insider threat risks and ensuring that access is revoked across all services simultaneously.
Simplified Administration and Compliance
From an administrative perspective, federated identity offers substantial efficiencies. IT departments can manage user identities and access rights from a single point of control, simplifying user provisioning (creating accounts), de-provisioning (revoking access), and attribute management. This centralized management reduces manual errors and administrative overhead. For compliance, federated identity provides a clear audit trail of who accessed what and when, across various services, which is invaluable for meeting regulatory requirements such as GDPR, HIPAA, or SOC 2. The ability to demonstrate consistent identity governance is a significant boon for regulatory adherence.
Scalability and Flexibility
As organizations grow and adopt more cloud services, SaaS applications, and even IoT devices, the number of distinct identity silos can quickly become unmanageable. Federated identity provides a scalable solution, allowing new services to be seamlessly integrated by simply establishing a trust relationship with the existing IdP. This flexibility supports rapid expansion and adaptation to evolving business needs without rebuilding identity infrastructure for each new application. It enables organizations to embrace best-of-breed services and connect with external partners or customers effortlessly, fostering a more agile and interconnected ecosystem.
Challenges and Considerations in Implementation
While the benefits of federated identity are compelling, its implementation is not without its complexities and challenges. Organizations must carefully consider several factors to ensure a successful deployment that maximizes advantages while mitigating potential risks.
Interoperability and Standard Compliance
One of the primary challenges lies in ensuring true interoperability across diverse systems and vendors. Although protocols like SAML and OIDC are standards, their implementations can sometimes vary, leading to compatibility issues. Organizations must ensure that their chosen IdP and SPs fully adhere to the specified standards and are rigorously tested for interoperability. Customizations or non-standard interpretations by vendors can complicate integration efforts, requiring additional development or configuration. A thorough understanding of the specific profiles and extensions of the chosen protocols is essential to avoid integration headaches.
Security Risks and Data Privacy
While federated identity generally enhances overall security, it also introduces a centralized point of failure: the Identity Provider. If the IdP is compromised, it could potentially grant unauthorized access to all connected SPs. Therefore, the security of the IdP itself, including its infrastructure, authentication mechanisms (e.g., strong MFA), and protection against sophisticated attacks, must be paramount. Furthermore, data privacy is a significant concern. Organizations must ensure that identity attributes shared between IdPs and SPs are minimal, necessary, and compliant with relevant data protection regulations like GDPR, CCPA, or regional equivalents. Secure attribute release policies and robust encryption for data in transit and at rest are crucial.
Complexity of Initial Setup
The initial setup of a federated identity system can be complex and resource-intensive. It involves meticulous planning, configuration of trust relationships, certificate management, attribute mapping, and integration with existing identity stores (e.g., LDAP directories). Organizations need skilled personnel or expert consultants to design and implement the architecture correctly. The process often requires extensive testing to ensure that authentication flows, attribute assertions, and authorization decisions function as expected across all federated entities. The upfront investment in time and expertise can be substantial, though it typically pays off in long-term operational efficiencies.
Vendor Lock-in and Customization
Choosing an Identity Provider vendor involves a significant commitment, and organizations can sometimes face the risk of vendor lock-in. While open standards aim to mitigate this, the specific features, management interfaces, and proprietary extensions of a given IdP can make it difficult to switch providers later. Additionally, while federated identity solutions are designed for broad applicability, specific organizational needs might require customization. Balancing the benefits of standardized, off-the-shelf solutions with the necessity for tailored configurations can be a delicate act, requiring careful evaluation of vendor capabilities and flexibility.
Federated Identity in the Modern Tech Landscape
Federated identity is not merely a theoretical construct; it is a vital enabler of many modern technological paradigms, continually evolving to meet the demands of an increasingly complex and distributed digital world.
Cloud Computing and SaaS Integration
The rapid adoption of cloud computing and Software-as-a-Service (SaaS) applications has made federated identity an indispensable technology. Organizations routinely subscribe to dozens, if not hundreds, of cloud-based services (e.g., Salesforce, Microsoft 365, Slack, Workday). Without federated identity, each of these would require separate user accounts and authentication processes. Federated identity allows enterprises to leverage their existing corporate directories (like Active Directory) as the IdP, extending a single, trusted login experience to all cloud applications. This simplifies cloud adoption, improves security by centralizing control, and enhances the user experience for employees accessing mission-critical tools from anywhere.
Internet of Things (IoT) and Edge Computing
As the Internet of Things (IoT) expands to billions of connected devices, and Edge Computing pushes processing closer to data sources, managing identities for both human users and autonomous devices becomes incredibly complex. Federated identity principles are crucial for securing these vast and distributed ecosystems. Imagine smart city infrastructure, industrial IoT sensors, or autonomous vehicles all needing to authenticate and authorize access to various services and data streams. Federated identity provides a framework for these devices to securely establish their identities, communicate with cloud platforms, and interact with other devices in a trusted manner, enabling scalable and secure IoT deployments.
The Future of Identity: Decentralized Identity and Verifiable Credentials
Looking ahead, the field of identity is continuously innovating. Emerging concepts like Decentralized Identity (DID) and Verifiable Credentials (VCs) promise to reshape the future of federated identity. Decentralized Identity aims to give individuals more control over their own digital identities, allowing them to manage and present verifiable claims (credentials) directly, rather than relying solely on centralized IdPs. Verifiable Credentials, often built on blockchain technology, are cryptographically secured, tamper-proof digital proofs of identity attributes (e.g., a university degree, a driver’s license). While still in nascent stages, these innovations could augment or transform traditional federated models, offering enhanced privacy, security, and user autonomy, moving towards a more user-centric approach to identity in the digital age.
Conclusion
Federated identity stands as a pivotal advancement in the realm of Tech & Innovation, fundamentally reshaping how individuals and organizations interact with the digital landscape. By establishing robust trust relationships between disparate systems, it delivers a powerful combination of enhanced security, simplified administration, and unparalleled user convenience through Single Sign-On. While implementation requires careful planning and addresses specific challenges related to interoperability and security, the strategic advantages it offers in today’s cloud-centric, interconnected world are undeniable. As technology continues its relentless march forward, encompassing cloud computing, the vast expanse of the Internet of Things, and the promising horizons of decentralized identity, federated identity will remain a cornerstone. It will continue to evolve, adapting to new paradigms and cementing its role as an indispensable framework for secure, efficient, and seamless digital experiences, driving innovation and collaboration across the global tech ecosystem.
