In the vast and rapidly evolving world of technology, from the intricate operations of autonomous drones to the sophisticated algorithms powering artificial intelligence, a fundamental building block underpins much of our digital experience: the executable file. Often encountered as an .exe file extension on Windows systems, this seemingly simple file type represents the compiled instructions that a computer’s processor can directly understand and execute. It is the tangible manifestation of software, the command center that brings programs to life, allowing users to interact with applications, operate complex machinery, and drive innovation forward. Understanding what an .exe file is, how it functions, and its role in the broader technological landscape is crucial for anyone seeking to grasp the mechanics behind the digital age. This article delves into the core nature of executable files, exploring their structure, functionality, security implications, and enduring relevance in an era defined by continuous technological advancement.
The Core Mechanics of Executable Files: From Code to Action
At its heart, an executable file is a program in a format that a computer’s operating system (OS) can load into memory and run. While the .exe extension is specific to Windows, the concept of an executable file is universal across all computing platforms, albeit with different file formats and extensions (e.g., ELF on Linux, Mach-O on macOS). These files are the culmination of a complex development process, transforming human-readable source code into machine-executable instructions.
Definition and Purpose
The term “EXE” is an abbreviation for “executable.” Its primary purpose is to contain a sequence of instructions that, when processed by a computer’s central processing unit (CPU), perform a specific task. This task can range from launching a simple calculator application to orchestrating a sophisticated drone flight control system or running a complex simulation model for a new AI algorithm. Essentially, an .exe file is the entry point for most software applications on Windows, providing the OS with everything it needs to initiate and manage a program’s execution. Without executables, the rich software environment we rely on daily—from productivity suites to cutting-edge research tools—would simply not exist. They bridge the gap between abstract programming logic and concrete machine operations, translating human intent into digital action.
The Anatomy of an .EXE File
While a user might perceive an .exe file as a single entity, it is, in fact, a structured collection of components designed to facilitate execution. The most common format for .exe files on Windows is the Portable Executable (PE) format. This structure is not just for programs; it’s also used for Dynamic Link Libraries (DLLs) and other system files.
A typical PE file includes several key sections:
- DOS Header: A legacy header that allows the file to run a small stub program under MS-DOS, typically displaying a message like “This program cannot be run in DOS mode.”
- PE Header: Contains crucial information for the Windows loader, such as the target machine architecture (32-bit or 64-bit), the entry point address (where the program execution begins), and the number of sections.
- Section Headers: Define the characteristics and location of the various data sections within the file.
- Code Section (.text): This is where the actual machine instructions (the compiled program logic) reside. When the program runs, these instructions are loaded into memory and executed by the CPU.
- Data Sections (.data, .rdata): These sections hold initialized global and static variables, read-only data (like strings and constants), and uninitialized data.
- Resource Section (.rsrc): Contains embedded resources such as icons, cursors, images, menus, and version information, which are part of the application’s user interface or metadata.
- Import/Export Sections (.idata, .edata): These sections list functions that the program imports from other DLLs (like system libraries) or functions that it exports for other programs to use. This modularity is a cornerstone of modern software development, preventing code duplication and promoting reuse.
This intricate structure ensures that the operating system can correctly load the program, allocate necessary memory, resolve dependencies, and begin execution efficiently, demonstrating a sophisticated design that has enabled decades of software innovation.
The Role of .EXE Files in Software Ecosystems and Innovation
The ubiquitous presence of .exe files underscores their foundational importance across diverse software ecosystems. They are not merely containers for code but active participants in how applications interact with operating systems, how software is distributed, and how new technologies are brought to fruition. Their function extends far beyond launching a simple application; they are the bedrock upon which complex systems, including those driving cutting-edge innovation, are built.
Operating System Interaction and Process Management
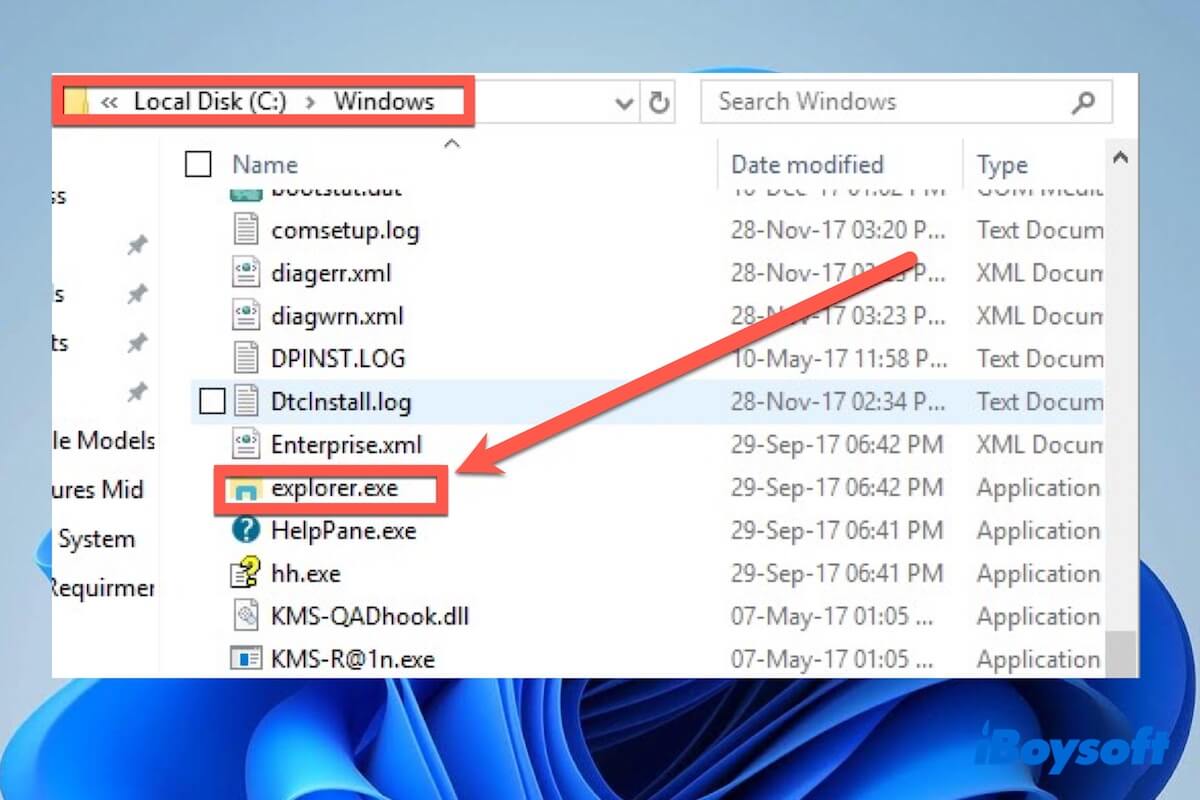
When a user double-clicks an .exe file, or when a system service initiates one, a complex sequence of events unfolds. The operating system’s loader reads the PE header, maps the file’s sections into the process’s virtual address space, and resolves any imported functions from other libraries. It then sets up the necessary environment for the program—allocating memory, creating threads, and establishing communication channels. The CPU’s instruction pointer is then directed to the program’s entry point, and execution begins.
This seamless interaction between the .exe file and the OS is crucial for multitasking, resource allocation, and maintaining system stability. Each running .exe file typically corresponds to a distinct process, managed independently by the OS. This isolation is vital for security and prevents one errant program from crashing the entire system. In advanced technological domains, such as drone flight control systems or robotic automation, multiple .exe files or their conceptual equivalents might run concurrently, each managing specific tasks (e.g., sensor data processing, motor control, navigation algorithms), all coordinated by the underlying OS. The efficiency and reliability of this interaction are paramount for the performance and safety of these innovative systems.
Application Delivery, Installation, and Updates
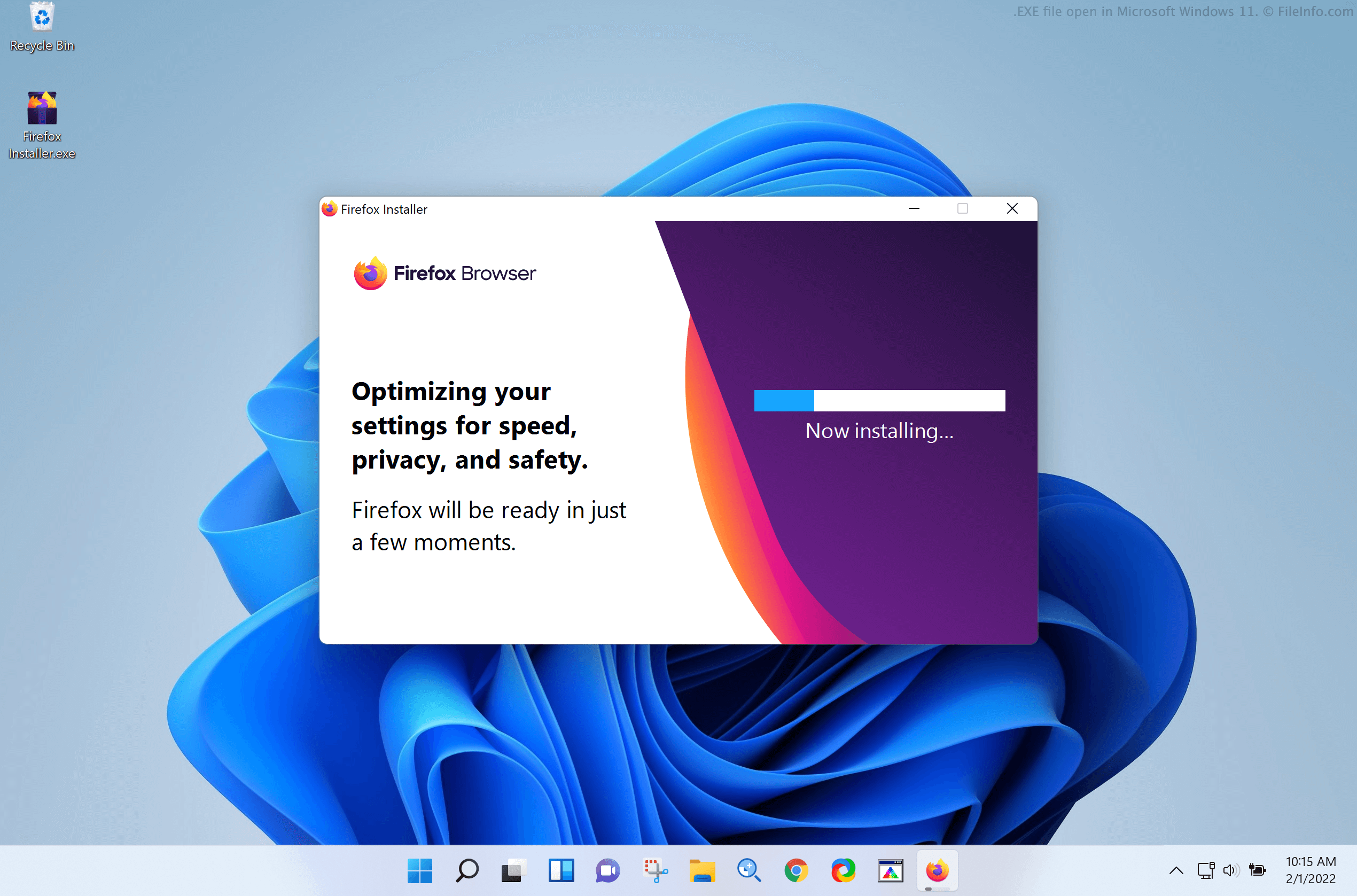
Executable files are the primary medium for software distribution and installation on Windows platforms. When you download an application, you often receive an .exe file, which might be the program itself or an installer that extracts and sets up the application’s components. These installers can be sophisticated packages that handle dependencies, create shortcuts, modify system registries, and ensure the software is correctly integrated into the user’s environment.
The ability to package complex software into a self-contained, deployable .exe file greatly simplifies software delivery. This principle extends to cloud-based services and enterprise applications, where executables might be part of server deployments or automated update mechanisms. For innovative tech companies, efficient software delivery through .exe files (or similar executable formats) means faster deployment of new features, security patches, and entirely new products to market, accelerating the pace of technological adoption and iteration. This ease of distribution fosters a dynamic environment where developers can rapidly disseminate their creations, from new drone firmware updates to revolutionary AI models packaged for local execution.
Driving Specialized Tech: Beyond the Desktop
While often associated with desktop applications, the principles embodied by .exe files are fundamental to a much broader spectrum of technology. In embedded systems, such as those found in drones, IoT devices, or industrial control systems, the “firmware” that dictates their behavior is essentially an executable program designed for specific hardware. These specialized executables, though not always carrying the .exe extension, perform functions like processing sensor data, controlling actuators, managing communication protocols, and executing autonomous decision-making algorithms.
Furthermore, in the realm of advanced tech and innovation, .exe files play a critical role in developing and deploying tools for:
- Scientific Simulation and Modeling: Executables run complex mathematical models for climate research, fluid dynamics, material science, and pharmaceutical development.
- Artificial Intelligence and Machine Learning: While often developed in scripting languages, the core inference engines, data processing tools, and custom hardware drivers for AI accelerators are frequently compiled into executables for performance.
- Robotics and Autonomous Systems: The operational logic, path planning algorithms, and low-level control loops for robots and drones are all compiled into executable code.
- Cybersecurity Tools: Antivirus software, intrusion detection systems, and vulnerability scanners are robust applications delivered as executables.
Thus, the humble .exe file is not just a relic of desktop computing but a living, evolving component at the heart of nearly every technological innovation, providing the raw power and instruction sets for machines to perform their designed tasks.
Security, Risks, and Trust in the Executable World
The power and versatility of executable files come with inherent risks. Because they directly command a computer’s processor, .exe files are prime targets for malicious actors seeking to exploit systems. Understanding these security implications and the measures designed to mitigate them is paramount in an increasingly interconnected and threat-laden digital landscape. Ensuring the integrity and trustworthiness of executables is a critical aspect of safeguarding technological infrastructure and user data.
Malware and Viruses: Exploiting Executable Trust
The most significant security concern associated with .exe files is their potential to harbor malware. Viruses, worms, trojans, ransomware, and spyware are frequently distributed as or embedded within executable files. A malicious .exe file, once executed, can perform a wide range of harmful actions:
- Data Theft: Stealing personal information, financial data, or intellectual property.
- System Damage: Corrupting files, deleting data, or rendering the operating system unusable.
- Remote Control: Allowing attackers to gain unauthorized access and control over the infected machine.
- Botnet Participation: Turning the compromised computer into a “bot” to participate in distributed denial-of-service (DDoS) attacks or spam campaigns.
- Ransomware Attacks: Encrypting files and demanding payment for their decryption.
The inherent trust users place in executable files, often by simply double-clicking them, makes them a potent vector for cyberattacks. This risk is amplified in rapidly evolving tech environments where new software and updates are constantly being deployed, making thorough vetting challenging.
Digital Signatures and Code Integrity
To combat the threat of malicious executables, robust security mechanisms have been developed. One of the most important is digital signing. A digital signature, applied to an .exe file by its developer, uses cryptographic techniques to verify two crucial aspects:
- Authenticity: It confirms the identity of the software publisher.
- Integrity: It guarantees that the file has not been tampered with or altered since it was signed.
When a user attempts to run a digitally signed .exe file, the operating system can verify the signature. If the signature is valid and belongs to a trusted certificate authority, the user can have a higher degree of confidence in the file’s legitimacy. Conversely, an unsigned executable or one with a corrupted signature should immediately raise a red flag. This mechanism is crucial for establishing trust in the software supply chain, especially for critical applications in tech innovation, such as those governing drone operations or sensitive data analytics.
Best Practices for Users and Developers
Navigating the executable world securely requires diligence from both developers and end-users:
- For Users:
- Source Verification: Only download executables from trusted, official sources. Avoid unknown websites, email attachments, or suspicious links.
- Antivirus/Anti-malware Software: Keep security software updated and perform regular scans.
- User Account Control (UAC): Pay attention to UAC prompts on Windows, as they indicate a program is attempting to make system-level changes.
- Check Digital Signatures: Before running an unfamiliar executable, check its digital signature through file properties.
- Sandbox Environments: For highly suspicious files, consider running them in a virtual machine or sandbox environment to prevent harm to the main system.
- For Developers:
- Code Signing: Always digitally sign your executables with a trusted certificate.
- Secure Coding Practices: Follow secure coding guidelines to prevent vulnerabilities that could be exploited by attackers.
- Vulnerability Testing: Regularly test applications for security flaws before deployment.
- Supply Chain Security: Ensure that all components and libraries used in development are trustworthy and free of known vulnerabilities.
- Patching and Updates: Provide timely security updates for applications to address newly discovered threats.
By adhering to these practices, the risks associated with .exe files can be significantly mitigated, fostering a safer environment for technological advancement and user interaction.
Evolution and Enduring Relevance in Tech Innovation
Despite the rise of cloud computing, web applications, and containerization, the fundamental concept of an executable file, particularly the .exe format on Windows, maintains its critical importance in the tech landscape. While the mechanisms of software delivery and execution have evolved, the need for compiled, machine-native instructions remains a cornerstone for performance, security, and specialized applications. The role of executables continues to adapt, proving their enduring relevance in an era of rapid technological innovation.
Cross-Platform Paradigms and Abstraction Layers
Modern software development often emphasizes cross-platform compatibility, leading to technologies that abstract away the underlying operating system and its native executable formats.
- Virtual Machines (VMs): Allow an entire operating system to run within another, executing its native executables (e.g., a Windows
.exerunning within a Windows VM on a Linux host). - Containers (e.g., Docker): Package applications and their dependencies into isolated units, ensuring consistent execution across different environments. While the application inside the container might be an
.exe(or ELF/Mach-O), the container runtime manages its execution more abstractly. - Web Assembly (Wasm): A binary instruction format for a stack-based virtual machine, designed as a portable compilation target for high-level languages like C/C++/Rust, enabling client-side web applications to run at near-native speed. While not an
.exeitself, it serves a similar purpose in its execution environment. - Managed Runtimes (e.g., Java Virtual Machine, .NET Common Language Runtime): These platforms execute bytecode, which is then translated or compiled just-in-time (JIT) into native machine instructions during runtime. The runtime itself is often a native executable.
These innovations do not replace .exe files but rather build upon them or offer alternative execution models for specific use cases, often relying on native executables for their foundational infrastructure. For instance, the Docker daemon, the JVM, or the .NET runtime are themselves native executables tailored for their respective operating systems, demonstrating that the need for a direct interface with the hardware persists.
Executables as Enablers for Cutting-Edge Technology
In the most advanced sectors of tech and innovation, .exe files and their counterparts are not just present; they are often the preferred format for achieving peak performance and control.
- High-Performance Computing (HPC): Supercomputers running complex scientific simulations or large-scale data analysis rely heavily on highly optimized, compiled executables to squeeze every bit of performance from the hardware.
- AI/ML Inferencing: While training models often happens on specialized hardware and cloud platforms, deploying these models for real-time inference on edge devices (like autonomous vehicles or smart cameras) frequently involves highly optimized executables that can run efficiently on limited resources.
- Gaming and Real-Time Graphics: The demanding performance requirements of modern video games necessitate native executables that can directly leverage GPU acceleration and low-level system resources.
- Aerospace and Defense: Critical systems in aircraft, spacecraft, and military technology are typically controlled by rigorously tested and highly reliable compiled executables.
- Industrial Automation and IoT: The firmware and control logic for factory robots, smart sensors, and industrial equipment are bespoke executables designed for precision and reliability.
In these domains, the ability of an .exe file to execute instructions directly on the CPU, with minimal overhead, is indispensable. It provides the speed, deterministic behavior, and direct hardware access that are critical for innovative applications where milliseconds matter.
The Enduring Legacy and Future Outlook
The .exe file, in its essence, represents the ultimate compiled form of a program, ready for execution. While the surrounding ecosystem evolves with new programming languages, cloud architectures, and development paradigms, the core need for machine-executable instructions remains. Future innovations might introduce new ways to package, distribute, and execute code, but the underlying principle of a direct, hardware-level set of instructions will persist. Whether it’s the brain of a sophisticated drone navigating complex airspace, the engine of an AI model making real-time decisions, or the core logic of a new scientific instrument, the concept embodied by the .exe file will continue to be a vital component in driving the next wave of technological breakthroughs. Its legacy is not just in its format, but in its fundamental role as the key that unlocks the power of computation, transforming abstract ideas into functional realities across the entire spectrum of tech and innovation.
