While the title “What is Error Code 268 in Roblox?” might initially suggest a deep dive into video game troubleshooting, a closer examination of the provided website topics reveals a fascinating connection to 6. Tech & Innovation. Specifically, error codes and their resolution often involve understanding complex digital systems, akin to troubleshooting advanced technological implementations in fields like autonomous flight, mapping, and remote sensing. This article will explore Error Code 268 within the framework of understanding digital system failures, their underlying causes, and the systematic approaches to their resolution, drawing parallels to the diagnostic processes employed in cutting-edge tech sectors.
Understanding Digital System Anomalies
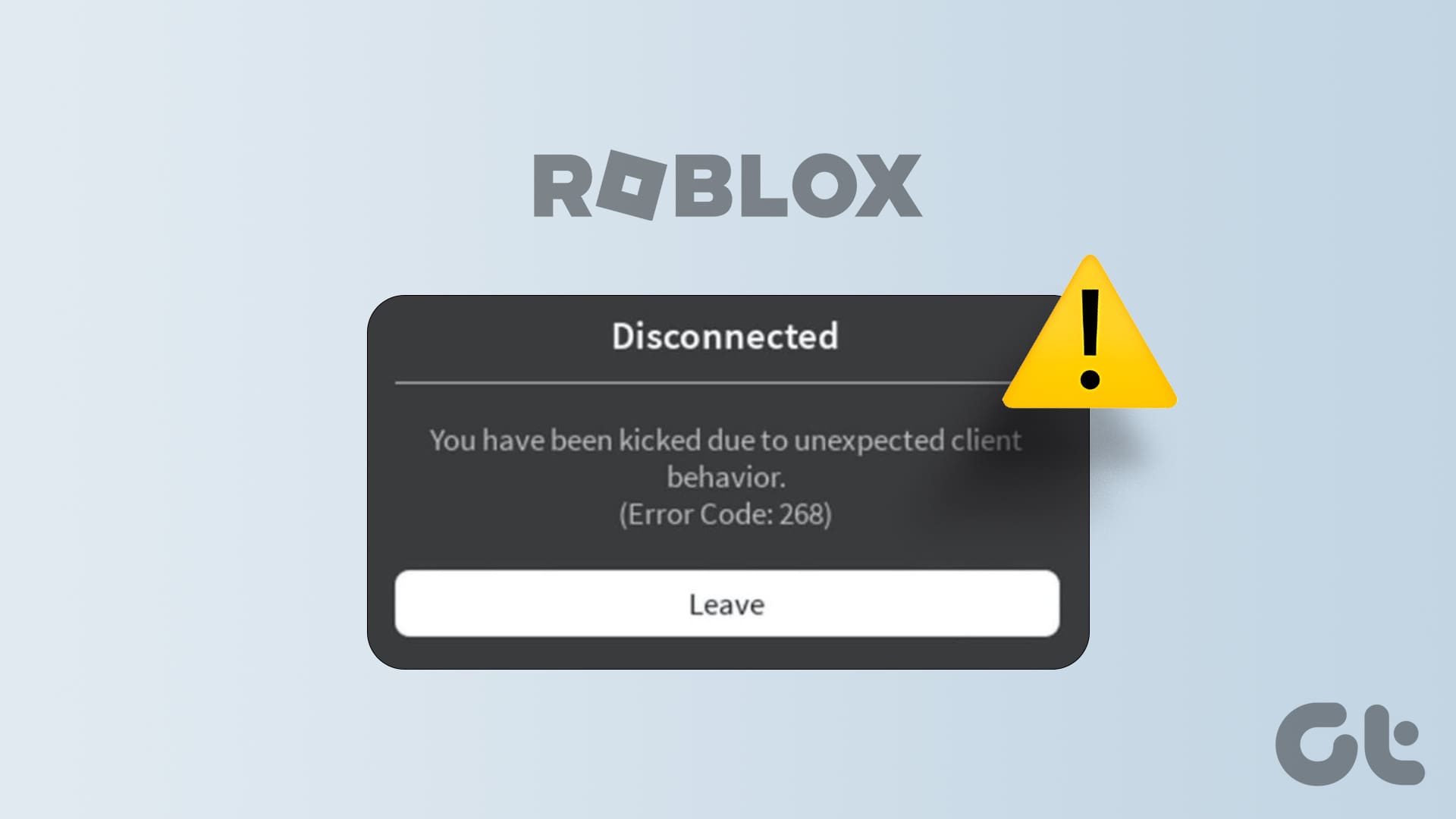
Error Code 268, often encountered by users of the popular online gaming platform Roblox, signifies a critical failure in the platform’s ability to authenticate a user’s connection. This typically manifests as an abrupt disconnection from a game server, frequently accompanied by a message indicating that the user is “unable to join” or that their “account has been logged in from another device.” From a broader tech perspective, this is a common manifestation of a security protocol or communication handshake failing to complete successfully.
The Role of Authentication Protocols
At its core, Error Code 268 points to a breakdown in the authentication process. When a user attempts to join a Roblox game, their client application must communicate with the game server, presenting credentials that verify their identity and authorization to access the server. This process involves a series of digital exchanges, often secured by encryption and cryptographic protocols.
In the realm of Tech & Innovation, robust authentication is paramount for any system involving sensitive data or critical operations. Consider the challenges of securing autonomous flight systems. A drone needs to authenticate its connection to a ground control station, ensuring that only authorized operators can issue commands. Similarly, mapping and remote sensing technologies, often deployed in critical infrastructure monitoring or environmental surveys, rely on secure data transmission and user access controls. A failure in these authentication protocols, whether in a gaming context or a high-stakes industrial application, can lead to system unavailability, data breaches, or operational failures. Error Code 268, in its Roblox manifestation, serves as a simplified, albeit frustrating, example of these complex digital security mechanisms at play.
Network Infrastructure and Connectivity
Beyond the immediate authentication handshake, network connectivity plays a crucial role in the successful establishment and maintenance of a connection. Error Code 268 can be a symptom of underlying network issues that disrupt the communication flow between the user’s device and Roblox’s servers. This includes problems with the user’s local network, their Internet Service Provider (ISP), or even issues with Roblox’s own server infrastructure.
In advanced technological domains, network reliability is not merely a convenience but a fundamental requirement. For instance, in the deployment of widespread remote sensing networks for climate monitoring, data transmission relies on stable and robust network connections. Any disruption, whether due to hardware failure, network congestion, or malicious interference, can compromise the integrity and timeliness of the collected data. Similarly, autonomous flight systems often depend on real-time data streams for navigation and control. A compromised network connection could lead to loss of control or critical navigation errors. Therefore, understanding and diagnosing network-related errors, such as those that might trigger Error Code 268, is a transferable skill across various tech sectors. The systematic troubleshooting of network issues, from checking router configurations to diagnosing firewall settings, is a common thread.
Common Causes of Error Code 268
While the underlying principle is a failed authentication, the specific triggers for Error Code 268 can vary. Identifying these common culprits is essential for effective resolution.
Security Software and Firewalls
One of the most frequent causes of authentication errors in online services is the interference of security software, including antivirus programs and personal firewalls. These applications are designed to protect a user’s system from potentially malicious online activity. However, they can sometimes be overzealous, mistaking legitimate Roblox connection attempts for suspicious behavior.
In the context of Tech & Innovation, robust cybersecurity is a cornerstone. Systems designed for autonomous operations or sensitive data processing are often protected by multi-layered security measures. When deploying AI for mapping or remote sensing, for example, the software controlling these systems must be carefully configured to allow necessary communication channels while blocking unauthorized access. Misconfigurations in these security protocols, much like on a personal computer, can lead to communication failures. For example, a sophisticated AI might be unable to initiate a data upload to a cloud server if a firewall is blocking the outgoing port. The diagnostic process for such an issue would involve reviewing firewall logs, examining software settings, and potentially creating exceptions for specific applications – a process directly analogous to troubleshooting Error Code 268 on Roblox.
Corrupted Game Files or Roblox Client Issues
Another potential cause for Error Code 268 lies within the Roblox client itself. If critical game files have become corrupted, or if there are underlying issues with the Roblox application’s installation, it can lead to an inability to properly authenticate with the game servers.
This mirrors issues that can arise in more complex technological systems. Imagine a sophisticated mapping drone that relies on specific software modules for its sensor data processing. If these modules become corrupted due to a power surge or a faulty update, the drone might be unable to calibrate its sensors or process incoming data, leading to operational failure. The solution in such cases often involves a clean reinstallation of the software or the replacement of corrupted data modules. For Roblox, this translates to uninstalling and reinstalling the Roblox player. The principle of ensuring the integrity of the core software components is a universal one in technology.
Server-Side Issues and Account Security
While less common, it’s also possible that Error Code 268 is not a problem on the user’s end but rather a temporary issue with Roblox’s servers. This could involve server maintenance, unexpected outages, or even a security flag raised on the user’s account due to suspicious activity detected by Roblox’s internal systems.
In the realm of large-scale technological deployments, server-side issues are a constant consideration. For instance, a global network of environmental sensors relies on a central data aggregation server. If this server experiences downtime, all connected devices will face communication or data transmission problems. Similarly, if an AI controlling a fleet of delivery drones is experiencing a temporary server overload, individual drones might encounter communication glitches.
Furthermore, account security is a paramount concern across all advanced tech sectors. In autonomous flight, for example, unauthorized access to an account controlling a drone could have severe consequences. Platforms implement sophisticated detection mechanisms to identify and flag potentially compromised accounts. If Roblox’s security systems detect unusual login patterns or activity that suggests an account has been compromised, they might temporarily lock access or trigger authentication errors as a protective measure. This proactive approach to security, while sometimes inconvenient for legitimate users, is a critical aspect of maintaining the integrity and safety of complex technological systems. The troubleshooting process for the user, in this case, often involves waiting for server issues to be resolved or contacting platform support to verify account security.

Strategies for Resolving Error Code 268
Successfully navigating the resolution of Error Code 268 requires a systematic approach, mirroring the diagnostic methodologies employed in other technology-intensive fields.
Basic Troubleshooting Steps
The initial steps in resolving Error Code 268 are often the most effective and involve ruling out common, easily fixable issues.
Restarting Devices and Network Equipment
A fundamental troubleshooting technique in any digital system is a simple restart. This applies to the user’s computer or mobile device, as well as their network equipment, such as their router and modem. Restarting these components can clear temporary glitches in their operating systems or network configurations, allowing for a fresh connection attempt.
In the world of Tech & Innovation, this principle is no less important. When deploying an autonomous system, for instance, a technician might initially power cycle the primary control unit and its associated communication modules. This can resolve transient memory errors or network interface card (NIC) hiccups that might be preventing proper communication. Similarly, when dealing with complex sensor arrays used in mapping, a simple reboot of the data acquisition unit can often clear temporary software hangs or connectivity issues.
Checking Internet Connection
A stable and reliable internet connection is the bedrock of any online service. Before delving into more complex solutions, it’s crucial to confirm that the user’s internet connection is functioning correctly. This can involve running internet speed tests, checking for other websites or online services that are inaccessible, and ensuring that no other devices on the network are experiencing similar connectivity issues.
For advanced technological applications, a reliable network is not just about convenience but about operational necessity. An autonomous vehicle relies on a constant flow of data from its sensors and communication with its navigation systems. Any interruption in this data stream, even a momentary one, could have significant safety implications. Therefore, network diagnostics are a critical part of the pre-flight checks and ongoing maintenance of such systems. For example, a pilot of a remote sensing drone would perform a thorough check of their ground control station’s internet connectivity before launching, ensuring that all data telemetry will be received without interruption.
Advanced Troubleshooting Techniques
When basic steps fail, more advanced techniques are often required to pinpoint and resolve the root cause of Error Code 268.
Updating Roblox and Operating System
Outdated software is a common source of compatibility issues and security vulnerabilities. Ensuring that both the Roblox client and the user’s operating system are up-to-date can resolve many problems, including authentication errors. Updates often include bug fixes, performance improvements, and patches for security exploits.
In the field of Tech & Innovation, software updates are a continuous process. AI algorithms are constantly refined, and operating systems for drones or mapping equipment are regularly patched to improve performance and security. For instance, a drone’s flight control software might receive an update that improves its GPS accuracy or introduces new obstacle avoidance features. Similarly, a remote sensing platform might have its data processing software updated to support new sensor types or enhance image analysis capabilities. Failing to keep these systems updated can lead to compatibility issues with new hardware or network protocols, similar to how an outdated Roblox client might struggle to connect to the latest server configurations.
Clearing Roblox Cache and Cookies
The Roblox client, like many applications, stores temporary data in its cache and cookies. Over time, this data can become corrupted or outdated, leading to various operational issues, including authentication failures. Clearing this cache forces the Roblox application to rebuild its temporary data, often resolving problems.
This concept of clearing temporary data or resetting application states is widely applicable in technology. For example, in managing a complex fleet of autonomous vehicles, a central management system might periodically need to clear its cache of vehicle status updates or route information to ensure it has the most current data. In imaging technology, if a camera’s internal memory or processing buffer becomes overloaded or corrupted, clearing it can resolve image artifacting or connectivity issues with the recording device. The principle is to remove potentially problematic transient data to allow the system to operate with a clean slate.

Modifying Network Settings and VPN Usage
For users experiencing persistent issues, modifying specific network settings or re-evaluating the use of Virtual Private Networks (VPNs) might be necessary. Some network configurations, particularly those involving strict security protocols or aggressive DNS settings, can interfere with Roblox’s connection. Similarly, VPNs, while offering privacy benefits, can sometimes route traffic in ways that conflict with online gaming platforms.
In the broader landscape of Tech & Innovation, network configuration and security are critical. When deploying systems in sensitive environments, such as government facilities or corporate networks, intricate firewall rules, proxy servers, and network segmentation are often in place. These configurations must be carefully managed to allow essential communication for autonomous systems or data transfer protocols without compromising security. For instance, an AI designed for mapping urban environments might need specific network ports opened on a corporate network to communicate with cloud-based processing servers. Misconfigurations in these settings could prevent the AI from functioning. The decision to use a VPN, or to configure network settings to bypass a VPN, is a common consideration for individuals and organizations alike, balancing security needs with operational requirements, a principle that extends to ensuring the seamless functioning of advanced technological systems.
By understanding Error Code 268 not just as a gaming inconvenience but as a manifestation of fundamental digital communication and authentication principles, users can gain valuable insights into the complex world of technology. The systematic approach to troubleshooting, the importance of software integrity, and the critical role of reliable network infrastructure are all transferable concepts that underpin much of the innovation we see today in fields ranging from autonomous flight to remote sensing.
