The Evolving Landscape of Mobile Device Security and Productivity
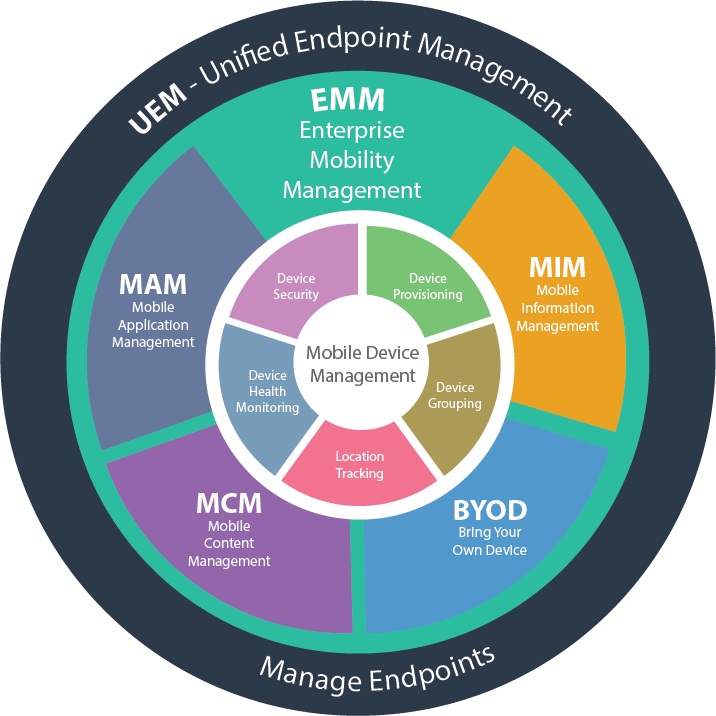
In today’s hyper-connected business environment, the ubiquitous presence of mobile devices – from smartphones and tablets to ruggedized laptops – has fundamentally reshaped how organizations operate. This proliferation, while enabling unprecedented flexibility and efficiency, also introduces a complex web of security risks and management challenges. Enterprise Mobility Management (EMM) has emerged as the crucial framework designed to address these challenges, encompassing the policies, processes, and technologies that organizations employ to secure and manage their mobile device ecosystem.
At its core, EMM aims to strike a delicate balance: empowering employees with the tools they need to be productive on the go, while simultaneously safeguarding sensitive corporate data from unauthorized access, breaches, and other threats. This intricate dance requires a comprehensive approach that extends beyond simple device provisioning. It involves a deep understanding of device lifecycles, application management, data protection, and user access controls, all within the context of an ever-evolving threat landscape. As businesses increasingly rely on mobile workers, remote teams, and a bring-your-own-device (BYOD) culture, the strategic importance of robust EMM solutions cannot be overstated. It’s no longer a peripheral IT concern but a foundational element of a modern, resilient enterprise.
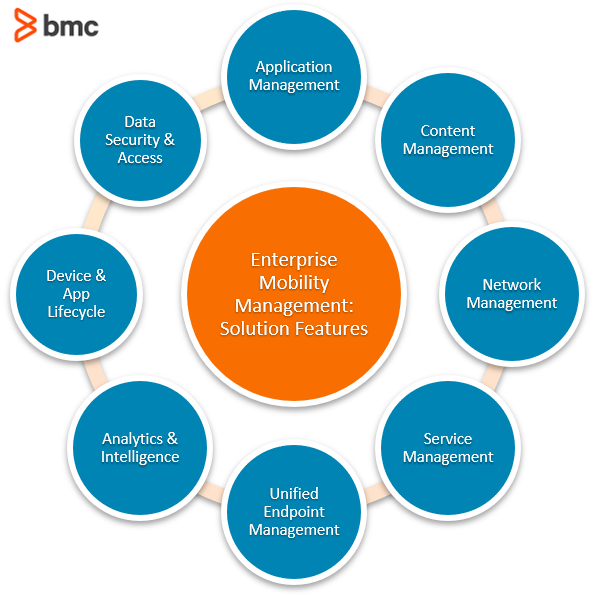
Key Components of an Effective Enterprise Mobility Management Strategy
A robust EMM strategy is built upon several interconnected pillars, each addressing a critical aspect of mobile device deployment and management within an enterprise. These components work in concert to provide a holistic solution for securing and optimizing the mobile workforce.
Mobile Device Management (MDM)
Mobile Device Management (MDM) forms the bedrock of EMM. Its primary function is to remotely configure, secure, manage, and support mobile devices across an organization. MDM capabilities typically include:
Device Enrollment and Provisioning
This is the initial stage where devices are brought into the EMM system. It can involve automated enrollment processes for corporate-owned devices, ensuring they are pre-configured with necessary security policies, applications, and network access settings before being handed over to employees. For BYOD scenarios, MDM facilitates secure enrollment of personal devices while maintaining a clear separation between personal and corporate data.
Policy Enforcement
MDM allows IT administrators to define and enforce a wide range of security policies. This includes setting password complexity requirements, configuring screen lock timeouts, enabling device encryption, restricting the use of certain features (like cameras or USB ports), and mandating the installation of antivirus software. These policies are crucial for mitigating common security vulnerabilities.
Remote Device Control
In cases of lost or stolen devices, MDM provides essential remote capabilities. Administrators can remotely lock a device, erase all corporate data from it, or even track its location. This is a vital last line of defense against data exfiltration.
Inventory Management and Compliance
MDM solutions offer detailed insights into the organization’s mobile device inventory. This includes tracking device models, operating systems, installed applications, and their compliance status against defined policies. This visibility is essential for auditing, troubleshooting, and maintaining a secure mobile environment.
Mobile Application Management (MAM)
While MDM focuses on the device itself, Mobile Application Management (MAM) zeroes in on the applications running on those devices. MAM is particularly critical in BYOD environments, where IT needs to manage corporate data within applications without necessarily controlling the entire personal device.
Application Deployment and Configuration
MAM enables IT to selectively deploy, update, and remove business applications to specific user groups or devices. This ensures that employees have access to the necessary tools for their roles. Furthermore, it allows for the secure configuration of these applications, such as enforcing strong authentication within a specific app or dictating how data is handled.
Data Leakage Prevention (DLP)
A key aspect of MAM is preventing sensitive corporate data from leaking out of managed applications. This can be achieved through features like:
- Containerization: Creating secure, encrypted “containers” for corporate apps and data, isolating them from personal apps and data on the device.
- Copy/Paste Restrictions: Preventing users from copying data from managed applications and pasting it into unmanaged personal applications.
- Selective Wipe: The ability to remotely wipe only the corporate data and applications from a device, leaving personal data untouched. This is invaluable in BYOD scenarios when an employee leaves the company.
Application Performance Monitoring
Some MAM solutions offer insights into application performance, helping IT identify issues that might be impacting user productivity.
Mobile Content Management (MCM)
Mobile Content Management (MCM) focuses on securely distributing, managing, and synchronizing corporate content to mobile devices. This ensures that employees have access to the latest versions of important documents, presentations, and other files, wherever they are.
Secure Content Repository
MCM provides a secure, centralized repository for corporate documents. Access to this content is controlled through user authentication and authorization.
Document Synchronization and Access
MCM solutions enable seamless synchronization of content across devices, ensuring that users always have the most up-to-date versions of files. Offline access to critical documents is also often a feature, allowing employees to work even without a network connection.
Content Security and Tracking
MCM incorporates security measures such as encryption, digital rights management (DRM), and access logging to protect content from unauthorized sharing or access. Administrators can often track who has accessed specific documents and when.
Identity and Access Management (IAM) for Mobile
Identity and Access Management (IAM) plays a crucial role in EMM by ensuring that only authorized users can access corporate resources on their mobile devices. This involves robust authentication and authorization mechanisms.
Single Sign-On (SSO)
SSO simplifies the user experience by allowing employees to log in once to access multiple corporate applications and resources on their mobile devices. This enhances productivity and reduces the frustration associated with managing multiple credentials.
Multi-Factor Authentication (MFA)
MFA adds an extra layer of security by requiring users to provide multiple forms of verification before granting access. This can include something they know (password), something they have (a code from a security token or smartphone), or something they are (biometric data).
Role-Based Access Control (RBAC)
RBAC ensures that users are granted access only to the specific data and applications they need to perform their job functions. This principle of least privilege significantly reduces the attack surface.
The Strategic Imperative of Enterprise Mobility Management
The adoption of EMM is no longer a mere IT best practice; it has become a strategic imperative for organizations seeking to thrive in the modern digital economy. The benefits extend far beyond basic security, impacting operational efficiency, employee satisfaction, and overall business agility.
Enhancing Security Posture
The most immediate and often cited benefit of EMM is the enhanced security it provides. By centralizing the control and monitoring of mobile devices, organizations can significantly reduce the risk of data breaches, malware infections, and unauthorized access. The ability to enforce stringent security policies, remotely manage compromised devices, and protect corporate data within applications creates a more resilient and secure mobile environment.
Boosting Employee Productivity and Flexibility
EMM empowers employees to work more effectively, regardless of their location. By providing secure access to corporate resources, applications, and data, employees can remain productive whether they are in the office, at home, or on the road. This flexibility can lead to increased job satisfaction, improved work-life balance, and a more engaged workforce.
Supporting Diverse Device and Operating System Environments
Modern enterprises often support a heterogeneous mix of devices, including corporate-owned and personally-owned devices (BYOD), running various operating systems like iOS, Android, and Windows. EMM solutions are designed to manage this diversity, allowing IT departments to implement consistent security and management policies across different platforms, simplifying administration and ensuring compliance.
Facilitating Digital Transformation Initiatives
As businesses embrace digital transformation, mobile technology often sits at its core. EMM provides the foundational infrastructure necessary to securely deploy and manage mobile applications and services that are critical for these initiatives, such as field service management, mobile sales tools, and customer engagement platforms.
Ensuring Regulatory Compliance
Many industries are subject to stringent data protection regulations (e.g., GDPR, HIPAA). EMM solutions help organizations meet these compliance requirements by providing auditable control over mobile data, enforcing data privacy policies, and enabling secure data handling practices.
Challenges and Considerations in Implementing EMM
While the benefits of EMM are clear, successful implementation requires careful planning and consideration of potential challenges.
User Adoption and Experience
One of the primary challenges is ensuring smooth user adoption. If EMM solutions are perceived as overly restrictive or cumbersome, employees may resist them, leading to workarounds that compromise security. Striking the right balance between security and usability is paramount. Clear communication about the benefits and proper training are essential.
Integration with Existing IT Infrastructure
EMM solutions need to integrate seamlessly with an organization’s existing IT infrastructure, including identity management systems, network security tools, and backend systems. This integration can sometimes be complex and require significant technical expertise.
Cost of Implementation and Management
Implementing and maintaining an EMM solution involves costs related to software licensing, hardware, and IT personnel. Organizations must carefully assess the total cost of ownership and ensure that the return on investment justifies the expenditure.
Evolving Threat Landscape
The mobile threat landscape is constantly evolving, with new vulnerabilities and attack vectors emerging regularly. EMM solutions must be continuously updated and adapted to address these emerging threats, requiring ongoing vigilance and investment.
Data Privacy Concerns
In BYOD scenarios, addressing employee concerns about data privacy on their personal devices is crucial. EMM strategies must clearly delineate between corporate and personal data and ensure that only corporate data is managed and protected, respecting the employee’s privacy.
The Future of Enterprise Mobility Management
The field of Enterprise Mobility Management is dynamic and continues to evolve. Several trends are shaping its future:
Increased Reliance on AI and Machine Learning
AI and machine learning are increasingly being integrated into EMM platforms to automate threat detection, proactively identify security vulnerabilities, and optimize device performance. Predictive analytics can help anticipate potential issues before they impact users.
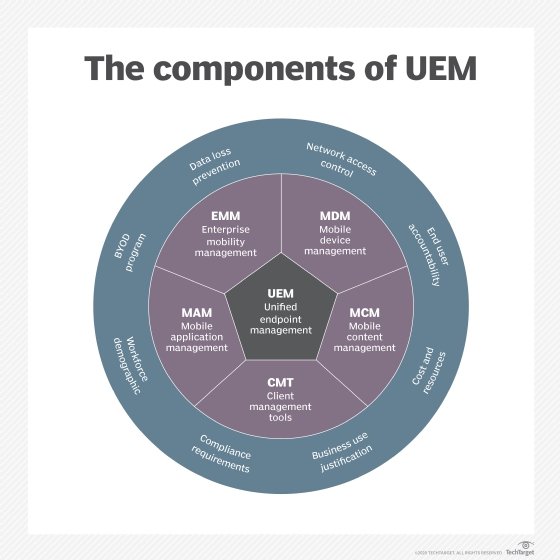
Focus on Unified Endpoint Management (UEM)
The lines between managing traditional endpoints (desktops, laptops) and mobile devices are blurring. Unified Endpoint Management (UEM) is emerging as a more comprehensive approach, aiming to manage all endpoints from a single console, simplifying IT administration and policy enforcement across the entire device landscape.
Enhanced Application Security and Containerization
As applications become more sophisticated, the focus on securing them will intensify. Advanced containerization technologies and robust application wrapping techniques will become more prevalent to ensure data protection at the application level.
Greater Emphasis on Zero Trust Security Models
The Zero Trust security model, which assumes no user or device can be trusted by default, is gaining traction in enterprise mobility. EMM will play a crucial role in implementing Zero Trust principles, ensuring continuous verification of users and devices before granting access to resources.
In conclusion, Enterprise Mobility Management is an indispensable component of modern business operations. It provides the framework to harness the power of mobile technology securely and efficiently, enabling organizations to remain agile, productive, and protected in an increasingly mobile-first world. Its evolution will continue to be driven by the need to adapt to new technologies, emerging threats, and the ever-changing demands of the global workforce.
