In an increasingly interconnected world, where our lives unfold digitally across countless platforms, the safeguarding of our private conversations has never been more paramount. From casual chats with friends to sensitive business discussions, the deluge of data transmitted daily creates a fertile ground for privacy breaches, surveillance, and cybercrime. Amidst this complex digital landscape, End-to-End Encrypted (E2EE) messaging has emerged as a critical technological innovation, offering a robust shield for our communications. It’s more than just a feature; it’s a fundamental shift in how digital conversations are secured, providing a sanctuary of privacy in a world constantly striving for transparency, sometimes at the expense of individual liberty.
At its core, E2EE messaging is a communication system where only the communicating users can read the messages. In theory, no eavesdropper—not even the internet service provider, application provider, or hosting provider—can access the cryptographic keys needed to decrypt the conversation. This means that the content of your messages remains private from the moment you hit “send” until it reaches the intended recipient, existing as an indecipherable jumble to anyone else in between. This article delves into the intricacies of E2EE, exploring its underlying technology, its profound benefits, and the evolving challenges it faces within the broader realm of digital security and innovation.
The Critical Need for Secure Communication in the Digital Age
The digital revolution, while bringing unprecedented convenience and connectivity, has also ushered in an era of heightened vulnerability for personal and professional communications. The traditional models of online messaging, often built without robust privacy as a foundational principle, expose users to myriad risks that underscore the urgent need for E2EE.
The Erosion of Digital Privacy
For years, the internet operated under a loose assumption of privacy, which has steadily eroded with the rise of data-driven economies and pervasive digital surveillance. Every message, email, or social media post typically traverses multiple servers and networks, each a potential point of interception. Without proper encryption, this data is often transmitted in plain text or with easily circumvented security protocols, making it vulnerable to anyone with the technical means or authorization to snoop. This erosion isn isn’t merely theoretical; it manifests in widespread data breaches, identity theft, and the unauthorized collection of personal information by corporations and state actors alike. The sheer volume and granularity of data collected daily paint an alarming picture, highlighting a systemic vulnerability that demands a sophisticated solution.
The Risks of Unencrypted Data Transmission
The act of sending an unencrypted message across the internet is akin to shouting your secrets across a crowded room. While you intend for only one person to hear, anyone within earshot can listen in. In digital terms, this includes malicious hackers, government agencies, and even the companies that provide the messaging services themselves. Interception can occur at various points: on the user’s device if compromised, during transit over an insecure network (like public Wi-Fi), or on the server hosting the messaging service. Once intercepted, unencrypted data can be read, altered, or stored indefinitely, leading to financial fraud, reputational damage, blackmail, and even threats to physical safety in extreme cases. For businesses, the stakes are even higher, encompassing intellectual property theft, corporate espionage, and devastating compliance failures.
The Evolution of Digital Threats
The landscape of digital threats is not static; it’s a dynamic battleground where attackers constantly devise new methods to bypass security measures. From sophisticated phishing campaigns and malware designed to capture keystrokes, to state-sponsored advanced persistent threats (APTs) targeting specific individuals or organizations, the adversary is increasingly sophisticated and well-resourced. This evolving threat landscape necessitates an equally dynamic and robust defense strategy. Simple encryption that protects data “in transit” (like HTTPS for websites) or “at rest” (on a server) is no longer sufficient on its own. While valuable, these methods still leave the data accessible to the service provider. E2EE specifically addresses this gap, ensuring that the content itself is secure from the moment of creation to the moment of consumption, even from the platform provider itself, thereby raising the bar for digital security in a world teeming with evolving digital dangers.
Unpacking End-to-End Encryption: The Core Technology
Understanding E2EE requires a dive into the sophisticated cryptographic principles that underpin its security guarantees. It’s a marvel of modern computer science, combining mathematical algorithms to create an impenetrable digital lock.
Asymmetric Cryptography: The Foundation
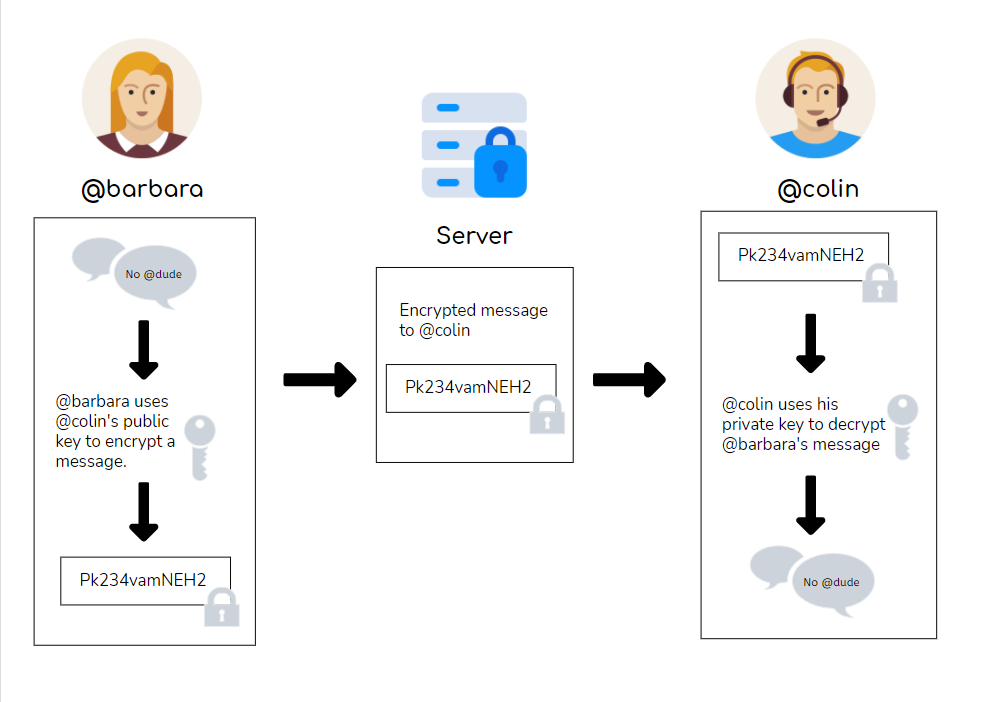
The bedrock of E2EE is asymmetric cryptography, often referred to as public-key cryptography. Unlike symmetric encryption, where the same key is used for both encryption and decryption, asymmetric cryptography employs a pair of keys: a public key and a private key. Each user possesses both. The public key can be freely distributed and used by anyone to encrypt a message intended for that user. However, only the corresponding private key—held secretly by the owner—can decrypt that message.
When you want to send an E2EE message, you use the recipient’s public key to encrypt it. When the recipient receives the message, they use their private key to decrypt it. This elegant system ensures that even if someone intercepts the encrypted message and knows the public key, they cannot decrypt it without the private key, which never leaves the owner’s device.
The Handshake: Establishing a Secure Channel
Before any messages are exchanged, E2EE systems perform a “handshake” or key exchange process to securely share public keys and establish a shared secret session key. A common protocol for this is the Diffie-Hellman key exchange. During this process, two parties, without ever sharing a secret directly over an insecure channel, can mathematically arrive at a shared secret key. This session key is then used for symmetric encryption of the actual message content, which is much faster than asymmetric encryption for large amounts of data. The beauty is that even if an eavesdropper monitors the entire key exchange, they cannot derive the shared secret key. This initial secure channel establishment is crucial for the integrity and confidentiality of all subsequent communications.
The Journey of an Encrypted Message: From Sender to Receiver
Let’s trace the typical path of an E2EE message:
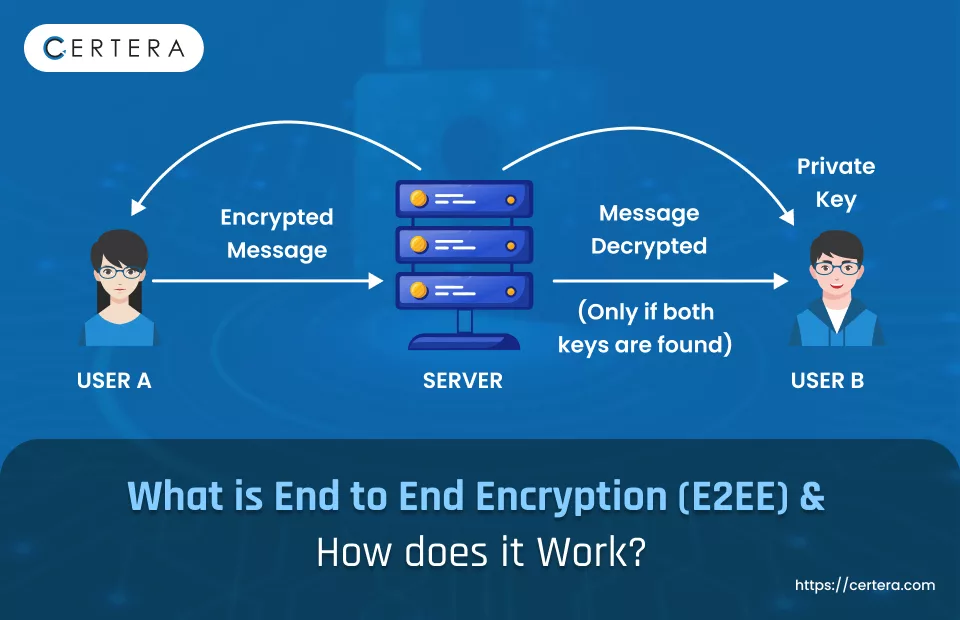
- Encryption on Sender’s Device: When you type a message and hit send, your messaging app uses the recipient’s public key (retrieved securely during the handshake) or a derived session key to encrypt your message on your device. This means the message is encrypted before it ever leaves your phone or computer.
- Transmission through Servers: The encrypted message is then transmitted over the internet to the messaging service’s servers. At this point, the message is already an unreadable ciphertext. The servers merely act as conduits, routing the encrypted data without ever being able to read its contents.
- Decryption on Recipient’s Device: Upon arrival, the recipient’s messaging app receives the encrypted message. Using their unique private key (or the shared session key), the app decrypts the message on their device, making it readable only to them.
This process ensures that the message is encrypted from “end to end”—from your device directly to the recipient’s device—bypassing any intermediaries, including the messaging service provider, who could otherwise access the content.
Key Management and Verification
A critical aspect of E2EE is robust key management. Users often have “safety numbers” or “security codes” associated with their conversations. These are typically fingerprints of the public keys involved in the conversation. Users can compare these codes out-of-band (e.g., in person, over a verified phone call) to verify that they are indeed communicating with the intended party and not an imposter (a “man-in-the-middle” attack). If the codes match, it confirms the authenticity of the public keys being used. Furthermore, advanced E2EE protocols like Signal Protocol implement “forward secrecy,” meaning that even if a long-term private key is compromised in the future, past session keys cannot be derived, thus protecting past conversations. They also include “deniability,” which means that any party in a conversation can deny having sent a specific message, as the cryptographic proof doesn’t definitively link a message to a sender in a way that can be independently verified by a third party without compromising the entire system. This layer of verification and sophisticated key handling is what elevates E2EE beyond simple encryption to a truly secure communication standard.
The Profound Benefits of E2EE for Individuals and Organizations
The implementation of E2EE is not merely a technical upgrade; it represents a significant advancement in digital rights and security, delivering profound benefits that resonate across individual privacy and organizational integrity.
Ensuring Absolute Confidentiality and Integrity
The primary and most celebrated benefit of E2EE is its guarantee of absolute confidentiality. By design, the content of the message is scrambled on the sender’s device and only unscrambled on the recipient’s device. This means that no entity—not internet service providers, not network administrators, not even the messaging app developers themselves—can read the actual content of your messages. This level of privacy extends to voice and video calls in E2EE-enabled applications, ensuring that spoken words and visual information are equally protected. Furthermore, E2EE protocols are often designed to ensure message integrity, meaning that any attempt to tamper with a message during transit will be detected, preventing unauthorized alterations. This dual assurance of confidentiality and integrity is fundamental to trust in digital communication.
Protection Against Interception and Surveillance
In an era marked by pervasive digital surveillance, both from state actors and sophisticated cybercriminals, E2EE stands as a crucial bulwark against unauthorized interception. Without E2EE, communications traversing the internet are vulnerable to passive listening or active attacks, where third parties can monitor, record, and analyze conversational data. E2EE effectively neutralizes these threats by rendering intercepted data useless to anyone without the specific private key required for decryption. This protection is vital for journalists safeguarding sources, activists organizing in oppressive regimes, lawyers discussing sensitive client information, and healthcare providers transmitting patient data. It democratizes the ability to communicate freely and privately, regardless of one’s technical prowess or political context.
Fostering Trust and Freedom of Speech
The ability to communicate without fear of eavesdropping or censorship is a cornerstone of free societies. E2EE fosters an environment where individuals can express themselves freely, engage in critical discourse, and exchange sensitive information without the chilling effect of potential surveillance. This freedom extends to personal relationships, allowing individuals to share intimate details and build trust without the specter of external intrusion. For businesses, E2EE builds trust with customers by demonstrating a commitment to their privacy, an increasingly valued commodity. It also enables secure internal communications, protecting proprietary information and fostering an environment where employees can discuss sensitive topics without fear of leaks or corporate espionage.
Empowering Data Sovereignty
E2EE plays a pivotal role in empowering individuals and organizations with greater control over their data—a concept often referred to as data sovereignty. When communications are E2EE, the data “belongs” more definitively to the users, as only they possess the keys to unlock it. This fundamentally shifts power away from centralized service providers and towards the end-users. It means that even if a messaging service’s servers are breached or compelled by legal orders to disclose data, the actual content of the E2EE messages remains inaccessible. This is a critical distinction in jurisdictions where data privacy laws are weak or non-existent, providing a technological safeguard where legal protections might fall short. It ensures that the conversation remains a private interaction between the participants, an essential right in the digital age.
Navigating the Landscape: Challenges, Innovations, and Best Practices in E2EE
While E2EE offers unparalleled security benefits, its implementation and widespread adoption come with inherent challenges, ongoing innovations, and critical considerations for users and developers alike.
Addressing Usability and Accessibility
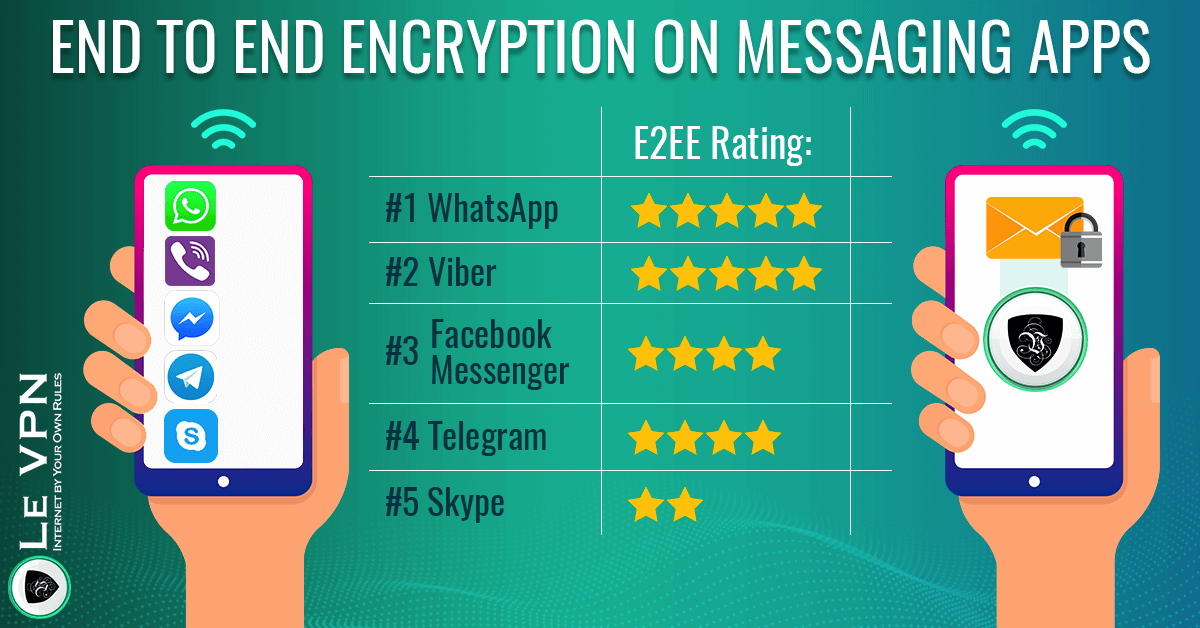
One of the significant hurdles for E2EE has traditionally been the trade-off between security and usability. Early E2EE solutions often required a degree of technical sophistication, making them inaccessible to the average user. Setting up PGP (Pretty Good Privacy) for email, for instance, can be daunting. Modern E2EE messaging apps have made tremendous strides in bridging this gap, integrating strong encryption seamlessly into intuitive user interfaces. Apps like Signal, WhatsApp (for individual chats), and Telegram (for secret chats) have demonstrated that robust security doesn’t have to come at the expense of user experience. However, challenges remain, particularly around key management verification and ensuring users understand the limitations and capabilities of their chosen E2EE solution. Continued innovation in UI/UX design is crucial for broader adoption.
The Specter of Quantum Cryptography and Future-Proofing
A significant long-term challenge for all forms of modern cryptography, including E2EE, is the impending threat of quantum computing. Current asymmetric encryption algorithms, like RSA and ECC, rely on the computational difficulty of factoring large numbers or solving elliptic curve discrete logarithm problems. Future quantum computers, if they achieve sufficient scale, could theoretically break these algorithms relatively quickly using Shor’s algorithm. This prospect necessitates a shift towards “post-quantum cryptography” (PQC), which refers to cryptographic algorithms thought to be secure against attacks by quantum computers. The research and development in this area are intense, and standard bodies are actively working on standardizing new PQC algorithms. For E2EE, this means a future transition to quantum-resistant key exchange and digital signature schemes to maintain its security guarantees in the post-quantum era, representing a crucial area of ongoing innovation in digital security.
Regulatory Demands and the Debate Over Backdoors
The unwavering security of E2EE has often put it at odds with law enforcement agencies and governments, who argue that it impedes their ability to investigate crimes and prevent terrorism. This tension frequently leads to demands for “backdoors” – intentional vulnerabilities built into encryption systems that would allow authorized parties (e.g., government agencies with a warrant) to bypass encryption and access communications. The cybersecurity community overwhelmingly opposes backdoors, asserting that any backdoor, once created, could inevitably be exploited by malicious actors, effectively weakening the security for everyone. This ongoing debate highlights the ethical, legal, and technical complexities surrounding E2EE, where the right to privacy clashes with national security concerns. Maintaining the integrity of E2EE without compromise remains a paramount goal for privacy advocates and technology innovators.
Choosing the Right E2EE Solution: Key Considerations
For individuals and organizations seeking to secure their communications with E2EE, choosing the right platform is critical. Several factors should be considered:
- Open Source vs. Proprietary: Open-source E2EE solutions (like Signal) allow independent security experts to audit the code for vulnerabilities, fostering transparency and trust. Proprietary solutions (like WhatsApp) can still be secure, but users must trust the company’s claims without full visibility into the code.
- Audited Security Protocols: Look for apps that use well-established, peer-reviewed cryptographic protocols (e.g., Signal Protocol) and have undergone independent security audits.
- Default E2EE: Ensure that E2EE is enabled by default for all communications, not just as an optional feature. This eliminates the risk of accidentally sending unencrypted messages.
- Key Verification: The app should offer a simple way to verify contact keys out-of-band to prevent man-in-the-middle attacks.
- Metadata Protection: While E2EE secures message content, some apps may still collect metadata (who you talk to, when, for how long). Consider apps that minimize metadata collection for comprehensive privacy.
- Reputation and History: Research the app’s history regarding security breaches, transparency, and its stance on user privacy.
In conclusion, End-to-End Encrypted messaging is a cornerstone of modern digital privacy and a testament to the power of technological innovation in safeguarding fundamental rights. As digital life becomes increasingly intertwined with our personal and professional realities, the continuous evolution and adoption of robust E2EE solutions are not just beneficial but essential for fostering a secure, private, and free digital world. The journey is ongoing, marked by persistent challenges and the relentless pursuit of ever more resilient cryptographic defenses, ensuring that our conversations remain truly our own.
