In an increasingly interconnected world, where digital footprints are ubiquitous and online privacy is a paramount concern, understanding the intricate mechanisms that govern our internet interactions becomes critical. Among the more insidious yet often overlooked vulnerabilities is the phenomenon known as a DNS leak. Far from being a niche IT problem, a DNS leak represents a significant erosion of online privacy and security, undermining the very tools designed to protect us. As an area of continuous technological development and innovation, addressing DNS leaks requires a deep dive into the foundational internet protocols and the cutting-edge solutions designed to fortify our digital defenses.
At its core, a DNS leak occurs when a user’s Domain Name System (DNS) requests are sent outside of an encrypted tunnel—typically a Virtual Private Network (VPN)—thereby exposing their online activity and potentially their real IP address to third parties. This seemingly technical glitch has profound implications for individuals seeking anonymity, businesses safeguarding sensitive data, and organizations striving for operational security. This article will unravel the complexities of DNS leaks, exploring their fundamental causes, the tangible risks they pose, and the innovative solutions being developed to counteract them, situating this discussion within the broader context of evolving tech and digital security innovation.
The Fundamental Role of DNS in the Digital Ecosystem
To truly grasp the significance of a DNS leak, one must first understand the foundational role of the Domain Name System itself. Often dubbed the “phonebook of the internet,” DNS is one of the most critical, yet often invisible, components of our daily online experience. Without it, navigating the web as we know it would be impossible.
How DNS Translates the Internet
Imagine trying to remember the IP address (a string of numbers like 192.0.2.1) for every website you wanted to visit. It would be an insurmountable task. This is where DNS steps in. Every time you type a human-readable website address, such as www.example.com, into your browser, DNS acts as the translator. It converts that domain name into the corresponding IP address that computers use to identify each other on the internet. This translation process is what allows your device to locate and connect to the correct server hosting the website you wish to access.
The DNS Query Process
The process begins when your computer sends a DNS query to a DNS resolver (typically provided by your Internet Service Provider, or ISP). If the resolver has the IP address cached, it returns it instantly. If not, it recursively queries a hierarchy of other DNS servers – starting with root servers, then top-level domain (TLD) servers (like .com or .org), and finally authoritative nameservers for the specific domain – until it finds the correct IP address. Once found, this IP address is sent back to your computer, allowing your browser to establish a connection with the website’s server. This entire process typically happens within milliseconds, making it seamless and largely imperceptible to the user.
Why DNS is Critical for Modern Connectivity
The efficiency and reliability of DNS are paramount for modern internet connectivity. Beyond simply translating domain names, DNS is fundamental for email delivery, content distribution networks (CDNs), and numerous other internet services that rely on accurate and fast resolution of domain names. Its distributed nature and hierarchical structure make it incredibly resilient, yet its inherent transparency in query handling also introduces the vulnerabilities that DNS leaks exploit. Understanding this foundational system is the first step in appreciating the innovative efforts required to secure it.
Unpacking the Concept of a DNS Leak
With a clear understanding of how DNS operates, we can now delve into the specific mechanics of a DNS leak. This is where the theoretical architecture of the internet intersects with the practical challenges of maintaining privacy and security.
What Constitutes a Leak?
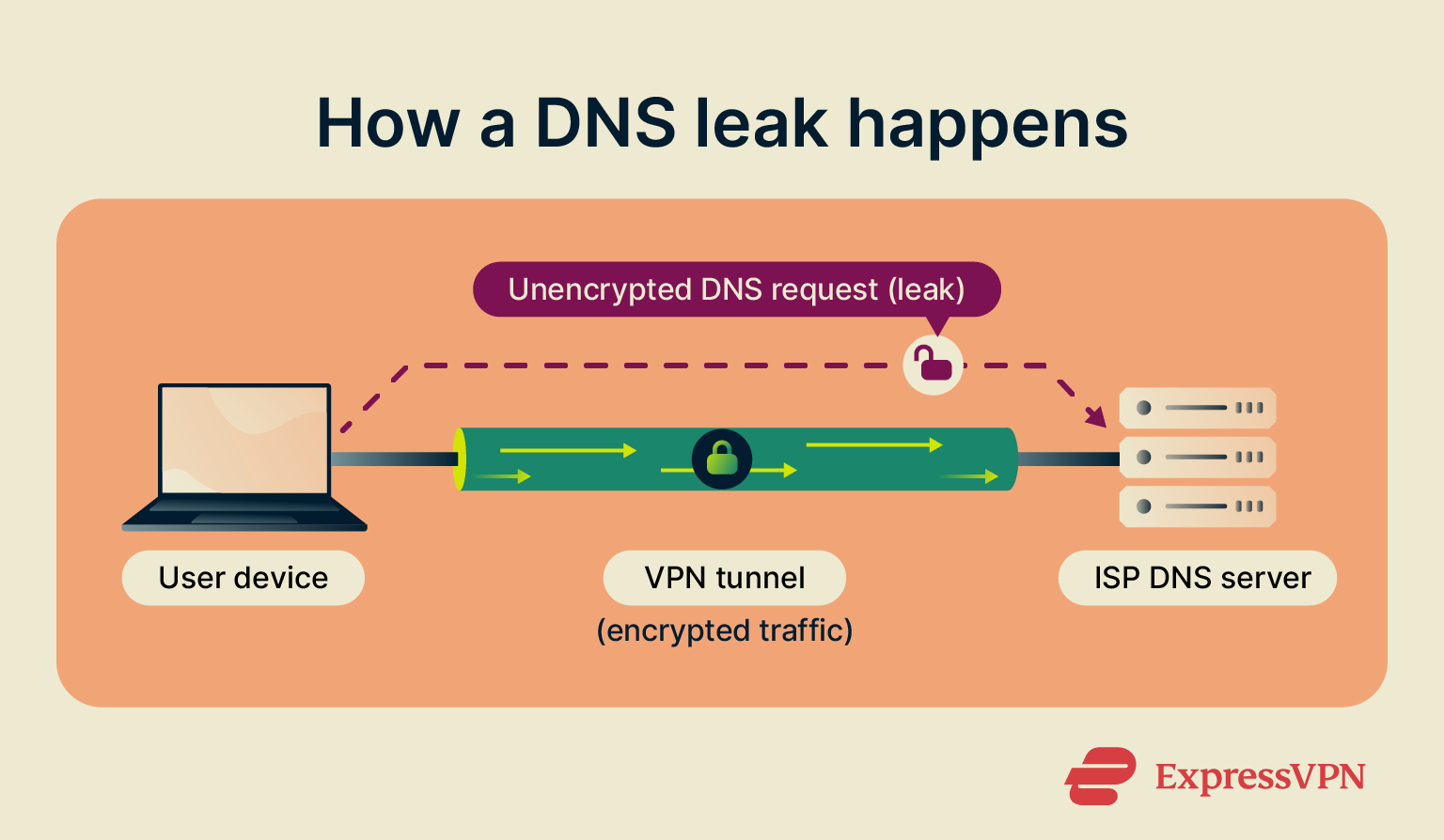
A DNS leak occurs when your device, despite being connected to a privacy-enhancing service like a VPN, inadvertently sends DNS queries outside of the secure, encrypted tunnel. Instead of routing these queries through the VPN’s designated secure DNS servers, your system might revert to using your ISP’s default DNS servers or other unencrypted servers. This exposure means that your ISP, or anyone monitoring those servers, can see which websites you are trying to access, effectively defeating the primary purpose of using a VPN—to mask your online activities and true location. The “leak” is the exposure of this information, which should otherwise be hidden.
VPNs and the Expectation of Privacy
Virtual Private Networks (VPNs) have become a cornerstone of digital privacy for millions. Their core function is to create an encrypted tunnel between your device and a server operated by the VPN provider. All your internet traffic—including DNS queries—is supposed to flow through this tunnel. This not only encrypts your data, protecting it from eavesdroppers, but also makes it appear as if your internet traffic originates from the VPN server’s location, masking your real IP address. Users pay for and expect this comprehensive protection, making DNS leaks a critical flaw that undermines trust and security.
How DNS Leaks Circumvent VPN Protection
The circumvention happens due to various factors, often stemming from how operating systems and network configurations prioritize DNS requests. When you connect to a VPN, your device is typically instructed to use the VPN provider’s DNS servers. However, this instruction isn’t always absolute. For instance, if your operating system defaults to a specific DNS server (like your ISP’s) or if there are multiple network adapters, your DNS requests might inadvertently bypass the VPN tunnel and go directly to those external servers. The encrypted VPN tunnel only protects the data within it; if a DNS query never enters the tunnel, it remains exposed, revealing your browsing intentions to external parties, primarily your ISP.
Common Causes and Mechanisms of DNS Leaks
Understanding that DNS leaks happen is one thing; knowing why and how they happen is crucial for prevention. These leaks often stem from a combination of operating system behaviors, network configurations, and the protocols involved.
Operating System DNS Handling
Different operating systems (Windows, macOS, Linux, Android, iOS) handle DNS resolution with varying degrees of complexity and default behaviors. Some operating systems, especially Windows, are known to have mechanisms that can lead to DNS leaks. For example, some versions of Windows might prioritize DNS servers from all available network adapters, or even default back to the original ISP’s DNS servers if the VPN’s DNS servers are momentarily unreachable or configured incorrectly. This can happen even when a VPN is active, as the OS attempts to ensure continuous internet access.
Manual VPN Configurations and Misconfigurations
While reputable VPN services aim to automatically manage DNS settings to prevent leaks, manual VPN setups or certain software configurations can introduce vulnerabilities. If a user manually configures their VPN connection (e.g., through a router or an unsupported client) and fails to explicitly direct all DNS queries through the VPN’s secure servers, leaks can occur. Similarly, if the VPN client itself is poorly designed or updated, it might not adequately enforce its DNS routing rules, allowing the system to revert to default unencrypted DNS resolvers.
IPv6 Leaks
Many VPN services primarily focus on protecting IPv4 traffic, which is still the dominant internet protocol. However, IPv6, the newer generation of IP addresses, is becoming increasingly prevalent. If your operating system is configured to use IPv6 and your VPN client does not properly tunnel or block IPv6 DNS requests, these requests can leak out, even if your IPv4 traffic is securely routed. An IPv6 DNS leak can reveal your real location and activities, completely bypassing the VPN’s IPv4 protection. This is a common and often overlooked vector for DNS leaks.
Transparent DNS Proxies
Some ISPs employ “transparent DNS proxies” (or DNS hijacking), which means they intercept all DNS requests, regardless of which DNS server your device is configured to use, and redirect them to their own servers. Even if your VPN successfully changes your DNS settings, a transparent DNS proxy from your ISP can override these changes by inspecting traffic on port 53 (the standard DNS port) and forcing it through their own resolvers. This advanced form of interception can be particularly difficult to detect and prevent without robust VPN features designed to combat it.
The Tangible Risks and Implications of DNS Leaks
The technicalities of DNS leaks translate into real-world consequences, impacting privacy, security, and even regulatory compliance. These implications underscore why innovation in preventing such leaks is a continuous priority in cybersecurity.
Erosion of Online Privacy
The most immediate and significant risk of a DNS leak is the severe erosion of online privacy. If your DNS requests are leaking, your ISP (and potentially other entities monitoring network traffic) can compile a detailed log of every website you visit. This data can be used to build comprehensive profiles of your online behavior, which can then be sold to advertisers, targeted for surveillance, or subjected to government requests without your knowledge or consent. For individuals who rely on VPNs for journalistic activities, political activism, or simply to maintain personal anonymity, this exposure is a critical breach of trust and a direct threat to their freedom and safety.
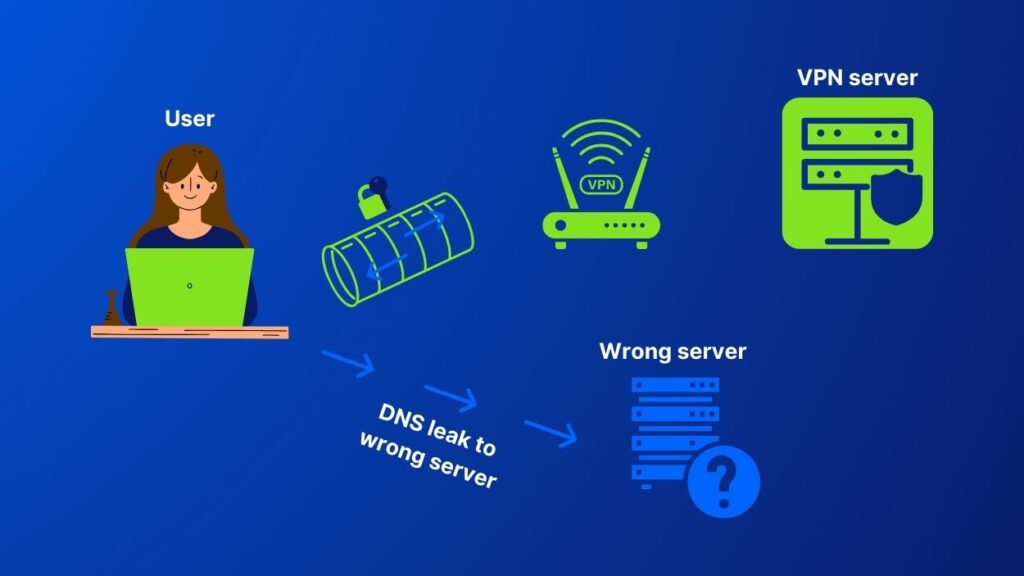
Bypassing Geo-restrictions
Many users employ VPNs to bypass geo-restrictions, enabling access to content or services that are unavailable in their physical location. If a DNS leak occurs, the content provider’s servers can detect that your DNS requests are originating from your real geographical location, rather than the VPN server’s location. This immediately defeats the purpose of the VPN for geo-unblocking, leading to access denial and revealing your true location to the service provider. For streaming services, online gaming, or international business operations, this can be a major inconvenience and a barrier to access.
Security Vulnerabilities and Targeted Attacks
Beyond privacy concerns, DNS leaks can expose users to significant security vulnerabilities. Knowing a user’s true IP address and browsing habits provides valuable intelligence for malicious actors. It can be used for targeted phishing attacks, social engineering schemes, or even more sophisticated cyberattacks aimed at exploiting known vulnerabilities associated with a specific ISP or geographic region. Businesses, in particular, face heightened risks, as leaked DNS information could expose proprietary browsing patterns, intellectual property access, or even sensitive internal network configurations to corporate espionage or state-sponsored threats.
Compliance and Regulatory Challenges for Businesses
For businesses operating under strict data protection regulations (like GDPR, HIPAA, CCPA), DNS leaks represent a critical compliance failure. If employee internet activity is exposed, it could constitute a data breach, leading to hefty fines, reputational damage, and legal repercussions. Organizations that handle sensitive client information or operate in highly regulated industries must ensure comprehensive protection against all forms of data leakage, including DNS. Innovative solutions that provide robust, auditable security are not just a best practice but a regulatory imperative in such environments.
Innovative Solutions and Best Practices for Prevention
The challenges posed by DNS leaks have spurred significant innovation in cybersecurity. A multi-layered approach, combining robust technology and vigilant user practices, is essential to mitigate these risks effectively.
Reliable VPN Services with Built-in Protection
The first line of defense against DNS leaks is selecting a high-quality VPN service that prioritizes security and privacy. Reputable VPN providers incorporate specific features to prevent DNS leaks, such as:
- Proprietary DNS servers: Running their own DNS servers ensures that all DNS queries are handled within their encrypted network, without relying on external parties.
- Automatic DNS leak protection: Their software clients are designed to automatically override system DNS settings and block any attempts to use external DNS servers.
- Kill switch: A kill switch immediately cuts off internet access if the VPN connection drops, preventing any unprotected data (including DNS queries) from leaking.
- IPv6 leak protection: Explicitly handling or blocking IPv6 traffic to prevent IPv6 DNS leaks.
Innovation in VPN technology continues to focus on making these protections seamless and resilient against new forms of leakage.
Manual DNS Configuration and Secure Servers
For users who prefer a more hands-on approach or want an additional layer of security, manually configuring DNS settings on their devices is an option. This involves setting your device to use secure, privacy-focused public DNS resolvers like Cloudflare’s 1.1.1.1, Google Public DNS (8.8.8.8), or OpenDNS. While this doesn’t offer the full protection of a VPN (as your IP is still exposed), it encrypts your DNS queries (if using DoH/DoT) and prevents your ISP from logging your requests. This is a common strategy for enhancing general internet privacy.
Testing for DNS Leaks
Regularly testing for DNS leaks is a critical best practice. Several online tools (e.g., dnsleaktest.com, ipleak.net) allow users to quickly check if their DNS queries are being routed correctly through their VPN. These tools show the IP addresses of the DNS servers being used; if they reveal your ISP’s servers or any servers outside of your VPN provider’s network, you have a leak. This proactive testing is essential for verifying the efficacy of your privacy setup and for diagnosing potential issues.
Implementing DNSSEC and Encrypted DNS Protocols (DoH/DoT)
Technological innovation is constantly pushing the boundaries of DNS security.
- DNSSEC (Domain Name System Security Extensions): Adds a layer of security to DNS by cryptographically signing DNS data, ensuring its authenticity and integrity. While DNSSEC doesn’t prevent privacy leaks, it protects against DNS spoofing and cache poisoning attacks, ensuring you’re connecting to the legitimate website.
- DoH (DNS over HTTPS) and DoT (DNS over TLS): These protocols encrypt DNS queries, preventing third parties from snooping on your DNS traffic. DoH wraps DNS queries in HTTPS, similar to web traffic, while DoT uses TLS encryption directly. Many modern browsers (Chrome, Firefox, Edge) and operating systems (Windows, Android) are increasingly integrating DoH/DoT support, representing a significant leap in DNS privacy and security by making DNS traffic indistinguishable from other encrypted web traffic.
Operating System Level Protections and Firewall Rules
Beyond VPNs and encrypted DNS, configuring operating system-level firewalls and network settings can add further layers of defense. By creating firewall rules that block all traffic over port 53 (the standard unencrypted DNS port) unless it originates from the VPN client or specific secure DNS servers, users can prevent accidental leaks. Advanced network configurations, especially on routers, can also enforce DNS routing for all devices on a network, ensuring comprehensive protection. These measures, combined with ongoing education and awareness, form a robust strategy against the ever-evolving landscape of digital threats and privacy infringements.
In conclusion, DNS leaks represent a significant challenge in the pursuit of online privacy and security, underscoring the delicate balance between convenience and protection in the digital realm. As technology evolves, so too must our understanding and mitigation strategies. The continuous innovation in VPN technologies, encrypted DNS protocols, and user-empowering tools reflects a collective commitment to building a more secure and private internet—an ongoing journey in the vast landscape of Tech & Innovation.
