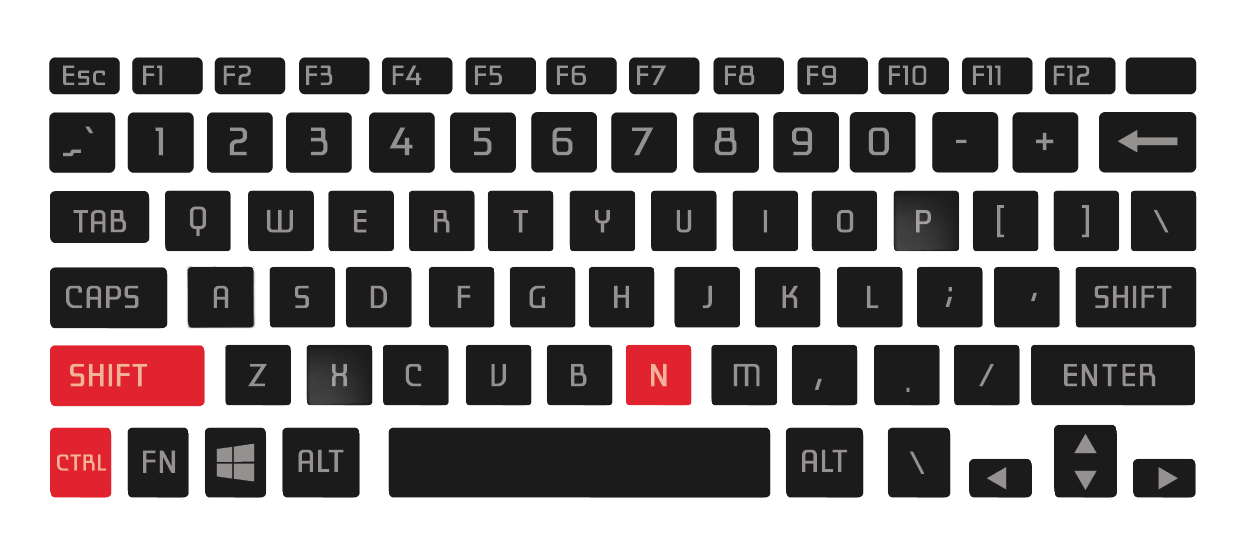
In the rapidly evolving digital landscape, understanding the nuances of our online tools is paramount. While often associated with the physical world of keyboards and computer commands, certain keyboard shortcuts have transcended their initial utility to become deeply embedded in our digital vernacular. One such sequence, “Ctrl+Shift+N,” is a ubiquitous command that unlocks a powerful, yet often misunderstood, facet of online exploration: private browsing.
This article delves into the functionality, implications, and widespread use of the Ctrl+Shift+N shortcut, exploring its role in maintaining user privacy, its integration across different operating systems and browsers, and the broader technological underpinnings that enable this seemingly simple command.
The Genesis and Functionality of Incognito Mode
The “Ctrl+Shift+N” command is the gateway to what is commonly known as “Incognito Mode,” “Private Browsing,” or “InPrivate Browsing,” depending on the specific web browser. Its primary purpose is to allow users to browse the internet without their browsing history, cookies, site data, or information entered into forms being saved on their local device. This creates a temporary, isolated browsing session that is effectively wiped clean once the private window is closed.
How Incognito Mode Works: A Technical Overview
At its core, Incognito Mode alters the default behavior of a web browser. When a standard browsing session is active, the browser diligently records various pieces of information to enhance user experience and facilitate site functionality. This includes:
- Browsing History: A chronological record of all websites visited.
- Cookies: Small text files stored by websites to remember user preferences, login status, and track user activity across different sessions.
- Site Data: This encompasses a broader range of information stored by websites, such as cached images and files, local storage, and session storage.
- Form Data: Information automatically filled into web forms, like names, addresses, and passwords.
- Download History: A record of files downloaded from the internet.
When Incognito Mode is activated via Ctrl+Shift+N, the browser essentially suspends the saving of this data for that particular session. Instead of writing to the persistent storage associated with the user’s profile, the browser operates in a temporary memory space. Upon closing all Incognito windows, this temporary data is discarded.
It is crucial to understand what Incognito Mode does not do. It does not render the user completely anonymous online. Websites can still track your IP address, and if you log into accounts (e.g., Google, Facebook, your email), those services will still know it’s you and can associate your activity with your profile. Furthermore, if your employer or school network uses monitoring software, your activity might still be visible to them. Incognito Mode primarily protects your privacy on the device you are using.
The User Interface and Accessibility
The Ctrl+Shift+N shortcut is designed for swift and intuitive access. Pressing these three keys simultaneously typically opens a new browser window with a distinct visual indicator, often a darker theme or an icon signifying privacy (e.g., a spy icon or a mask). This visual cue serves as a constant reminder that the user is operating in a private browsing session.
The widespread adoption of this shortcut across major web browsers such as Google Chrome, Mozilla Firefox, Microsoft Edge, and Brave has cemented its place as a standard digital command. While the exact key combination might vary slightly on certain operating systems or for specific browser configurations, Ctrl+Shift+N remains the most prevalent and universally recognized method for initiating private browsing.
Navigating the Spectrum of Online Privacy
The introduction and popularization of Incognito Mode, triggered by shortcuts like Ctrl+Shift+N, reflect a growing user demand for greater control over their digital footprint. In an era where online tracking and data collection are pervasive, users seek tools that empower them to manage their privacy more effectively.
Privacy Considerations and Best Practices
While Incognito Mode offers a valuable layer of privacy for local device usage, it’s not a panacea for all online privacy concerns. Understanding its limitations is key to leveraging it effectively.
- Local Device Protection: The primary benefit is preventing the browser from storing your activity on your computer or mobile device. This is particularly useful when using shared computers, as it prevents subsequent users from seeing your browsing history.
- No Protection Against Network Surveillance: Your Internet Service Provider (ISP), network administrators (at work or school), and even governments can still potentially monitor your online traffic. Incognito Mode does not encrypt your connection or mask your IP address from these entities.
- Website Tracking Persists (During Session): Websites can still collect data about your visit, such as your IP address and browsing behavior within that session, especially if you log into their services.
- Account Logins: As mentioned, logging into any online account will link your Incognito browsing activity to your established profile on that service.
To enhance online privacy beyond Incognito Mode, users often employ additional tools and strategies, such as Virtual Private Networks (VPNs), which encrypt internet traffic and mask IP addresses, and privacy-focused browsers or extensions.

The Psychological Impact and User Behavior
The availability of Incognito Mode has also influenced user behavior and perceptions of privacy. Knowing that their activity is not being permanently recorded locally can embolden users to perform searches or visit websites they might otherwise feel hesitant about. This can range from researching sensitive health information to exploring potentially controversial topics.
However, this perceived anonymity can sometimes lead to a false sense of complete invisibility. It’s important for users to remember that while their local history is protected, their online actions can still have repercussions, particularly concerning data collection by websites and services.
The Technological Underpinnings and Browser Implementations
The seemingly simple act of pressing Ctrl+Shift+N is a result of sophisticated software engineering within web browsers. Each browser developer implements Incognito Mode with specific goals and technical considerations.
Cross-Browser Compatibility and Variations
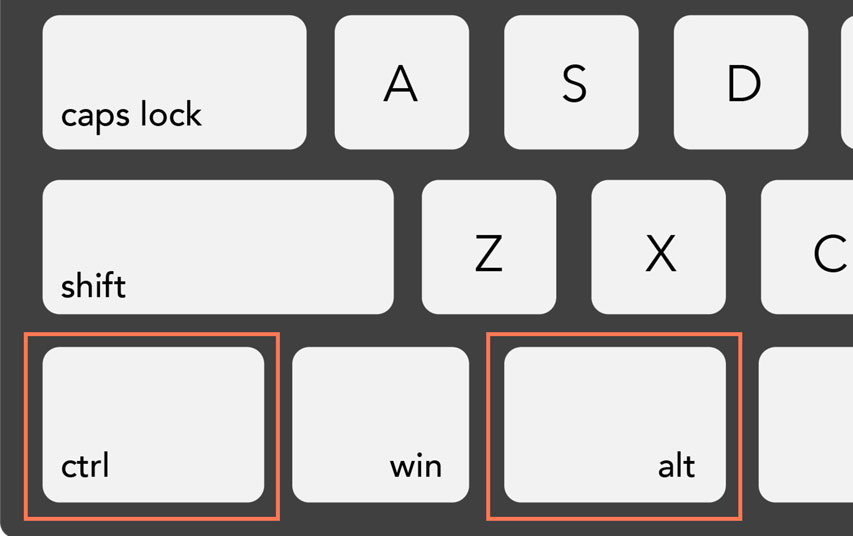
The universal adoption of Ctrl+Shift+N as the shortcut for Incognito/Private Browsing is a testament to its user-centric design. However, minor variations exist:
- Google Chrome: Ctrl+Shift+N (Windows/Linux), Cmd+Shift+N (macOS)
- Mozilla Firefox: Ctrl+Shift+P (Windows/Linux), Cmd+Shift+P (macOS) – Firefox uses “Private Browsing” and a slightly different key combination by default.
- Microsoft Edge: Ctrl+Shift+N (Windows/Linux), Cmd+Shift+N (macOS)
- Brave: Ctrl+Shift+N (Windows/Linux), Cmd+Shift+N (macOS)
- Safari: Cmd+Shift+N (macOS) – Safari uses “Private Browsing” and a distinct shortcut.
These variations, while sometimes confusing, are generally well-documented within browser help sections. The core functionality remains the same: to create a temporary, non-recording browsing session.
Evolution of Privacy Features in Browsers
The development of Incognito Mode reflects a broader trend in web browser evolution, where privacy and user control have become increasingly significant features. Early web browsers were primarily focused on functionality and speed. However, as concerns about online tracking, data breaches, and the monetization of user data grew, browser developers began incorporating more robust privacy tools.
Features like Enhanced Tracking Protection in Firefox, Brave’s built-in ad and tracker blockers, and Chrome’s ongoing efforts to phase out third-party cookies are all part of this larger movement. Shortcuts like Ctrl+Shift+N are the most accessible entry points for users to engage with these privacy enhancements, offering an immediate and tangible way to protect their local browsing data.
The ongoing dialogue around digital privacy, regulatory changes like GDPR and CCPA, and public awareness campaigns continue to shape the development of these features. The Ctrl+Shift+N command, therefore, is more than just a shortcut; it’s a symbol of the user’s agency in navigating the complex and interconnected world of the internet.
Beyond Browsers: Contextualizing the Shortcut
While Ctrl+Shift+N is overwhelmingly associated with web browsers, it’s worth noting that similar keyboard shortcut conventions exist in other software applications. The use of “Ctrl” or “Cmd” in conjunction with “Shift” and another letter often signifies an “advanced,” “new,” or “special” mode or function. This convention is a common design pattern in user interface (UI) and user experience (UX) design, aimed at providing users with efficient ways to access less frequently used but powerful features.
In the context of web browsing, Ctrl+Shift+N perfectly encapsulates this principle. It provides a quick and easy way to access a functionally distinct mode of operation – private browsing – without cluttering the main interface or requiring users to navigate through multiple menus.
Conclusion: The Enduring Significance of Ctrl+Shift+N
The Ctrl+Shift+N shortcut, while deceptively simple, represents a significant milestone in the democratization of online privacy. It offers a readily accessible tool for users to exert a degree of control over their digital footprint, particularly on their local devices. Its widespread adoption across major browsers underscores a growing user awareness of digital privacy and a demand for practical solutions.
Understanding the precise functionality and limitations of Incognito Mode, as activated by Ctrl+Shift+N, is crucial for users to make informed decisions about their online activities. While it is not a solution for complete anonymity, it serves as an invaluable first step in managing one’s digital presence and ensuring a more private browsing experience. As the digital landscape continues to evolve, the significance of such straightforward yet powerful commands will only continue to grow, empowering users to navigate the online world with greater confidence and control.
