In the dynamic and interconnected world of modern technology, where web applications form the backbone of almost every digital interaction, the importance of robust security cannot be overstated. Among the myriad of threats that developers and users face, Cross-Site Scripting (XSS) stands out as one of the most prevalent and insidious web vulnerabilities. Often misunderstood or underestimated, XSS allows attackers to inject malicious code into a legitimate website, which is then executed by an unsuspecting user’s browser. This seemingly simple act can lead to devastating consequences, ranging from data theft and session hijacking to website defacement and the distribution of malware.
Understanding XSS is not merely a task for cybersecurity professionals; it is crucial for anyone involved in building, maintaining, or even regularly using web applications. As technology continues to evolve, incorporating AI, autonomous systems, and advanced mapping capabilities, the attack surface expands, making the fundamental principles of web security like XSS prevention more critical than ever. This article will delve into the intricacies of XSS, exploring its mechanisms, various types, potential impacts, and the essential strategies for its detection and mitigation.
Understanding the Core Concept of XSS
At its heart, Cross-Site Scripting exploits the trust a user has in a legitimate website. When a website is vulnerable to XSS, it doesn’t properly validate or sanitize user-supplied input before rendering it back to the user’s browser. An attacker leverages this flaw to inject client-side scripts, typically JavaScript, into web pages viewed by other users. Since the browser executes the script, believing it originated from a trusted source, the malicious code gains access to the user’s session data, cookies, and other sensitive information.
The Client-Side Vulnerability
Unlike many server-side vulnerabilities that directly target the web server or its database, XSS primarily targets the client-side – specifically, the web browser of the victim. The attacker doesn’t directly interact with the victim’s machine but rather injects code into a web application that the victim subsequently visits. When the victim’s browser loads the vulnerable page, it executes the malicious script as if it were a legitimate part of the page’s content. This inherent trust mechanism within browsers, designed to enable dynamic web experiences, is what XSS exploits.
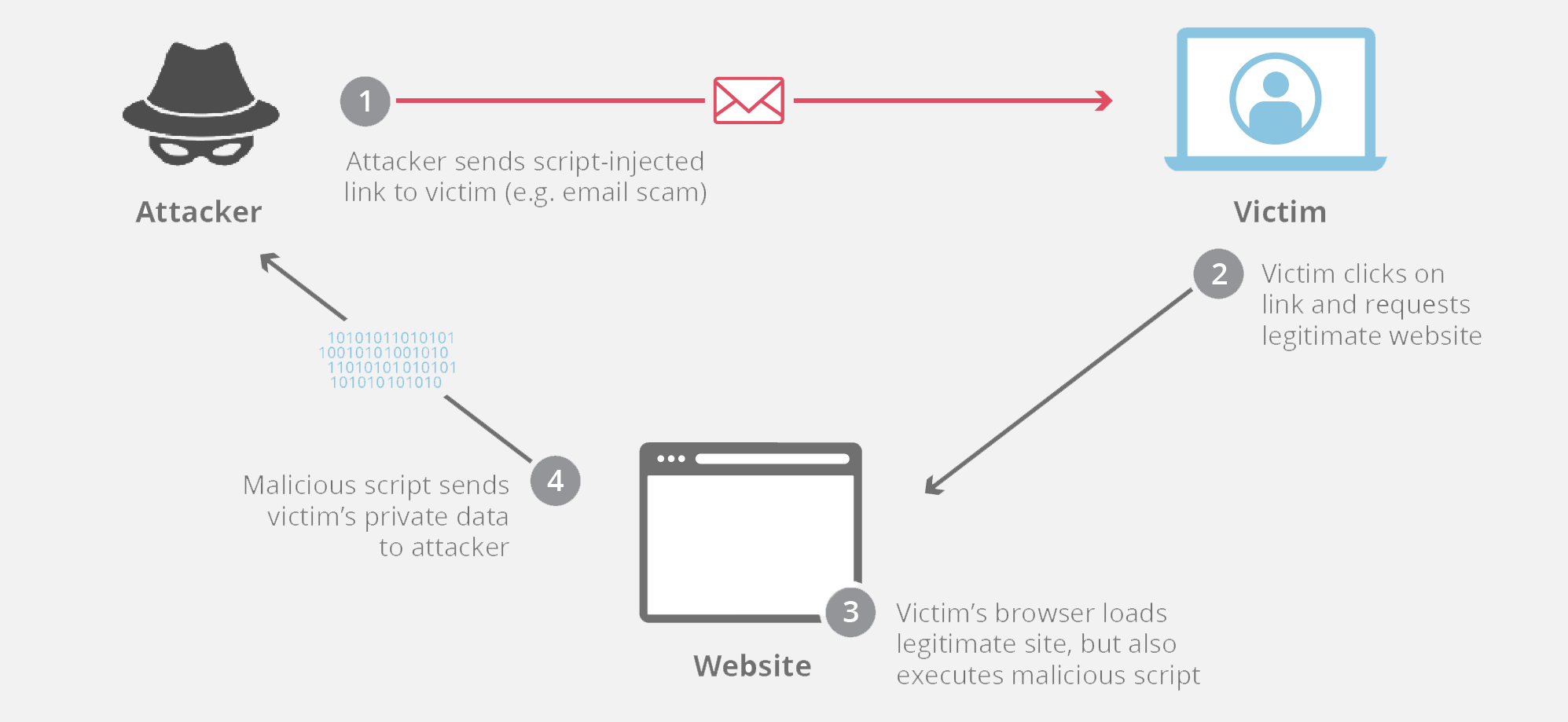
How XSS Attacks Work
A typical XSS attack involves three main parties: the attacker, the vulnerable web application, and the victim.
- Injection: The attacker discovers an input field or parameter in a web application (e.g., a search bar, comment section, URL parameter) that is not properly sanitized. They then submit malicious JavaScript code as input.
- Storage/Reflection: Depending on the type of XSS, this malicious script is either stored by the web application (e.g., in a database) or reflected back in the application’s response to the attacker’s request.
- Execution: When the victim’s browser loads the page containing the injected script (either directly from the stored script or via a specially crafted link provided by the attacker), the browser executes the script. Since the script appears to come from the legitimate website, it operates with the same privileges as other scripts from that site, allowing it to bypass the browser’s Same-Origin Policy.
Common Attack Vectors
XSS vulnerabilities commonly arise in functionalities where user input is displayed back to the user without proper sanitization. These include:
- Search fields: When search queries are displayed on the results page.
- Comment sections and forums: Where user-submitted content is posted and viewed by others.
- User profiles: Fields like “About Me” or “Bio” that display user-provided text.
- Error messages: Applications that echo back user input in error messages.
- URL parameters: Data passed via the URL, such as
http://example.com/search?query=<script>alert('XSS')</script>.
Types of Cross-Site Scripting Attacks
XSS attacks are generally categorized into three primary types, each differing in how the malicious script is injected and delivered to the victim. Understanding these distinctions is crucial for effective prevention.
Stored (Persistent) XSS
Stored XSS, also known as Persistent XSS, is arguably the most dangerous type. In this scenario, the malicious script is permanently stored on the target server. This could be in a database, a comment field, a forum post, or even a profile description. When other users visit the vulnerable page, their browsers retrieve the malicious script from the server and execute it.
The “persistence” aspect means that once the script is injected, it continues to affect users who view the compromised page until it is removed. This can impact a large number of users over an extended period without requiring the attacker to continuously lure victims to a specific malicious link.
Reflected (Non-Persistent) XSS
Reflected XSS, or Non-Persistent XSS, involves the malicious script being “reflected” off the web server onto the victim’s browser. Unlike stored XSS, the script is not permanently saved on the server. Instead, it is typically delivered via a specially crafted URL containing the malicious payload.
The attacker crafts a URL that includes the XSS payload and then tricks the victim into clicking it (e.g., through phishing emails or malicious advertisements). When the victim’s browser requests the URL, the server reflects the malicious script back in its response, which is then executed by the browser. The attack’s success depends on the victim clicking the malicious link, making it less scalable than stored XSS but still highly effective for targeted attacks.
DOM-based XSS
DOM-based XSS is a more client-side oriented attack. It occurs when a web application’s client-side script processes user-supplied data in a way that modifies the Document Object Model (DOM) environment in the victim’s browser, leading to the execution of malicious code. The server never processes the malicious payload; the vulnerability lies entirely within the client-side JavaScript.
For example, if a JavaScript function reads a URL parameter and dynamically writes content to the page without sanitization, an attacker can craft a URL to inject a script. The browser executes this script because the client-side code itself makes the mistake of including the attacker’s data. This type of XSS is often harder to detect with traditional server-side scanning tools because the payload never reaches the server.
The Far-Reaching Impact of XSS Vulnerabilities
The consequences of a successful XSS attack can be severe and multifaceted, affecting both the users and the reputation of the compromised web application. Attackers can leverage XSS for a variety of malicious purposes, often leading to significant data breaches, financial losses, and erosion of user trust.
Session Hijacking and Data Theft
One of the most common and damaging impacts of XSS is session hijacking. By executing malicious JavaScript in a victim’s browser, an attacker can steal session cookies, which often contain authentication tokens. With these tokens, the attacker can impersonate the victim, gaining unauthorized access to their account on the vulnerable website without needing their password. This can lead to the theft of personal information, financial data, and other sensitive credentials. Attackers can also directly access and manipulate the DOM, extracting data that is displayed on the page.
Defacement and Malware Distribution
XSS can be used to alter the content of a web page as it is rendered in the victim’s browser. This can range from minor defacement, where embarrassing or misleading content is displayed, to more severe alterations designed to trick users into revealing information or downloading malicious software. An attacker might inject code that redirects users to phishing sites, modifies legitimate links to point to malicious downloads, or even silently downloads and executes malware on the victim’s machine (known as a drive-by download).
Denial of Service and Phishing
While less common, XSS can sometimes be leveraged for denial-of-service (DoS) attacks. An attacker could inject a script that causes the victim’s browser to continuously send requests to the server, overwhelming it, or to crash the victim’s browser, leading to a localized DoS. Furthermore, XSS is a potent tool for sophisticated phishing campaigns. By injecting a fake login form into a legitimate website, attackers can trick users into entering their credentials directly into the attacker’s control, making these phishing attempts incredibly convincing due to the trusted domain name.
Defending Against XSS: Best Practices and Solutions
Preventing XSS vulnerabilities requires a multi-layered approach, focusing on secure coding practices, robust input validation, and proper output handling. For developers in the “Tech & Innovation” space, where new platforms and functionalities are constantly emerging, understanding and implementing these defenses is paramount to building secure and resilient applications.
Input Validation and Sanitization
The first line of defense against XSS is rigorous input validation. This involves checking all user-supplied data to ensure it conforms to expected formats and does not contain any malicious characters or scripts.
- Validation: Ensure data types, lengths, and patterns match what is expected (e.g., an email field should only accept valid email formats).
- Sanitization: If input is meant to contain HTML or special characters, these characters must be “cleaned” to remove any potentially executable code. This often involves stripping tags, attributes, or event handlers that could introduce XSS. Many libraries and frameworks provide built-in sanitization functions.
Output Encoding
Output encoding is perhaps the most critical defense against XSS. Before displaying any user-supplied data back to the browser, it must be properly encoded. Encoding translates characters that have special meaning in HTML (like <, >, ", ', &) into their entity equivalents (e.g., < becomes <). This renders any injected script harmless, as the browser will interpret it as plain text rather than executable code.
Different contexts require different encoding schemes (e.g., HTML entity encoding for HTML content, URL encoding for URLs, JavaScript encoding for JavaScript contexts). Using context-aware encoding libraries is vital.
Content Security Policy (CSP)
A Content Security Policy (CSP) is an HTTP response header that web developers can use to specify which dynamic resources (like scripts, stylesheets, and images) are allowed to load and execute on a given page. CSP acts as an additional layer of defense, even if an XSS vulnerability exists. By defining a strict CSP, developers can limit where scripts can be loaded from (e.g., only from the same origin) and prevent inline scripts from executing, significantly reducing the impact of XSS. While not a replacement for input validation and output encoding, CSP provides a powerful mitigation strategy.
Secure Development Practices
Beyond specific technical implementations, fostering a culture of secure development is crucial. This includes:
- Using Security-Focused Frameworks: Modern web frameworks (e.g., React, Angular, Vue, Django, Laravel) often have built-in XSS protection mechanisms, but developers must use them correctly.
- Regular Security Audits and Penetration Testing: Proactively identifying vulnerabilities through regular scans and ethical hacking.
- Developer Education: Ensuring all developers are aware of common vulnerabilities like XSS and how to prevent them.
- Least Privilege Principle: Limiting the capabilities of scripts and components to only what is absolutely necessary.
XSS in the Broader Tech & Innovation Landscape
As technology continues its rapid advancement, the nature of web applications and the platforms we interact with are evolving. From sophisticated AI-driven interfaces to the ever-expanding Internet of Things (IoT), the principles of secure development remain foundational, and XSS remains a persistent threat.
The Evolving Threat in Modern Web Applications
Modern web applications are often single-page applications (SPAs) that rely heavily on client-side JavaScript, APIs, and dynamic content loading. While offering rich user experiences, this complexity can introduce new vectors for DOM-based XSS and make it harder to track all data flows. The shift towards microservices and API-first architectures also means that an XSS vulnerability in one component could potentially affect others if not properly secured at every integration point. Innovative features, if not built with security in mind from the ground up, can inadvertently expose new attack surfaces.
Securing Innovative Platforms (e.g., AI/ML Interfaces, IoT)
Even seemingly disparate fields like AI/ML or IoT can indirectly be affected by XSS. For instance, an administrative interface for managing autonomous drone flight paths or processing remote sensing data, if vulnerable to XSS, could be compromised. An attacker could inject scripts to alter configuration data, steal administrator credentials, or disrupt monitoring dashboards. While XSS directly targets web applications, the control panels and data visualization tools for cutting-edge technologies are often web-based, making their security against such vulnerabilities paramount. Ensuring the integrity of data input into AI models or command interfaces for robotics is crucial, and XSS represents a significant risk if the web front-ends are not meticulously secured.
In essence, as we push the boundaries of “Tech & Innovation” with advanced capabilities, the fundamentals of web security, including understanding and preventing XSS, become even more critical. They form the unseen bedrock upon which trust, functionality, and progress are built. Ignoring these foundational vulnerabilities would be akin to building a state-of-the-art autonomous vehicle on structurally unsound wheels – a recipe for disaster.
By diligently applying robust security practices, developers and organizations can ensure that their innovative platforms and applications remain secure, reliable, and trustworthy in an increasingly complex digital landscape.