Cloud computing has fundamentally reshaped how businesses and individuals store, process, and access data. This paradigm shift, while offering unprecedented flexibility, scalability, and cost-efficiency, also introduces a unique set of security challenges. Understanding “what is cloud computing security” is paramount for anyone leveraging cloud services, as it encompasses the collective of policies, technologies, controls, and processes designed to protect data, applications, and the underlying infrastructure of cloud environments. It’s not merely about securing a server; it’s about safeguarding a complex, distributed ecosystem where data and services reside on shared resources managed by a third-party provider.
The core principle of cloud computing security is to establish and maintain trust within these shared environments. This involves a multi-layered approach, addressing threats at various points of interaction, from user access to the deep intricacies of the cloud provider’s infrastructure. Unlike traditional on-premises security models, where an organization has direct physical and logical control over its entire IT stack, cloud security often involves a shared responsibility model. This means that both the cloud provider and the customer have distinct security obligations, and misinterpreting these responsibilities can lead to significant vulnerabilities.
The Shared Responsibility Model: A Foundation of Cloud Security
At the heart of effective cloud computing security lies the understanding of the shared responsibility model. This model dictates that cloud providers are responsible for the security of the cloud, while customers are responsible for security in the cloud. The specific division of responsibilities varies depending on the cloud service model being used: Infrastructure as a Service (IaaS), Platform as a Service (PaaS), and Software as a Service (SaaS).
Understanding the Tiers of Responsibility
Infrastructure as a Service (IaaS)
In an IaaS model, the cloud provider is responsible for the physical security of the data centers, the underlying hardware (servers, storage, networking), and the virtualization layer. This includes managing the physical access to facilities, maintaining the integrity of the hardware, and ensuring the hypervisor is secure. The customer, however, is responsible for everything above the hypervisor. This means securing the operating systems, applications, data, identity and access management, and network configurations within their virtualized environment. For example, if a customer deploys a virtual machine and fails to patch its operating system, that becomes a customer security vulnerability, not a provider’s.
Platform as a Service (PaaS)
PaaS abstracts away more of the underlying infrastructure. Here, the cloud provider is responsible for securing the infrastructure, operating systems, middleware, and runtime environments. The customer’s responsibility shifts to securing their applications, data, and user access. For instance, if a customer develops an application that has a coding vulnerability, that’s a security lapse on the customer’s part. The provider handles the security of the platform upon which the application runs, but not the security of the application’s code itself.
Software as a Service (SaaS)
SaaS offers the highest level of abstraction. The cloud provider manages the entire stack – infrastructure, operating systems, middleware, applications, and data. The customer’s responsibility is primarily focused on managing user access, data usage, and configuring application-level security settings. For example, a SaaS user might be responsible for setting strong passwords, enabling multi-factor authentication for their users, and defining data access policies within the SaaS application. The security of the application’s infrastructure and codebase is solely the provider’s domain.
The Crucial Role of Customer Awareness
Regardless of the service model, a clear understanding of one’s own security obligations is critical. A common pitfall is assuming the cloud provider handles all security. This misconception can lead to misconfigurations, unauthorized access, and data breaches that could have been prevented with proper customer diligence. Proactive security awareness and education for all personnel interacting with cloud services are therefore non-negotiable components of robust cloud computing security.
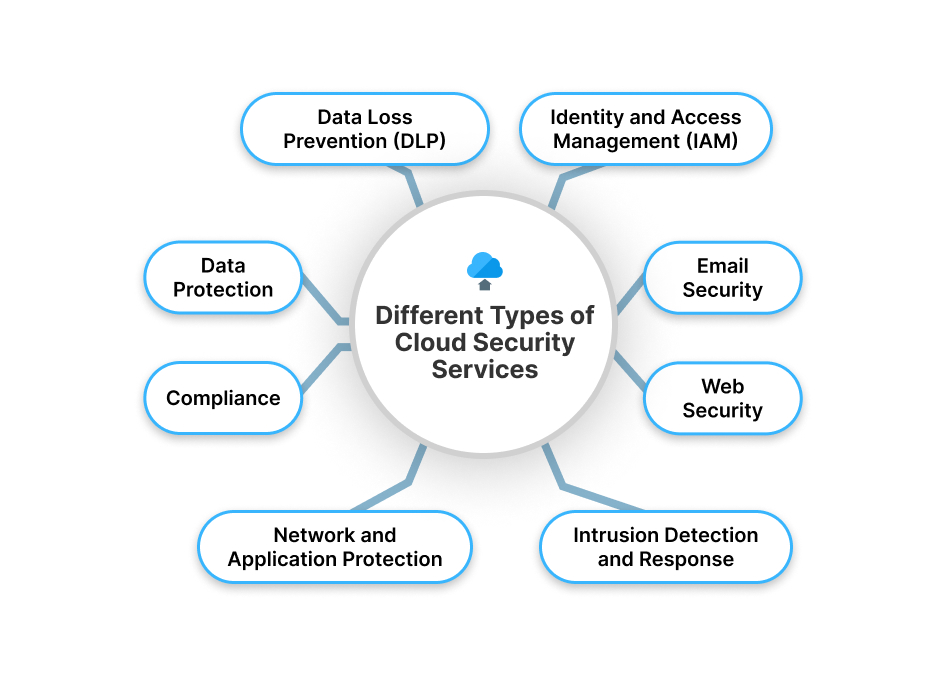
Key Pillars of Cloud Computing Security
Effective cloud computing security is built upon several interconnected pillars, each addressing a specific facet of protection. These pillars represent the core functionalities and considerations that organizations must implement to safeguard their cloud assets.
Data Security and Privacy
Data is often the most valuable asset in any organization. In the cloud, protecting this data involves a comprehensive strategy that extends beyond simple encryption.
Encryption and Data Protection
Encryption is a fundamental layer of data security. Data can be encrypted both at rest (when stored in cloud databases or object storage) and in transit (when moving between services or to users). Cloud providers offer various encryption services, often managed by them, simplifying the implementation. However, customers must ensure appropriate encryption keys are managed securely and that access controls are in place to prevent unauthorized decryption. Beyond encryption, data loss prevention (DLP) tools can identify and protect sensitive data from accidental or malicious exfiltration. Data classification and labeling are also crucial to understanding what data needs the most stringent protection.
Compliance and Regulatory Adherence
Many industries are subject to strict data privacy regulations, such as GDPR, HIPAA, and CCPA. Cloud computing security must align with these regulations. Cloud providers often offer services that are compliant with various standards, but the responsibility for demonstrating and maintaining compliance for the data processed and stored on their platforms ultimately rests with the customer. This involves understanding data residency requirements, audit trails, and how data is handled throughout its lifecycle within the cloud environment.
Identity and Access Management (IAM)
Controlling who can access what within a cloud environment is a cornerstone of security. IAM ensures that only authorized individuals and services can perform specific actions.
Principle of Least Privilege
The principle of least privilege dictates that users and services should only be granted the minimum permissions necessary to perform their designated tasks. This significantly reduces the attack surface and limits the potential damage if an account is compromised. Implementing granular role-based access control (RBAC) is a common method to achieve this, assigning specific roles with predefined permissions to users or groups.
Authentication and Authorization
Strong authentication mechanisms are vital. This includes enforcing complex password policies, implementing multi-factor authentication (MFA) for all users, and leveraging single sign-on (SSO) solutions that integrate with cloud services. Authorization then determines what actions an authenticated user or service is permitted to perform. This involves carefully defining policies that govern access to cloud resources, such as virtual machines, storage buckets, and databases. Regularly reviewing and auditing access privileges is essential to revoke unnecessary permissions and adapt to changing roles and responsibilities.
Network Security and Infrastructure Protection
While cloud providers manage the underlying physical network infrastructure, customers are responsible for securing the virtual networks they create and the services they deploy within them.

Virtual Private Clouds (VPCs) and Segmentation
Cloud providers allow customers to create Virtual Private Clouds (VPCs), which are isolated network environments within the public cloud. This provides a foundational layer of network security. Further segmentation within a VPC using subnets, security groups, and network access control lists (NACLs) is crucial for limiting the lateral movement of threats within the cloud environment. For example, a web server might be placed in a public subnet with specific firewall rules allowing only inbound HTTP/S traffic, while a database server resides in a private subnet, only accessible by the web servers.
Intrusion Detection and Prevention Systems (IDPS)
Similar to on-premises environments, cloud networks benefit from intrusion detection and prevention systems. These systems monitor network traffic for malicious activity and can alert administrators or automatically block suspicious connections. Cloud providers offer managed IDPS solutions or integrate with third-party security tools that can be deployed within customer VPCs.
Vulnerability Management and Patching
While the cloud provider secures the underlying infrastructure, customers are responsible for managing vulnerabilities within the operating systems, applications, and configurations they deploy. This includes establishing a robust vulnerability scanning program and a timely patching strategy to address newly discovered security flaws before they can be exploited. Automated patching solutions can streamline this process.
Advanced Cloud Security Concepts and Practices
Beyond the foundational elements, sophisticated cloud computing security often involves adopting advanced strategies and leveraging specialized tools to address evolving threats and complex environments.
Security Monitoring and Incident Response
Proactive monitoring and a well-defined incident response plan are critical for detecting and mitigating security incidents in the cloud.
Logging and Auditing
Comprehensive logging of all activities within the cloud environment is essential. This includes logs from compute instances, network devices, storage services, and access control events. These logs provide invaluable data for security analysis, forensic investigations, and compliance audits. Cloud-native logging services, coupled with centralized log management solutions, can aggregate and analyze these vast amounts of data to identify anomalies and potential threats.
Security Information and Event Management (SIEM)
SIEM systems play a vital role in correlating security events from various sources across the cloud infrastructure. By analyzing logs and security alerts in real-time, SIEM solutions can detect sophisticated threats that might otherwise go unnoticed. They provide a consolidated view of the security posture, enabling security teams to prioritize and respond to incidents more effectively.
Incident Response Planning and Playbooks
Despite best efforts, security incidents can occur. A well-documented incident response plan is crucial for minimizing damage and downtime. This plan should outline the steps to be taken during an incident, including containment, eradication, recovery, and post-incident analysis. Cloud-specific incident response playbooks can provide detailed, step-by-step guidance for common cloud security scenarios.
Cloud-Native Security Tools and Automation
Cloud providers offer a suite of native security tools that can be integrated into a comprehensive security strategy. Leveraging these tools and automating security processes can significantly enhance efficiency and effectiveness.
Security Groups and Network ACLs
As mentioned earlier, security groups and network ACLs act as virtual firewalls, controlling inbound and outbound traffic at the instance and subnet level, respectively. These are fundamental tools for network segmentation and access control within the cloud.
Identity and Access Management (IAM) Policies
Cloud providers offer robust IAM services that allow for granular control over resource access. Creating and managing IAM policies based on the principle of least privilege is a core security practice.
Automated Security Checks and Compliance Tools
Many cloud platforms provide tools for automated security checks and compliance reporting. These tools can scan configurations for common misconfigurations, identify compliance violations, and provide remediation recommendations. Automating these checks reduces the likelihood of human error and ensures continuous adherence to security best practices.
The Evolving Landscape of Cloud Security
The threat landscape is constantly evolving, and so too must cloud computing security. Emerging technologies and new attack vectors necessitate continuous adaptation.
Container and Serverless Security
The rise of containerization (e.g., Docker, Kubernetes) and serverless computing (e.g., AWS Lambda, Azure Functions) introduces new security considerations. Securing container images, managing container orchestration platforms, and ensuring the security of serverless functions require specialized knowledge and tooling.

DevSecOps Integration
Integrating security into the DevOps lifecycle, known as DevSecOps, is becoming increasingly important. This approach emphasizes building security into every stage of the software development process, from coding and testing to deployment and operations, ensuring that security is not an afterthought but a fundamental aspect of cloud-native application development.
In conclusion, cloud computing security is a dynamic and multifaceted discipline. It requires a thorough understanding of the shared responsibility model, the implementation of robust security pillars like data protection and IAM, and the adoption of advanced strategies and cloud-native tools. As organizations continue to embrace cloud technologies, prioritizing and investing in comprehensive cloud computing security will remain paramount for safeguarding their digital assets and ensuring business continuity in an increasingly interconnected world.
