In an era defined by distributed workforces, cloud adoption, and an ever-evolving threat landscape, endpoint security has transcended its traditional role to become the bedrock of an organization’s defense strategy. Among the leaders in delivering robust, integrated security solutions stands Cisco, and central to its endpoint security portfolio is the Cisco Secure Client. More than just a virtual private network (VPN) client, Cisco Secure Client represents a powerful, unified platform designed to protect users, devices, and data wherever they reside, integrating multiple security functions into a single, cohesive agent. This comprehensive solution is a critical component for modern enterprises aiming to secure their digital perimeter in a world without traditional boundaries.
The Evolution of Endpoint Security and Cisco’s Vision
The journey of Cisco Secure Client is deeply rooted in the evolution of network access and threat protection. What began as a focused VPN solution has expanded into a sophisticated, multi-faceted security platform, reflecting Cisco’s strategic vision for integrated, cloud-delivered security.
From AnyConnect to Secure Client: A Strategic Shift
For years, Cisco AnyConnect was synonymous with secure remote access. It provided reliable VPN connectivity, allowing users to securely connect to corporate networks from anywhere. However, as cyber threats grew more complex and attack surfaces expanded beyond the traditional corporate network, the need for a more comprehensive endpoint security agent became evident. Organizations required not just secure access, but also robust threat detection, posture assessment, and compliance enforcement, all managed seamlessly.
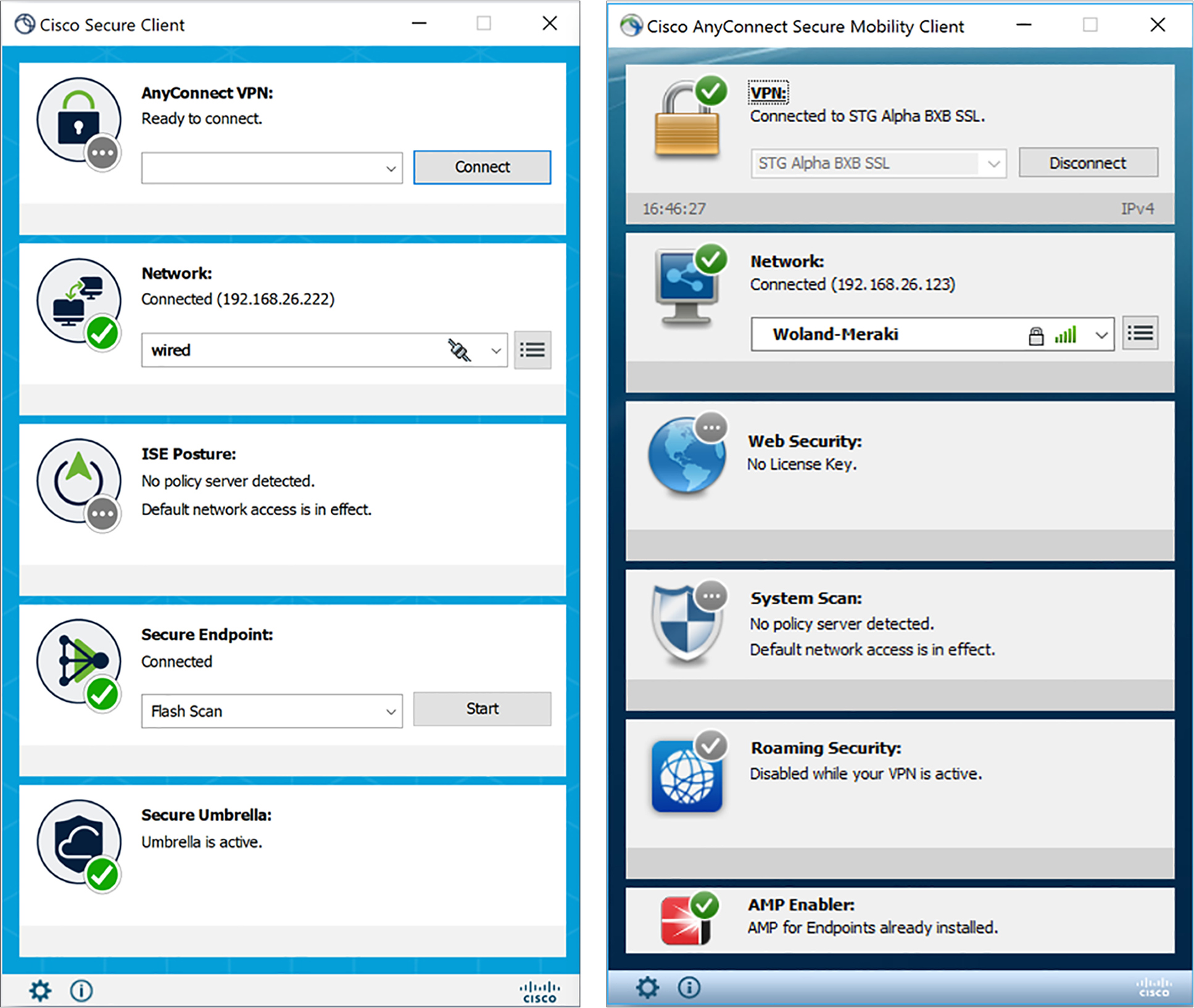
This recognition led to the strategic evolution from AnyConnect to Cisco Secure Client. This transformation was more than just a rebranding; it signified a fundamental shift towards a unified agent that consolidates various security modules. Cisco Secure Client integrates capabilities that were once disparate, offering a singular point of deployment and management for a broad spectrum of security functions. This move aligns with Cisco’s broader security strategy to provide a simpler, more effective, and more integrated security experience across the entire attack continuum. It embodies a proactive approach to security, moving beyond reactive threat responses to predictive prevention and automated remediation.
Addressing Modern Cyber Threats
Today’s cyber threats are increasingly sophisticated, ranging from ransomware and phishing attacks to advanced persistent threats (APTs) and zero-day exploits. The proliferation of remote work and the “bring your own device” (BYOD) trend have further complicated the security landscape, making every endpoint a potential entry point for attackers. Traditional perimeter-based security models are no longer sufficient.
Cisco Secure Client is engineered to address these modern challenges head-on. By converging multiple security functions—such as VPN, endpoint threat protection, network visibility, and cloud security integration—it provides a layered defense that protects against a wide array of threats. It aims to empower organizations to enforce granular access policies, detect malicious activity in real-time, and ensure compliance, all while maintaining a seamless user experience. The client acts as the eyes and ears on the endpoint, reporting critical security telemetry and enforcing policies dictated by centralized security management platforms. This holistic approach is crucial for maintaining business continuity and protecting sensitive data in an unpredictable digital environment.
Core Capabilities and Features of Cisco Secure Client
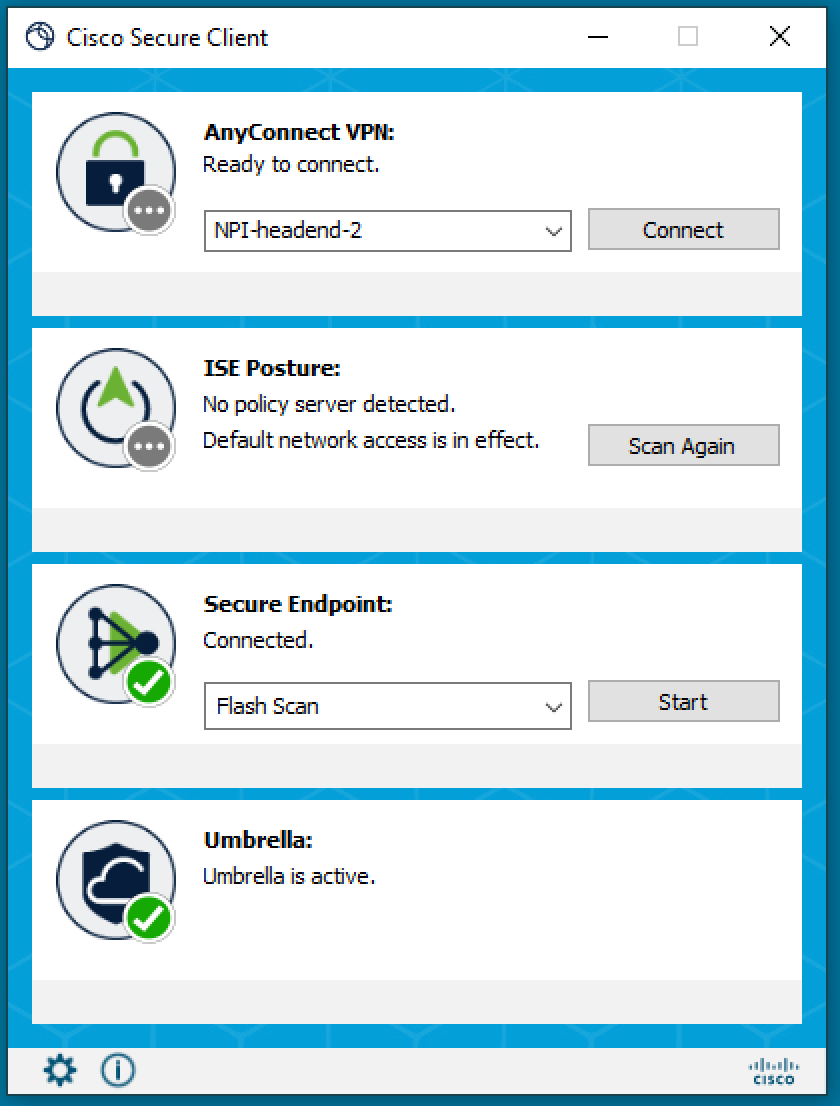
Cisco Secure Client stands out due to its comprehensive suite of features, designed to provide layered protection and flexible access. These capabilities are integrated into a single agent, simplifying deployment and management while maximizing security efficacy.
Robust VPN Connectivity
At its heart, Cisco Secure Client maintains its strong legacy as an industry-leading VPN solution. It offers highly secure, always-on remote access, enabling users to connect to corporate networks from any location, on any device. This critical functionality ensures that remote and hybrid workers can access necessary resources securely, encrypting data in transit and protecting against eavesdropping and man-in-the-middle attacks. It supports various VPN protocols, including IPsec IKEv2 and SSL, providing flexibility and compatibility across diverse network infrastructures. The VPN component is designed for resilience, offering automatic reconnection and seamless roaming between networks, ensuring uninterrupted productivity for the end-user.
Advanced Threat Protection (AMP for Endpoints Integration)
A key differentiator for Cisco Secure Client is its tight integration with Cisco Secure Endpoint (formerly AMP for Endpoints). This integration transforms the client into a powerful endpoint detection and response (EDR) tool. It provides continuous monitoring, advanced malware detection, and real-time threat analysis, leveraging Cisco Talos threat intelligence. The endpoint agent can detect, block, and remediate advanced threats, including fileless malware, ransomware, and polymorphic viruses, even when the endpoint is offline. This proactive protection extends beyond signature-based detection, employing behavioral analysis and machine learning to identify novel threats that traditional antivirus solutions might miss.
Network Visibility and Compliance
Understanding what is happening on endpoints and across the network is paramount for effective security. Cisco Secure Client enhances network visibility by collecting rich telemetry data from connected devices. This data feeds into Cisco’s security analytics platforms, providing administrators with deep insights into user behavior, device posture, application usage, and potential security anomalies. With this visibility, organizations can enforce compliance policies more effectively, ensuring that only devices meeting specific security requirements (e.g., up-to-date patches, antivirus installed) are granted access to sensitive resources. This visibility is crucial for incident response, allowing security teams to quickly identify the scope of a breach and initiate remediation efforts.
Posture Assessment and Access Control
To further strengthen security, Cisco Secure Client incorporates robust posture assessment capabilities. Before granting network access, the client can assess the security health of an endpoint, verifying compliance with organizational policies. This includes checking for operating system updates, firewall status, presence of necessary security software, and even specific registry settings. Based on this assessment, dynamic access policies can be applied, granting full, limited, or no access to network resources. This ensures that only healthy, compliant devices can connect, significantly reducing the risk of compromised endpoints introducing threats into the network. This capability is foundational for Zero Trust Network Access (ZTNA initiatives.
Cloud-Delivered Security with Umbrella Integration
The integration with Cisco Umbrella—Cisco’s cloud-delivered security service—extends protection beyond the traditional network perimeter. When Cisco Secure Client is deployed with Umbrella, all DNS requests from the endpoint are routed through Umbrella’s global network. This allows Umbrella to block malicious domains, command-and-control callbacks, and phishing attempts at the DNS layer, often before a connection to a malicious server can even be established. This provides an additional layer of defense, protecting users whether they are on or off the corporate network, regardless of whether they are connected via VPN. This cloud-native integration is particularly effective against emerging threats and offers seamless protection without impacting performance.
Why Cisco Secure Client is Essential for Modern Enterprises
The confluence of remote work, cloud migration, and sophisticated cyber threats makes a unified endpoint security solution not just beneficial, but critical for business resilience. Cisco Secure Client addresses these challenges head-on, delivering tangible benefits for organizations.
Hybrid Work Model Support
The rise of hybrid work models has blurred the lines between the office and home, making secure remote access and consistent security enforcement more challenging than ever. Cisco Secure Client is purpose-built for this environment. It ensures that employees working from anywhere, on any device, have secure, reliable access to corporate resources while simultaneously being protected from cyber threats. Its always-on VPN and cloud-delivered security modules ensure that the security posture of an endpoint is maintained, regardless of its physical location or network connection. This seamless experience is vital for maintaining productivity without compromising security.
Unified Security Experience
Managing multiple security agents from different vendors can lead to operational complexity, security gaps, and increased costs. Cisco Secure Client consolidates various security functions into a single, lightweight agent. This unification simplifies deployment, reduces endpoint resource consumption, and minimizes the administrative burden on IT and security teams. A unified agent also means a more consistent security policy enforcement across all modules, reducing the chances of misconfigurations or conflicting policies that could leave an organization vulnerable. It presents a single pane of glass for many endpoint security tasks, streamlining operations significantly.
Operational Efficiency and Centralized Management
The ability to manage diverse security functions from a single console significantly boosts operational efficiency. Cisco Secure Client integrates with Cisco’s security management platforms, offering centralized visibility, policy creation, and reporting. This allows security teams to efficiently monitor endpoint health, deploy updates, enforce policies, and respond to incidents across the entire organization. Automation capabilities further reduce manual effort, enabling teams to focus on strategic security initiatives rather than day-to-day administrative tasks. This centralized approach translates into faster incident response times and a more agile security posture.
Scalability and Future-Proofing
As businesses grow and their security needs evolve, solutions must be able to scale effortlessly. Cisco Secure Client is designed with scalability in mind, capable of protecting thousands of endpoints across diverse environments. Its modular architecture allows organizations to activate only the security features they need, with the flexibility to add more as requirements change. Furthermore, as part of Cisco’s broader security portfolio, it benefits from continuous innovation, leveraging global threat intelligence from Cisco Talos and integrating with new security technologies. This ensures that organizations are equipped with a future-proof solution that can adapt to emerging threats and technological advancements.
Implementing and Managing Cisco Secure Client
Effective deployment and ongoing management are key to maximizing the value of Cisco Secure Client. It’s not just about installing software, but about integrating it strategically within an organization’s security ecosystem.
Deployment Scenarios
Cisco Secure Client offers flexible deployment options to suit various organizational structures and needs. It can be deployed via traditional methods such as Group Policy Objects (GPOs), System Center Configuration Manager (SCCM), or other enterprise software distribution tools. For smaller organizations or those leveraging cloud-native solutions, it can also be deployed through cloud-based management platforms. A phased rollout is often recommended, starting with pilot groups to ensure compatibility and fine-tune policies before a broader deployment. Careful planning of profiles and security policies is essential to tailor the client’s behavior to different user groups and device types.
Integration with Existing Security Ecosystems
One of the strengths of Cisco Secure Client lies in its ability to integrate seamlessly with other components of an organization’s security infrastructure. Beyond its internal integrations with Cisco Secure Endpoint and Umbrella, it can share telemetry data with Security Information and Event Management (SIEM) systems, threat intelligence platforms, and other security orchestration and automation response (SOAR) tools. This interoperability enhances overall security posture by providing a holistic view of threats and enabling automated responses. When combined with identity and access management (IAM) solutions, it further strengthens authentication and authorization processes, reinforcing the principle of least privilege.
Best Practices for Configuration
Proper configuration is paramount for Cisco Secure Client to perform optimally. This involves defining granular access policies, configuring posture assessment rules, and setting up threat detection and response actions. Organizations should establish distinct profiles for different user groups (e.g., administrators, general users, contractors) to enforce appropriate levels of access and security. Regular review and updating of these configurations are crucial to adapt to changes in the threat landscape, compliance requirements, and business operations. Implementing multi-factor authentication (MFA) with VPN connections is also a critical best practice to prevent unauthorized access, even if credentials are compromised.
The Future of Endpoint Security with Cisco Secure Client
As the digital landscape continues to evolve, so too will the capabilities of Cisco Secure Client. Its strategic position within Cisco’s security architecture points towards a future driven by intelligence, automation, and a unified approach to security.
AI and Machine Learning in Threat Detection
The integration of advanced AI and machine learning algorithms will continue to be a significant focus. These technologies enhance the client’s ability to detect novel and sophisticated threats, moving beyond known signatures to identify anomalous behaviors and predictive indicators of compromise. AI-driven analytics will enable more precise threat classification, reduce false positives, and accelerate automated response actions, making the endpoint an even more intelligent and autonomous defense mechanism. This continuous learning capability ensures that the client remains effective against an ever-changing array of threats.
Zero Trust Architecture Alignment
Cisco Secure Client is a natural fit for Zero Trust Network Access (ZTNA) initiatives. Its core functionalities—device posture assessment, granular access control, and continuous verification—are fundamental to a Zero Trust model where no user or device is inherently trusted, regardless of their location. The future will see even tighter integration with ZTNA frameworks, enabling organizations to move closer to a security model where access is granted only after explicit verification of identity, device health, and context for every connection attempt. This continuous verification ensures the highest level of security in a perimeter-less world.
Continuous Innovation and Updates
Cisco’s commitment to continuous innovation means that Secure Client will regularly receive updates that introduce new features, enhance existing capabilities, and address emerging vulnerabilities. Leveraging the vast threat intelligence from Cisco Talos, the client will stay ahead of attackers, adapting its defenses as new threats emerge. This ongoing development ensures that organizations deploying Cisco Secure Client are equipped with a dynamic, resilient, and adaptive security solution that can evolve with the complex demands of modern cybersecurity. The platform will serve as a crucial component in delivering pervasive, integrated security that simplifies protection without compromising efficacy.
In conclusion, Cisco Secure Client is far more than just a VPN. It is a unified, intelligent endpoint security platform that integrates critical functions for secure access, advanced threat protection, visibility, and compliance. In today’s interconnected and threat-laden world, it represents an indispensable tool for enterprises striving to protect their distributed workforce, sensitive data, and overall digital integrity.