In an increasingly digital world, data security has become paramount for individuals and organizations alike. Microsoft’s BitLocker Drive Encryption is a powerful tool designed to protect data by encrypting entire volumes on Windows operating systems. While BitLocker offers robust security, there are scenarios where users might encounter a “BitLocker recovery” prompt. Understanding what BitLocker recovery is, why it occurs, and how to navigate it is crucial for maintaining access to your encrypted data. This process, deeply embedded in the realm of Tech & Innovation, highlights the intricate balance between security and accessibility, showcasing the intelligence behind modern data protection strategies.
Understanding BitLocker: A Foundation of Data Security
BitLocker Drive Encryption is a full-disk encryption feature included with Microsoft Windows versions starting from Windows Vista. Its primary goal is to protect data at rest, meaning data stored on a hard drive or solid-state drive (SSD), against unauthorized access. This is particularly vital for laptops and portable devices that are at a higher risk of loss or theft. By encrypting the entire drive, even if the device falls into the wrong hands, the data remains inaccessible without the correct decryption key.
The Core Purpose of BitLocker
The fundamental purpose of BitLocker is to provide an additional layer of security beyond traditional password protection. A stolen computer with an unencrypted drive can have its drive removed and connected to another system, bypassing the operating system’s login screen. With BitLocker, this avenue of attack is effectively shut down. The encryption scrambles the data in such a way that it appears as gibberish without the specific cryptographic key, rendering the information unusable to anyone without authorization. This protection extends to sensitive personal documents, proprietary business information, financial records, and any other data stored on the encrypted volume.
How BitLocker Works: Encryption in Action
BitLocker typically works in conjunction with a Trusted Platform Module (TPM) chip, a specialized microcontroller embedded in many modern computers. The TPM acts as a secure cryptographic processor, capable of storing cryptographic keys and measuring the integrity of the system’s boot process. When BitLocker is enabled, it generates an encryption key that is securely stored by the TPM. This key is only released to unlock the drive if the boot integrity check passes, meaning no unauthorized changes have been made to the boot files, BIOS/UEFI firmware, or other critical system components.
In systems without a TPM, or when additional security is desired, BitLocker can also be configured to use a USB flash drive containing the startup key or require a PIN entered during boot-up. The encryption process itself happens in the background, making the drive’s contents opaque to anyone lacking the proper decryption credentials. This seamless operation for the legitimate user, coupled with impenetrable security for unauthorized access, exemplifies elegant technological innovation.
The Necessity of BitLocker Recovery
While BitLocker is designed for seamless operation, there are specific circumstances under which the system will initiate a “BitLocker recovery” process. This is not a malfunction but rather a security measure designed to ensure that only an authorized user can access the encrypted data if there’s any suspicion of tampering or an unusual system state. It’s an intelligent failsafe, built into the core logic of the encryption system.
When BitLocker Recovery is Triggered
BitLocker recovery is triggered when the system detects a change that could potentially compromise the security of the encrypted drive. Since BitLocker relies on the TPM to verify the integrity of the boot environment, any modification to this environment will cause the TPM to withhold the encryption key, prompting the user for a recovery key. Common scenarios that lead to recovery mode include:
- Hardware Changes: Replacing a motherboard, CPU, hard drive, or even significant changes to peripherals.
- Firmware/BIOS/UEFI Updates: Flashing a new BIOS/UEFI version or changing certain BIOS settings (e.g., boot order, enabling/disabling secure boot, virtualization settings).
- Failed Software Updates: Windows updates that affect boot files or system partitions.
- Malicious Software: Viruses or malware that attempt to modify boot components.
- TPM Issues: A malfunction or clearing of the TPM module.
- Boot Manager Changes: Rebuilding the boot manager or boot configuration data (BCD).
- Forgotten PIN or Startup Key: If BitLocker is configured to use a PIN or a USB startup key and the user forgets the PIN or loses the USB.
- Battery Depletion: In some rare cases, a completely drained laptop battery can cause a recovery prompt upon reboot.
Each of these events, from the perspective of BitLocker, could represent an attempt to bypass security, and thus, the system intelligently defaults to a secure, locked state.
Protecting Against Unauthorized Access
The very mechanism that triggers BitLocker recovery is its strength against unauthorized access. By demanding a recovery key for any perceived change in the boot environment, BitLocker ensures that even sophisticated attackers who manage to alter system components cannot simply boot into the operating system and access the encrypted data. The recovery key is distinct from the regular login password and is typically a long, alphanumeric string (48 digits) that acts as a master key to unlock the drive. This multilayered security approach is a cornerstone of robust cybersecurity in modern tech solutions.
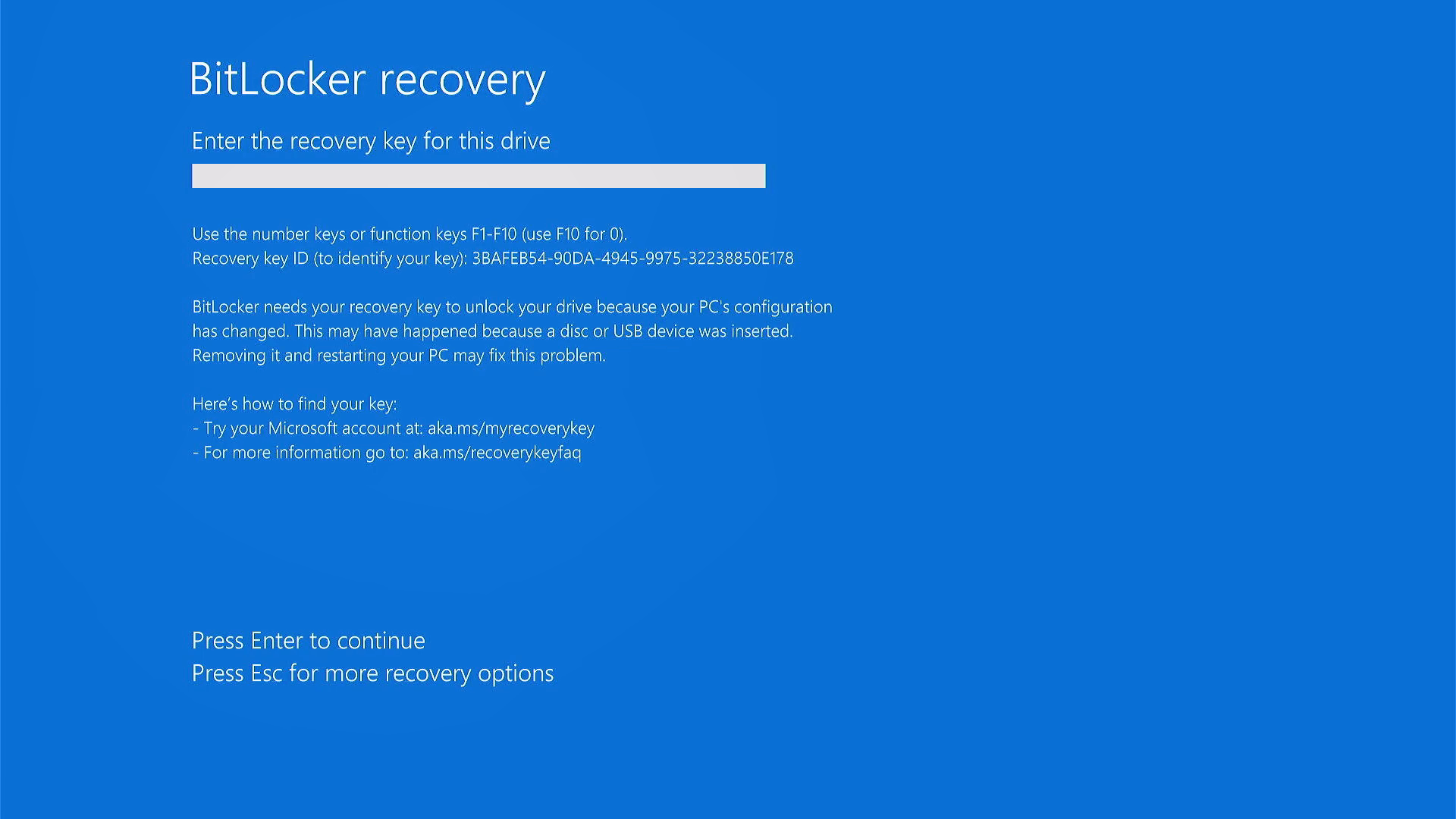
Navigating the BitLocker Recovery Process
When faced with a BitLocker recovery screen, the most critical piece of information you need is your BitLocker recovery key. Without it, recovering access to your data can be exceptionally difficult, if not impossible, underscoring the importance of proper key management.
Identifying Your Recovery Key
Fortunately, Microsoft provides several ways to store your recovery key, and it’s imperative that users understand where to find it before a recovery situation arises. When BitLocker is initially enabled, the system prompts the user to save the recovery key in one or more of the following locations:

- Microsoft Account (Recommended for personal devices): If you sign in to your Windows device with a Microsoft account, the recovery key is automatically uploaded to the cloud and can be accessed via
account.microsoft.com/devices/recoverykey. This is often the easiest and most reliable method for home users. - Print the Recovery Key: The option to print a hard copy of the key. This should be stored in a safe, secure location, separate from the computer itself.
- Save to a File: Saving the key to a text file on another drive (e.g., a USB flash drive). This external drive should also be stored securely.
- Save to an Azure AD Account (for organizational devices): In corporate environments managed with Azure Active Directory, the recovery key is typically stored in the organization’s Azure AD account, accessible by IT administrators.
- Active Directory Domain Services (AD DS) (for enterprise devices): For devices connected to a traditional corporate network, the recovery key can be backed up to AD DS. IT departments will usually manage this.
Knowing where you saved your key when BitLocker was first configured is the first and most crucial step in the recovery process.
Steps to Successfully Recover Your Drive
Once you have located your 48-digit BitLocker recovery key, the recovery process itself is straightforward:
- Enter the Key: On the BitLocker recovery screen, you will be prompted to enter the recovery key. Carefully type in all 48 digits. It’s often helpful to double-check each section of the key.
- Continue to Windows: After successfully entering the key, the system should proceed to boot into Windows normally.
- Investigate the Cause (Optional but Recommended): Once logged in, it’s advisable to investigate why BitLocker recovery was triggered. Check Windows Update history, review system logs (Event Viewer), and consider any recent hardware or firmware changes. This can help prevent future recovery prompts.
- Suspend/Resume BitLocker (if necessary): If you plan to make legitimate changes (like a BIOS update), you can temporarily “Suspend protection” in the BitLocker Drive Encryption control panel (
Control Panel > System and Security > BitLocker Drive Encryption). Remember to “Resume protection” afterward.
Common Pitfalls and Troubleshooting Tips
- Incorrect Key: Ensure you are entering the correct 48-digit key. There might be multiple keys if you have encrypted multiple drives or re-enabled BitLocker multiple times. Check the “Key Identifier” displayed on the recovery screen against the one associated with your saved key.
- Typo: It’s easy to make a typo. Take your time and verify each digit.
- Lost Key: If you cannot find your recovery key in any of the potential locations, data recovery becomes extremely difficult. Microsoft cannot recover the key for you. Professional data recovery services might be able to help in some extreme cases, but success is not guaranteed and often comes at a high cost.
- Keyboard Layout: Sometimes the keyboard layout on the recovery screen might differ from your usual one. Be mindful of special characters or number keys.
Best Practices for BitLocker Management and Prevention
Proactive management of BitLocker can significantly reduce the likelihood of encountering recovery scenarios and ensures a smoother experience should one occur. This foresight is a hallmark of intelligent tech management.
Secure Storage of Recovery Keys
The paramount best practice is to always store your BitLocker recovery key securely and separately from the device it encrypts.
- For personal users: Utilize the Microsoft account backup feature and consider a printed copy stored in a secure physical location (e.g., a safe deposit box or home safe).
- For organizations: Enforce policies for backing up keys to Active Directory or Azure AD, ensuring IT administrators have access. Regular audits of key storage are also recommended. Never store the key directly on the encrypted device itself.
Regular Backups and System Health Checks
While BitLocker protects against unauthorized access, it does not protect against data loss due to drive failure or accidental deletion. Regular backups of your critical data are essential, regardless of encryption status. Furthermore, maintaining system health by running antivirus scans, applying Windows updates, and monitoring drive health can help prevent unforeseen issues that might trigger BitLocker recovery. Understanding your system’s configuration and keeping track of hardware changes is also crucial.
User Education and Organizational Policies
In corporate environments, user education is key. Employees should be informed about the importance of BitLocker, how to properly handle recovery keys, and what actions might trigger recovery mode (e.g., changing boot settings). Clear organizational policies regarding BitLocker deployment, key management, and incident response for recovery scenarios are vital for maintaining a secure and productive environment. This integration of human behavior and technological protocols forms a robust security posture.
The Broader Implications of Data Encryption in Tech & Innovation
BitLocker, and indeed the concept of full-disk encryption, represents a critical pillar in the broader landscape of Tech & Innovation. It underscores the industry’s commitment to data privacy, regulatory compliance, and robust cybersecurity.
BitLocker’s Role in Compliance and Privacy
For many industries, data encryption is not just a best practice but a legal and regulatory requirement. Standards like GDPR, HIPAA, and PCI DSS often mandate the encryption of sensitive data. BitLocker provides an accessible and effective solution for organizations to meet these compliance obligations, helping them avoid hefty fines and reputational damage associated with data breaches. Its integration directly into the operating system makes it a compelling choice for businesses looking for streamlined security solutions without needing third-party software.
Future Trends in Encryption and Security
As technology evolves, so too do the methods of attack and defense. The field of encryption is constantly innovating, exploring new algorithms, quantum-safe encryption, and more sophisticated hardware-based security measures. BitLocker will undoubtedly continue to adapt, incorporating these advancements to provide ongoing protection in an ever-changing threat landscape. The intelligent design behind BitLocker recovery exemplifies a proactive approach to security, anticipating potential vulnerabilities and building in mechanisms to mitigate risks. It’s a testament to the ongoing innovation in cybersecurity, striving to keep pace with an increasingly complex digital world and reinforcing the principle that secure data is the foundation of digital trust.
