CEO Fraud, a sophisticated and increasingly prevalent form of Business Email Compromise (BEC) scam, operates by impersonating senior executives to deceive employees into transferring funds or divulging sensitive information. While the term “CEO Fraud” is widely recognized, several other designations capture the essence of this malicious activity, each highlighting a distinct facet of its modus operandi. Understanding these alternative names is crucial for a comprehensive grasp of the threat and for developing more targeted defensive strategies.
Understanding the Deception: Beyond the “CEO”
The core of CEO Fraud lies in the manipulation of trust and authority. Scammers leverage the hierarchical structure of organizations, targeting individuals who are accustomed to following directives from those in positions of power. The “CEO” in the title is merely the most common, but not the only, impersonated persona.
Executive Impersonation Scams
This broader term accurately reflects the reality that the scam is not limited to the chief executive officer. Perpetrators may pose as the Chief Financial Officer (CFO), Chief Operating Officer (COO), or any other high-ranking executive with the perceived authority to issue urgent financial instructions. The effectiveness of the scam often hinges on the perceived legitimacy of the sender’s role. By adopting the guise of a trusted leader, the attacker aims to bypass normal security protocols and elicit an immediate, unquestioning response.
The communication typically involves a sense of urgency and confidentiality. Employees may be instructed to act swiftly to close a deal, make a discreet payment, or secure a sensitive piece of information before a competitor or external auditor becomes aware. The lack of direct oversight and the emphasis on speed are designed to prevent the intended victim from verifying the legitimacy of the request through conventional channels, such as speaking directly with the purported executive or consulting with colleagues.
Spear Phishing Attacks with Executive Targeting
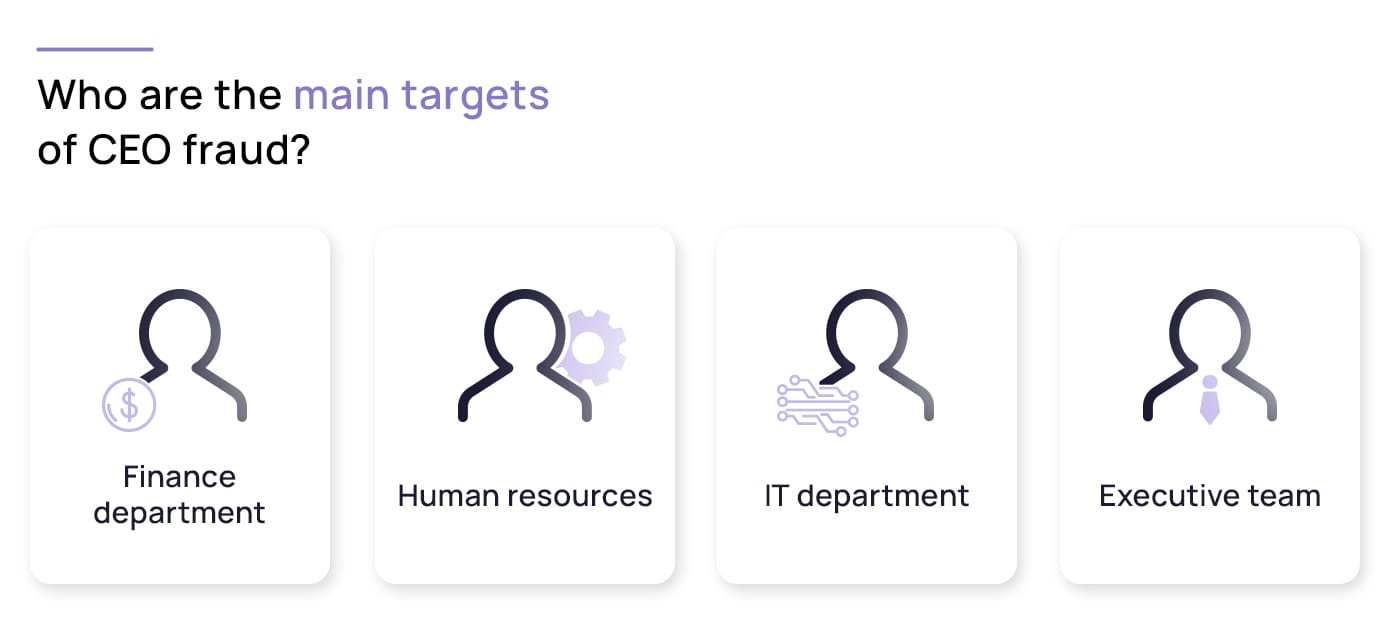
CEO Fraud is, in essence, a highly targeted form of spear phishing. Unlike broad-based phishing campaigns that cast a wide net, spear phishing meticulously researches its targets, gathering information about individuals, their roles, and their organizational structure. In the context of CEO Fraud, this research is focused on identifying key personnel in finance or accounts payable who have the authority to initiate wire transfers or access confidential data.
The “spear” aspect is crucial. The emails are crafted with personalized details, often referencing internal projects, upcoming mergers, or specific financial transactions. This level of customization makes the fraudulent email appear far more convincing than a generic phishing attempt. The attacker might even mimic the writing style and typical phrasing of the executive they are impersonating, further blurring the lines between authentic and malicious communication. The success of this approach is directly proportional to the depth of reconnaissance undertaken by the fraudster.
The “Whaling” Phenomenon
“Whaling” is a term frequently used as a synonym for CEO Fraud, and it vividly illustrates the high-stakes nature of these attacks. Just as a whaling ship targets the largest, most valuable prey, these scams aim for individuals at the highest levels of an organization or, more commonly, target employees who can fulfill significant financial requests from those at the top.
The term “whaling” emphasizes the elevated target profile. It’s not just any employee; it’s often someone in a finance department, a controller, or an executive assistant who has the direct ability to execute large monetary transfers. The perceived value of the “catch” for the attacker is substantial, making these scams particularly attractive to sophisticated criminal organizations. The psychological pressure on the targeted individual is also immense, as they are being commanded by what appears to be their direct superior to perform an action with potentially significant financial consequences.
The Mechanics of the Scam: Beyond Simple Email
While email is the primary vehicle for CEO Fraud, the methods employed are multifaceted and continuously evolving, often incorporating other digital communication channels and tactics to enhance credibility.
Business Email Compromise (BEC)
CEO Fraud is a specific subtype of the broader category of Business Email Compromise (BEC). BEC encompasses a range of fraudulent schemes where attackers use email to trick businesses into sending money to fraudulent accounts. CEO Fraud is characterized by the impersonation of a senior executive, but other BEC scams might involve impersonating vendors, legal counsel, or HR personnel.

The common thread across all BEC attacks is the exploitation of human trust and the circumvention of established financial controls. Attackers understand that simply sending an email requesting money is unlikely to succeed. Therefore, they employ elaborate social engineering tactics to create a sense of urgency, legitimacy, and confidentiality that compels the recipient to act without proper verification. The financial impact of BEC attacks, including CEO Fraud, has been estimated to be in the billions of dollars annually, underscoring the severity of this threat.
Wire Transfer Fraud
A significant proportion of CEO Fraud schemes culminate in wire transfer fraud. The imposter, posing as a CEO or other executive, instructs an employee to initiate an urgent wire transfer to a specific bank account. This account is typically controlled by the fraudsters and is often established to launder the illicitly obtained funds. The speed at which wire transfers occur makes them particularly attractive to criminals, as the money can be difficult to recover once it has been moved.
The instructions for these transfers are often detailed, specifying the amount, the beneficiary, and the purpose of the payment. This apparent specificity adds to the legitimacy of the request. The attacker may even provide fake invoice numbers or project codes to further solidify the illusion of a legitimate business transaction. The pressure to act quickly, often under the guise of a time-sensitive business opportunity or a critical supplier payment, is a key element in the success of these operations.
Gift Card Scams (A Less Common but Evolving Variant)
While less common for large-scale financial fraud, some variants of executive impersonation scams have extended to requesting employees purchase gift cards. In these instances, the imposter might claim that immediate payment is required for a business-related purpose, and that gift cards are the quickest way to settle the obligation. The reasoning provided can vary, from covering an urgent employee bonus to making a last-minute purchase for a client event.
These scams often target smaller businesses or specific departments where the perceived value of individual transactions is lower, making them less likely to trigger automated fraud detection systems. The attacker might then instruct the employee to provide the gift card codes, which can then be used by the fraudster to purchase goods or services online. This evolution highlights the adaptability of these criminal tactics, seeking new avenues to exploit unsuspecting individuals.
Identifying and Preventing the Threat
Recognizing the various names and manifestations of CEO Fraud is the first step in developing effective countermeasures. Organizations must foster a culture of security awareness and implement robust protocols to mitigate these risks.
The Importance of Verification Procedures
The most critical defense against CEO Fraud is the implementation of stringent verification procedures for all financial transactions, especially those initiated via email and involving significant sums. This means establishing clear policies that require verbal confirmation from a known, trusted contact (ideally the executive in question, via a known phone number, not one provided in the fraudulent email) before any wire transfer or payment is processed.
Segregating duties within the finance department can also add a layer of security. For instance, the person who receives a payment request should not be the same person who authorizes or executes the transfer. This separation of responsibilities creates a natural check and balance that can help catch fraudulent instructions before they result in financial loss. Regular training for employees on how to identify phishing and BEC attempts is also paramount.
Recognizing the Hallmarks of a Scam
Several red flags can indicate a CEO Fraud attempt. These include:
- Urgency and Secrecy: Requests that demand immediate action and emphasize the need for absolute confidentiality.
- Unusual Payment Methods: Requests for payment via wire transfer to a new or unusual beneficiary, or through non-standard channels like gift cards.
- Impersonated Email Addresses: Slight variations in an executive’s email address (e.g., a misspelled domain name or an extra character).
- Generic Greetings: While sophisticated attacks can be highly personalized, sometimes an email might begin with a generic greeting like “Dear Employee” or “Dear Team,” which is uncharacteristic of a direct executive communication.
- Grammar and Spelling Errors: While some attackers are highly skilled, less sophisticated attempts may contain noticeable grammatical errors or awkward phrasing that is inconsistent with the usual communication style of the purported executive.
- Requests to Bypass Normal Procedures: Any instruction to deviate from established company policies for financial transactions should be viewed with extreme suspicion.

The Role of Technology in Defense
While human vigilance is crucial, technology plays an increasingly important role in identifying and blocking these threats. Email security gateways with advanced threat detection capabilities can identify suspicious patterns, unusual sender behavior, and malicious links. Multi-factor authentication (MFA) for accessing critical systems, including email and financial platforms, adds a significant layer of security, making it harder for attackers to gain unauthorized access even if they obtain credentials.
Furthermore, organizations are increasingly employing AI-powered solutions that can analyze email content and sender behavior for anomalies indicative of BEC attacks. These systems can flag emails that exhibit characteristics of impersonation, such as unusual phrasing, inconsistent sender information, or unexpected financial requests. Implementing and regularly updating these technological defenses is a vital component of a comprehensive cybersecurity strategy against CEO Fraud and its many aliases.
