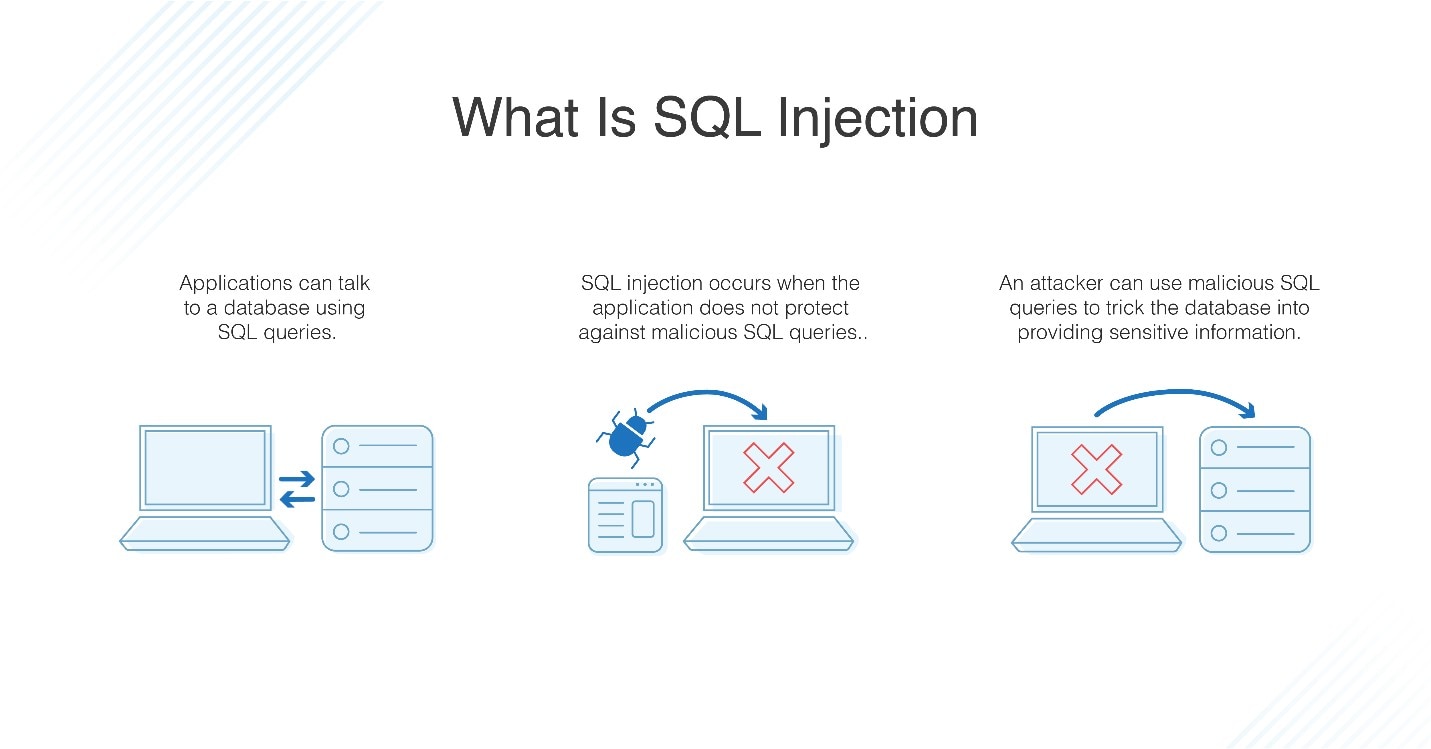
In the ever-evolving landscape of digital technology, where data is king and applications serve as the gateways to vast information repositories, the security of these systems is paramount. Among the myriad threats that loom over web applications and databases, one of the oldest, most prevalent, and potentially devastating is the SQL Injection (SQLi) attack. Far from being a relic of the past, SQLi remains a critical vulnerability that cybersecurity professionals tirelessly combat, and that developers must rigorously guard against. Understanding what an SQL injection attack is, how it works, and its profound implications is not just for security experts; it’s essential for anyone involved in building or maintaining web-connected systems.
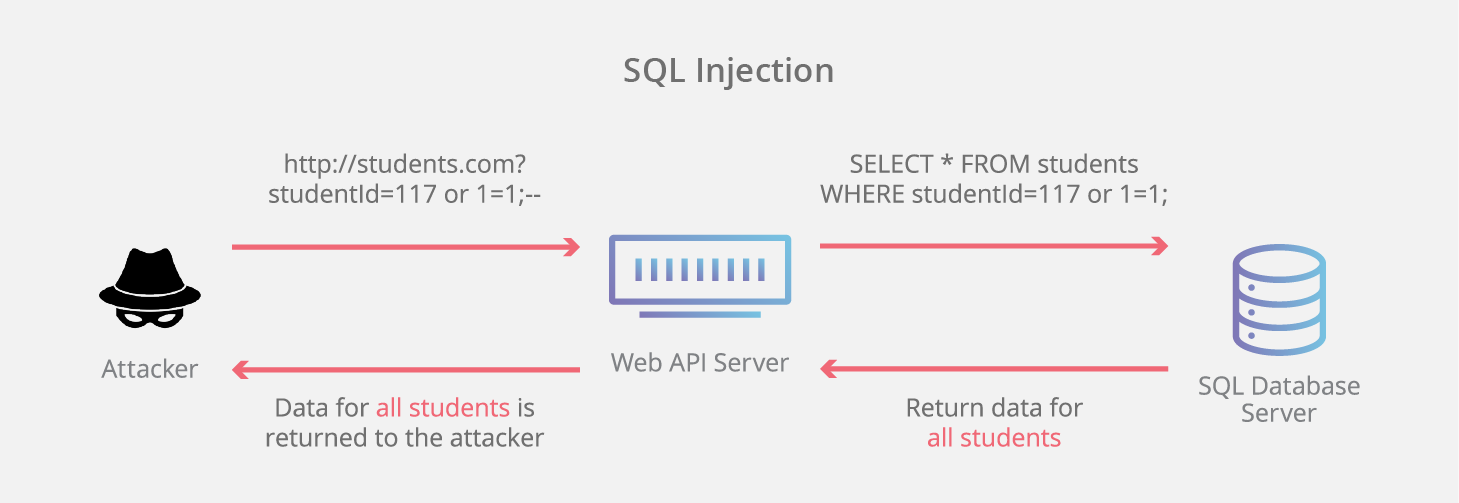
At its core, an SQL injection attack exploits a fundamental trust relationship: the trust a web application places in user input. When an application constructs SQL queries using concatenated user-supplied data without proper validation or sanitization, an attacker can inject malicious SQL code. This injected code then becomes part of the legitimate query, altering its intended logic and granting the attacker unauthorized access, manipulation, or even destruction of database content. It’s akin to speaking directly to the database, bypassing the application’s intended controls.
The Fundamental Concept: Understanding SQL and Injection
To fully grasp the mechanics of an SQL injection, it’s crucial to first understand the two core components involved: SQL itself and the “injection” process.
What is SQL?
SQL, or Structured Query Language, is the standard language used to communicate with and manage relational databases. Almost every dynamic web application, from e-commerce sites and social media platforms to corporate portals and banking systems, relies on databases to store and retrieve information. SQL commands allow applications to perform operations like:
- SELECT: Retrieving data from a database.
- INSERT: Adding new data into a database.
- UPDATE: Modifying existing data in a database.
- DELETE: Removing data from a database.
- CREATE/DROP: Defining or deleting database tables and structures.
When you log into a website, search for a product, or update your profile, an underlying SQL query is executed against the database to fulfill your request. For example, a login form might generate a query like: SELECT * FROM Users WHERE Username = 'user_input' AND Password = 'password_input';
The “Injection” Mechanism
The “injection” part of the attack occurs when an attacker manipulates the “user_input” in a way that tricks the database into executing malicious SQL code. Instead of providing the expected data, an attacker inputs specially crafted strings that include SQL syntax.
Consider a simple login scenario where an application uses a query like this:
SELECT * FROM Users WHERE Username = ' [username_from_form] ' AND Password = ' [password_from_form] ';
If a legitimate user enters john_doe and mypassword123, the query becomes:
SELECT * FROM Users WHERE Username = 'john_doe' AND Password = 'mypassword123';
Now, imagine an attacker enters ' OR '1'='1 into the username field and anything into the password field. The query then becomes:
SELECT * FROM Users WHERE Username = '' OR '1'='1' AND Password = ' [any_password] ';
The ' character closes the string for the username, the OR '1'='1' introduces a condition that is always true, and the final -- (or # in some SQL dialects) comments out the rest of the original query (including the password check). The resulting simplified query effectively becomes:
SELECT * FROM Users WHERE Username = '' OR TRUE;
Since TRUE is always met, this query would return the first user record in the database, potentially allowing the attacker to bypass authentication and log in as an administrator or the first user. This simple example highlights the core vulnerability: the application trusts and concatenates user input directly into an SQL query without distinguishing between data and executable code.
How SQL Injection Attacks Work: Common Scenarios
SQL injection attacks aren’t monolithic; they manifest in various forms, each exploiting different aspects of database interaction and error handling. Understanding these types helps in both identification and prevention.
Blind SQL Injection
Blind SQLi occurs when an attacker cannot directly see the results of their malicious query on the web page. Instead of receiving data back, the attacker infers information about the database by observing the application’s behavior or response times.
- Boolean-Based Blind SQLi: The attacker sends a query that evaluates to true or false. If the condition is true, the application’s response (e.g., page loads normally, specific content appears) is different from when it’s false (e.g., error message, no content). By systematically testing true/false conditions, attackers can extract data character by character.
- Time-Based Blind SQLi: Similar to Boolean-based, but instead of observing content changes, the attacker injects queries that cause the database to pause for a specified amount of time if a condition is true. For example,
IF(condition, SLEEP(5), 0). If the page takes 5 seconds longer to load, the attacker knows the condition was true. This method is slow but effective against systems that don’t provide explicit error messages.
Error-Based SQL Injection
In this type of attack, the attacker leverages verbose error messages generated by the database. If an application is configured to display database errors directly to the user, an attacker can intentionally craft queries that cause errors, forcing the database to reveal information such as table names, column names, or even data values within the error message itself. This method is often quicker than blind SQLi, as information is revealed more directly.
Union-Based SQL Injection
Union-based attacks exploit the UNION SELECT operator in SQL, which allows combining the results of multiple SELECT statements into a single result set. If an attacker can inject a UNION SELECT statement, they can retrieve data from other tables or databases within the same database instance and display it directly on the web page, alongside the legitimate query results. The challenge here is to match the number of columns and data types between the original query and the injected UNION SELECT query.
Out-of-Band SQL Injection
This is a less common but highly effective form of SQLi, used when an attacker cannot use the same channel to inject and retrieve results. Instead, the attacker makes the database perform an action that triggers a response outside the web application’s normal communication path, such as making an HTTP request to an attacker-controlled server or a DNS lookup. This method often relies on specific database features (e.g., UTL_HTTP in Oracle, xp_cmdshell in SQL Server) that allow the database to interact with external systems.
The Devastating Impact: Why It Matters
The consequences of a successful SQL injection attack can range from embarrassing data leaks to catastrophic system compromise, affecting confidentiality, integrity, and availability.
Data Breaches and Confidentiality Loss
This is perhaps the most common and damaging outcome. Attackers can gain access to sensitive information stored in the database, including:
- Personal Identifiable Information (PII): Usernames, passwords (often hashed, but sometimes plaintext), email addresses, phone numbers, home addresses.
- Financial Data: Credit card numbers, bank account details (though usually stored in encrypted forms or separate, highly secured systems, the risk remains).
- Proprietary Business Data: Trade secrets, customer lists, internal communications, intellectual property.
Such breaches lead to regulatory fines, reputational damage, and significant financial losses.
Data Integrity and Manipulation
Beyond merely reading data, SQL injection can allow attackers to modify or delete existing data, or insert entirely new, malicious data.
- Website Defacement: An attacker could alter content displayed on a website.
- Fraudulent Transactions: In an e-commerce context, an attacker might change product prices, order statuses, or even generate fraudulent orders.
- System Corruption: Deleting critical records or altering configuration settings could render an application or an entire system unusable.
Authentication Bypass and Privilege Escalation
As demonstrated in the basic example, SQLi can be used to bypass login credentials, allowing attackers to gain unauthorized access to an application. Once inside, they might further exploit vulnerabilities to escalate their privileges, moving from a regular user account to an administrator account, gaining control over critical application functions.
Remote Code Execution and Denial of Service
In some database systems and configurations, SQL injection can be leveraged to execute arbitrary commands on the underlying operating system of the server hosting the database. This is the holy grail for attackers, as it grants full control over the server. Alternatively, attackers can use SQLi to delete tables, drop databases, or overload the database with complex queries, leading to a Denial of Service (DoS) where legitimate users can no longer access the application.
Preventing SQL Injection: Best Practices and Defenses
Given the severe risks, preventing SQL injection is a paramount concern for developers and organizations. A multi-layered approach combining secure coding practices, robust configurations, and ongoing security testing is essential.
Prepared Statements with Parameterized Queries
This is the golden rule for preventing SQL injection and is considered the most effective defense. Instead of directly concatenating user input into an SQL query string, prepared statements separate the SQL code from the data. The query structure is defined first, with placeholders for user input, and then the user-supplied data is passed as parameters to these placeholders. The database treats parameters purely as data, never as executable SQL code.
Example (PHP PDO):
$stmt = $pdo->prepare("SELECT * FROM Users WHERE Username = :username AND Password = :password");
$stmt->bindParam(':username', $username);
$stmt->bindParam(':password', $password);
$stmt->execute();
This method ensures that even if an attacker enters ' OR '1'='1', it’s treated as a literal string value for the username, not as SQL code.
Input Validation and Sanitization
While prepared statements are the primary defense, robust input validation and sanitization act as an important secondary layer.
- Validation: Ensure that user input conforms to expected formats (e.g., an email address should look like an email, a number should be numeric). Reject input that doesn’t meet these criteria.
- Sanitization: Remove or encode potentially malicious characters from user input before it’s processed. For example, escaping single quotes (
') or other special characters. This should be used cautiously and is not a substitute for parameterized queries, but it can help against other injection types (like XSS) and provides an additional layer of safety.
Least Privilege Principle
Database users and application accounts should operate with the minimum necessary privileges. If an application only needs to read data from a specific table, its database user should not have permissions to delete tables, modify database schemas, or access other sensitive data. This limits the damage an attacker can inflict if an SQLi vulnerability is successfully exploited.
Web Application Firewalls (WAFs)
A Web Application Firewall (WAF) sits between the user and the web application, inspecting incoming HTTP requests and outgoing HTTP responses. WAFs can detect and block known SQL injection attack patterns, providing an external layer of defense. While WAFs are not a magic bullet and should not replace secure coding, they offer valuable protection by filtering malicious traffic before it reaches the application.
Regular Security Audits and Penetration Testing
Even with best practices in place, vulnerabilities can still creep into complex applications. Regular security audits, code reviews, and penetration testing (simulated attacks by ethical hackers) are crucial to identify and fix SQL injection flaws before malicious actors can exploit them. Automated static and dynamic application security testing (SAST/DAST) tools can also aid in this process.
Real-World Examples and Evolution
SQL injection is not a theoretical threat; it has been the root cause of some of the most significant data breaches in history. From government websites to major corporations, the trail of compromised data is extensive. Notable examples include attacks against Sony, Heartland Payment Systems, and various government agencies, leading to millions of records being exposed.
The evolution of SQL injection hasn’t been about changing the core principle, but rather about sophistication and automation. Attackers now use advanced tools that can automatically scan websites for SQLi vulnerabilities, probe them with various techniques (including blind and time-based), and even extract entire databases with minimal manual intervention. The development of next-generation databases and ORM (Object-Relational Mapping) frameworks has made parameterized queries the default, significantly reducing the prevalence of simple SQLi. However, custom legacy codebases and misconfigurations still leave a vast attack surface.
In conclusion, an SQL injection attack represents a critical flaw in the interaction between web applications and their underlying databases. By exploiting trust and insufficient input handling, attackers can gain unparalleled access to sensitive information, manipulate data, and compromise entire systems. While the techniques for SQLi have evolved, the fundamental defense remains consistent: never trust user input. Through the diligent application of prepared statements, input validation, the principle of least privilege, and continuous security scrutiny, developers can build robust applications that stand resilient against this persistent and dangerous cyber threat.
