IP spoofing is a cybersecurity technique where a malicious actor disguises network traffic originating from an unknown source as if it were coming from a known and trusted IP address. This deception is a critical tool in the arsenal of cybercriminals, enabling them to bypass security measures, launch more sophisticated attacks, and obscure their true origins. Understanding IP spoofing is paramount for anyone involved in network security, whether managing a small business network or a large enterprise infrastructure.
The Mechanics of IP Spoofing
At its core, IP spoofing exploits the fundamental trust inherent in many network protocols. The Internet Protocol (IP) is responsible for addressing and routing data packets across networks. Each packet contains a header, which includes the source IP address (where the packet originated) and the destination IP address (where it’s intended to go). In a standard, non-spoofed communication, the source IP address accurately reflects the origin of the packet. However, in IP spoofing, the attacker manipulates this header, replacing their actual IP address with a forged one.
How It Works: Packet Manipulation
The process typically involves the attacker crafting network packets with a falsified source IP address. This can be achieved through various methods, often requiring a degree of technical expertise.
- Direct Packet Crafting: Tools exist that allow attackers to manually construct IP packets, including the header fields. They can then inject these packets into the network, specifying any source IP address they desire. This is particularly effective in internal networks where the attacker might have already gained a foothold.
- Exploiting Network Protocols: Certain older or less secure network protocols might be more susceptible to IP spoofing. For instance, some protocols might rely on source IP addresses for authentication or trust without performing robust verification.
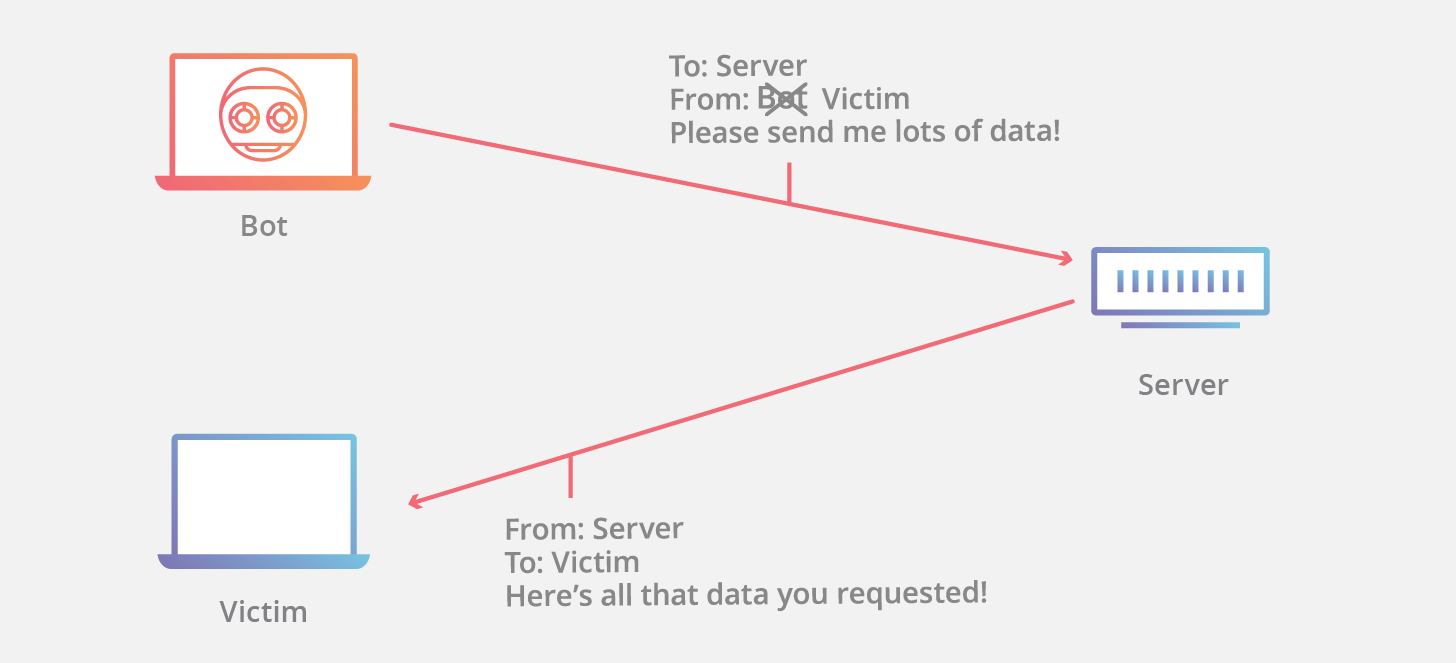
- Botnets and Compromised Machines: A common scenario involves attackers using a botnet – a network of compromised computers controlled remotely – to launch spoofed attacks. Each compromised machine can be instructed to send packets with a spoofed source IP, making it significantly harder to trace the true origin of the attack. The attacker might spoof the IP address of a trusted server on the target network, or even the IP address of the victim themselves (a technique known as “smiley face attack”).
The Illusion of Trust
The effectiveness of IP spoofing hinges on the concept of network trust. Many network protocols and security systems operate on the assumption that traffic originating from a specific IP address is genuinely from that address. For example, older firewall rules might allow all traffic from a trusted internal IP range. If an attacker can spoof an IP address from that trusted range, they can potentially bypass these defenses.
Similarly, some authentication mechanisms rely on the source IP address. If a system trusts traffic from a particular IP address for administrative access, an attacker spoofing that IP could gain unauthorized entry. This reliance on IP-based trust, while often simplifying network management, creates a vulnerability that IP spoofing exploits.
Common Types of IP Spoofing Attacks
IP spoofing is not a standalone attack but rather a foundational technique used to facilitate a variety of malicious activities. The objective is usually to gain an advantage, evade detection, or directly harm the target.
Denial of Service (DoS) and Distributed Denial of Service (DDoS) Attacks
One of the most prevalent applications of IP spoofing is in orchestrating DoS and DDoS attacks. In a DoS attack, the goal is to overwhelm a target system (like a web server) with traffic, rendering it unavailable to legitimate users.
- Standard DoS: An attacker uses a single machine to flood the target with requests. If the source IP is spoofed, the target cannot simply block the attacking IP address because the requests appear to be coming from many different, and potentially legitimate, sources.
- DDoS: This is a more potent version where multiple compromised machines (a botnet) simultaneously launch attacks. When combined with IP spoofing, it becomes incredibly difficult to mitigate. The sheer volume of traffic, originating from seemingly legitimate but spoofed IPs, can cripple even robust systems. A common DDoS technique leveraging spoofing is the SYN flood. The attacker sends a large number of TCP SYN packets (the first step in establishing a connection) with a spoofed source IP. The target server responds with a SYN-ACK packet to the spoofed IP and waits for an ACK, allocating resources for each pending connection. Since the spoofed IP is not a real client, the ACK never arrives, and the server’s resources are exhausted, leading to a denial of service.
Man-in-the-Middle (MitM) Attacks
While not directly an IP spoofing attack, IP spoofing can be a precursor or a supporting element in MitM attacks. In a MitM attack, an attacker secretly intercepts and potentially alters the communication between two parties who believe they are communicating directly with each other.
- ARP Spoofing: A common method to achieve MitM within a local network is Address Resolution Protocol (ARP) spoofing. ARP maps IP addresses to MAC addresses. An attacker can send falsified ARP messages, claiming that their MAC address corresponds to the IP address of the default gateway or another critical server. When other devices on the network receive these spoofed ARP messages, they update their ARP tables accordingly. Consequently, their traffic intended for the legitimate gateway is instead routed to the attacker’s machine. The attacker can then forward the traffic to the actual gateway, effectively becoming a transparent interceptor, and potentially eavesdrop on or modify the data.
Evasion of Security Measures and Authentication
IP spoofing can be used to circumvent security controls that rely on IP addresses for identification and access control.
- Bypassing Firewalls: As mentioned earlier, firewalls configured to trust traffic from certain IP ranges can be fooled by spoofed packets originating from outside those ranges but appearing to come from within.
- Impersonating Trusted Hosts: An attacker might spoof the IP address of a legitimate, trusted server within an organization. If other internal systems grant elevated privileges or access based on the source IP of this trusted server, the attacker can exploit this to gain unauthorized access.
- Bypassing Intrusion Detection Systems (IDS): Some IDSs might be configured to alert or block traffic from known malicious IP addresses. By spoofing a legitimate IP address, an attacker can make their malicious traffic appear to originate from a trusted source, potentially avoiding detection.
Other Exploits
- Session Hijacking: In certain scenarios, an attacker might use IP spoofing to hijack an established TCP session. By predicting or knowing the sequence numbers of a legitimate session, an attacker could inject packets with the spoofed source IP and the correct sequence numbers, causing the victim’s machine to accept the attacker’s packets as part of the legitimate session.
- Exploiting Vulnerabilities in UDP-based Protocols: Many UDP-based protocols, which are connectionless, are more susceptible to IP spoofing because they don’t involve the handshake process that TCP uses to verify endpoints. This makes them ideal for quick, fire-and-forget spoofed attacks.
The Challenge of Detection and Mitigation
Detecting and mitigating IP spoofing attacks presents a significant challenge for network administrators due to their inherent deceptive nature. The very act of spoofing aims to make malicious traffic appear legitimate.
Detection Difficulties
- Appearing Legitimate: The core problem is that spoofed packets, when traversing intermediate networks, often appear as normal traffic. If an attacker is spoofing an IP address that is within the same subnet as the target or a trusted internal IP, it becomes even harder to distinguish malicious packets from benign ones.
- Distributed Nature: In DDoS attacks, the spoofed IPs can be highly randomized, making it difficult to pinpoint a single source to block. The attack traffic can appear to originate from thousands or even millions of different IP addresses simultaneously.
- Lack of Return Path: A key indicator of spoofing is that the attacker has no genuine network path to receive return traffic from the target. However, detecting this absence of a return path in real-time across a complex network can be challenging. For instance, if a server sends a response to a spoofed IP address, that response will go to an IP address that is not expecting it and has no connection to the original request.
Mitigation Strategies
Despite the difficulties, several strategies can be employed to reduce the risk and impact of IP spoofing.
- Ingress and Egress Filtering: This is one of the most effective preventive measures.
- Ingress Filtering: Network administrators should configure routers to drop incoming packets that have source IP addresses that do not belong to the network’s address space. For example, if a network is assigned the IP range 192.168.1.0/24, any incoming packet with a source IP outside of this range should be discarded by the edge router. This prevents attackers from the outside from spoofing internal IP addresses.
- Egress Filtering: Similarly, routers should be configured to drop outgoing packets that have source IP addresses that do not belong to the network’s address space. This prevents compromised internal machines from launching spoofed attacks against external targets.
- Using Stronger Authentication Mechanisms: Relying solely on IP addresses for authentication is inherently risky. Implementing more robust authentication methods, such as multi-factor authentication (MFA), certificates, or more sophisticated behavioral analysis, can significantly enhance security.
- Intrusion Detection and Prevention Systems (IDPS): While they can be bypassed by sophisticated spoofing, IDPS can still play a role. By analyzing traffic patterns, anomaly detection, and known attack signatures, IDPS can flag suspicious activity that might indicate spoofing, even if the source IP is disguised. Rate limiting and behavioral analysis within IDPS can help identify unusual traffic spikes.
- Firewall Configuration: Properly configuring firewalls to restrict traffic based on port, protocol, and originating IP address is crucial. While not a complete solution for spoofing, it can limit the attack surface.
- Network Segmentation: Dividing a network into smaller, isolated segments can limit the blast radius of a spoofed attack. If an attacker manages to gain access to one segment, it becomes harder for them to reach other critical parts of the network through spoofing.
- Rate Limiting: Implementing rate limiting on network devices can help mitigate the impact of DoS/DDoS attacks that use spoofing by restricting the number of packets or connections allowed from any given source within a specific timeframe.
- Using TCP Sequence Number Prediction Resistance: For applications that rely on TCP, employing mechanisms that make it harder to predict sequence numbers can help prevent session hijacking via spoofing.
- Collaboration and Information Sharing: Staying informed about emerging threats and vulnerabilities, and collaborating with other security professionals and organizations, can provide valuable insights into new spoofing techniques and effective countermeasures.

The Future of IP Spoofing and Cybersecurity
As networks become more complex and the sophistication of cyberattacks continues to evolve, IP spoofing will remain a relevant threat. The ongoing adoption of technologies like IPv6, with its vast address space, introduces new considerations for IP spoofing. While IPv6 offers more robust security features, misconfigurations and legacy vulnerabilities can still create opportunities for attackers.
The continuous arms race between attackers and defenders means that cybersecurity professionals must remain vigilant, adapting their strategies to counter new methods of deception. The fundamental principle of verifying the true origin of network traffic, rather than simply trusting the source IP address, is key to building a resilient defense against IP spoofing and the myriad of attacks it enables. By understanding the mechanics, recognizing the common attack vectors, and implementing robust mitigation strategies, organizations can significantly reduce their vulnerability to this pervasive cyber threat.
