In the rapidly evolving landscape of technology and innovation, where digital interactions form the backbone of almost every system, the concept of identity has become paramount. From securing vast enterprise networks to managing user access for cutting-edge autonomous systems or safeguarding data in remote sensing applications, robust identity management is no longer a luxury but an absolute necessity. At the heart of this digital security paradigm lies the Identity Provider (IdP) – a foundational component that streamlines and secures how users prove who they are across various digital services.
An Identity Provider is, fundamentally, a system that creates, maintains, and manages identity information for principals (users, services, or other entities) and then provides authentication services to relying party applications within a distributed network. Imagine a central authority that vouches for your identity to multiple different online services, saving you the hassle of creating a new account and remembering a new password for each one. This is the core function of an IdP. In an era where digital ecosystems are becoming increasingly interconnected and complex, IdPs are the silent architects ensuring both security and user convenience. They are indispensable for enabling seamless, secure access to the myriad innovative technologies that define our modern world, from AI-powered platforms to sophisticated mapping and remote sensing solutions that demand high levels of data integrity and authorized access.
The Cornerstone of Modern Digital Security: Understanding Identity Providers (IdPs)
The digital age is characterized by an explosion of online services, applications, and platforms, each often requiring users to authenticate their identity. Without a standardized approach, users would face “identity fatigue” – the tedious process of creating and managing countless unique usernames and passwords. More critically, each service would bear the significant burden and security risk of managing user credentials and performing authentication independently. This fragmented approach is inefficient, prone to security vulnerabilities, and detrimental to user experience.
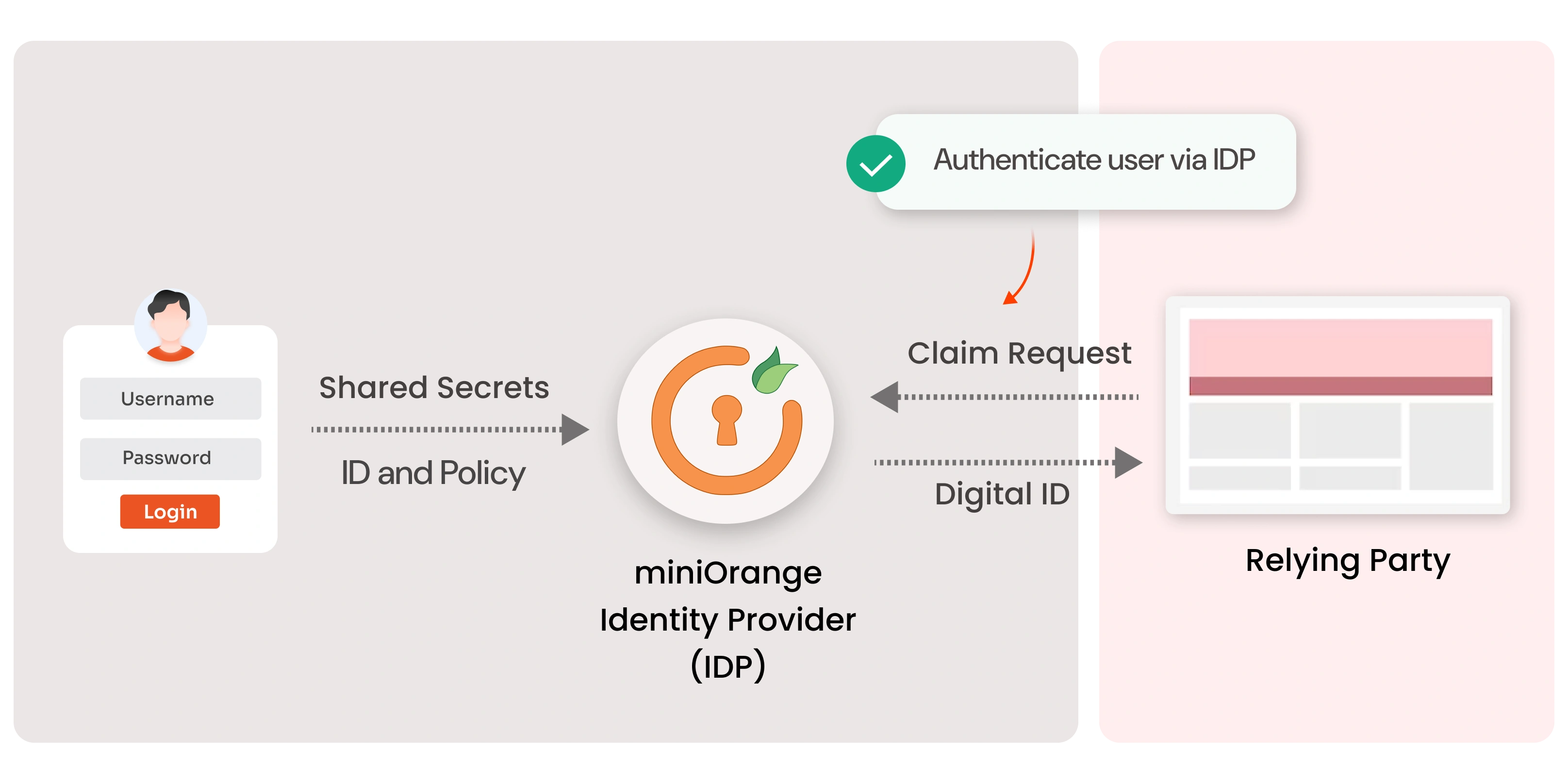
An Identity Provider emerges as the elegant solution to this sprawling challenge. It acts as a trusted entity that authenticates a user’s identity once and then issues an assertion (a digitally signed statement) that this identity is valid. Other services, known as Service Providers (SPs) or Relying Parties (RPs), trust the IdP’s assertion and grant the user access without needing to store or re-verify their credentials. This model fundamentally shifts the responsibility of identity management from individual services to a centralized, specialized entity, dramatically improving overall security posture and user convenience.
In the context of modern tech and innovation, where complex systems often interact across different domains (e.g., an autonomous system needing access to cloud-based mapping data, or an AI model requiring authenticated input from various data sources), IdPs are crucial. They facilitate secure, interoperable communication and access control, ensuring that only authorized entities can interact with sensitive data and functionalities. This centralized approach reduces the attack surface, simplifies compliance efforts, and enables rapid scaling of new services without re-inventing the authentication wheel each time.
Why IdPs are Indispensable for Innovative Tech Ecosystems
The relevance of IdPs in advanced technological contexts cannot be overstated. Consider platforms that leverage AI for data analysis, complex autonomous flight systems, or remote sensing infrastructures that collect and process vast amounts of sensitive information. Each of these requires stringent access control.
- Enhanced Security: By centralizing authentication, IdPs can implement advanced security measures like multi-factor authentication (MFA), adaptive authentication, and continuous threat monitoring more effectively than individual service providers. This significantly reduces the risk of credential theft and unauthorized access.
- Improved User Experience: Single Sign-On (SSO) is a prime benefit of IdPs, allowing users to log in once and gain access to multiple connected applications without re-entering credentials. This seamless experience is vital for complex workflows common in innovative tech environments.
- Scalability and Agility: As new services and applications are developed, integrating them with an existing IdP is far more efficient than building bespoke authentication for each. This agility is critical for rapid innovation cycles.
- Compliance and Governance: Centralized identity management simplifies auditing and helps organizations meet regulatory compliance requirements (e.g., GDPR, HIPAA) by providing a clear audit trail of who accessed what, when.
- Interoperability: IdPs facilitate secure interaction between disparate systems and organizations, which is essential for collaborative innovation, supply chain integration, and data sharing initiatives.
How Identity Providers Work: A Deep Dive into Authentication Flows
Understanding the mechanics of an IdP involves exploring the protocols and processes that enable secure and efficient identity verification. The magic often happens behind the scenes, governed by well-established standards that dictate how an IdP communicates with Service Providers (SPs).
Key Protocols and Standards
Several industry-standard protocols underpin the functionality of Identity Providers:
- SAML (Security Assertion Markup Language): An XML-based standard that enables secure cross-domain communication of user authentication and authorization data. SAML is particularly prevalent in enterprise environments and for web-based SSO, allowing a user to authenticate once at an IdP and then access multiple cloud applications without re-authenticating. The IdP creates a SAML assertion (a digitally signed XML document) that contains information about the authenticated user, which the SP then trusts.
- OAuth (Open Authorization): Not an authentication protocol itself, but rather an authorization framework. OAuth allows a user to grant a third-party application limited access to their resources on another service without exposing their credentials. For example, allowing a photo editing app to access your images on a cloud storage service.
- OpenID Connect (OIDC): Built on top of OAuth 2.0, OIDC adds an identity layer that enables clients to verify the identity of the end-user based on the authentication performed by an authorization server (which can act as an IdP). OIDC provides information about the user in a JSON Web Token (JWT), making it lightweight and suitable for mobile and modern web applications. It has become a de facto standard for consumer-facing identity systems.
- LDAP (Lightweight Directory Access Protocol) / Active Directory: While not an IdP in the modern sense of issuing assertions, these are often the underlying directories where user identities are stored and managed within an organization. Many IdPs integrate with or leverage these directories to authenticate users.
The Authentication Flow: A Simplified Overview
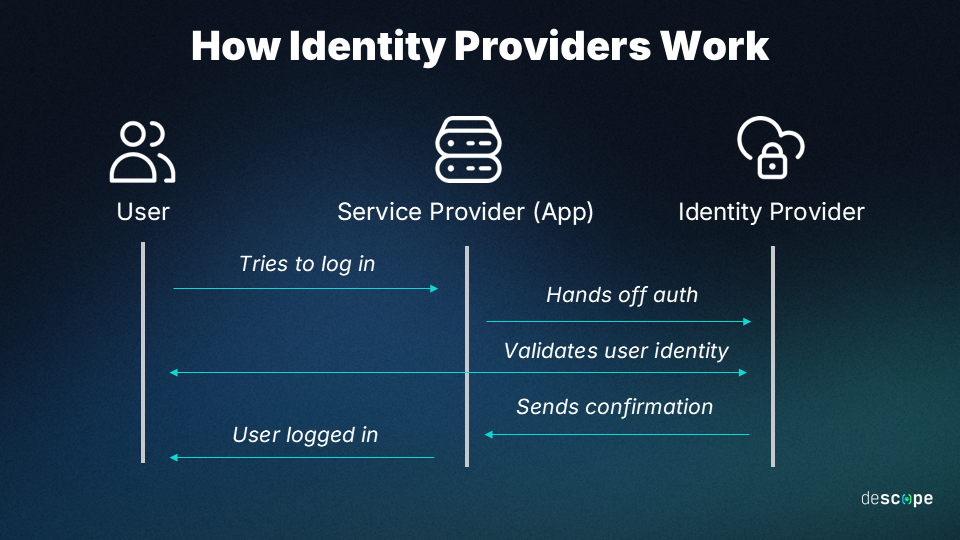
The typical interaction between a user, an SP, and an IdP follows a well-defined flow, often initiated by the user attempting to access a resource on an SP:
- Request for Access: A user attempts to access a protected resource on a Service Provider (e.g., a specific dashboard in a remote sensing application).
- Redirection to IdP: The SP recognizes that the user is not authenticated and redirects the user’s browser to the designated IdP for authentication. This redirection often includes information about which SP initiated the request.
- User Authentication: The IdP prompts the user for their credentials (username/password, biometrics, etc.). Upon successful verification against its stored identities, the IdP authenticates the user.
- Assertion/Token Issuance: The IdP generates a cryptographically signed assertion (SAML) or an ID token (OIDC) containing information about the authenticated user, potentially including attributes like their name, email, and roles.
- Redirection back to SP: The IdP redirects the user’s browser back to the SP, including the signed assertion or token.
- Verification and Access Grant: The SP receives the assertion/token, verifies its cryptographic signature using the IdP’s public key (ensuring it hasn’t been tampered with and comes from a trusted IdP), and processes the user’s identity information. If valid, the SP grants the user access to the requested resource.
This process ensures that the SP never sees the user’s actual credentials, only the IdP’s trusted confirmation of identity, significantly enhancing security.
Key Benefits of Implementing an IdP in Innovative Tech Ecosystems
For organizations pushing the boundaries of technology, integrating a robust Identity Provider is not merely a technical decision; it’s a strategic imperative that underpins operational efficiency, security, and user adoption.
Streamlined User Experience with Single Sign-On (SSO)
One of the most tangible benefits of an IdP is the enablement of Single Sign-On (SSO). In complex tech environments, users often interact with a multitude of applications – development tools, project management platforms, data analysis dashboards, and various operational interfaces (e.g., for managing autonomous systems). Without SSO, each requires separate authentication, leading to password fatigue, forgotten credentials, and significant productivity loss. SSO, powered by an IdP, allows users to log in once with a single set of credentials and seamlessly access all authorized applications. This dramatically improves user satisfaction and reduces helpdesk calls related to password resets, freeing up IT resources for more strategic tasks.
Fortified Security Posture and Centralized Control
IdPs centralize the critical function of authentication, allowing for the consistent application of advanced security policies across all connected services.
- Reduced Attack Surface: User credentials are only stored and managed in one place (the IdP), rather than being scattered across numerous applications. This significantly shrinks the attack surface for cyber adversaries.
- Advanced Authentication Mechanisms: IdPs are designed to support and enforce robust authentication methods, including multi-factor authentication (MFA) – such as biometrics, hardware tokens, or one-time passcodes – which adds crucial layers of security beyond simple passwords. They can also implement adaptive authentication, adjusting security requirements based on contextual factors like user location or device.
- Centralized Auditing and Logging: All authentication events are logged and managed by the IdP, providing a comprehensive audit trail critical for security monitoring, incident response, and regulatory compliance.
Scalability and Agility for Rapid Innovation
Innovative tech companies thrive on rapid development and deployment of new features and services. An IdP significantly accelerates this process:
- Faster Onboarding of New Applications: Integrating new applications into the ecosystem becomes a matter of configuring them to trust the existing IdP, rather than building bespoke authentication logic for each. This dramatically reduces development time and costs.
- Efficient User Lifecycle Management: Managing user accounts (provisioning, de-provisioning, role changes) is simplified through the IdP. When an employee joins or leaves, their access to all integrated applications can be managed from a single point, ensuring immediate access revocation for security.
- Support for Diverse Technologies: Modern IdPs support various protocols (SAML, OIDC) and integration points, making them adaptable to heterogeneous tech stacks, from legacy systems to cutting-edge cloud-native applications and microservices architectures.
Types of Identity Providers and Their Applications in Emerging Technologies
The landscape of Identity Providers is diverse, catering to different scales, use cases, and deployment models. Understanding these variations is crucial for selecting the right IdP strategy for various innovative tech applications.
Cloud-Based IdPs (Identity-as-a-Service – IDaaS)
Cloud-based IdPs, also known as Identity-as-a-Service (IDaaS) providers, offer identity management and authentication services hosted in the cloud. They are often SaaS (Software-as-a-Service) offerings, managed by a third party.
- Examples: Okta, Auth0, OneLogin, Microsoft Azure AD, Google Cloud Identity.
- Applications in Emerging Technologies:
- Startup Agility: Ideal for startups and smaller tech companies that need robust identity infrastructure without the overhead of managing on-premise solutions.
- Hybrid/Multi-cloud Environments: Seamlessly integrate with various cloud services, essential for companies leveraging diverse cloud platforms for AI model training, data storage for remote sensing, or IoT device management.
- Developer-Friendly Integration: Many IDaaS platforms offer extensive APIs and SDKs, enabling developers to quickly integrate secure authentication into new applications, machine learning platforms, or autonomous system control interfaces.
- Global Scalability: Easily scale to support a global user base, crucial for consumer-facing innovative apps or globally deployed remote sensing projects.
Enterprise On-Premise IdPs
These are identity systems managed and hosted within an organization’s own data centers. They offer maximum control and customization but come with higher operational overhead.
- Examples: Microsoft Active Directory Federation Services (AD FS), PingFederate.
- Applications in Emerging Technologies:
- Highly Regulated Industries: Organizations in sectors with stringent compliance requirements (e.g., defense contractors managing autonomous vehicle projects, financial institutions developing AI trading algorithms) often prefer the control offered by on-premise solutions.
- Legacy System Integration: Necessary for integrating modern applications with existing legacy systems and directories that cannot easily migrate to the cloud.
- Sensitive Data Environments: For highly sensitive internal systems, like those involved in classified mapping projects or proprietary AI research, where data locality and absolute control are paramount.
Social Identity Providers
These are consumer-facing IdPs provided by major social media or tech companies, allowing users to log in to third-party applications using their existing social accounts.
- Examples: Google, Facebook, Apple, Twitter login.
- Applications in Emerging Technologies:
- Consumer-Facing Apps: Highly effective for innovative applications targeting a broad consumer base, such as drone piloting apps, citizen science platforms for remote sensing data contribution, or AR/VR experiences, where ease of onboarding is critical.
- Reduced Friction: Lowers the barrier to entry for new users, as they don’t need to create a new account, fostering faster adoption of new technologies.
The choice of IdP type often depends on the specific requirements of the innovative tech project – its scale, security needs, integration complexity, and target user base.
Challenges and Future Trends in Identity Management for the Age of Innovation
While Identity Providers offer immense benefits, the dynamic nature of technology also presents evolving challenges and exciting future trends in identity management. For the age of innovation, these aspects are not just about overcoming hurdles but about shaping the next generation of secure and seamless digital interactions.
Navigating Privacy Concerns and Data Sovereignty
As IdPs centralize user data, privacy becomes a paramount concern. With innovations in data analysis and AI, the potential for using identity data in unforeseen ways raises ethical and regulatory questions. Future IdP solutions must not only comply with strict data protection regulations (like GDPR, CCPA) but also offer users greater transparency and control over their personal information. Data sovereignty, particularly for global tech deployments (e.g., remote sensing projects spanning multiple continents), requires careful consideration of where identity data is stored and processed. Innovative IdP architectures will need to incorporate privacy-by-design principles, differential privacy techniques, and consent management frameworks more robustly.
The Rise of Decentralized Identity (DID)
A significant future trend is the emergence of Decentralized Identity (DID). Unlike traditional IdPs, which are centralized authorities, DIDs leverage blockchain or other distributed ledger technologies to give individuals sovereign control over their digital identities. Users would own and manage their own verifiable credentials (e.g., a pilot license, a university degree) issued by trusted organizations, rather than relying on a third-party IdP to vouch for them.
- Implications for Innovation:
- Enhanced User Privacy: Users share only the specific information required, without exposing their entire identity profile to a central IdP or multiple SPs.
- Trust without Intermediaries: Reduces reliance on central authorities, potentially enhancing trust in highly sensitive applications like secure data exchange between autonomous systems or verifying the authenticity of data sources in critical mapping projects.
- Self-Sovereign Identity: Empowers users, which could drive adoption in communities wary of centralized data control.
While still in its nascent stages, DID holds transformative potential for identity management, particularly for secure data sharing and verification in highly distributed and trust-sensitive innovative ecosystems.
Passwordless Authentication and Beyond
The traditional username-password model is increasingly recognized as a weak link in security. Future IdPs are moving aggressively towards passwordless authentication.
- Biometrics: Fingerprint scans, facial recognition, and iris scans are becoming common, offering both security and convenience.
- FIDO (Fast IDentity Online) Standards: FIDO alliances are promoting open standards for stronger authentication that eliminates passwords, using methods like public-key cryptography tied to devices. This is crucial for securing devices in the IoT realm or remote controllers for advanced systems.
- Behavioral Biometrics: Analyzing unique user behaviors (typing patterns, mouse movements) to continuously verify identity.
- AI and Machine Learning in Identity: AI is being leveraged to enhance fraud detection, analyze login patterns for anomalies, and power adaptive authentication systems that dynamically adjust security requirements based on context and risk. This is particularly relevant for securing access to complex AI-driven platforms themselves.
Seamless Integration with AI and Autonomous Systems
As AI becomes more pervasive, IdPs will need to evolve to manage not just human identities but also the identities of AI agents, autonomous systems, and IoT devices (Machine-to-Machine Identity). Securely authenticating and authorizing these non-human entities will be critical for the integrity and safety of future innovations, especially in areas like autonomous flight or smart city infrastructure. This requires IdPs to support standards for device identity, credential provisioning for edge devices, and secure API access for machine-to-machine communication.
In conclusion, Identity Providers are fundamental pillars supporting the security, usability, and scalability of modern tech and innovation. As technology continues its relentless march forward, the role of IdPs will only grow in complexity and importance, adapting to new challenges and embracing groundbreaking solutions to secure our increasingly interconnected digital world.
