In the increasingly interconnected digital landscape, the security of our personal data and online accounts has become paramount. Apple, a leading technology company, offers robust security features to protect its users, and a crucial component of this security infrastructure is the recovery key. This enigmatic phrase, often encountered during account setup or security checks, plays a vital role in safeguarding your digital life. Understanding what a recovery key is, how it functions, and how to manage it effectively is essential for maintaining the integrity of your Apple ID and the sensitive information it controls.
The concept of a recovery key stems from the need for a secure, yet accessible, method to regain control of an account if the primary means of authentication are compromised or lost. For Apple, this translates into a multi-layered security approach, where the recovery key acts as a last resort, an ultimate failsafe designed to prevent permanent lockout from your digital ecosystem. It’s not a password you use daily, but rather a powerful tool for extreme circumstances, ensuring that even if you forget your password, lose your trusted devices, or your two-factor authentication becomes inaccessible, your Apple ID and its associated data remain within your reach.
The Pillars of Apple ID Security
Apple’s approach to account security is built upon a foundation of robust authentication mechanisms designed to protect users from unauthorized access. The recovery key is a vital, albeit often overlooked, element within this comprehensive security framework. To truly appreciate the significance of a recovery key, it’s important to understand the other layers of protection Apple employs.
Two-Factor Authentication (2FA): The First Line of Defense
Two-factor authentication is the cornerstone of modern account security, and Apple has integrated it deeply into its ecosystem. When you sign in to your Apple ID on a new device or browser, after entering your password, you’ll be prompted to enter a six-digit verification code. This code is either displayed on your trusted Apple devices (like your iPhone, iPad, or Mac) or sent via SMS to a trusted phone number. This significantly reduces the risk of account compromise, as an attacker would need not only your password but also physical access to one of your trusted devices or your phone.
The presence of trusted devices and phone numbers is critical for 2FA. These are devices and numbers that you have previously verified and associated with your Apple ID. Apple uses these to ensure that only you can access your account. If you were to get a new iPhone, for example, and try to sign in with your Apple ID, you would be prompted to enter your password, and then a verification code would appear on your old iPhone (if it’s still logged in and connected) or be sent to your trusted phone number. This is where the recovery key starts to become relevant.
Trusted Devices and Phone Numbers: The Helpers in Your Security Journey
Trusted devices and phone numbers are not just passive recipients of verification codes. They are active participants in your Apple ID’s security. When you enable 2FA, you designate specific devices and phone numbers as “trusted.” These devices are logged into your Apple ID, and your trusted phone number receives verification codes. If you lose your primary device, you can still potentially access your account from another trusted device. Similarly, if you lose access to your primary device’s connectivity, you can still receive codes via SMS to your trusted phone number.
However, what happens if you lose all your trusted devices and no longer have access to your trusted phone number? This is the scenario where the recovery key becomes indispensable. It serves as a fallback mechanism, a pre-arranged method to prove your identity and reclaim access to your account when all other options are exhausted. It’s a safety net woven into the fabric of Apple’s security, designed to prevent you from being permanently locked out of your digital world.
Understanding the Recovery Key: Its Purpose and Function
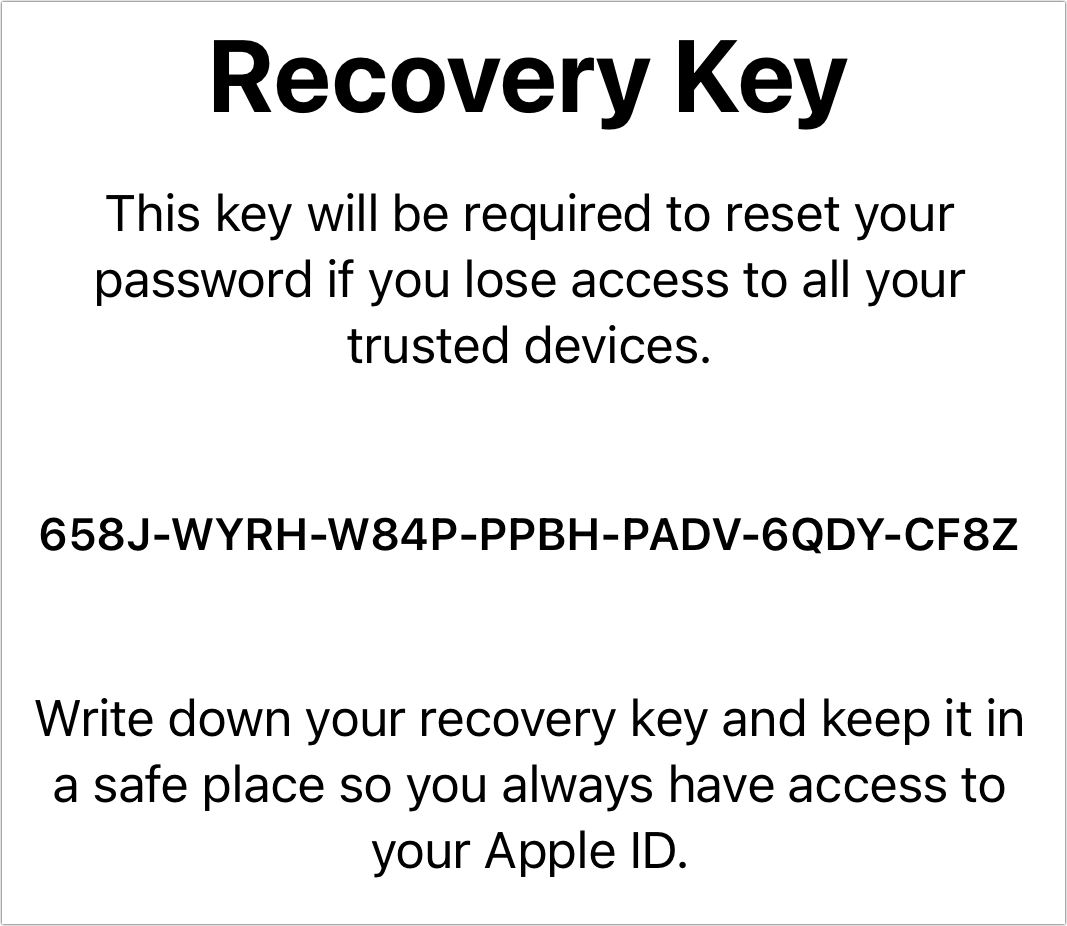
The recovery key is a unique, randomly generated alphanumeric string that you create and store separately from your Apple ID password. Its sole purpose is to provide an alternative method of verifying your identity and regaining access to your Apple ID. Unlike your password or the verification codes from 2FA, which are dynamic and often require proximity to your devices, the recovery key is a static piece of information that you are solely responsible for keeping safe.
The Role of the Recovery Key in Account Recovery
Imagine a worst-case scenario: you’ve forgotten your Apple ID password, your iPhone (your only trusted device) has been lost or stolen, and you’ve changed your phone number, rendering your trusted phone number inaccessible. In such a situation, without a recovery key, your Apple ID would effectively be lost forever, potentially locking you out of iCloud, App Store purchases, iMessage, and all the other services tied to your account. This is where the recovery key steps in as your lifeline.
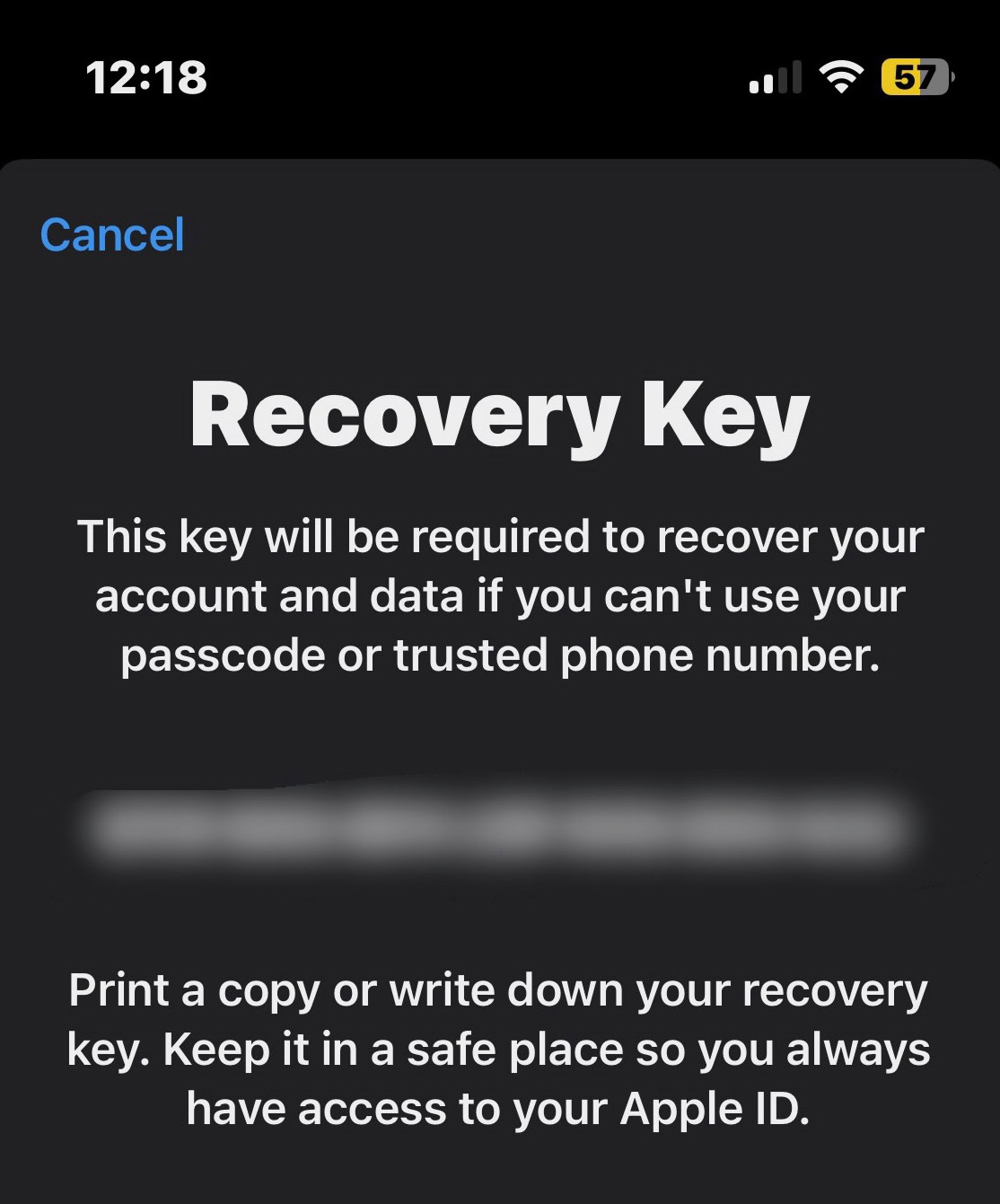
When you initiate an account recovery process with Apple, and you can no longer use 2FA, you will be presented with the option to use your recovery key. This process typically involves a series of verification steps, including providing information that only you would know. However, the definitive proof of ownership in such dire circumstances is the correct recovery key. Entering this key correctly will allow Apple to verify your identity and initiate the process of resetting your password and re-establishing access to your account. It’s a powerful tool, but its power comes with the significant responsibility of secure storage.
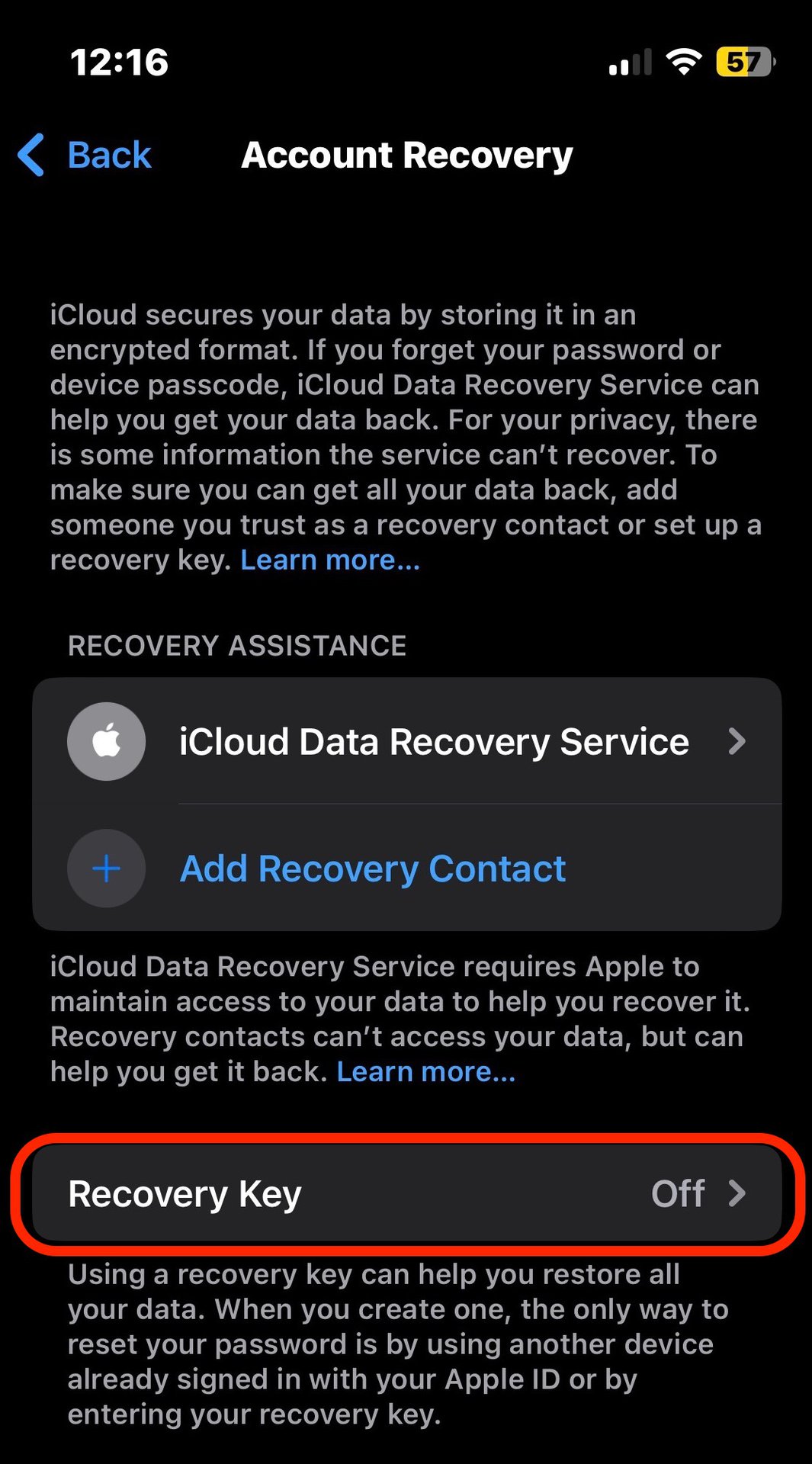
How to Generate and Store Your Recovery Key
The process of generating and storing your recovery key is a critical step in setting up robust Apple ID security. Apple encourages users to create a recovery key when they enable certain advanced security features, such as Legacy Contacts or when they opt for a more stringent security model. The generation process is straightforward but requires careful attention.
When you are prompted to create a recovery key, Apple will present you with a long, complex string of characters. It is imperative that you do not simply copy and paste this into a digital note on your computer or phone, as this would defeat the purpose of a secure, independent recovery method. Instead, you should:
- Write it down: The most secure method is to physically write down your recovery key on a piece of paper.
- Store it securely: Keep this piece of paper in a safe and memorable location. Think of it like a physical key to a secure vault. This could be a safe deposit box, a secure fireproof safe in your home, or a location that you trust implicitly and can access if needed.
- Avoid digital storage: Do not store your recovery key digitally on any device that is connected to the internet or synced across multiple devices. This includes cloud storage services, email drafts, or even password managers (unless the password manager itself has extremely robust offline security features and is treated with the same level of caution).
- Consider redundancy (with extreme caution): Some users opt to create a backup copy of their recovery key. If you choose to do this, ensure that both copies are stored in separate, highly secure physical locations.
The key takeaway is that your recovery key should be accessible only to you and should be stored in a way that it is protected from both loss and theft, as well as digital compromise. It is a piece of information that should exist in the physical world, independent of your digital devices.
The Importance of Responsible Recovery Key Management
The existence of a recovery key signifies a heightened level of security for your Apple ID, but it also places a significant burden of responsibility squarely on your shoulders. Mismanaging your recovery key can lead to the very lockout it is designed to prevent, rendering it useless in a crisis. Therefore, understanding the implications of its management is as crucial as knowing its purpose.
Scenarios Where a Recovery Key is Essential
The true value of a recovery key becomes apparent in specific, often stressful, situations. Being aware of these scenarios can help you understand why taking the time to generate and secure your key is so important.
- Password Amnesia: The most common reason users might need a recovery key is simply forgetting their Apple ID password. While Apple has password reset options, if these are also compromised or unavailable, the recovery key is your last resort.
- Loss or Theft of All Trusted Devices: If all your iPhones, iPads, and Macs are lost or stolen, and you haven’t set up an alternative trusted device, you will be unable to receive the six-digit verification codes required for 2FA. This is a critical juncture where the recovery key shines.
- Inaccessibility of Trusted Phone Number: If you change your phone number and forget to update it as a trusted number for your Apple ID, or if your trusted phone number is lost and you have no other way to verify it, the recovery key becomes the only avenue to regaining access.
- Account Compromise and Lockout: In rare cases, if your account is flagged for suspicious activity, Apple might temporarily lock it down as a security measure. In such situations, the recovery key can be instrumental in proving your identity and unlocking your account.
- Legacy Contact Setup: If you have set up a Legacy Contact, the recovery key can sometimes be used as part of the process for your Legacy Contact to access your account after your passing, though this usually involves additional verification steps.
These scenarios highlight that the recovery key is not just a theoretical security feature; it’s a practical tool designed for real-world emergencies that can affect anyone.
The Risks of Misplacing or Forgetting Your Recovery Key
The flip side of having a powerful recovery tool is the significant risk associated with its mismanagement. The very act of securing a recovery key in a way that it’s inaccessible to others also means it can become inaccessible to you if not handled with care.
- Permanent Account Lockout: This is the most severe consequence. If you lose your recovery key and can no longer access your Apple ID through any other means, your account will be permanently inaccessible. All your data, purchases, and services linked to that Apple ID will be lost forever. There is no “backdoor” or customer service intervention that can bypass the need for a valid recovery key in such extreme circumstances.
- Loss of Data: Losing access to your Apple ID means losing access to iCloud Drive, iCloud Photos, Notes, Reminders, and any other data you’ve synced. This can be devastating, especially if you don’t have local backups of this information.
- Financial Loss: You would lose access to any apps, music, movies, or other digital content purchased through the App Store, iTunes, or Apple Books. This represents a direct financial loss.
- Inability to Use Apple Services: Core Apple services like iMessage, FaceTime, and Apple Music would become unusable, disrupting communication and entertainment.
The responsibility of safeguarding the recovery key is therefore immense. It is a testament to Apple’s commitment to user security that they provide such a powerful tool, but it is equally a reflection of their trust in the user to manage that tool responsibly. The recovery key is not a trivial piece of information; it is the ultimate master key to your Apple digital life, and its security rests entirely in your hands.
