The Foundation of Secure Wireless Connectivity in Tech & Innovation
In the rapidly evolving landscape of technology and innovation, particularly within the realm of autonomous systems like drones, the underlying infrastructure of connectivity is paramount. Wi-Fi, as a ubiquitous wireless communication technology, forms the backbone for countless innovative applications, from real-time data transmission for remote sensing to control links for sophisticated drone operations. At the heart of securing these vital wireless connections lies the “network key,” a critical component that dictates access and protects the integrity and confidentiality of data exchanged over Wi-Fi networks. Without a robust understanding and implementation of network keys, the very innovations they enable would be vulnerable to interception, tampering, or unauthorized access, undermining their reliability and trust.
Wi-Fi’s Role in Modern Drone Ecosystems
Drones, often operating at the cutting edge of tech innovation, leverage Wi-Fi for a diverse array of functions. This includes the initial setup and configuration via mobile apps, downloading mission plans, real-time video streaming from onboard cameras for FPV (First Person View) or surveillance, and the transfer of post-flight telemetry or payload data. Advanced applications, such as autonomous inspection missions, precision agriculture mapping, or sophisticated remote sensing operations, frequently rely on seamless and secure Wi-Fi connectivity to transmit critical commands, receive positional feedback, and offload high-resolution datasets. The reliability and security of these Wi-Fi links directly impact the success, safety, and operational efficiency of the entire drone ecosystem, making the network key an unsung hero of modern aerial technology.
The Imperative of Data Security
The data handled by drones, especially in professional and innovative applications, can be highly sensitive. This might include proprietary mapping data, critical infrastructure inspection details, personal privacy information captured by cameras, or even classified intelligence in defense applications. In an era where data breaches and cyber threats are increasingly sophisticated, ensuring the security of these data streams is not merely a best practice but a fundamental requirement. A network key acts as the first line of defense, encrypting the wireless traffic and authenticating devices seeking to connect. Without it, or with a weak key, an attacker could potentially intercept communications, inject malicious commands, or steal valuable intellectual property, severely compromising the integrity and trustworthiness of drone-powered innovation.
Understanding the Network Key: Principles and Types
A network key for Wi-Fi is essentially a password or passphrase used to secure a wireless network. Its primary function is twofold: to authenticate devices attempting to join the network and to encrypt the data transmitted over the air. This encryption ensures that even if wireless signals are intercepted, the content remains unreadable without the correct key. Over the years, Wi-Fi security protocols, and consequently the nature of network keys, have evolved significantly to counter emerging threats and provide stronger protection.
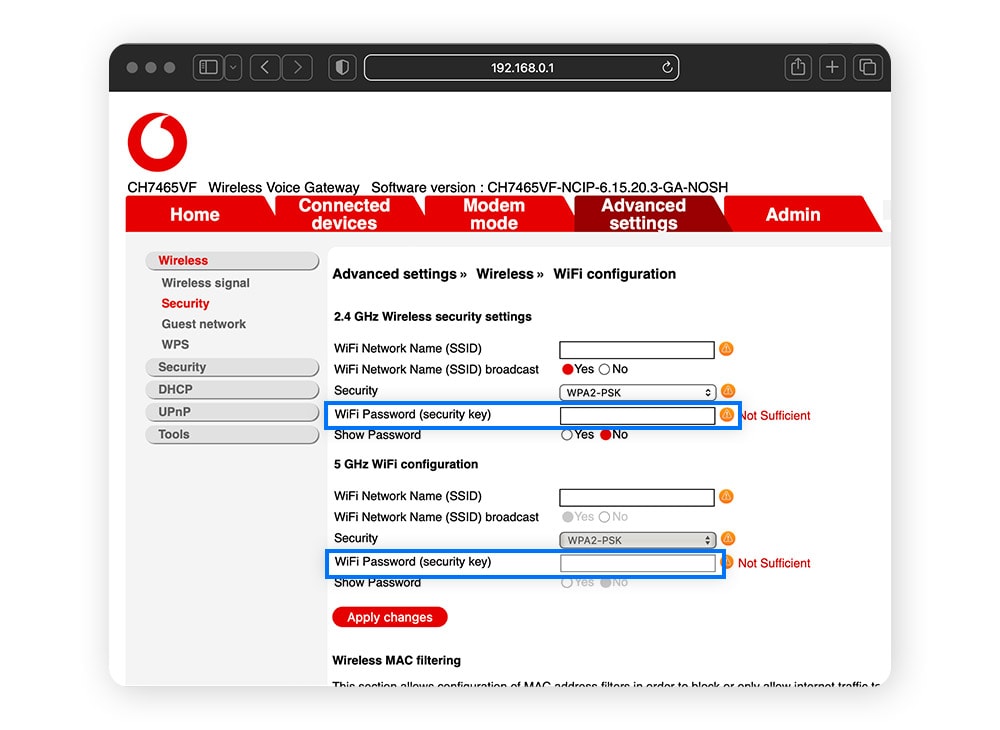
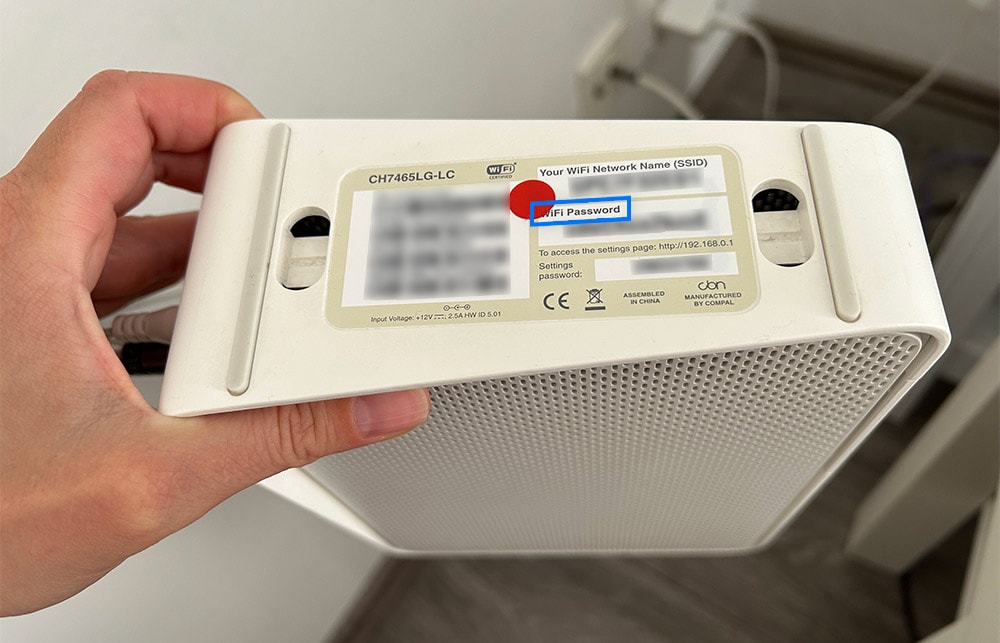
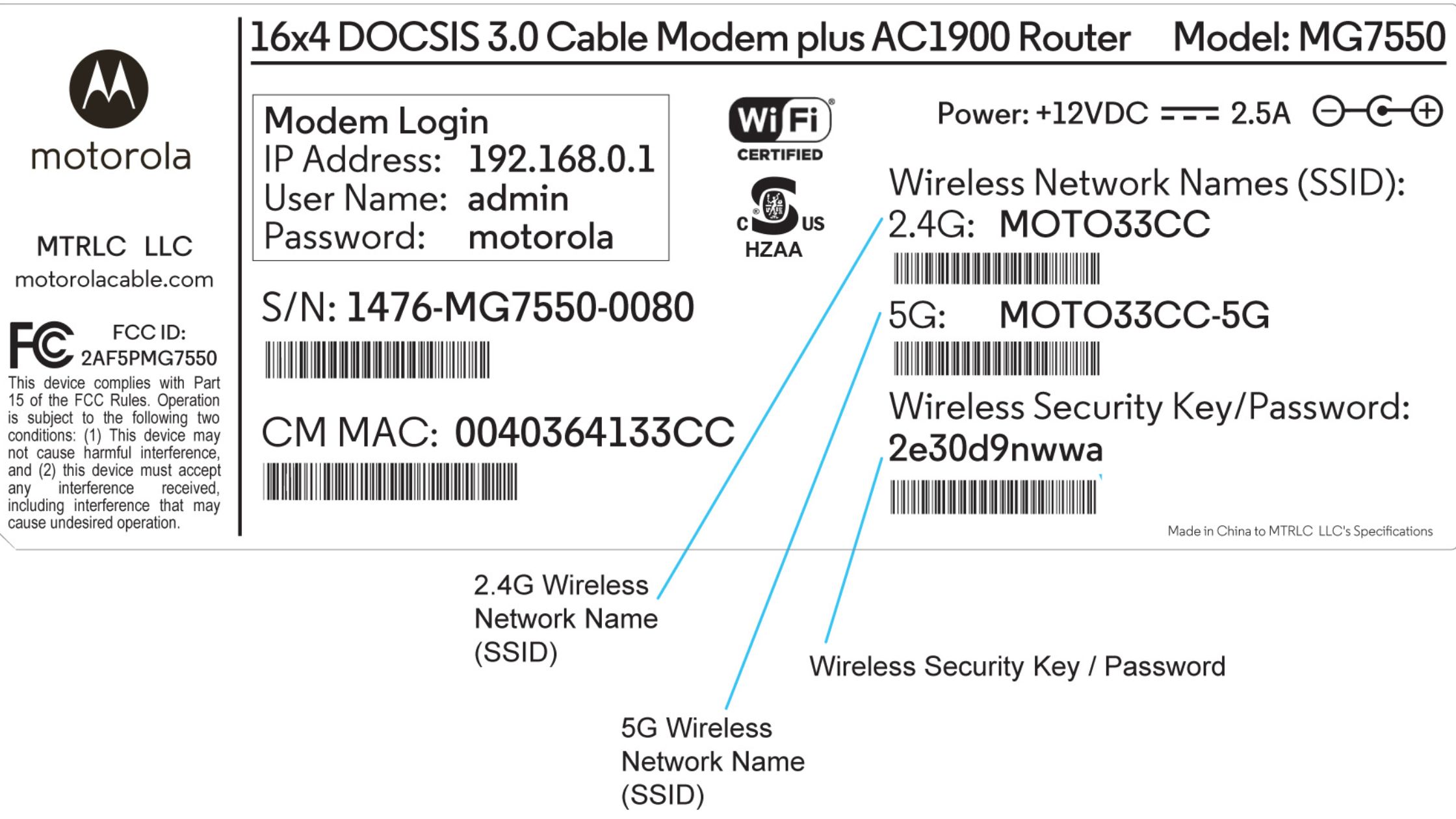
PSKs, Passphrases, and Authentication
Most home and small business Wi-Fi networks utilize a Pre-Shared Key (PSK). This is a single password, or passphrase, that is shared among all authorized devices and the Wi-Fi router. When a device attempts to connect, it presents the PSK, and if it matches the one stored on the router, access is granted, and an encrypted session is established. Passphrases are user-friendly representations of these keys, typically longer and more memorable combinations of words, numbers, and symbols that translate into the complex cryptographic keys used by the underlying security protocols. Effective authentication prevents unauthorized devices from joining the network, thereby isolating legitimate traffic from potential eavesdroppers.
Evolution of Wi-Fi Security Protocols (WEP, WPA, WPA2, WPA3)
The journey of Wi-Fi security protocols reflects a continuous arms race against cyber threats:
- WEP (Wired Equivalent Privacy): Introduced in 1999, WEP was the first attempt at securing Wi-Fi. It quickly proved to be fundamentally flawed and easily crackable due to weak encryption algorithms and key management. For any modern tech or innovation application, WEP is entirely inadequate and should never be used.
- WPA (Wi-Fi Protected Access): As a stopgap measure, WPA emerged in 2003 to address WEP’s severe vulnerabilities. It introduced stronger encryption (TKIP – Temporal Key Integrity Protocol) and improved key management. While a significant improvement, WPA also showed weaknesses over time, particularly against sophisticated dictionary attacks.
- WPA2 (Wi-Fi Protected Access II): Standardized in 2004, WPA2 adopted the Advanced Encryption Standard (AES) with CCMP (Counter Mode with Cipher Block Chaining Message Authentication Code Protocol), offering much more robust security. WPA2 remains widely used today, providing strong protection against most common attacks when a strong passphrase is employed. It’s the baseline for secure drone operations and data transfer in many innovative contexts.
- WPA3 (Wi-Fi Protected Access 3): The latest iteration, launched in 2018, builds upon WPA2 with several enhancements. It introduces Simultaneous Authentication of Equals (SAE) for stronger password-based authentication, making offline dictionary attacks much more difficult. WPA3 also provides enhanced privacy in open, public Wi-Fi networks through individualized data encryption and better security for IoT devices, which can include various drone accessories or sensors. For drone tech pushing the boundaries of autonomy and data sensitivity, migrating to WPA3 offers a distinct security advantage, especially in environments where multiple devices (drones, ground stations, sensors) might form part of an integrated, innovative ecosystem.
Enterprise-Grade Security and Its Implications
While PSK is suitable for many scenarios, large organizations and critical infrastructure deployments often employ WPA2/WPA3-Enterprise. This robust security model uses 802.1X authentication, typically integrating with a RADIUS (Remote Authentication Dial-In User Service) server. Instead of a single shared key, each user or device authenticates with unique credentials (e.g., username/password, digital certificates). This provides granular access control, centralizes user management, and enhances accountability. For drone operations involved in sensitive industrial inspections, public safety, or defense, leveraging enterprise-grade Wi-Fi security is crucial. It ensures that only authorized personnel and trusted drone systems can access the network, minimizing the risk of insider threats or advanced persistent threats targeting the operational framework.
Network Keys and Drone Operations: A Critical Link
The selection and management of Wi-Fi network keys have profound implications for the security and reliability of drone operations, particularly as these technologies become integral to critical infrastructure and data-intensive applications.
Securing Telemetry and Control Links
Many commercial and prosumer drones use Wi-Fi for telemetry (data from the drone like altitude, speed, GPS coordinates) and, in some cases, for direct control commands. A compromised network key on these links could allow an unauthorized party to intercept critical operational data, potentially glean insights into flight paths, or even attempt to inject malicious commands to hijack the drone. In autonomous flight scenarios, where AI-driven decisions are being made based on real-time data, the integrity of these links is paramount. A strong network key, coupled with modern encryption, protects against such vulnerabilities, ensuring that commands originate from the legitimate ground control station and that telemetry is accurately received.
Protecting Sensitive Data Streams (Mapping, Remote Sensing)
Drones equipped with high-resolution cameras, LiDAR, or thermal sensors generate vast amounts of sensitive data for mapping, 3D modeling, environmental monitoring, and infrastructure inspection. This data is often transferred wirelessly from the drone to a local storage device or directly to cloud platforms via Wi-Fi. If the network key protecting this transfer is weak or compromised, the valuable intellectual property, critical infrastructure details, or private information contained within these data streams becomes vulnerable to interception. This could lead to industrial espionage, disclosure of sensitive facility layouts, or breaches of privacy regulations, highlighting why secure Wi-Fi is foundational to responsible innovation in these fields.
Preventing Unauthorized Access and Hijacking
The ultimate nightmare for any drone operator or innovator is the hijacking of a drone. While sophisticated jamming or GPS spoofing attacks exist, a simpler vector can be a compromised Wi-Fi network key that allows an attacker to gain control of the drone’s communication link. Once connected, an attacker could potentially take over flight controls, divert the drone, or retrieve data directly from the device. This poses not only a significant security risk but also a safety hazard, especially when drones are operating near populated areas or sensitive sites. Robust Wi-Fi security, initiated by a strong network key, is a primary deterrent against such unauthorized access attempts.
Best Practices for Robust Wi-Fi Security in Drone Innovation
To fully harness the potential of drones and associated technologies without succumbing to preventable security breaches, adopting rigorous Wi-Fi security practices is non-negotiable.
Choosing Strong, Unique Passphrases
The simplest yet most effective defense against brute-force or dictionary attacks on WPA2/WPA3-PSK networks is to use strong, unique passphrases. These should be long (ideally 12-20 characters), combine uppercase and lowercase letters, numbers, and symbols, and avoid easily guessable information such as personal names, dates, or common words. Each Wi-Fi network supporting drone operations should have its own unique passphrase, never reused across different networks or services.
Regular Firmware Updates and Patching
Wi-Fi routers, access points, and drone controllers or integrated systems that utilize Wi-Fi connectivity are essentially mini-computers. They contain firmware that can have vulnerabilities. Manufacturers regularly release firmware updates that patch security holes and improve performance. Keeping all networking equipment and drone system components up to date is crucial to protect against newly discovered exploits that could bypass even strong network keys.
Network Segmentation for Critical Assets
In larger or more complex drone operations, it’s advisable to implement network segmentation. This involves creating separate Wi-Fi networks (VLANs or separate SSIDs) for different purposes. For instance, a dedicated, highly secured network could be used exclusively for drone control and critical data transfer, while a separate, less privileged network serves general internet access or guest users. This minimizes the attack surface for critical drone assets, ensuring that a breach on a less secure segment does not compromise the core operational infrastructure.
Leveraging Advanced Authentication Methods
For professional and enterprise-level drone deployments, moving beyond simple PSKs to advanced authentication methods significantly enhances security. Implementing WPA2/WPA3-Enterprise with 802.1X authentication and a RADIUS server allows for individual user/device credentials, strong certificate-based authentication, and centralized logging of access attempts. This level of control and auditing is indispensable for regulatory compliance and robust security in sensitive or high-value drone-driven innovation projects.
