In the rapidly evolving landscape of unmanned aerial vehicles (UAVs), the focus is often placed on physical hardware—rotors, carbon fiber frames, and high-capacity batteries. However, as the industry shifts toward autonomous flight, remote sensing, and complex mapping, the invisible infrastructure of data transmission has become equally critical. At the heart of this digital transformation is HTTPS (Hypertext Transfer Protocol Secure). For drone professionals, developers, and tech-focused hobbyists, understanding HTTPS is no longer optional; it is the fundamental layer that ensures the integrity of mission data, the safety of autonomous flight paths, and the privacy of remote sensing telemetry.
As drones become sophisticated “flying computers” integrated into the Internet of Things (IoT), the way they communicate with ground stations, mobile apps, and cloud servers determines the reliability of the entire operation. HTTPS provides the encrypted tunnel through which modern drone innovation travels, protecting against the growing threats of data interception and unauthorized command overrides.
Decoding the Protocol: HTTPS in the Ecosystem of Modern Drones
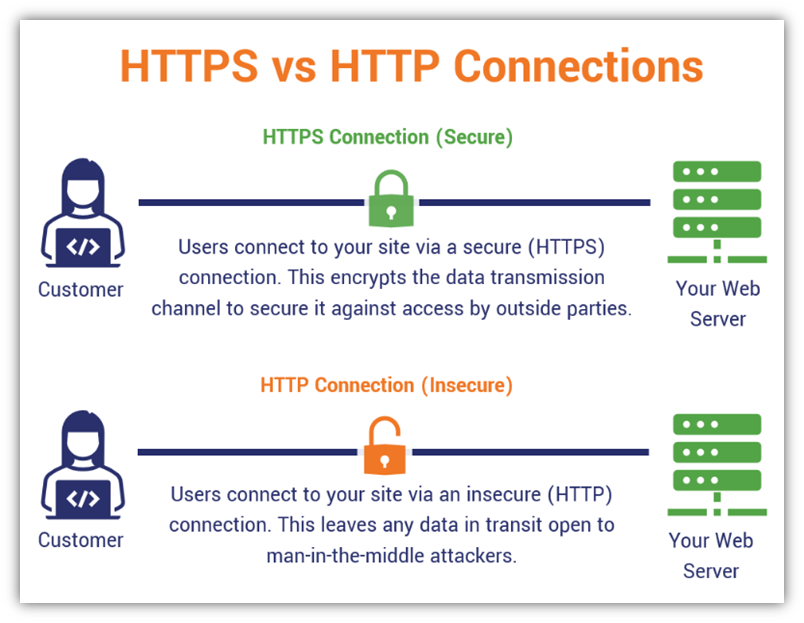
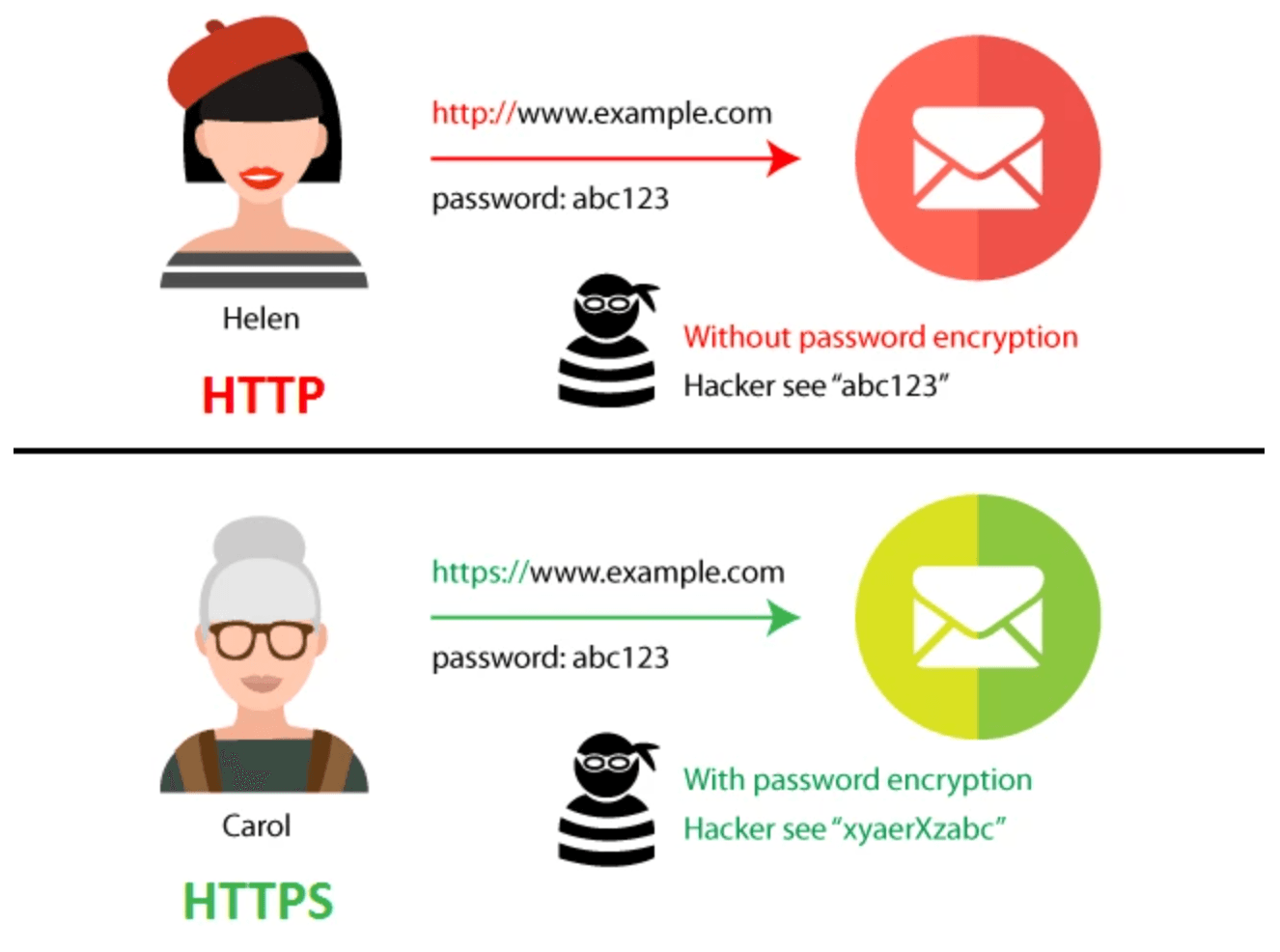
To understand why HTTPS is vital for drone technology, one must first understand its structure. HTTPS is the secure version of HTTP, the primary protocol used to send data between a web browser and a website. The “S” stands for “Secure,” and it signifies that the communication is encrypted via Transport Layer Security (TLS), formerly known as Secure Sockets Layer (SSL).
In the context of drone innovation, the “website” is often a cloud-based fleet management platform or a remote mapping server, and the “browser” is the drone’s onboard computer or the tablet used by the pilot.
The Mechanics of the Encrypted Handshake
When a drone initiates a connection to a cloud server—perhaps to upload a high-resolution photogrammetry set or to download the latest autonomous flight coordinates—an “HTTPS handshake” occurs. During this process, the drone and the server exchange digital certificates to verify each other’s identities. This ensures that the drone is actually talking to the intended server and not a malicious interceptor. Once identity is verified, a unique encryption key is generated for that specific session. Every packet of data sent thereafter is scrambled, making it unreadable to anyone who might attempt to “sniff” the wireless signal.
Why “Secure” Matters for Autonomous Systems
Autonomous flight relies heavily on real-time data synchronization. If an AI-driven drone is navigating a complex industrial site, it may be pulling obstacle data or updated terrain maps from a centralized database. Without HTTPS, this data would be sent in plain text. A sophisticated attacker could intercept the data or, worse, inject false information (a “man-in-the-middle” attack). By utilizing HTTPS, developers ensure that the instructions received by the drone’s AI are authentic and have not been tampered with during transit.
The Intersection of HTTPS and Remote Sensing Data
Remote sensing is one of the most data-intensive niches in the drone industry. Whether a drone is using LiDAR, multispectral sensors for precision agriculture, or thermal imaging for search and rescue, the value of the mission lies entirely in the data collected. HTTPS serves as the primary safeguard for this intellectual property.
Protecting Photogrammetry and 3D Mapping Assets
In high-stakes industries like construction and mining, drone-captured 3D models are sensitive assets. These maps often contain proprietary information about site progress, resource volume, and structural vulnerabilities. When these multi-gigabyte files are moved from the drone to the cloud for processing, HTTPS ensures that the data remains confidential.
Furthermore, many modern mapping platforms use Web APIs to integrate with other software. These APIs (Application Programming Interfaces) require HTTPS to protect the authentication tokens used by pilots. If these tokens were leaked through an insecure HTTP connection, unauthorized parties could gain access to a company’s entire historical mapping database.
Securing Cloud-Based Analytics Pipelines
The innovation of “edge-to-cloud” processing allows drones to send low-latency data to powerful servers that run AI algorithms to detect anomalies—such as cracks in a dam or pest infestations in a crop field. HTTPS is the industry standard for these pipelines. It provides data integrity, ensuring that the images analyzed by the AI are exactly what the drone captured. Even a single bit of altered data in a high-resolution image could potentially lead to a false positive or negative in an automated detection system, making the reliability of the transport protocol a matter of operational safety.
Autonomous Flight and the Necessity of Secure Command Links
The shift toward BVLOS (Beyond Visual Line of Sight) operations is perhaps the greatest leap in drone tech today. BVLOS requires the drone to be connected to the pilot or a command center via cellular networks (4G/5G) or satellite links. In these scenarios, the drone is essentially an IoT device operating over the public internet, making the role of HTTPS paramount.
Safeguarding Mission Logs and Flight Paths
Every time an autonomous drone takes off, it generates a flight log. This log contains GPS coordinates, altitude data, battery health, and pilot inputs. Tech-forward companies use this data to refine their AI follow modes and autonomous navigation algorithms. By transmitting these logs over HTTPS, companies prevent competitors or bad actors from reverse-engineering their flight paths or identifying sensitive operational areas.
Moreover, when new mission parameters or geofencing updates are pushed to a fleet of drones, HTTPS ensures that these updates are legitimate. An insecure update could allow a “hijacker” to redirect a drone to a different location by spoofing the command server.
Remote ID and Compliance through Secure Protocols
As regulatory bodies like the FAA and EASA implement Remote ID requirements, drones are becoming more digitally visible. Remote ID systems often rely on web-based registration and real-time reporting. The interaction between the drone’s broadcast system and the regulatory database must be secured. HTTPS provides the framework for this secure reporting, ensuring that a pilot’s private information is not exposed while still satisfying the legal requirement for digital “license plates” in the sky.
Innovations in Drone Connectivity: HTTPS as the Foundation of the IoD
The “Internet of Drones” (IoD) is a concept where fleets of UAVs work in a coordinated manner, communicating with each other and with ground infrastructure. This level of innovation requires a standardized, secure communication protocol that can handle the scale of hundreds of thousands of concurrent connections.
5G, Edge Computing, and Encrypted Communication
The rollout of 5G technology has provided the bandwidth necessary for real-time 4K streaming and low-latency autonomous control. However, 5G alone does not guarantee end-to-end encryption at the application layer. HTTPS fills this gap. As drones utilize edge computing—where data is processed at the nearest cell tower rather than a distant server—HTTPS ensures that the “hand-off” between different network nodes remains secure. This is particularly important for AI follow modes that require sub-second response times; the security overhead of HTTPS has been optimized in recent years to ensure it does not introduce significant latency.
The Role of AI in Detecting Communication Vulnerabilities
Innovations in drone software now include AI-driven security modules. These modules monitor the HTTPS connections for any signs of anomalies, such as certificate mismatches or unusual packet loss, which could indicate a jamming attempt or a cyber-attack. By using the structured nature of HTTPS, these AI systems can quickly validate the health of the communication link, allowing the drone to initiate “return to home” (RTH) procedures if the secure connection is compromised.
Best Practices for Implementing HTTPS in Drone Software Development
For innovators developing the next generation of drone apps and remote sensing platforms, implementing HTTPS is more than just a checkbox; it is about building trust with the end-user.
- Strict Transport Security (HSTS): Tech-forward drone platforms should use HSTS to force connections to use HTTPS exclusively, preventing “downgrade attacks” where a hacker tries to force the drone to communicate over insecure HTTP.
- Certificate Pinning: In high-security drone applications (such as military or high-tier industrial use), developers use certificate pinning. This technique tells the drone to only trust a specific, pre-defined certificate, making it nearly impossible for an attacker to use a fraudulent certificate to intercept the data.
- End-to-End Encryption (E2EE): While HTTPS encrypts data in transit, the most innovative platforms are moving toward E2EE, where data is encrypted on the drone and only decrypted at the final destination, with HTTPS serving as the secure delivery vehicle.
As we look toward the future of drone technology, the focus will continue to shift from how high a drone can fly to how securely it can communicate. HTTPS is the silent enabler of this progress. It protects the massive datasets generated by remote sensing, secures the command links of autonomous fleets, and ensures that the “Tech & Innovation” side of the industry remains a safe and reliable frontier for global enterprise. Without the security provided by HTTPS, the dream of fully autonomous, cloud-integrated drone swarms would be a logistical and security nightmare. With it, the sky is truly the limit for secure, data-driven aerial innovation.
