As the drone industry transitions from a recreational hobby into a cornerstone of industrial technology, the infrastructure supporting these unmanned aerial vehicles (UAVs) has become increasingly complex. One of the most critical, yet often overlooked, components of modern drone “Tech & Innovation” is the CA (Certificate Authority) certificate. In an era where drones are used for autonomous mapping, remote sensing, and critical infrastructure inspection, ensuring the integrity of communication and data is paramount. A CA certificate serves as the digital bedrock of this security, acting as a “digital passport” that validates the identity of devices, servers, and software within the drone ecosystem.
In the context of advanced drone technology, a CA certificate is not just a file on a computer; it is a vital instrument for maintaining the Chain of Trust in wireless environments. Whether it is ensuring that a firmware update is legitimate or verifying the identity of a drone via Remote ID, the CA certificate ensures that the innovation driving the industry remains secure from cyber threats and data manipulation.
The Foundation of Trust: Defining the CA Certificate for Unmanned Systems
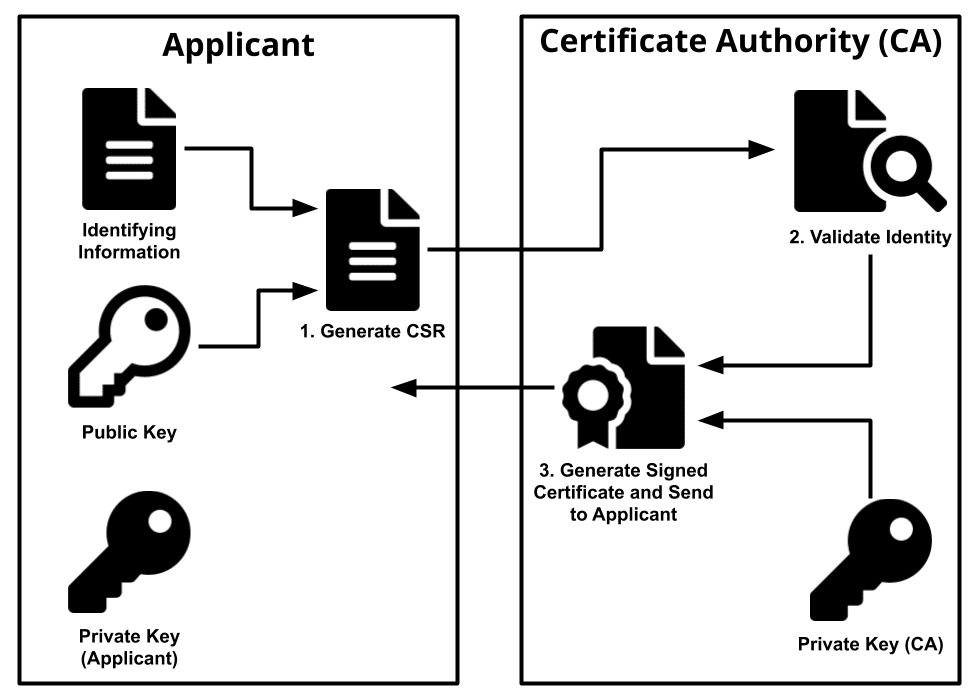
At its core, a CA Certificate is a digital document used to prove the ownership of a public key. These certificates are issued by a trusted third party known as a Certificate Authority (CA). In the realm of drone tech and innovation, these certificates allow drones, controllers, and cloud-based management platforms to verify each other’s identities before exchanging sensitive information.
How Public Key Infrastructure (PKI) Protects Drone Data
To understand CA certificates, one must understand Public Key Infrastructure (PKI). PKI is the framework that manages digital certificates and public-key encryption. In a drone operation, the drone uses a “private key” to sign data and a “public key” (wrapped in a CA certificate) to allow others to verify that the data actually came from that specific drone.
Innovation in drone technology has led to the deployment of “Zero Trust” architectures. In these systems, no device is trusted by default. Every time a drone connects to a 4G/5G network for remote sensing or communicates with a ground control station, it must present its CA certificate. This process ensures that a malicious actor cannot “spoof” a drone’s identity to feed false data into a mapping system or take control of an autonomous flight path.
The Chain of Trust in Remote Operations
The “Chain of Trust” refers to the hierarchy of certificates that leads back to a “Root CA.” For drone manufacturers and software developers, maintaining this chain is essential for long-range operations. When a drone sends a telemetry packet, the receiving server checks the certificate against a list of trusted authorities. If the certificate is revoked or invalid, the communication is terminated. This prevents “Man-in-the-Middle” (MitM) attacks, which are a significant risk in the open-air wireless frequencies used by UAVs.
CA Certificates and the Evolution of Remote ID
One of the most significant regulatory and technological innovations in recent years is the implementation of Remote ID (Remote Identification). Often described as a “digital license plate” for drones, Remote ID allows authorities and other pilots to identify a drone’s position and identity in real-time. This system relies heavily on the security provided by CA certificates.
Standardizing Identity in National Airspaces
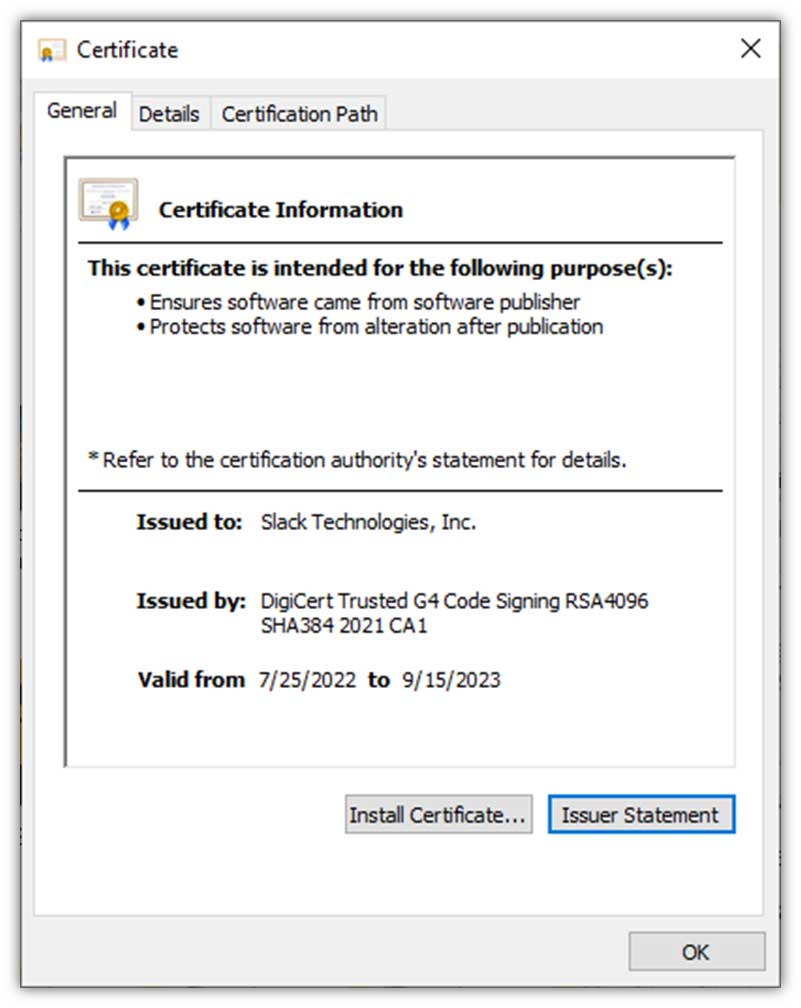
As drones are integrated into national airspaces alongside manned aircraft, the need for standardized, verifiable identity is non-negotiable. CA certificates facilitate this by providing a standardized format (such as X.509) that can be read by different systems. When a drone broadcasts its Remote ID signal, it includes digital signatures that are validated using certificates issued by authorized bodies. This ensures that the identification data has not been tampered with and that the drone is registered and compliant with local aviation laws.
Preventing Spoofing and Unauthorized Access
Innovation in drone “spoofing”—where an attacker broadcasts a fake drone signal—poses a threat to air safety. Without a CA certificate-based verification system, a malicious actor could create “ghost drones” on an air traffic controller’s screen. However, by using encrypted certificates, the system can distinguish between a legitimate broadcast from a registered UAV and a fraudulent signal. This level of security is essential for the future of “Drone Delivery” and urban air mobility, where hundreds of drones may occupy the same small geographic area.
Secure Data Transmission in Mapping and Remote Sensing
The value of a drone is often found in the data it collects. Whether it is LiDAR scans, thermal imaging, or high-resolution photogrammetry, the data represents significant intellectual property and operational intelligence. CA certificates play a dual role here: they secure the transmission of this data and verify the integrity of the sensors.
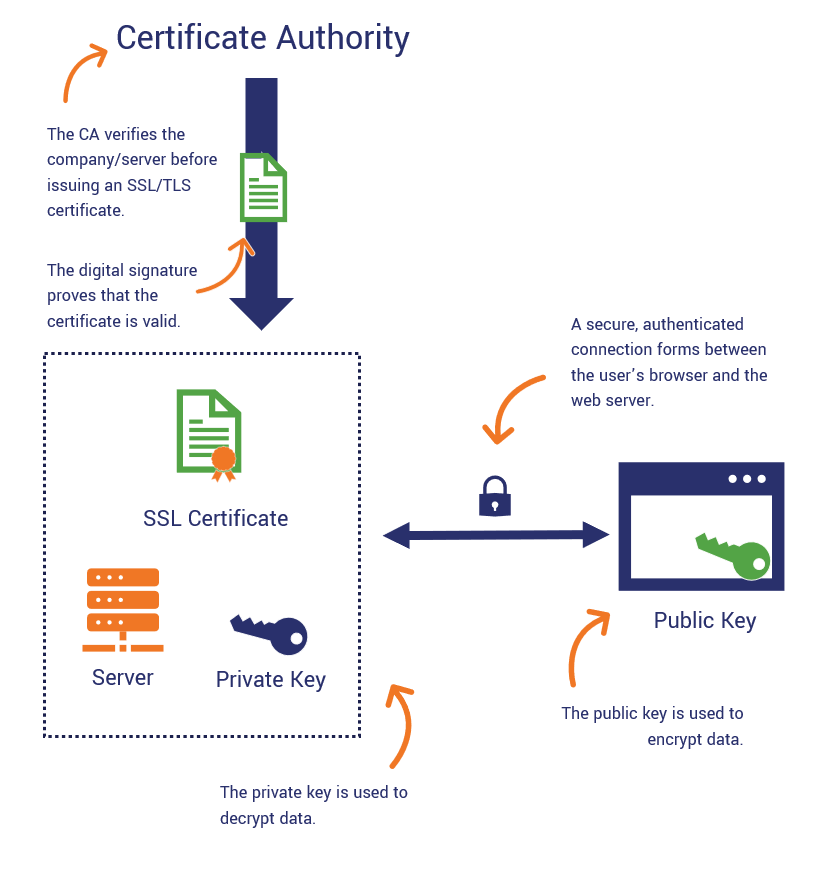
Encrypting the Flow from Sensor to Cloud
In modern remote sensing, drones often upload data directly to the cloud via LTE or satellite links while still in flight. This process uses SSL/TLS (Secure Sockets Layer/Transport Layer Security) protocols, which are powered by CA certificates. The certificate ensures that the “handshake” between the drone and the cloud server is encrypted. This means that even if the data is intercepted, it remains unreadable to unauthorized parties. For industries like oil and gas or defense, this encryption is the difference between a successful mission and a catastrophic data breach.
Validating Firmware Updates and Software Integrity
Innovation in drone technology moves fast, requiring frequent firmware updates to improve autonomous flight algorithms or sensor accuracy. These updates are a prime target for hackers who might try to inject “malware” into a drone’s flight controller. To prevent this, drone manufacturers use CA certificates to “sign” their firmware. The drone’s internal hardware will only accept an update if it carries a valid signature from the manufacturer’s certificate. This ensures that the “Tech” inside the drone remains untainted and performs as intended by the developers.
The Future of Autonomous Flight and Encrypted Communication
As we move toward a future of fully autonomous drone swarms and AI-driven fleet management, the role of the CA certificate will only expand. We are seeing a shift from manual certificate management to automated “Identity Management” systems within the drone tech space.
AI-Driven Fleet Management and Decentralized Trust
Autonomous fleets require drones to communicate with each other (Machine-to-Machine, or M2M) to avoid collisions and coordinate tasks. In these scenarios, there is no human operator to verify the identity of a neighboring drone. Instead, AI-driven systems use CA certificates to instantly authenticate “peer” drones. Innovation in blockchain technology is also being explored to create decentralized CAs, where the “trust” is distributed across a network, making it nearly impossible for a single point of failure to compromise an entire fleet of autonomous UAVs.
Implementing Zero-Trust Architectures in Drone Operations
The ultimate goal of tech innovation in drone security is the implementation of a “Zero-Trust” architecture. In this model, every action—from a command to tilt the gimbal to a request to change the flight path—must be authenticated. CA certificates are the keys to this architecture. By assigning unique certificates to every component of a drone (the flight controller, the GPS module, the camera system), manufacturers can ensure that even if one component is compromised, the rest of the system remains secure.
Conclusion
The question “What is a CA certificate?” is no longer just a concern for IT professionals; it is a fundamental question for anyone involved in drone technology and innovation. As drones become more autonomous and more integrated into our digital infrastructure, the CA certificate acts as the invisible guardian of the skies. It ensures that the data we collect is accurate, the identities we broadcast are genuine, and the autonomous systems we build are resilient against interference.
In the rapidly evolving landscape of remote sensing, mapping, and AI-driven flight, the CA certificate is the silent enabler of progress. By establishing a robust framework of trust, these digital certificates allow the drone industry to push the boundaries of what is possible, moving us toward a future where unmanned systems can operate safely, securely, and with total integrity in every corner of the globe. Understanding and implementing high-level certificate management is not just a technical requirement—it is the hallmark of professional drone innovation.
