The digital age has bestowed upon us an unprecedented level of connectivity, allowing us to communicate with others across vast distances instantaneously. However, this constant accessibility can also lead to unwanted intrusions, necessitating tools to manage our digital interactions. One such fundamental tool is the ability to block a phone number. While seemingly a simple act, understanding the implications and technical realities of blocking a number offers a fascinating glimpse into the intricate workings of telecommunications networks and mobile operating systems. This exploration delves into what truly occurs when you activate the block feature, not just from a user experience perspective, but also from the underlying technological infrastructure that makes it possible.

The User Experience of Blocking
From the perspective of the person initiating the block, the process is remarkably straightforward and designed for user privacy and control. Mobile operating systems on both iOS and Android offer intuitive interfaces for managing blocked contacts.
Initiating a Block
When you decide to block a number, you are essentially instructing your device to filter incoming communications from that specific source. The exact steps vary slightly between operating systems, but the core functionality remains consistent.
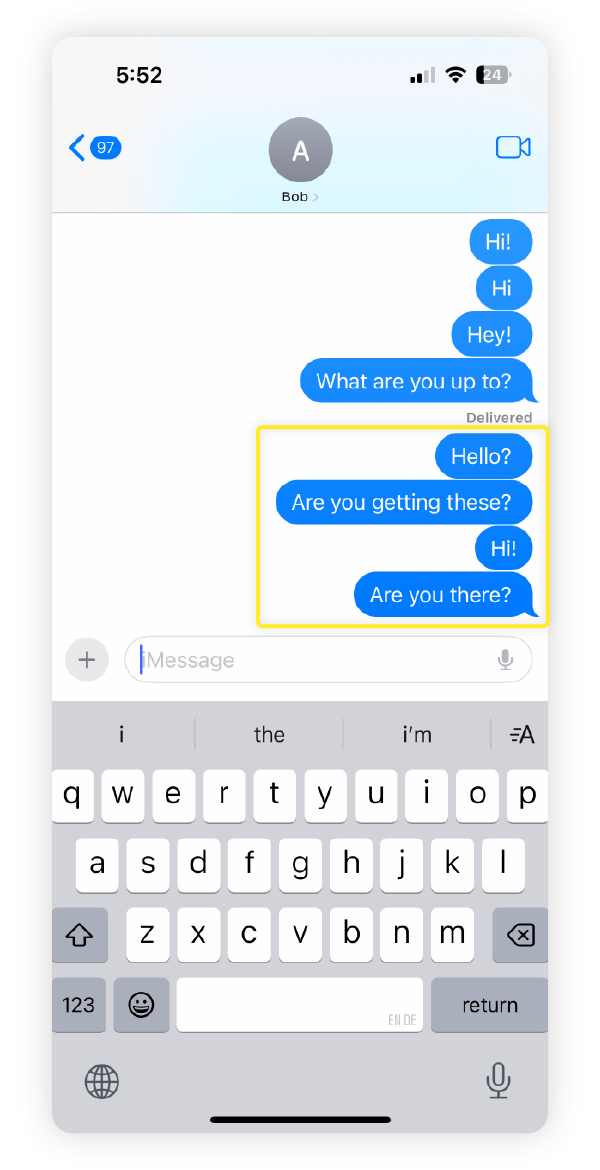
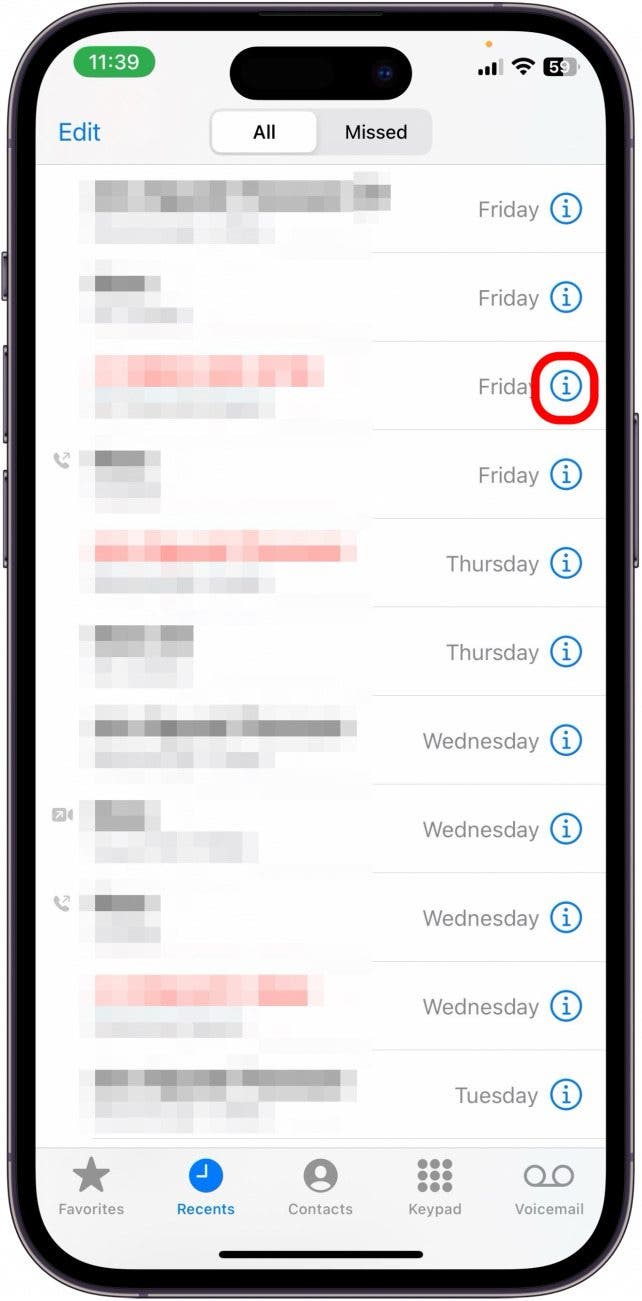
On iOS Devices
In iOS, blocking can typically be done directly from a contact card, from recent calls, or from FaceTime. For a contact, you navigate to their contact card, scroll down, and tap “block this caller.” For a number in your recent calls, you tap the “info” icon next to the number and then select “block this caller.” This action adds the number to a global list of blocked contacts stored within your device’s settings.
On Android Devices
Android’s approach is similarly user-friendly. Most Android phones allow you to block a number from your recent calls list or from within the contacts app. You’ll typically find an option like “Block number” or “Add to block list” within the options menu for a specific call or contact. Like iOS, this adds the number to your device’s internal blocklist. Some Android variations also offer the ability to block unknown or private numbers, which is a broader setting that applies to any incoming call where the caller ID is not transmitted.
The Consequences for the Blocked Caller
Once a number is blocked, the experience for the person on the other end changes significantly, though they are generally unaware of the specific action taken against them.
Silenced Communications
The most immediate and obvious consequence is that any calls or text messages from the blocked number will be intercepted by your device before they reach you.
- Calls: When a blocked number attempts to call you, their call will likely be routed directly to your voicemail without your phone ringing or displaying an incoming call notification. Some carriers might even terminate the call before it reaches voicemail, depending on their network configuration. The blocked caller will not receive any indication that their call was not delivered; they will simply hear a normal ringing tone, or if you have voicemail, it will eventually go to voicemail as if you were unavailable.
- Text Messages (SMS/MMS): Text messages sent from a blocked number will not appear in your messaging application. They are silently discarded by your device. The sender will not receive any notification of non-delivery. They will believe their message has been sent and received normally.
A Deceptive Sense of Connectivity
This silent interception creates a peculiar situation where the blocked individual believes they are communicating successfully, while the blocking individual remains entirely shielded from their attempts. There is no “blocked” message, no notification sent to the caller or texter. This is a deliberate design choice to protect the privacy and peace of mind of the user who has initiated the block.
Other Communication Avenues
It’s important to note that blocking a number typically only affects calls and SMS/MMS messages made through the cellular network. It generally does not extend to other communication platforms.
- VoIP Services: Apps like WhatsApp, Signal, Telegram, and others that use internet-based calling and messaging will not be automatically blocked by your phone’s native blocking feature. You would need to block the contact within each individual application.
- Email: Email communication is entirely separate and is not affected by phone number blocking.
- Social Media: Similarly, direct messages or friend requests on social media platforms are unaffected.
The Technical Underpinnings of Blocking
Behind the seamless user interface lies a complex interplay of mobile operating system functions and cellular network protocols. Blocking isn’t merely a software trick; it involves a layered approach to filtering communications.
Mobile Operating System’s Role
The primary layer of blocking occurs at the operating system level of your smartphone. Your device is programmed to recognize and filter incoming signals based on the number identified.
Local Filtering Mechanisms
When a call or message arrives, your phone’s operating system first checks its internal database of blocked numbers.
- Call Handling: For incoming calls, the OS intercepts the signal. If the originating number matches an entry in the blocklist, the OS instructs the modem to either disconnect the call, divert it to voicemail, or simply prevent the device from alerting you. This processing happens very early in the call establishment process, before your phone even rings.
- Message Handling: For SMS/MMS messages, the OS receives the message data. Before the messaging application can display it, the OS checks the sender’s number against the blocklist. If it’s blocked, the message is intercepted and discarded, never reaching the user’s inbox.
App-Specific Blocking
As mentioned, many third-party communication apps have their own independent blocking mechanisms. These apps maintain their own lists of blocked users within their server infrastructure or locally on your device. When you block someone within an app like WhatsApp, you are instructing that app’s servers to prevent messages and calls from that user to reach your account. This is distinct from the phone’s native blocking feature and is necessary because these apps operate outside the direct control of the core cellular network protocols.
Cellular Network and Carrier Contributions
While the bulk of blocking occurs on your device, the cellular network and your carrier also play a role, particularly in how calls are handled.
Call Routing and Termination
When you block a number, your device doesn’t just ignore the incoming signal; it communicates instructions back to the network.
- Early Termination: In some cases, the device can signal to the network to terminate the call before it even reaches your phone. This is a more efficient method as it conserves battery and network resources.
- Voicemail Diversion: If early termination isn’t feasible or configured, the network might still route the call to your voicemail, as if your phone were unavailable. The specific behavior can vary between carriers and device models. The key is that the call is effectively silenced from your perspective.
Signal Processing and Identification
The cellular network uses sophisticated systems to identify and route calls. When a blocked number attempts to connect, the network receives the caller ID information. Your device, through its operating system, acts as a gatekeeper, deciding whether to accept or reject this incoming information based on the pre-defined blocklist.
The Illusion of Privacy and the Limits of Blocking
The blocking feature is designed to provide a sense of security and control. However, it’s important to understand its limitations.
Spoofed Numbers
One significant limitation is the ability of malicious actors to “spoof” caller ID information. This means they can make it appear as though a call or message is coming from a different number than the one they are actually using. If someone is spoofing a number that you have not blocked, their communication will still get through. Similarly, if a blocked number is being used by someone else to contact you, their messages might bypass your block if the caller ID information is altered or if they are using a different device with a different number.
Dynamic Numbers and Burner Phones
Individuals who intentionally wish to evade blocking might use “burner phones” or constantly change their phone numbers. In such scenarios, blocking a single number will only be a temporary solution, as they can simply acquire a new number to continue their attempts.
Network-Level Blocking (Carrier or Legal Intervention)
While user-level blocking is common, carriers can also block numbers at a network level, usually in response to illegal activity or repeated spam complaints. This is a more robust form of blocking that affects all users on that carrier who might attempt to contact the blocked number, or vice versa. Legal intervention can also lead to number blocking through court orders.
Legal and Ethical Considerations
The ability to block a number also touches upon legal and ethical considerations, particularly concerning harassment and stalking.
Harassment and Stalking
Blocking is a crucial tool for individuals experiencing harassment or stalking. It allows them to immediately cease unwanted contact without needing to engage with the harasser. However, in cases of severe harassment or stalking, blocking alone may not be sufficient. Law enforcement intervention, restraining orders, and evidence collection become paramount.
Documentation of Attempts
While the blocked individual is unaware of the specific attempts, your device logs can sometimes show “missed calls” from blocked numbers or indicate that messages were received but not displayed. Some security-conscious users might maintain a separate log or rely on phone logs to document persistent attempts at contact from blocked individuals, should legal action become necessary.
Freedom of Speech vs. Right to Privacy
The power to block a number raises questions about the balance between freedom of speech and the right to privacy and personal safety. While individuals have the right to express themselves, this right is not absolute and does not extend to the right to harass or annoy others. Blocking is a mechanism that allows individuals to assert their right to privacy and to control their own digital space, setting boundaries for acceptable communication.
The Digital Boundary
In essence, blocking is the digital equivalent of putting up a fence around your property. You are not silencing the person’s ability to speak in general; you are simply dictating that they cannot speak within your designated private space. This ability to establish and maintain digital boundaries is a cornerstone of managing personal well-being in an increasingly interconnected world.
Beyond the Basics: Advanced Blocking and Management
While the core functionality of blocking is simple, there are nuances and advanced features that users might encounter.
Blocked Lists Management
Both iOS and Android provide a central place to view and manage your blocked numbers. This is crucial for reviewing who you have blocked and for unblocking numbers if circumstances change.
Adding and Removing Numbers
Users can typically add numbers to their blocked list directly from call logs, contacts, or by manually entering a number. Similarly, they can remove numbers from the list to reinstate communication. This flexibility ensures that blocking is a reversible action.
Carrier-Level Blocking Services
Some mobile carriers offer additional blocking services beyond what is available on the device itself. These might include:
- Spam Blocking: Services that automatically identify and block known spam or robocall numbers.
- Number Portability: If a blocked number is ported to a new carrier, the block may need to be reapplied or managed through the carrier’s systems. However, most modern systems handle number portability relatively seamlessly.
Future of Communication Filtering
As technology evolves, so too will the methods of filtering unwanted communications. AI-powered systems are already being developed to better identify and categorize spam, and potentially even to intelligently manage incoming communications based on user preferences and context. This could lead to more sophisticated blocking mechanisms that go beyond simple number identification.
In conclusion, blocking a number is a powerful tool that, while simple in its execution, is supported by a robust technological framework. It provides users with a vital sense of control over their digital interactions, shielding them from unwanted intrusions. Understanding the journey of a blocked communication, from the user’s tap of a button to the silent interception by their device and the subtle cues from the network, reveals the intricate design and thoughtful engineering that underpins our ability to manage our connected lives.
