The world of technology is replete with specialized tools, each designed to address a specific niche within broader disciplines. While the term “putty” might initially conjure images of soft, malleable substances, in the context of computing, it refers to a free and open-source terminal emulator. Within the suite of tools bundled with PuTTY, one particularly valuable utility is pscp.exe. This Secure Copy Protocol (SCP) client is indispensable for secure file transfers between different systems. Understanding its functionality and application is crucial for anyone involved in system administration, network management, or secure data handling. This article will delve into the intricacies of pscp.exe, exploring its purpose, syntax, common use cases, and its vital role in maintaining secure data operations.
Understanding Secure File Transfer Protocols
Before dissecting pscp.exe, it’s important to grasp the underlying principles of secure file transfer. In the realm of computing, transferring files from one location to another is a fundamental operation. However, when these transfers occur over a network, particularly the internet, security becomes a paramount concern. Unencrypted data can be intercepted, read, and even modified by malicious actors. This is where secure file transfer protocols come into play.
The Evolution of File Transfer Security
Historically, protocols like FTP (File Transfer Protocol) were widely used for file transfers. While functional, FTP transmits data in plain text, making it inherently insecure. Sensitive information, including usernames, passwords, and the content of transferred files, is vulnerable to eavesdropping.
Recognizing these vulnerabilities, secure alternatives emerged. SSH (Secure Shell) is a cryptographic network protocol for operating network services securely over an unsecured network. SSH provides a suite of services, including secure remote login, secure file transfer, and secure tunneling.
Introducing SCP and SFTP
Within the SSH framework, two primary protocols are commonly used for secure file transfers: SCP and SFTP.
-
SCP (Secure Copy Protocol): SCP is an older, but still widely used, file transfer protocol that leverages SSH for its security. It allows for the secure copying of files between a local and a remote host, or between two remote hosts. SCP operates by initiating an SSH connection and then executing remote commands to transfer files. Its simplicity and efficiency have made it a staple for many system administrators.
-
SFTP (SSH File Transfer Protocol): SFTP is a more modern and feature-rich protocol also built on top of SSH. Unlike SCP, which essentially uses SSH as a transport layer to run the legacy
rcpcommand, SFTP is a protocol in its own right, defining a distinct set of commands for file operations. SFTP offers more robust functionality, including directory listing, file renaming, and resuming interrupted transfers, which are not natively supported by SCP.
pscp.exe is an implementation of the SCP protocol, allowing users to harness the security of SSH for their file transfer needs.
The Role and Functionality of pscp.exe
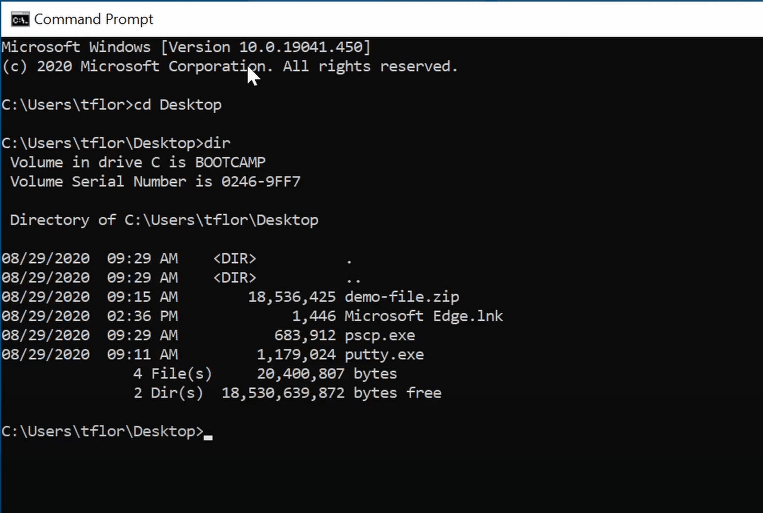
pscp.exe, as part of the PuTTY suite, acts as a command-line utility for securely copying files between systems using the SCP protocol. It is designed to be run from a command prompt or terminal on a Windows machine, enabling users to transfer files to and from remote servers that support SSH.
Core Functionality
The primary function of pscp.exe is to facilitate the secure transfer of files. This can involve:
- Uploading: Transferring files from your local Windows machine to a remote server.
- Downloading: Retrieving files from a remote server to your local Windows machine.
- Remote-to-Remote Transfers: Although less common for end-users and often managed via shell commands on a server,
pscp.execan technically facilitate transfers between two remote hosts through the originating machine.
The security provided by pscp.exe stems directly from its reliance on SSH. This means that all data transmitted, including authentication credentials and the files themselves, is encrypted, protecting it from unauthorized access during transit.
Key Features and Advantages
- Security: The most significant advantage is the encryption provided by SSH. This ensures the confidentiality and integrity of transferred data.
- Command-Line Interface: For users comfortable with the command line,
pscp.exeoffers a powerful and scriptable way to manage file transfers. This is invaluable for automating routine tasks. - Cross-Platform Compatibility: While
pscp.exeis a Windows executable, it can connect to SSH servers running on various operating systems, including Linux, macOS, and other Windows machines with an SSH server installed. - Simplicity: Compared to more complex FTP clients or even some GUI-based tools, the basic syntax of
pscp.exeis relatively straightforward for common transfer operations.
Limitations of SCP (and thus pscp.exe)
It’s important to note that SCP, and by extension pscp.exe, has some limitations compared to SFTP:
- No Directory Listing: SCP does not natively support listing the contents of remote directories. You need to know the exact file path to transfer a file.
- No Resuming Interrupted Transfers: If a transfer is interrupted, you typically have to start over.
- Less Granular Control: The command set is more basic than SFTP, offering fewer options for file manipulation.
Despite these limitations, for straightforward secure file copying, pscp.exe remains an effective and widely used tool.
Practical Usage and Syntax of pscp.exe
The power of pscp.exe lies in its command-line interface, which allows for precise control over file transfers. Understanding its syntax is key to leveraging its capabilities effectively.
Basic Syntax
The general syntax for pscp.exe follows this pattern:
pscp [options] source destination
Where:
[options]: These are flags that modify the behavior ofpscp.exe.source: The file or directory you want to transfer. This can be a local path or a remote path.destination: Where you want the file or directory to be transferred. This can also be a local or remote path.
Specifying Remote Locations
Remote locations are specified using the format:
username@hostname:path
username: The username on the remote server.hostname: The IP address or hostname of the remote server.path: The absolute or relative path to the file or directory on the remote server.
Common Options

Here are some of the most frequently used options for pscp.exe:
-r: Recursive copy. This option is essential for copying entire directories and their contents.-v: Verbose mode. Displays detailed information about the transfer process, including connection details and file transfer progress. This is very useful for troubleshooting.-l username: Specify username. Explicitly sets the username for the remote connection. This is equivalent to usingusername@hostname:path.-pw password: Specify password. Sets the password for authentication. Note: Using this option is generally discouraged for security reasons, as it exposes your password in command history. It’s better to letpscp.exeprompt you for the password.-i privatekey: Specify private key. Use this to authenticate with an SSH private key file (e.g.,id_rsa). This is a more secure method of authentication than using passwords.-P port: Specify port. If the SSH server is not running on the default port 22, you can specify the correct port number.-unsafe: Allow unsafe options. Use with caution; this can bypass certain security checks.-s: Size of compression. (Experimental) Affects compression behavior.
Illustrative Examples
Let’s explore some practical scenarios:
1. Uploading a single file from local to remote:
pscp.exe C:UsersYourUserDocumentsmyfile.txt remote_user@remote.server.com:/home/remote_user/documents/
This command uploads myfile.txt from your local Documents folder to the documents directory on remote.server.com under the remote_user‘s home directory.
2. Downloading a single file from remote to local:
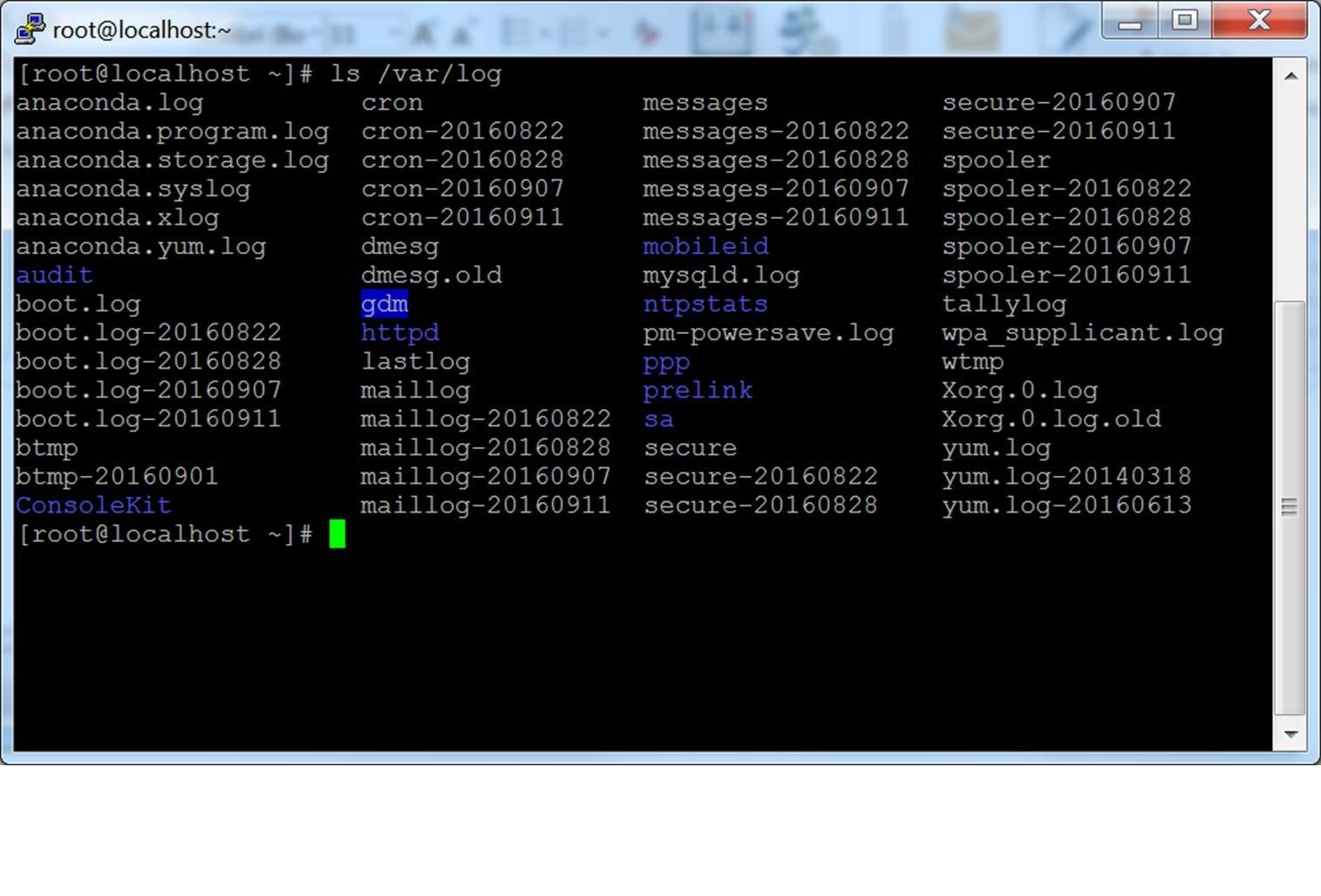
pscp.exe remote_user@remote.server.com:/var/log/syslog C:UsersYourUserDownloads
This command downloads the syslog file from the remote server to your local Downloads folder.
3. Uploading an entire directory recursively:
pscp.exe -r C:UsersYourUserProjectsmy_project remote_user@remote.server.com:/opt/webserver/
This command uploads the entire my_project directory, including all its subdirectories and files, to the /opt/webserver/ directory on the remote server.
4. Downloading an entire directory recursively:
pscp.exe -r remote_user@remote.server.com:/home/remote_user/data C:UsersYourUserBackupserver_data
This command downloads the data directory from the remote server to your local Backupserver_data location.
5. Using a specific port and private key for authentication:
pscp.exe -P 2222 -i C:UsersYourUser.sshid_rsa local_file.zip user@server.example.com:/tmp/
This command connects to server.example.com on port 2222, uses the private key id_rsa for authentication, and uploads local_file.zip to the /tmp/ directory.
Secure File Transfer in Practice: Use Cases for pscp.exe
pscp.exe is not just a theoretical tool; it plays a critical role in various real-world scenarios, particularly in environments where security and automation are paramount.
System Administration and Server Management
System administrators frequently need to transfer configuration files, scripts, logs, and application binaries between servers or from their local workstations to production environments. pscp.exe provides a secure and reliable method for these operations. For instance:
- Deploying Applications: Uploading new versions of web applications, backend services, or executables to a web server.
- Configuration Management: Pushing updated configuration files to multiple servers simultaneously via scripting.
- Log Collection: Downloading log files from remote servers for analysis and troubleshooting.
- Backup Operations: Transferring backup files from a remote server to a local storage location.
Scripting and Automation
The command-line nature of pscp.exe makes it an ideal candidate for integration into shell scripts or batch files. This allows for the automation of repetitive file transfer tasks, saving significant time and reducing the risk of human error. A common pattern involves using pscp.exe within a scheduled task or a deployment script. For example, a script might:
- Build a software package locally.
- Use
pscp.exeto transfer the built package to a staging server. - Execute remote commands via
plink.exe(another PuTTY utility) to install the package on the staging server.
Secure Data Exchange
In organizations, sensitive data often needs to be exchanged between different departments or with external partners. pscp.exe can be employed to ensure that this data transfer is protected. For example:
- Sharing Sensitive Reports: Transferring financial reports, customer data, or proprietary research securely to a designated recipient’s server.
- Data Synchronization: Periodically synchronizing datasets between a central database and remote data collection points.
Development Workflows
Developers often work with remote development servers or cloud instances. pscp.exe can be used to:
- Upload Source Code: Transferring updated source code files from a local development machine to a remote server for compilation and testing.
- Download Artifacts: Retrieving compiled binaries, libraries, or deployment packages from a build server.
Troubleshooting and Maintenance
When encountering issues on a remote system, administrators often need to retrieve diagnostic information. pscp.exe facilitates the secure download of:
- System Logs: Gathering application logs, system event logs, or kernel logs for analysis.
- Configuration Dumps: Downloading current configuration files to compare against known good states.
- Crash Dumps: Transferring memory dumps or crash reports for debugging.
In conclusion, pscp.exe is a powerful and essential utility for anyone who needs to perform secure file transfers. Its integration with the robust security of SSH makes it a reliable choice for a wide array of technical tasks, from routine system administration to complex automated workflows. By understanding its capabilities and mastering its syntax, users can significantly enhance their efficiency and security in managing data across networks.
