In the rapidly evolving landscape of technical communication, precision is as critical as the hardware we deploy in the field. For professionals operating within the spheres of remote sensing, autonomous flight, and aerial mapping, the tools used for coordination must be understood with the same level of mastery as a flight controller or a LiDAR sensor. One such fundamental tool in the digital communication stack is the “BCC” function in email. While it may seem like a vestige of early computing, understanding what BCC means in email—and more importantly, how to use it strategically—is essential for maintaining operational security and professional integrity in high-tech industries.
The Mechanics of Blind Carbon Copy in Technical Communications
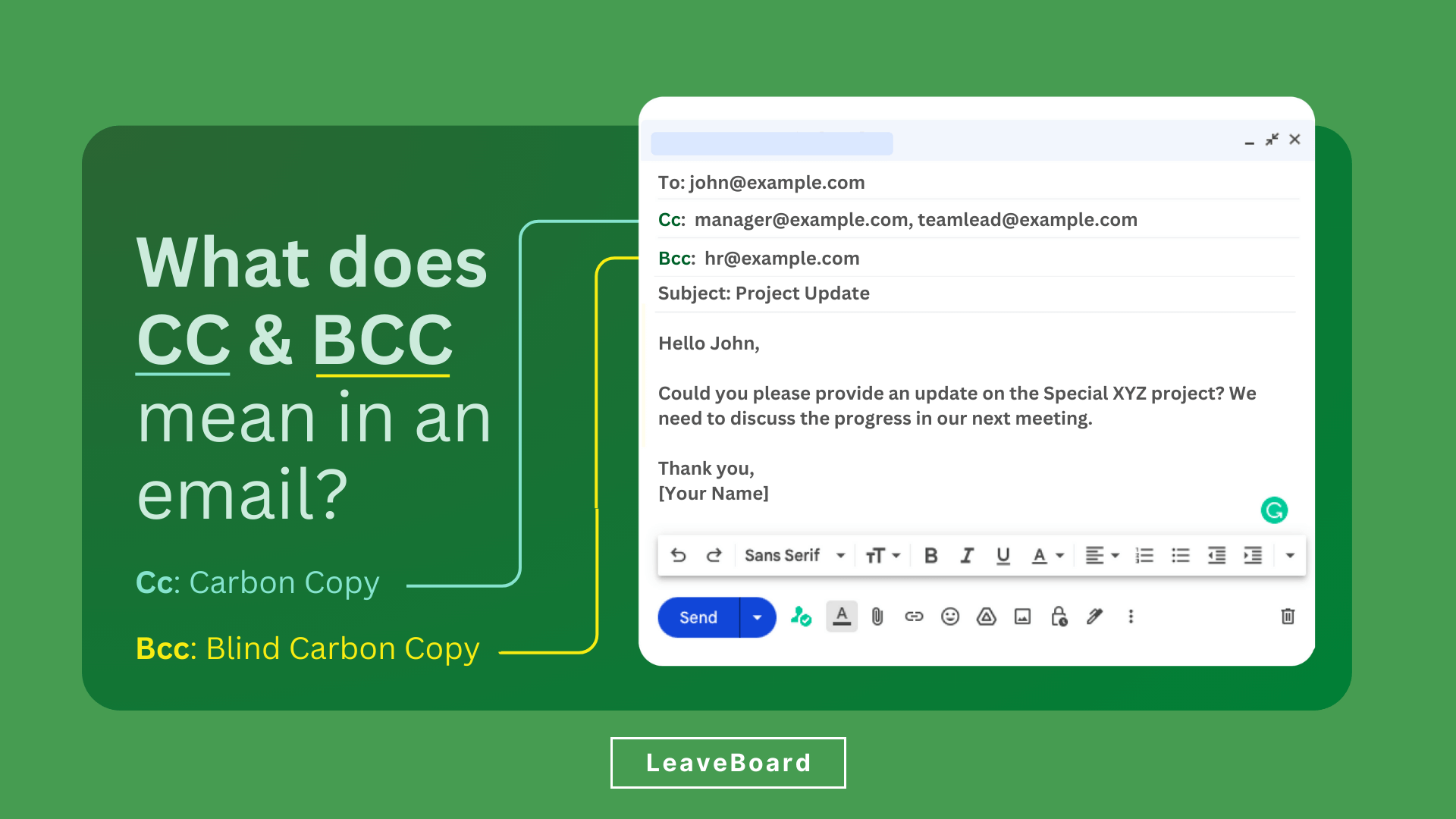
To understand what BCC means in email, one must first look at its mechanical namesake: carbon paper. In the pre-digital era, engineers and administrators placed a sheet of carbon paper between two pieces of stationary to create an identical copy of a document as it was being written. The “Carbon Copy” (CC) in email serves the same purpose, allowing a secondary recipient to see the communication. However, the “Blind Carbon Copy” (BCC) adds a layer of privacy by hiding the identity of the additional recipients from the primary “To” and “CC” parties.
Defining BCC vs. CC vs. To
In the context of managing a drone fleet or a remote sensing project, the “To” field is reserved for the primary action-taker—the individual responsible for the flight mission or the data analysis. The “CC” field is utilized for transparency, ensuring that stakeholders, such as project managers or secondary engineers, are kept in the loop. The “BCC” field, however, is a strategic tool. When you place an address in the BCC field, the mail server processes the delivery to that recipient without including their address in the header information sent to the other parties.
The Architecture of SMTP and Hidden Headers
From a technical innovation perspective, the functionality of BCC is handled at the Simple Mail Transfer Protocol (SMTP) level. When an email is dispatched from a client, the SMTP server receives a list of recipients. It then creates separate “envelopes” for the delivery. While the “To” and “CC” addresses are written into the message headers (the metadata that the recipient’s email client displays), the BCC addresses are stripped from these headers before the email reaches the primary recipients’ inboxes.
This architectural separation is vital for developers and tech-innovators who handle sensitive data. It ensures that while the BCC recipient receives the full content of the message, their presence remains invisible to the rest of the thread. In the world of tech and innovation, where proprietary flight algorithms and sensitive mapping coordinates are frequently discussed, this level of controlled visibility is a basic but necessary form of data hygiene.
Operational Applications in Drone and Remote Sensing Workflows
For those involved in the drone industry, communication is rarely a one-to-one affair. It involves a complex web of regulatory bodies, private landowners, software developers, and end-clients. Knowing how to leverage BCC can be the difference between a streamlined operation and a logistical nightmare.
Privacy and Client Confidentiality in Mapping
In large-scale mapping projects, a single firm might be coordinating with dozens of different landowners to gain flight permission over a specific geographic area. Using the “To” or “CC” fields to message all these landowners at once would be a significant breach of privacy, as every recipient would see the email addresses of every other participant. This could lead to unsolicited contact between parties or, in more sensitive cases, reveal the scope of a commercial project to competitors.
By using BCC, an aerial imaging firm can send a standardized update regarding flight schedules or safety protocols to all participants simultaneously. Each recipient sees only their own address and the sender’s address, preserving the confidentiality of the project’s stakeholder list. This is not just a matter of etiquette; in many jurisdictions, protecting the personal contact information of clients and partners is a legal requirement under data protection regulations.
Scaling Communications for Large-Scale UAV Deployments
As autonomous flight and AI-driven follow modes become more prevalent, the scale of drone deployments is increasing. Tech innovators managing “drone-in-a-box” solutions or automated monitoring fleets often need to send status reports or firmware update notifications to a broad list of site managers.

Using BCC allows these innovators to distribute information efficiently without triggering the dreaded “Reply All” storm. In a professional tech environment, there is nothing more disruptive to a workflow than a notification chain where 50 people are mistakenly replying to a group list. BCC effectively disables this risk, as any reply from a BCC recipient goes only to the original sender, keeping the communication channel clean and focused.
The Security Paradigm: Why BCC Matters for Tech Innovators
In the niche of tech and innovation, information security is paramount. The way we communicate is often the weakest link in a cybersecurity chain. Understanding the implications of BCC is a core component of maintaining a secure professional presence.
Mitigating the Risks of Data Leaks
A common error in the tech industry is the accidental disclosure of a high-value contact list. For example, if a startup developing new obstacle avoidance sensors is reaching out to potential venture capital partners, using the CC field instead of BCC would reveal the entire prospect list to every competitor on that list. This is an amateur mistake that can have devastating consequences for a company’s competitive advantage.
BCC acts as a safeguard against this type of accidental intelligence leak. It allows for the mass distribution of white papers, technical specs, or project updates while ensuring that the recipient list—which is often a curated and valuable asset—remains internal to the organization.
GDPR and Privacy Compliance in Professional Aerial Services
With the rise of the General Data Protection Regulation (GDPR) and similar privacy frameworks globally, the handling of email addresses has become a compliance issue. Email addresses are considered Personal Identifiable Information (PII). In the professional drone services sector, where operations often cross international borders, the misuse of CC instead of BCC can result in significant fines.
Innovators in the space must implement BCC as a standard operating procedure when communicating with any group of external individuals who have not consented to have their contact details shared with one another. This applies to newsletters, community updates for local flight areas, and bulk distribution of aerial survey results.
Beyond the Inbox: Integrating BCC Concepts into Drone Fleet Management Systems
As we look toward the future of drone technology, the concepts underlying BCC—privacy, selective visibility, and streamlined notification—are being integrated into the software that manages autonomous systems.
Automated Reporting and Notification Chains
Modern drone fleet management apps often include automated reporting features. When a mission is completed, the system may need to notify the pilot, the client, and the maintenance team. Innovation in this space involves creating “logic-based BCC” systems. In these configurations, the software determines who needs to see the data and who needs to remain “blind” to the other recipients to ensure that maintenance logs don’t clutter the client’s inbox, or that sensitive telemetry data is only visible to the engineering team.

The Future of Secure Communication in Autonomous Systems
As AI follow modes and remote sensing technologies become more integrated with cloud-based platforms, the “email” format itself is evolving. We are seeing the rise of secure API-driven notifications that function similarly to a BCC. For instance, a remote sensing drone detecting a structural anomaly in a power line might send a high-priority alert to the utility company’s repair team (the “To” party) while silently logging the event in a secure, “blind” administrative database for regulatory auditing.
The principle remains the same: the right information must reach the right people without unnecessary exposure to unauthorized parties. Whether it is an email about a new 4K gimbal camera release or a technical brief on GPS stabilization improvements, the BCC function remains a cornerstone of professional communication in the tech industry.
In conclusion, understanding what BCC means in email is more than just knowing a shortcut in your mail client. For the drone pilot, the tech innovator, and the aerial filmmaker, BCC is a tool for privacy, a shield for proprietary information, and a method for maintaining professional standards in an increasingly connected world. By mastering this simple yet powerful function, professionals can ensure that their communications are as precise and secure as the high-tech hardware they operate. In a field where the margin for error is slim, every detail of the operation—down to the way an email is sent—matters.
