The digital landscape is an increasingly complex environment, and for those involved in the cutting-edge fields of drones, flight technology, and advanced imaging, the threat of a cyberattack is a stark reality. While the exhilaration of piloting a sophisticated UAV or capturing breathtaking aerial footage is immense, the underlying systems are not immune to malicious actors. Understanding what to do if you suspect your systems have been compromised is paramount to protecting your valuable data, equipment, and operational integrity. This guide focuses on the specific vulnerabilities and responses relevant to the drone ecosystem.

Immediate Actions for Suspected Drone System Compromise
When you first suspect a breach, swift and decisive action is crucial. The longer a malicious actor has access, the more damage they can inflict, whether it’s stealing proprietary flight data, disrupting your operations, or even commandeering your drone.
Securing Your Network and Devices
The first line of defense is to isolate the affected systems. If your drone or its associated ground control station is connected to a network, disconnect it immediately. This could involve unplugging Ethernet cables, disabling Wi-Fi, and ensuring no other devices on that network are inadvertently compromised.
Disconnecting from the Internet
The most immediate step is to sever any internet connectivity for the compromised device or network. This prevents further data exfiltration and stops the attacker from issuing remote commands. If the drone itself is connected via a cellular modem, disable that connection.
Isolating Ground Control Stations (GCS)
Your ground control station is a central hub for data and commands. If you suspect it’s been compromised, disconnect it from all external networks, including Wi-Fi, cellular, and any wired Ethernet connections. Also, disconnect any peripherals that are not essential for diagnostics.
Checking Other Connected Devices
A compromise on one device can easily spread. If your GCS or drone controller is connected to a laptop or tablet, or if other devices share the same Wi-Fi network, those devices also need to be checked for signs of compromise and isolated.
Changing Passwords and Access Credentials
Once you’ve contained the immediate threat, it’s time to revoke and reset access. This includes not only passwords but any form of authentication that might have been accessed.
Critical Account Security
If your drone or associated services (e.g., cloud storage for flight logs, manufacturer accounts) use username and password logins, change these immediately. Prioritize accounts that have administrative privileges or access to sensitive flight data. Use strong, unique passwords for each service.
Two-Factor Authentication (2FA)
If you haven’t already, implement 2FA on all relevant accounts. This adds a significant layer of security, requiring a second form of verification beyond just a password, such as a code from your phone.
Reviewing Access Logs
Where possible, review access logs for your drone manufacturer’s platform, cloud storage, and any other services connected to your drone operations. Look for unusual login attempts, locations, or times.
Identifying the Scope of the Breach
Once initial containment measures are in place, the next critical step is to understand the extent of the compromise. This involves a thorough investigation to determine what data was accessed or stolen, which systems were affected, and how the breach occurred.
Examining Drone and Controller Logs
Modern drones and their controllers generate extensive logs. These can be invaluable for forensic analysis.
Flight Data and Telemetry
Review flight logs for any anomalies. Unusual flight paths, unexpected disconnections, or unauthorized commands could indicate external control. Telemetry data might reveal deviations from normal operational parameters.
System Event Logs
Many advanced flight controllers and GCS software maintain event logs. These can record software updates, connection attempts, user activity, and potential error messages that might point to malicious activity. Look for unusual timestamps or unexpected processes running.
Firmware Integrity Checks
For sophisticated drones, especially those used in commercial or industrial applications, checking firmware integrity is vital. A hack might involve subtle modifications to the firmware to gain persistent access or control.
Assessing Data Compromise
The nature of the compromised data will dictate the severity of the breach and the subsequent response.
Intellectual Property and Proprietary Data
For businesses using drones for mapping, inspection, or other specialized services, intellectual property and proprietary flight data are highly sensitive. Determine if this data has been accessed, copied, or exfiltrated.
Personal Information
If your drone operations involve collecting personal information (e.g., from surveillance or community projects), assess if this data has been compromised. This has significant privacy and legal implications.
System Configurations and Credentials
Any sensitive configuration files, API keys, or stored credentials within the GCS or drone system that have been accessed or stolen can lead to further vulnerabilities.
Investigating the Attack Vector
Understanding how the breach occurred is crucial for preventing future incidents.
Network Vulnerabilities
Was the breach due to an unsecured Wi-Fi network, a compromised router, or a phishing attack that led to credential compromise? Identifying the entry point is key.
Software Exploits
Attackers often exploit known vulnerabilities in drone firmware, GCS software, or operating systems. Ensure all your software is up-to-date.
Physical Access
While less common in remote drone operations, physical access to a GCS or drone controller could also lead to a compromise.
Recovery and Mitigation Strategies
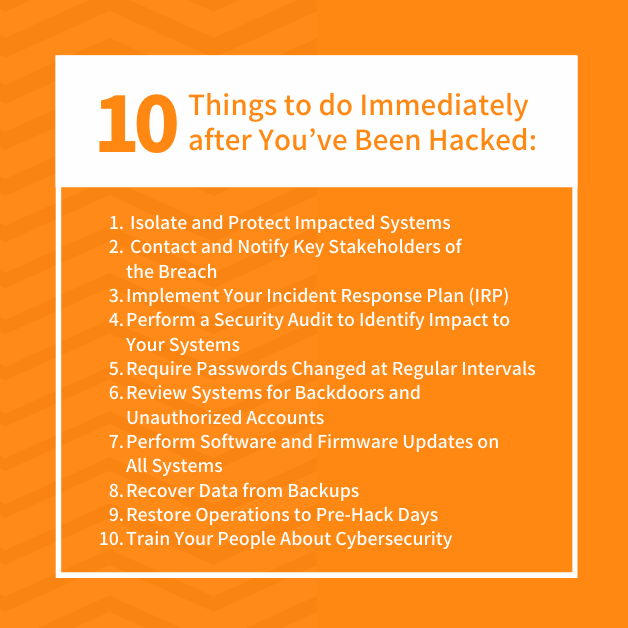
After identifying the scope of the breach, the focus shifts to recovery and implementing robust measures to prevent future attacks. This is a multi-faceted process that involves restoring systems, enhancing security, and potentially reporting the incident.
System Restoration and Rebuilding
Restoring compromised systems to a secure and operational state is a priority.
Data Backup and Restoration
If you have regular, verified backups of your critical data (flight logs, configuration files, captured imagery), this is the time to use them. Ensure the backup source itself is not compromised.
Reinstalling Software and Firmware
In severe cases, a complete reinstallation of the operating system, GCS software, and drone firmware may be necessary. This ensures that any hidden malware or backdoors are removed. Always use official and verified software sources.
Secure Configuration
When reconfiguring systems, prioritize security. This means implementing strong password policies, disabling unnecessary services, and configuring firewalls appropriately.
Enhancing Drone and GCS Security Post-Breach
The incident should serve as a catalyst for improving your overall security posture.
Regular Software and Firmware Updates
This is non-negotiable. Manufacturers regularly release patches to address security vulnerabilities. Ensure your drone firmware, GCS software, and any associated mobile apps are always up-to-date.
Network Segmentation
If your drone operations are part of a larger network, consider segmenting them onto a dedicated, isolated network. This limits the potential spread of a future breach.
Encryption
Implement encryption for sensitive data both in transit and at rest. This applies to data stored on the GCS, transmitted between the controller and drone, and stored in cloud services.
Physical Security
For high-value drone assets or critical GCS equipment, ensure adequate physical security measures are in place to prevent unauthorized access.
Reporting and Incident Response
Depending on the nature and impact of the breach, reporting the incident to relevant authorities or stakeholders may be necessary.
Manufacturer Support
Contact the manufacturer of your drone and GCS. They may have specific protocols for handling security incidents and can offer specialized assistance.
Cybersecurity Professionals
For significant breaches, engaging with cybersecurity professionals specializing in IoT or aviation security can provide expert guidance and support for forensic analysis and recovery.
Regulatory Bodies
If your drone operations are subject to specific regulations (e.g., commercial drone operations, data privacy laws), you may have reporting obligations to regulatory bodies.
Long-Term Prevention and Best Practices
Moving forward, adopting a proactive security mindset is essential to safeguard your drone operations against evolving cyber threats. This involves continuous vigilance, education, and the implementation of robust security frameworks.
Security Awareness and Training
Human error remains a significant factor in many cyber incidents. Educating yourself and your team about cybersecurity best practices is vital.
Phishing and Social Engineering
Understand the common tactics used in phishing and social engineering attacks. Be skeptical of unsolicited emails, messages, or links, especially those requesting credentials or sensitive information.
Secure Data Handling
Implement clear guidelines for how sensitive data related to drone operations is handled, stored, and shared.
Hardware and Software Security Measures
Beyond regular updates, consider broader hardware and software security strategies.
Secure Boot and Trusted Execution Environments
For advanced drone platforms, explore features like secure boot mechanisms and trusted execution environments (TEEs) that help ensure the integrity of the system’s boot process and sensitive operations.
Firewall and Intrusion Detection Systems
Implement robust firewall configurations on your GCS and network infrastructure. For critical operations, consider deploying intrusion detection systems (IDS) to monitor for suspicious network activity.
Access Control Policies
Enforce strict access control policies. Only grant necessary permissions to users and systems, and regularly review and revoke access that is no longer required.
Staying Informed About Emerging Threats
The threat landscape is constantly changing. Staying informed about new vulnerabilities and attack methods specific to drones and flight technology is crucial.
Cybersecurity News and Alerts
Subscribe to relevant cybersecurity news feeds, vulnerability databases, and alerts from drone manufacturers and aviation authorities.

Threat Intelligence Sharing
Participate in industry forums or groups where threat intelligence is shared among drone operators and cybersecurity professionals. This collaborative approach can provide early warnings and insights into emerging threats.
By understanding the specific vulnerabilities within the drone ecosystem and implementing comprehensive security strategies, you can significantly mitigate the risk of a cyberattack and protect your valuable assets and operations. The journey from a potential breach to robust security is ongoing, demanding constant attention and adaptation.
