While the title “What CVV in Debit Card” might initially seem like it pertains to financial transactions, upon closer examination within the context of relevant technological domains, it points towards a niche area of Cameras & Imaging – specifically, how imaging technologies are evolving to verify or authenticate the identity of a user or device, a concept analogous to a CVV in digital security. In this context, the “CVV” can be interpreted metaphorically as a unique visual signature or code embedded within the imaging data itself, detectable by advanced camera systems and AI. This article will explore this cutting-edge intersection of imaging and authentication.

The Evolving Landscape of Visual Authentication
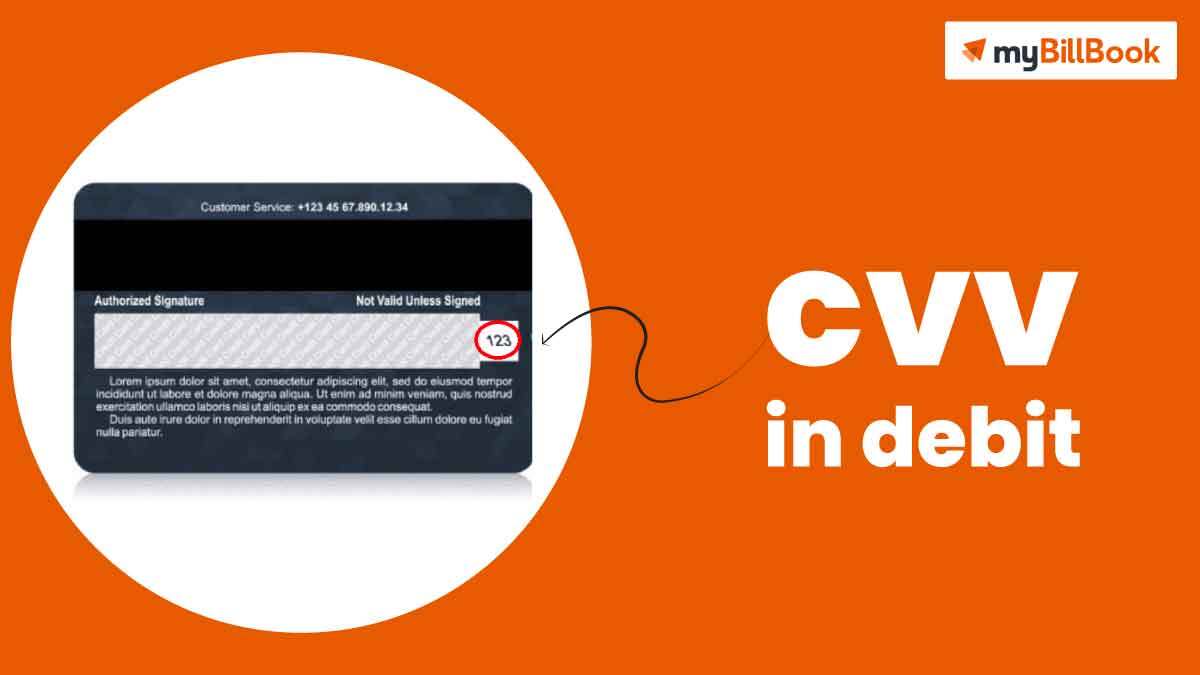
Traditional security measures for debit cards rely on physical attributes and encoded data. The CVV (Card Verification Value) is a prime example – a three or four-digit security code typically found on the back of a credit or debit card. Its primary purpose is to verify that the physical card is in the possession of the user during a transaction, especially for online or phone purchases where a physical swipe is not possible. This code acts as a crucial layer of fraud prevention.
However, the digital age and the proliferation of advanced imaging technologies are opening up new avenues for authentication that go beyond simple visual recognition or magnetic stripe data. Instead of a static numerical code, we are exploring dynamic, image-based verification methods. This involves leveraging the sophisticated capabilities of modern cameras and imaging systems to generate and interpret unique visual identifiers. These identifiers are not just about recognizing a face or an object; they are about capturing subtle, inherent characteristics within an image that can serve as a digital fingerprint.
The core principle is to embed a form of “visual CVV” within the image data itself, detectable and verifiable by specialized imaging systems. This “visual CVV” isn’t a printed number. Instead, it can be derived from:
- Micro-patterns and noise signatures: Every imaging sensor has unique imperfections and noise characteristics. Sophisticated algorithms can analyze these inherent variations to create a unique identifier for that specific camera or imaging system.
- Subtle light interactions: The way light interacts with surfaces, even seemingly uniform ones, can create incredibly detailed and unique patterns. Advanced cameras, particularly those with high dynamic range and spectral sensitivity, can capture these nuances.
- Proprietary encoding within image data: Similar to how some security features are embedded in physical currency, it’s conceivable to embed imperceptible digital watermarks or codes within the image data that are only detectable by authorized imaging hardware and software.
This concept moves beyond simple facial recognition, which can be fooled by high-quality photographs or masks. A “visual CVV” approach aims for a deeper, more intrinsic form of verification that is computationally difficult to replicate.
From Static Codes to Dynamic Signatures
The transition from static CVV codes to dynamic visual signatures represents a significant leap in how we conceive of digital and physical security. The traditional CVV, while effective for its time, is static and, once compromised, remains compromised. If a hacker obtains a list of card numbers and CVVs, they can potentially exploit this information.
Visual authentication, on the other hand, can be inherently dynamic. Imagine a scenario where a camera system not only captures an image but also analyzes its unique visual characteristics to generate a temporary, session-specific authentication key. This key would be generated on-the-fly and would be specific to the camera, the lighting conditions, and potentially even the user’s interaction with the device at that moment.
The Role of High-Resolution and Spectral Imaging
The effectiveness of any visual authentication system hinges on the capabilities of the imaging hardware.
High-Resolution Imaging
Modern cameras boast incredible resolution, capturing an astonishing amount of detail. This is crucial for visual authentication because subtle variations that might be imperceptible to the human eye can be clearly distinguished by high-resolution sensors. These variations, such as microscopic surface textures or minute imperfections, can form the basis of a unique visual signature. For instance, a camera analyzing a specific material might detect unique patterns at a microscopic level, providing a distinct identifier.
Spectral Imaging and Multi-Band Captures
Beyond the visible spectrum, advanced cameras can capture light in various bands, including infrared (IR) and ultraviolet (UV). Different materials and surfaces interact with these different wavelengths of light in unique ways. For example, certain inks or security features on a card might be invisible under normal light but glow under UV light or absorb IR light differently.
By capturing images across multiple spectral bands, a more robust and complex visual signature can be generated. This multi-spectral data provides a richer dataset for authentication algorithms, making it significantly harder for counterfeiters to replicate. The specific spectral response of a material or an embedded security feature can act as a sophisticated, multi-layered “CVV” within the image.
Implementing Visual CVV Concepts in Real-World Scenarios
The theoretical concept of a “visual CVV” can be translated into practical applications across various industries, particularly those reliant on secure imaging.
Secure Document Verification
One of the most immediate applications is in the verification of official documents like passports, driver’s licenses, and identity cards. Current methods often involve holograms, micro-printing, and UV-sensitive inks. A visual CVV system could enhance this by:
- Capturing multi-spectral images: A scanner equipped with advanced cameras could capture images across the visible, UV, and IR spectrum.
- Analyzing inherent image noise: The unique noise pattern of the scanner’s sensor could be cross-referenced with the captured image data for an additional layer of authenticity.
- Detecting subtle material variations: Algorithms could analyze microscopic textures and material properties embedded within the document itself, such as security threads or special paper fibers, to confirm their legitimacy.
This would move beyond simply comparing a photograph to the person holding the document. It would be a deep analysis of the document’s physical properties as captured by sophisticated imaging.
Authentication of Physical Goods
In the realm of high-value goods, such as luxury items, pharmaceuticals, or electronics, counterfeit products are a significant problem. Visual CVV technology could be applied to authenticate genuine items.
- Unique product marking: Manufacturers could embed imperceptible markings or patterns onto their products during the manufacturing process. These markings, when captured by a specialized camera, would generate a unique visual code.
- Packaging integrity checks: Even the packaging could be analyzed. The specific way light reflects off the plastic film, the subtle texture of the cardboard, or the unique patterns in the ink used for printing could all contribute to a verifiable visual signature.
- Traceability and anti-counterfeiting: A consumer could use a smartphone app with advanced camera capabilities to scan a product, and the app would instantly verify its authenticity by matching the captured visual data against a secure database of known product signatures.
This would provide a more sophisticated alternative to simple serial number verification or QR codes, which can be easily copied.
Biometric Security Enhancement
While not directly replacing traditional biometrics like fingerprint or facial recognition, visual CVV concepts can enhance their security.
- Liveness detection: Current facial recognition systems can sometimes be fooled by high-resolution photos or videos. By incorporating visual CVV analysis, the system could not only recognize a face but also verify the intrinsic visual properties of the skin, eye, or even the unique way light interacts with the subject’s features in real-time. This would make it far more difficult to impersonate someone.
- Implicit authentication: Imagine a system that, when you pick up your phone or approach a secure terminal, implicitly verifies your identity through the unique visual characteristics of your hand or even your gait as captured by a camera, without requiring an explicit scan or input. This would be a more seamless and less intrusive form of security.
Challenges and Future Directions
The development and widespread adoption of visual CVV technology are not without their hurdles.
Technical Sophistication and Cost
Implementing robust visual authentication systems requires highly sophisticated imaging hardware and advanced computational power for real-time analysis. The cost of such systems, especially for consumer-level devices, can be a significant barrier. Miniaturizing these technologies and reducing their cost will be crucial for broad adoption.
Standardization and Interoperability
For visual CVV systems to be effective across different platforms and devices, standardization will be essential. Without common protocols and data formats, a visual signature generated by one system might not be verifiable by another, limiting its practical utility. Developing industry-wide standards for image capture, data encoding, and verification algorithms will be a critical undertaking.
Privacy Concerns
As imaging systems become more sophisticated and capable of capturing nuanced visual data, privacy concerns will inevitably arise. Users will need to be assured that their visual data is being handled securely and ethically, and that it is not being used for purposes beyond authentication. Transparency and robust data protection measures will be paramount.
Algorithm Development and Adversarial Attacks
The algorithms used for visual CVV generation and verification will need to be incredibly robust. They must be able to reliably distinguish authentic signatures from sophisticated forgeries and must be resilient to adversarial attacks, where malicious actors attempt to trick the system. Continuous research and development in machine learning and computer vision will be necessary to stay ahead of evolving threats.
Future Outlook
Despite these challenges, the potential of visual authentication, inspired by the concept of a “visual CVV,” is immense. We are likely to see a gradual integration of these technologies, starting with high-security applications and progressively moving into consumer devices.
Imagine future debit cards that, in addition to their magnetic stripe and chip, possess subtle, unique visual properties embedded within their design or material. When tapped against a reader equipped with an advanced imaging sensor, the card’s intrinsic visual signature would be analyzed in conjunction with the reader’s unique imaging characteristics, creating an almost unforgeable layer of authentication.
The evolution from the simple three-digit CVV on a plastic card to complex, dynamic visual signatures captured by advanced imaging systems represents a significant paradigm shift. As cameras become more intelligent and our understanding of how to extract unique identifiers from visual data deepens, the concept of a “visual CVV” will undoubtedly play a crucial role in securing our digital and physical world. This is not just about preventing fraud; it’s about building a more trustworthy and seamless interaction between humans, devices, and the digital realm, all powered by the sophisticated language of light and image.
