In the rapidly evolving landscape of unmanned aerial vehicles (UAVs), the focus has shifted from mere flight mechanics to the sophisticated management of the data these machines generate. When we discuss “Access” in the context of modern drone technology, we aren’t simply talking about a legacy database program; rather, we are discussing the high-level architecture of fleet management, remote sensing, and the secure protocols that allow operators to control complex aerial assets. At the heart of this digital infrastructure lies the “Primary Key”—a fundamental concept in data science that has become the backbone of drone telemetry, pilot authentication, and autonomous flight logging.
As drone operations scale from hobbyist flights to enterprise-level fleet deployments, the ability to uniquely identify, categorize, and secure every packet of information becomes paramount. In this exploration of drone tech and innovation, we will dissect the technical significance of the primary key within drone “Access” systems, exploring how it ensures operational safety, regulatory compliance, and the seamless integration of AI-driven remote sensing.
The Role of Unique Identifiers in Drone Data Infrastructure
To understand the “Primary Key” in a drone ecosystem, one must first recognize that a drone is essentially a flying IoT (Internet of Things) device. Every second of flight generates thousands of data points—GPS coordinates, battery levels, motor RPMs, and gimbal angles. Without a rigorous structural framework to organize this information, the data becomes a chaotic “data swamp” rather than a valuable asset.
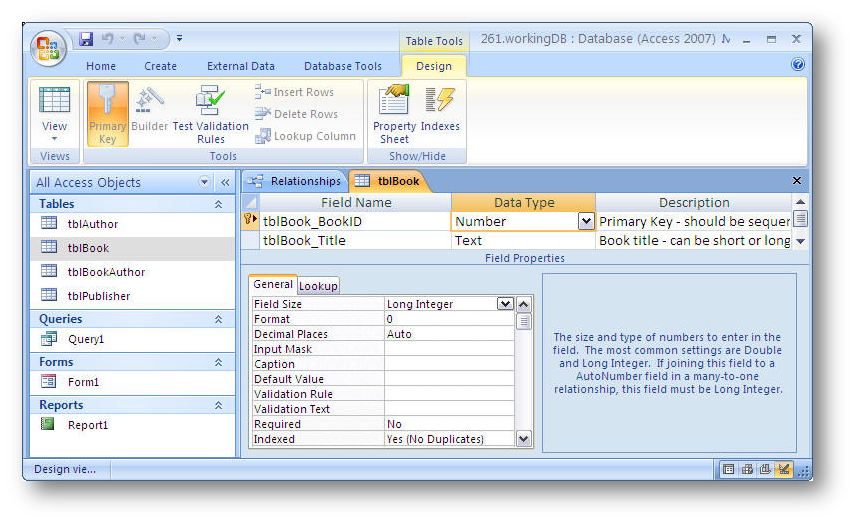
Hardware IDs as the Ultimate Primary Key
In drone technology, the most basic form of a primary key is the hardware’s unique serial number or Universal Unique Identifier (UUID). Just as a primary key in a database ensures that no two records are identical, the UUID ensures that every command sent and every log received is attributed to a specific physical unit. This is critical for maintenance tracking. For example, if a fleet manager sees a recurring vibration error in their “Access” dashboard, the primary key allows the software to link that specific error to a specific airframe’s history, preventing a catastrophic failure during the next mission.
Remote ID and Regulatory Tracking
The integration of FAA-mandated Remote ID is perhaps the most visible application of the primary key concept in the drone world today. Remote ID functions as a digital license plate. This unique identifier allows the “Access” systems used by air traffic control and law enforcement to distinguish between a legitimate commercial operation and an unauthorized flight. By using a primary key for each drone, the innovation in airspace management ensures that security protocols can be enacted without disrupting the entire local UAV network.
Managing Flight Log Databases and Secure System Access
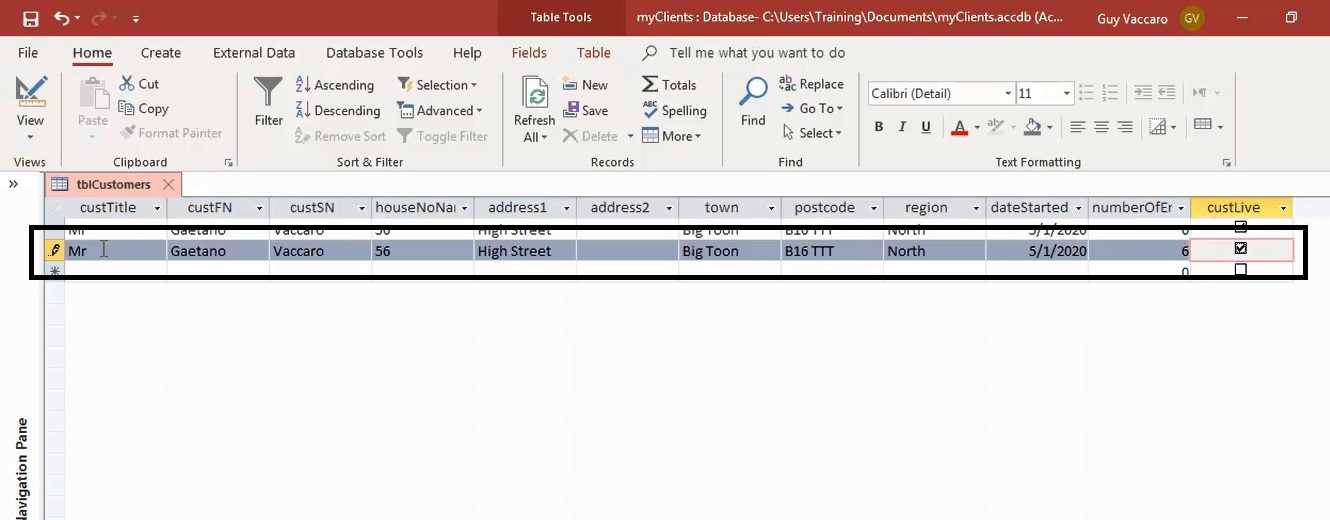
The term “Access” in professional drone circles frequently refers to the permission layers and software portals used by large enterprises to manage their pilots and assets. Within these platforms (such as DJI FlightHub or AirData), the “Primary Key” serves as the anchor for relational data—connecting a pilot’s identity to a specific flight log and a specific battery cycle.
Relational Data in Fleet Management
Modern drone operations are rarely solo endeavors. They involve teams of pilots, observers, and data analysts. In a fleet management database, the primary key enables “relational” mapping. For instance, a “Flight ID” (the primary key) can be linked to a “Pilot ID” (a secondary key) and a “Project ID.” This allows for complex queries, such as “How many hours did Pilot A spend on Project B using Drone C?” This level of granular insight is what allows companies to optimize their Return on Investment (ROI) and maintain the highest safety standards.
Ensuring Data Integrity in Cloud-Based Remote Sensing
When drones are used for remote sensing—such as LIDAR mapping or thermal inspections—the volume of data is immense. “Access” to this data must be both fast and secure. By utilizing primary keys in the cloud architecture, developers ensure data integrity. If a data packet is corrupted during a 5G transmission from the drone to the server, the system uses the primary key to identify exactly which segment of the mission is missing, allowing for automated re-transmission. This innovation eliminates the need for manual data checking, significantly speeding up the “drone-to-decision” workflow.

The Integration of Remote ID and Secure Access Control
As we move toward a future of Beyond Visual Line of Sight (BVLOS) operations, the “Access” part of drone tech becomes a security priority. Unauthorized access to a drone’s command link could have disastrous consequences. Here, the concept of a primary key evolves into a cryptographic token.
Encrypted Communication Protocols
In high-end drone technology, “Access” isn’t just about viewing data; it’s about the handshake between the controller and the UAV. Every session is assigned a unique session key—a temporary primary key—that encrypts the link. This prevents “man-in-the-middle” attacks where a third party might attempt to hijack the drone. Tech innovations in AES-256 bit encryption rely heavily on these unique identifiers to ensure that only the authorized pilot has “Access” to the flight systems.
User Permissions and Access Control Levels (ACL)
Large-scale drone deployments require tiered access. A junior pilot might have “Access” to fly the drone but not to change the geofencing parameters or update the firmware. An administrator, however, has full access. The primary key in the user database links these specific permissions to the individual’s biometric or two-factor authentication (2FA) login. This ensures that the technical “keys to the kingdom” are never misplaced and that every change made to the drone’s internal software is logged against a non-nullable primary key, creating a permanent audit trail.
Innovations in Autonomous Data Processing and Mapping
In the niche of mapping and remote sensing, the primary key takes on a spatial dimension. When drones capture thousands of high-resolution images to create a 3D orthomosaic, each image is tagged with metadata.
Stacking Temporal Data Sets
One of the most exciting innovations in drone tech is temporal analysis—monitoring how a site changes over time. By using geolocated coordinates as a spatial primary key, “Access” portals can “stack” maps from January, March, and June directly on top of one another. The software recognizes that the data points refer to the exact same physical location, allowing for automated change detection. This is used extensively in construction and environmental monitoring to track erosion, stock-pile volumes, or building progress with centimeter-level accuracy.
AI-Driven Metadata Tagging
AI is now being used to automatically tag objects within drone imagery. For example, in utility inspections, an AI might identify a “Cracked Insulator.” To manage thousands of such detections across miles of power lines, each “Event” is assigned a primary key in the inspection database. This allows the utility company to “Access” a list of all faulty components and sort them by severity, location, or date of discovery. This transition from raw video to actionable, indexed data is the hallmark of the current era of drone innovation.
The Future of “Access” and Data Management in UAVs
The convergence of 5G, AI, and edge computing is making the management of drone data more complex and more vital than ever. The “Primary Key” is no longer just a term for database administrators; it is a critical component of flight safety and operational efficiency. When we ask “What is primary key in access” within the drone industry, we are really asking how we maintain a “Single Source of Truth” in an environment where millions of drones are eventually expected to share the same airspace.
As autonomous systems become more prevalent, the “Access” systems will likely move toward decentralized ledgers (like blockchain) where the primary key is immutable and globally verifiable. This would allow a drone from one manufacturer to communicate its intent and identity to a drone from another manufacturer or to a “smart city” infrastructure, ensuring that everyone has access to the same, verified data.
In conclusion, the “Primary Key” is the invisible thread that sews together the disparate pieces of the drone tech world. It connects the physical drone to the pilot, the flight log to the regulatory agency, and the raw sensor data to the final analytical report. By mastering these data structures, the drone industry is moving away from being a “hobbyist niche” and into its rightful place as a pillar of the global digital economy. Whether it is through Remote ID, secure fleet management, or AI-powered mapping, the principles of data integrity and secure access remain the primary keys to unlocking the full potential of aerial innovation.
