In the ever-evolving landscape of digital connectivity, the security of network access has become paramount. As businesses increasingly rely on the internet for operations, communication, and data storage, the threat surface expands exponentially. Malicious actors are constantly developing sophisticated methods to breach defenses, exploit vulnerabilities, and compromise sensitive information. Within this challenging environment, a critical layer of security infrastructure has emerged as indispensable: the Secure Web Gateway (SWG). An SWG acts as a crucial intermediary between users and the internet, inspecting all web traffic to protect organizations from a wide array of cyber threats and enforce acceptable use policies.

The fundamental concept behind an SWG is to provide a centralized point of control and security for outbound web traffic. Instead of relying solely on individual endpoint security solutions, which can be fragmented and prone to bypass, an SWG consolidates security functions at the network perimeter. This approach offers a more robust and manageable defense against malware, phishing attacks, data leakage, and other web-based threats. By intercepting, inspecting, and sanitizing all web requests and responses, SWGs ensure that only legitimate and safe content reaches internal users and that sensitive data does not inadvertently leave the organization.
The necessity of SWGs is underscored by the sheer volume and sophistication of internet-borne threats. Traditional security measures, such as firewalls, are primarily designed to control network access at the port and protocol level. While essential, they often lack the granular inspection capabilities required to detect and block advanced threats embedded within web traffic. This is where SWGs excel. They delve deeper into the content of web communications, examining not just the origin and destination but also the payload, looking for malicious code, unauthorized data transfers, and policy violations. This comprehensive inspection capability is vital for protecting organizations in today’s interconnected world.
Core Functionality of a Secure Web Gateway
At its heart, a Secure Web Gateway is a comprehensive security solution designed to safeguard an organization’s users and data from the myriad threats present on the internet. It achieves this through a multifaceted approach, combining several key security technologies and functionalities. Understanding these core components is essential to appreciating the value and effectiveness of an SWG in modern cybersecurity strategies.
Threat Prevention
One of the primary roles of an SWG is to proactively prevent cyber threats from entering the network. This involves a sophisticated array of detection and blocking mechanisms designed to identify and neutralize malware, phishing attempts, and other malicious content before it can impact users or systems.
Malware Detection and Blocking
SWGs employ advanced malware detection techniques, including signature-based scanning, heuristic analysis, and sandboxing. Signature-based scanning compares incoming files and content against a database of known malware signatures. Heuristic analysis looks for suspicious patterns and behaviors that indicate potential malware, even if a specific signature is not yet available. Sandboxing involves executing suspicious files in an isolated environment to observe their behavior, allowing the SWG to identify zero-day threats that have not been previously cataloged. Once identified, the SWG can then block the download or execution of the malicious content, preventing it from infecting user devices.
Web Filtering and URL Categorization
Web filtering is a critical function of an SWG that allows organizations to control the types of websites their users can access. This is often achieved through URL categorization, where the SWG maintains a vast database of websites, classifying them based on their content and purpose. Organizations can then create policies to block access to categories deemed inappropriate or risky, such as adult content, gambling sites, or known sources of malware. This not only enhances security by reducing exposure to malicious sites but also helps enforce acceptable use policies and improve employee productivity.
Anti-Phishing and Anti-Malicious URL Detection
Phishing attacks, which aim to trick users into revealing sensitive information, and the use of malicious URLs to deliver malware are persistent threats. SWGs are equipped with specialized engines to detect and block access to known phishing sites and URLs that have been identified as malicious. This often involves real-time analysis of URLs, comparing them against constantly updated threat intelligence feeds, and examining the content of web pages for signs of deceptive practices.
Data Loss Prevention (DLP)
Beyond inbound threats, SWGs also play a vital role in preventing sensitive data from leaving the organization. Data Loss Prevention (DLP) capabilities within an SWG monitor outbound web traffic for specific types of sensitive data, such as credit card numbers, social security numbers, or proprietary intellectual property. If the SWG detects that such data is being transmitted through unauthorized channels or in violation of company policy, it can block the transmission, encrypt the data, or alert security personnel. This is crucial for maintaining regulatory compliance and protecting intellectual property.
Policy Enforcement
Beyond simply blocking threats, SWGs are instrumental in enforcing organizational security policies and acceptable use guidelines for internet access. This granular control over web usage ensures that employees are using internet resources appropriately and that the network remains secure.
Granular Access Control
SWGs enable administrators to define detailed access control policies based on user identity, group membership, time of day, and even the type of application being used. This allows for tailored security postures, granting different levels of access to different user groups. For instance, executive access might be less restricted for certain business-critical applications, while general employee access might be more tightly controlled.
Application Control
In today’s environment, much internet traffic is generated by applications rather than direct web browsing. SWGs can identify and control these applications, allowing administrators to permit, block, or throttle specific applications like social media, streaming services, or file-sharing programs. This not only helps in managing bandwidth but also in preventing the use of potentially risky or unproductive applications.
Content Inspection and Sanitization
SWGs can inspect the content of web pages and files for specific keywords, patterns, or malicious code. They can also perform content sanitization, which involves removing potentially harmful elements from web pages or files before they are delivered to the user. This might include stripping out active content like scripts or applets that could be exploited.

Advanced Features and Deployment Models
As the cybersecurity landscape continues to evolve, Secure Web Gateways have also advanced, incorporating more sophisticated features and offering flexible deployment options to meet the diverse needs of organizations.
Advanced Threat Intelligence Integration
Modern SWGs leverage extensive threat intelligence feeds from various sources to stay ahead of emerging threats. These feeds are continuously updated with information on new malware variants, malicious URLs, botnet command-and-control servers, and phishing campaigns. By integrating this real-time intelligence, SWGs can make more informed decisions about what traffic to block, significantly enhancing their ability to protect against zero-day threats and sophisticated attacks. This dynamic approach ensures that the gateway’s defenses are always current and effective.
SSL/TLS Decryption and Inspection
A significant portion of web traffic today is encrypted using SSL/TLS protocols. While this encryption is essential for privacy and security, it also presents a challenge for security solutions, as it can be used to hide malicious content. Advanced SWGs possess the capability to decrypt SSL/TLS traffic, inspect its content for threats, and then re-encrypt it before forwarding it to the user. This “SSL inspection” or “SSL decryption” feature is critical for uncovering threats hidden within encrypted channels, such as malware downloads or data exfiltration attempts. However, it must be implemented carefully to respect privacy concerns and comply with relevant regulations.
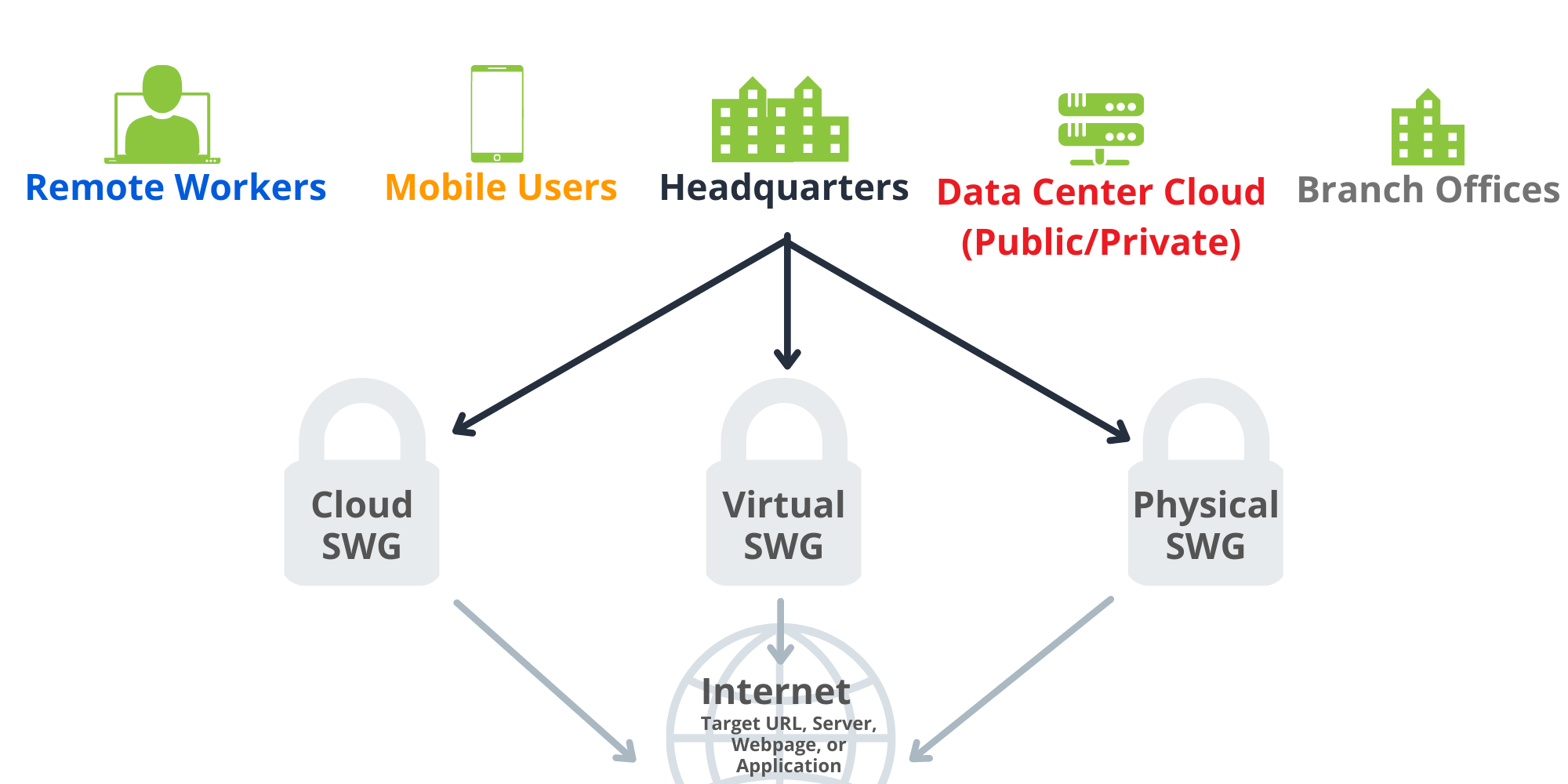
Cloud-Based vs. On-Premise Deployments
Secure Web Gateways can be deployed in various models to suit an organization’s infrastructure and security strategy.
Cloud-Based SWGs (Software-as-a-Service)
Cloud-based SWGs, often referred to as SWG-as-a-Service or Security Service Edge (SSE) components, offer significant advantages in terms of scalability, ease of management, and rapid deployment. In this model, the SWG functionality is hosted by a cloud provider, and traffic is routed through the provider’s secure infrastructure. This eliminates the need for on-premise hardware and software, reducing capital expenditure and IT overhead. Cloud-based SWGs are particularly well-suited for organizations with a distributed workforce or those embracing a cloud-first strategy. They benefit from the provider’s extensive global infrastructure and continuous updates to threat intelligence.
On-Premise SWGs
On-premise SWGs are deployed and managed within an organization’s own data center. This model provides organizations with complete control over their security infrastructure and data. It is often chosen by organizations with strict data residency requirements, highly sensitive data, or existing investments in on-premise security. While offering greater control, on-premise solutions require more resources for deployment, maintenance, and updates. Administrators are responsible for managing hardware, software, and threat intelligence feeds.
Hybrid Deployments
Many organizations opt for a hybrid approach, combining elements of both cloud-based and on-premise SWGs. This can involve using a cloud SWG for remote users and branch offices while maintaining an on-premise solution for the central corporate network. This offers a balance of flexibility, control, and cost-effectiveness, allowing organizations to tailor their security posture to specific needs and locations.
The Role of Secure Web Gateways in Modern Cybersecurity
In an era characterized by pervasive cyber threats and an increasingly complex digital infrastructure, the Secure Web Gateway stands as a cornerstone of effective cybersecurity. Its ability to provide centralized, granular control over internet access, coupled with its sophisticated threat prevention and policy enforcement capabilities, makes it an indispensable component of any robust security strategy.
Protecting Against Evolving Threats
The digital threat landscape is in constant flux, with new vulnerabilities discovered and novel attack vectors emerging regularly. SWGs, by integrating advanced threat intelligence and employing multiple layers of defense, are continuously updated to combat these evolving threats. From sophisticated malware and ransomware to evasive phishing schemes and zero-day exploits, the proactive inspection and blocking mechanisms of an SWG provide a crucial line of defense. The ability to inspect encrypted traffic further closes potential loopholes that attackers might exploit.
Ensuring Regulatory Compliance
Many industries are subject to stringent regulations regarding data privacy and security, such as GDPR, HIPAA, and PCI DSS. These regulations often mandate specific controls on data handling and internet usage. SWGs play a critical role in helping organizations meet these compliance requirements by enabling granular access control, enforcing data loss prevention policies, and providing audit trails of web activity. By ensuring that sensitive data is protected and that internet usage adheres to policy, SWGs contribute significantly to an organization’s compliance posture.
Enhancing User Productivity and Network Performance
While primarily a security tool, an SWG can also contribute to improved user productivity and network performance. Through effective web filtering, administrators can block access to non-work-related websites and distracting applications, helping employees stay focused on their tasks. Furthermore, by controlling bandwidth-intensive applications and potentially malicious content, SWGs can help optimize network performance and ensure that critical business applications have the necessary resources.
Supporting Remote and Mobile Workforces
The rise of remote and mobile work has created new challenges for cybersecurity. Employees accessing corporate resources from unmanaged networks and devices can significantly increase an organization’s vulnerability. SWGs, particularly cloud-based solutions, are adept at extending consistent security policies and controls to these dispersed users, regardless of their location or the device they are using. This ensures that all access to the internet and corporate resources is secured, creating a more unified and resilient security posture for the entire organization.
In conclusion, the Secure Web Gateway is far more than just a network appliance; it is a dynamic and essential security platform that provides comprehensive protection against the pervasive threats of the internet. By understanding its core functionalities, advanced features, and flexible deployment options, organizations can leverage SWGs to build a strong, resilient security foundation, safeguarding their data, users, and overall business operations in the digital age.
