Military identification cards serve a critical function within the armed forces, acting as a primary means of verifying a service member’s identity, status, and access privileges. Far from being simple pieces of plastic, these cards are sophisticated security documents, incorporating advanced features to prevent counterfeiting and ensure their integrity. The evolution of military ID cards reflects the broader advancements in identification technology and the ever-increasing need for robust security measures. Understanding their design, the information they contain, and the security features employed offers valuable insight into the operational security and administrative processes of the military.
The Evolution and Purpose of Military Identification
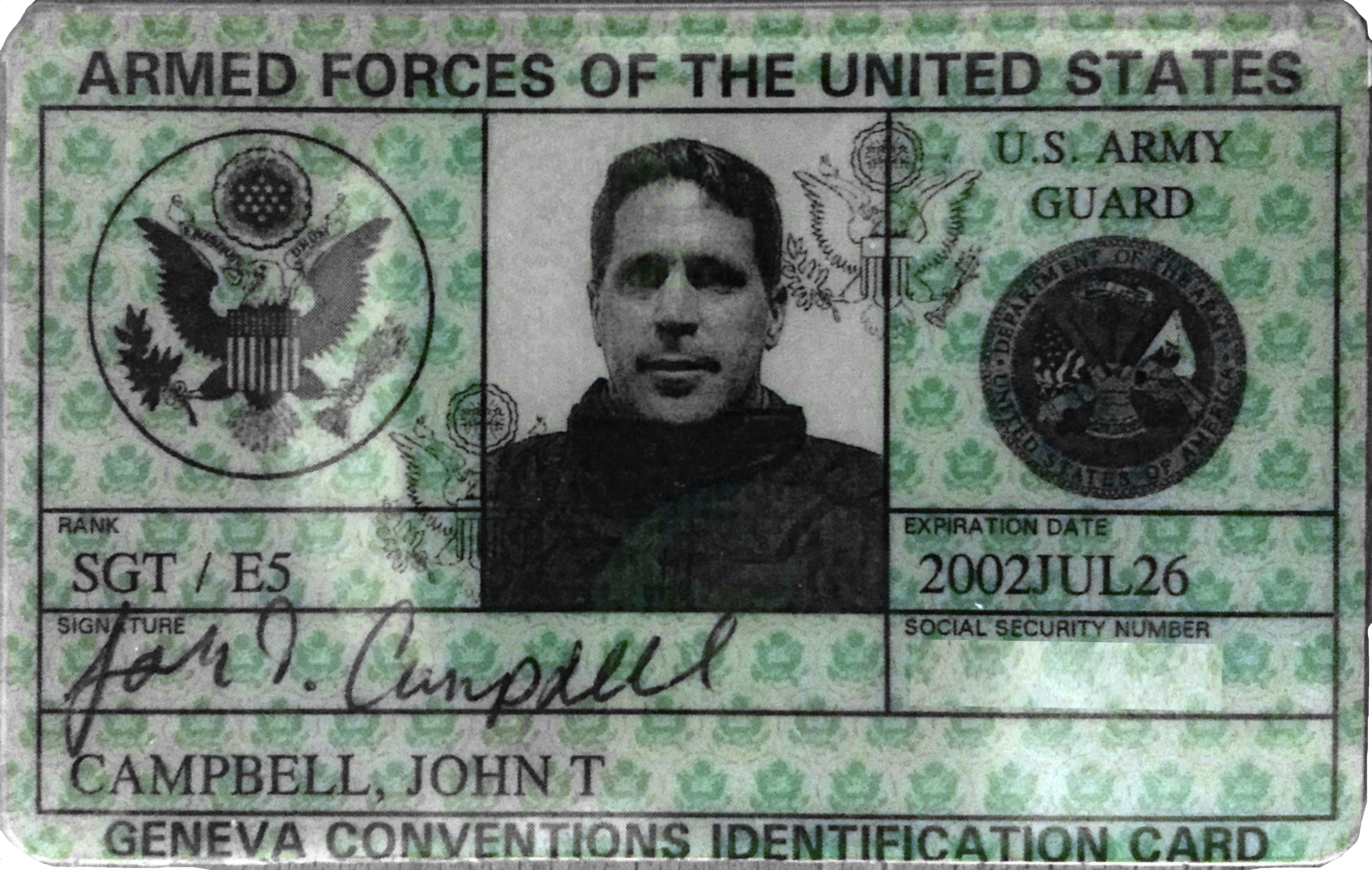
The concept of identifying military personnel has a long history, predating modern plastic cards. Historically, identification might have involved simple badges, written orders, or even verbal affirmations. However, as military operations became more complex and global, the need for a standardized and secure method of identification became paramount. Early forms of military identification often involved paper documents or metal tags, which were susceptible to damage, loss, and forgery.
The advent of more durable materials and printing technologies in the mid-20th century paved the way for the modern military ID card. The primary purpose of these cards remains consistent: to unequivocally identify an individual as a member of the armed forces. This identification is crucial for a multitude of reasons, including:
- Access Control: Granting entry to military installations, secure facilities, and restricted areas.
- Benefits and Entitlements: Verifying eligibility for medical care, commissary and exchange privileges, housing, and other service-related benefits.
- Travel: Facilitating official travel and ensuring proper identification when overseas or in transit.
- Force Protection: Enhancing security by allowing personnel to quickly and reliably identify fellow service members and distinguish them from potential threats.
- Administrative Purposes: Serving as a key document for pay, promotions, and other personnel management functions.
The development of these cards has been driven by a continuous effort to stay ahead of counterfeiters and to incorporate new functionalities that streamline military operations. From simple printed information to the inclusion of magnetic stripes, barcodes, and now sophisticated microchips, each iteration represents an advancement in security and utility.
Key Features and Information on Military ID Cards
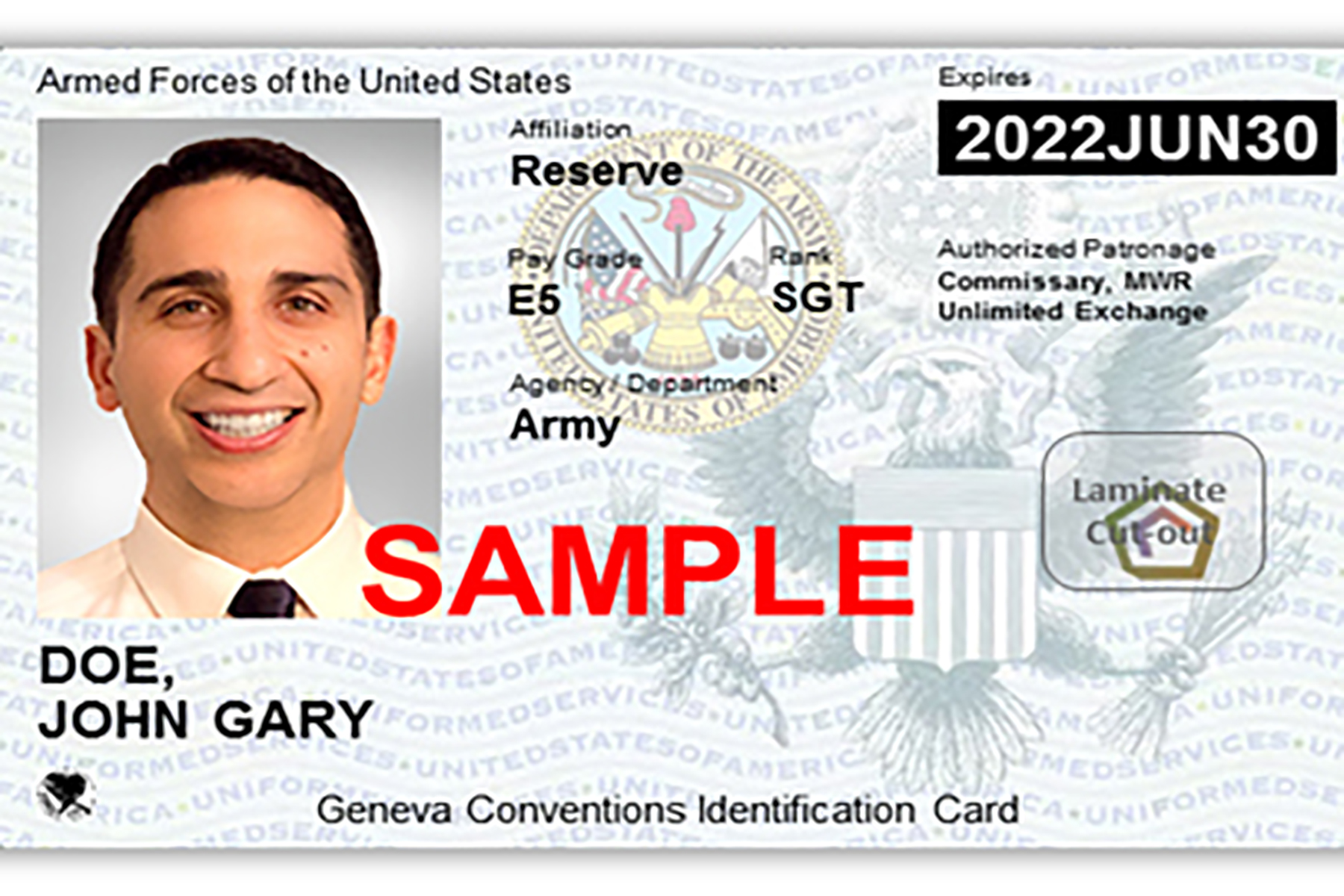
While specific details may vary slightly between branches of service and over time, most modern military ID cards share a common set of features and display essential information. The design is typically standardized to ensure easy recognition and verification across different military contexts.
Front of the Card
The front of the card is where the most immediately identifiable information is presented. This typically includes:
- Service Member’s Photograph: A recent, clear photograph is crucial for visual identification. The size and placement are usually standardized.
- Name: The full legal name of the service member.
- Rank and Title: The current rank (e.g., Sergeant, Lieutenant, Commander) and any relevant title or designation.
- Branch of Service: Clearly indicating whether the individual belongs to the Army, Navy, Air Force, Marine Corps, or Coast Guard. This is often represented by distinct emblems or colors.
- Issuing Authority and Date: Information about the military branch or department that issued the card, along with the date of issuance.
- Expiration Date: A critical security feature, indicating when the card is no longer valid. This helps to prevent the use of outdated or potentially compromised credentials.
- Unique Identification Number: A service-specific number that uniquely identifies the individual within the military system. This is distinct from a social security number.
- Service Component Identifier: A code or symbol indicating the specific component or branch the service member belongs to.
- Security Features: Holograms, microprinting, or other overt security features that are difficult to replicate.
Back of the Card
The back of the card often contains less visually prominent but equally important information and features, including:
- Barcode: A barcode that encodes essential information, allowing for quick scanning and data retrieval by authorized systems. This can include personnel data, security clearances, and access rights.
- Magnetic Stripe: A magnetic stripe, similar to those found on credit cards, which stores encoded data. While still present on some cards, its use is diminishing in favor of chip technology.
- Contact Information: Sometimes, contact information for the issuing authority or relevant personnel office may be present.
- Security Printing: Background patterns or watermarks that are difficult to reproduce, adding another layer of anti-counterfeiting protection.
- Human Readable Data: Certain data may be repeated in a human-readable format for situations where scanning technology is unavailable.
Embedded Technology: The CAC Card
The most significant advancement in military ID cards in recent decades has been the widespread adoption of the Common Access Card (CAC). The CAC is a smart card that contains an embedded microchip. This chip is the heart of the card’s advanced capabilities and is a cornerstone of modern military digital security.
The embedded chip on a CAC card allows for:
- Digital Signatures: Enabling service members to digitally sign documents, authenticate their identity in online systems, and ensure the integrity of electronic communications.
- Encryption: Facilitating the encryption of sensitive data, protecting communications and stored information from unauthorized access.
- Secure Network Access: Providing secure access to classified and unclassified military networks, email systems, and other digital resources.
- Two-Factor Authentication: The physical card itself, combined with a Personal Identification Number (PIN), serves as a robust two-factor authentication mechanism.
The CAC card is designed to be interoperable across different branches of the U.S. military and even with some allied forces, streamlining joint operations and information sharing. The introduction of the CAC has fundamentally changed how military personnel interact with digital systems and has significantly enhanced overall force protection and information security.
Security Features and Anti-Counterfeiting Measures
The integrity of military identification is paramount. Consequently, military ID cards are designed with a comprehensive suite of security features aimed at deterring counterfeiting and ensuring that only authorized individuals possess and use genuine credentials.
Overt Security Features
These are features that are visible to the naked eye and can be easily checked by an observer. They are designed to be difficult to replicate without specialized equipment.
- Holograms: Multi-layered holographic images, often featuring the service emblem or other insignia, are a common and effective overt security feature. These holograms appear to change color or design when viewed from different angles, making them notoriously difficult to counterfeit accurately.
- Microprinting: Extremely small text, often too small to be read without magnification, is printed in specific areas of the card. This microprint can be part of a border, a background pattern, or even within images, serving as a highly effective deterrent against standard photocopying or scanning.
- Embossed Text and Images: Raised lettering and images, particularly the service member’s name, rank, and photograph, provide a tactile element that is difficult for counterfeiters to replicate with flat printing methods.
- UV (Ultraviolet) Features: Invisible inks that become visible only under ultraviolet light are often incorporated into the card’s design. These can include unique patterns, text, or images that fluoresce in specific colors.
- Security Overlays: A clear, durable overlay that protects the printed information and can itself contain embedded security features like microprinting or holographic elements.
Covert Security Features
These features are not readily apparent to the casual observer and require specialized equipment or knowledge to detect. They provide an additional layer of security for thorough verification.
- Security Inks: Special inks that have unique chemical properties or react to specific light frequencies, making them difficult to analyze and reproduce.
- Machine-Readable Features: Beyond visible barcodes, advanced optical features or data embedded in the card material itself that can be read by specialized scanners.
- Chemical Tagging: Microscopic particles or chemical markers embedded within the card material or inks that can be identified through forensic analysis.

Data Security on Smart Cards (CAC)
For smart cards like the CAC, security extends beyond the physical card to the data stored on the embedded chip.
- Encryption: All sensitive data on the chip is encrypted, meaning it can only be accessed and decrypted using the correct cryptographic keys.
- Digital Certificates: The chip contains digital certificates that verify the identity of the cardholder and the authenticity of the card itself.
- PIN Protection: Access to the chip’s functionalities requires a Personal Identification Number (PIN), acting as a secondary authentication factor. Without the correct PIN, the chip’s advanced features cannot be utilized.
- Secure Access Modules (SAMs): In some contexts, secure access modules might be used in conjunction with card readers to further enhance the security of data processing.
The layered approach to security, combining overt, covert, and digital measures, ensures that military ID cards are among the most secure forms of identification in existence. This robust security framework is essential for maintaining operational security and protecting sensitive military information and resources.