Cyberterrorism represents a nexus of advanced technology and malicious intent, leveraging the digital infrastructure that underpins modern society as a battleground. Unlike traditional terrorism, which relies on physical force, cyberterrorism exploits the inherent vulnerabilities of interconnected systems to inflict damage, sow panic, and achieve ideological or political objectives. Within the broader landscape of “Tech & Innovation,” understanding cyberterrorism is crucial, as it signifies both a sophisticated application of technological knowledge for harmful purposes and a driving force for innovative defensive strategies. This phenomenon is not merely about hacking; it’s about weaponizing digital tools to create real-world disruption and fear on a scale previously unimaginable.

Defining Cyberterrorism in the Digital Age
At its core, cyberterrorism can be understood as the premeditated, politically motivated attack against information, computer systems, computer programs, and data that results in violence against non-combatant targets by sub-national groups or clandestine agents. The “Tech & Innovation” aspect here lies in the sophistication required to orchestrate such attacks and the innovative methods employed to bypass state-of-the-art security protocols. It’s an evolution of conflict, shifting from kinetic warfare to a struggle over data integrity, system availability, and control of critical digital infrastructure.
Blurring Lines: Cybercrime vs. Cyberterrorism
A critical distinction within the digital threat landscape, especially relevant to tech professionals, is differentiating cybercrime from cyberterrorism. While both involve illegal activities using technology, their primary motivations and objectives diverge. Cybercrime, often driven by financial gain or personal vendettas, typically involves data theft, ransomware, or fraud. Its impact, though severe for individuals or corporations, rarely extends to widespread societal destabilization or the direct promotion of terror.
Cyberterrorism, conversely, uses similar technological tools but with a distinct ideological or political agenda. Its aim is to incite fear, coerce governments, or disrupt critical national functions, creating consequences that ripple across entire populations. The innovative aspect here is how perpetrators might repurpose tools developed for cybercrime—like sophisticated malware or zero-day exploits—for terroristic ends, demonstrating a dangerous adaptability in their technological approach. This requires continuous innovation in threat intelligence and analysis to identify these subtle shifts in intent and application.
The Role of Technology in Modern Conflict
In contemporary geopolitics, technology has emerged as a pivotal element in conflict, and cyberterrorism exemplifies this shift. Modern nations and critical infrastructure heavily rely on complex networks, SCADA (Supervisory Control and Data Acquisition) systems, and cloud-based services. This dependence creates a vast attack surface, making them attractive targets for groups seeking to leverage advanced technology for destructive ends. The development of sophisticated cyber weapons, the proliferation of open-source hacking tools, and the increasing accessibility of advanced persistent threat (APT) techniques mean that state-level capabilities are increasingly available to non-state actors, blurring the lines of conventional warfare and ushering in an era of asymmetric digital conflict.
Modus Operandi: Technological Vectors of Attack
The operational methods of cyberterrorists are deeply embedded in technological exploitation and innovation. Their success hinges on identifying and leveraging vulnerabilities in hardware, software, and human-computer interfaces to achieve their objectives.
Exploiting Vulnerabilities: Software and Hardware Loopholes
Cyberterrorists extensively research and exploit vulnerabilities in widely used software and hardware systems. This includes zero-day exploits—previously unknown flaws that developers have not had a chance to patch—which are highly prized. They might also exploit misconfigurations in networks, weak authentication protocols, or outdated security practices within organizations. The innovative edge here is not just in discovering these flaws but in chaining multiple vulnerabilities together to create complex attack paths that bypass layered security defenses. For instance, an attack might combine social engineering (phishing) to gain initial access, then leverage a software exploit to elevate privileges, and finally deploy malware to disrupt operations.
Infrastructure as a Target: SCADA and Critical Systems
A primary target for cyberterrorist groups is critical national infrastructure (CNI), which includes energy grids, water treatment plants, transportation networks, and healthcare systems. These systems often rely on industrial control systems (ICS) and SCADA technologies that, historically, were not designed with robust cybersecurity in mind. An attack on a power grid, for example, could plunge regions into darkness, disrupting emergency services, financial markets, and daily life—a classic terroristic outcome achieved through technological means. The innovation required here involves deep understanding of these specialized, often proprietary, industrial protocols and the development of bespoke malware capable of manipulating physical processes through digital commands.
Data Manipulation and Disinformation Campaigns
Beyond direct system disruption, cyberterrorists increasingly engage in data manipulation and disinformation campaigns, a subtle yet powerful form of attack. This involves altering public records, financial data, or scientific information to create chaos or erode public trust. Furthermore, leveraging social media platforms and bot networks, they can disseminate propaganda, fabricate news stories (deepfakes), and amplify divisive narratives. This form of cyberterrorism specifically targets the integrity of information and the societal fabric, demonstrating an innovative approach to psychological warfare through digital channels. The rapid evolution of AI and machine learning tools makes the creation and spread of convincing false narratives more sophisticated and difficult to detect, posing significant challenges for tech companies and intelligence agencies.
Emerging Threats: AI, IoT, and Quantum Computing
The horizon of cyberterrorism is being reshaped by advancements in artificial intelligence (AI), the Internet of Things (IoT), and the nascent field of quantum computing. AI, while offering powerful defensive capabilities, can also be weaponized to automate sophisticated attacks, rapidly identify vulnerabilities, or create highly convincing phishing campaigns. The proliferation of inadequately secured IoT devices—from smart home appliances to industrial sensors—creates a massive, distributed attack surface that could be leveraged for large-scale botnet attacks or surveillance. Looking further ahead, the development of quantum computing poses a theoretical threat to current cryptographic standards, potentially rendering much of today’s secure communication vulnerable. This necessitates urgent innovation in quantum-resistant cryptography, a complex and evolving field within “Tech & Innovation.”
Impact and Consequences: A Technological Perspective
The impact of cyberterrorism extends far beyond the immediate digital sphere, manifesting in tangible real-world consequences driven by technological failures and disruptions.
Disrupting Essential Services and Economic Stability
The most direct and devastating impact of cyberterrorism involves the disruption of essential services. A successful attack on healthcare systems could cripple hospitals, leading to mass casualties. An assault on financial networks could halt transactions, erase records, and trigger economic crises. These aren’t hypothetical scenarios; they represent outcomes directly enabled by the technological interdependencies of modern society. The innovative nature of these attacks means they can be designed to maximize chaos and economic damage, targeting nodes of critical infrastructure whose failure would cascade across multiple sectors.
Erosion of Trust and Societal Disruption
Beyond physical and economic damage, cyberterrorism specifically targets the psychological aspect of societal stability. By demonstrating the vulnerability of seemingly secure systems—governments, banks, public utilities—cyberterrorists aim to erode public trust in institutions and technology itself. Disinformation campaigns, powered by advanced AI and social media algorithms, can amplify societal divisions, incite unrest, and destabilize democratic processes. This technological manipulation of public perception represents a significant threat to civic discourse and social cohesion, demanding innovative solutions in digital forensics and media literacy.
Global Interconnectivity: Amplifying Risk
The global interconnectedness fostered by modern technology, while beneficial for progress, also amplifies the potential reach and impact of cyberterrorist acts. An attack originating in one part of the world can quickly affect systems across continents, demonstrating the borderless nature of cyber threats. Supply chain attacks, where vulnerabilities in one vendor’s software or hardware are exploited to compromise numerous downstream clients, highlight this amplification effect. This global risk profile necessitates a global, technologically driven response.
Innovative Defenses: Countering the Cyberterrorist Threat
The fight against cyberterrorism is a continuous arms race, demanding constant innovation in cybersecurity technologies and strategies. Within the “Tech & Innovation” paradigm, this involves developing proactive defenses, resilient systems, and sophisticated analytical tools.
Advanced Threat Detection and AI-Driven Analytics
Traditional signature-based antivirus systems are increasingly insufficient against the polymorphic and adaptive nature of cyberterrorist malware. Innovative defenses now incorporate AI and machine learning for advanced threat detection. These systems can analyze vast amounts of network traffic, identify anomalous behaviors, and predict potential attack vectors, even for previously unknown threats. Behavioral analytics, anomaly detection, and natural language processing (NLP) are being deployed to detect sophisticated phishing attempts and insider threats, offering a proactive shield against evolving attack methodologies.
Robust Cybersecurity Frameworks and Resilient Infrastructure
Developing robust cybersecurity frameworks and building resilient infrastructure are paramount. This includes implementing zero-trust architectures, where no user or device is trusted by default, regardless of whether they are inside or outside the network perimeter. Continuous vulnerability management, regular penetration testing, and the adoption of secure coding practices are essential to minimize the attack surface. Furthermore, enhancing the resilience of critical infrastructure involves designing systems that can withstand attacks, isolate compromised components, and recover quickly, utilizing redundant systems and automated failovers. The concept of “cyber-resilience” is a key innovation, moving beyond mere prevention to embrace detection, response, and recovery.
International Cooperation and Information Sharing
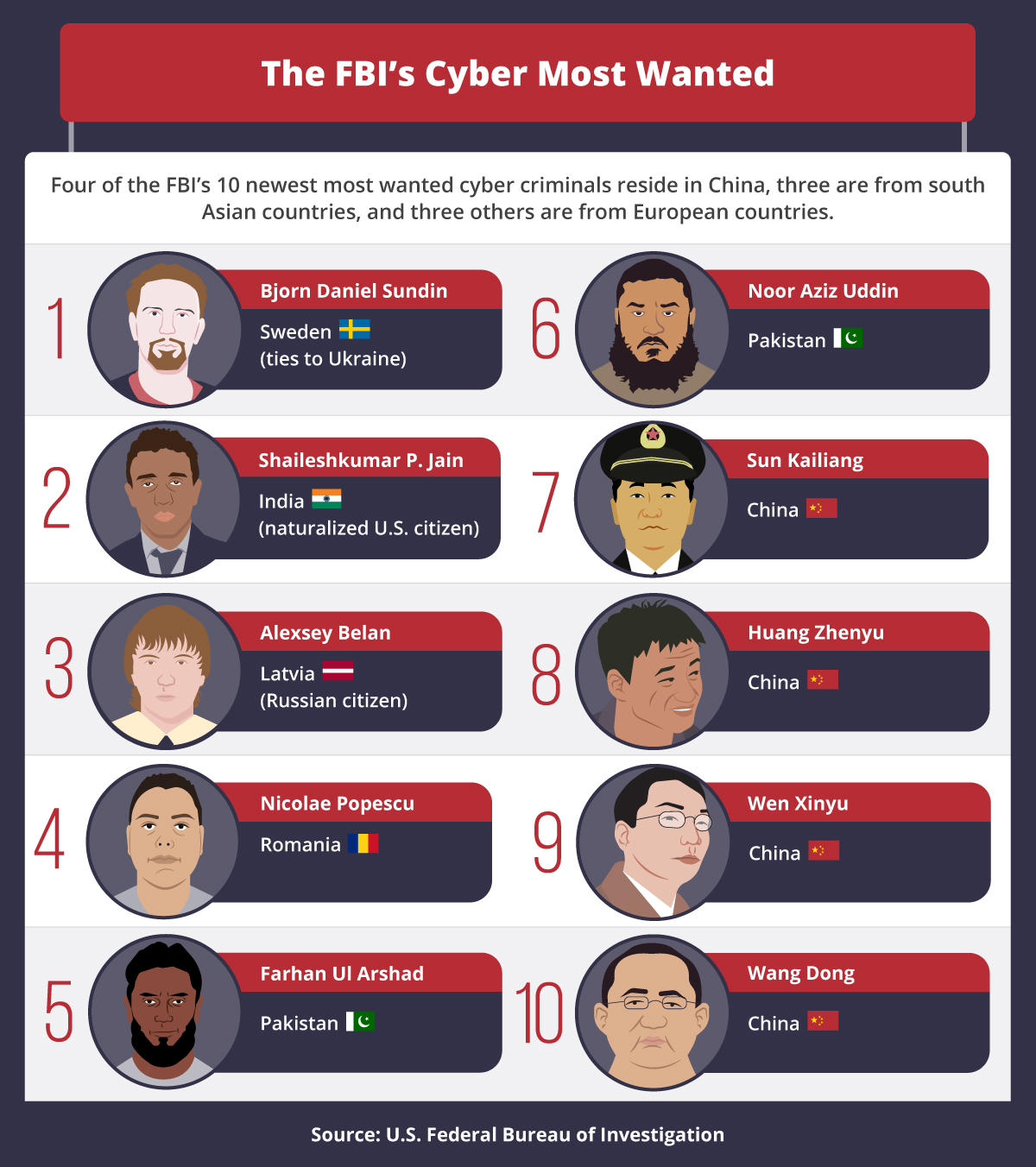
Given the borderless nature of cyberterrorism, international cooperation and timely information sharing are critical. This involves intelligence agencies, law enforcement, and private sector cybersecurity firms collaborating to track threat actors, share indicators of compromise (IoCs), and develop joint defensive strategies. Technological platforms designed for secure information exchange, standardized threat intelligence formats (like STIX/TAXII), and real-time threat feeds are essential innovations enabling a collective defense against sophisticated, globally distributed adversaries.
Quantum Cryptography and Future-Proofing
As quantum computing advances, the need for future-proof security solutions becomes urgent. Quantum cryptography, particularly Quantum Key Distribution (QKD), offers a theoretical solution by leveraging the principles of quantum mechanics to create unhackable encryption keys. While still in its early stages of deployment, research and development in quantum-resistant algorithms are vital for safeguarding future digital communications and data against the potential decryption capabilities of quantum computers. This forward-looking innovation underscores the continuous nature of the technological battle against cyberterrorism, ensuring that security measures evolve alongside emerging threats.
