In an increasingly interconnected and data-driven world, the bedrock of digital trust and operational integrity lies in robust cybersecurity. From the sophisticated algorithms powering autonomous vehicles to the intricate data streams flowing from remote sensing platforms, protecting information from unauthorized access and manipulation is paramount. At the heart of many modern encryption systems, particularly where speed and efficiency are critical, lies the concept of symmetric key cryptography. This fundamental technique represents a cornerstone of data security in the vast and rapidly evolving landscape of Tech & Innovation, offering a powerful yet elegantly simple approach to safeguarding sensitive information.

The Core Concept of Symmetric Key Cryptography
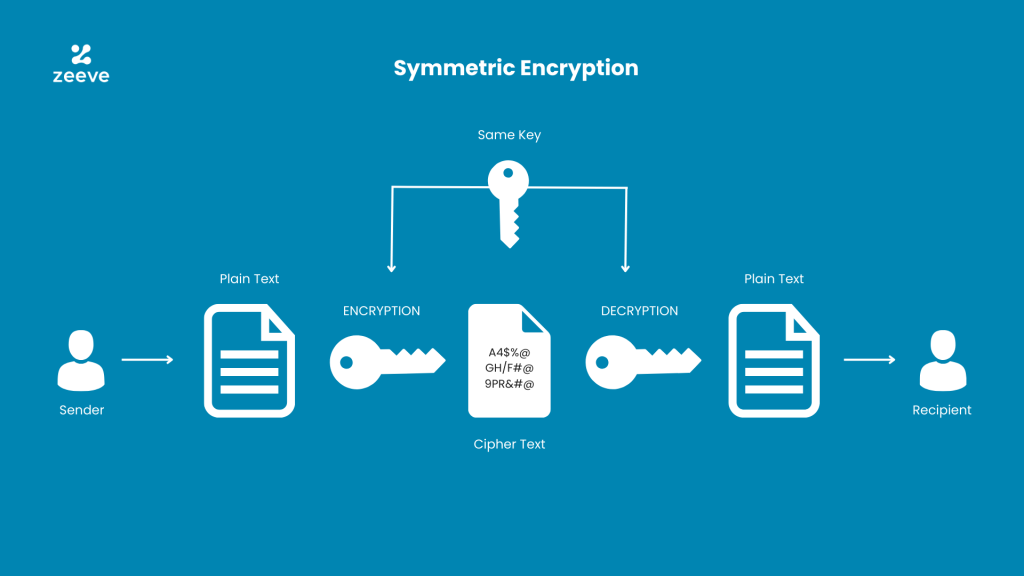
Symmetric key cryptography, sometimes referred to as secret key cryptography, is an encryption method where the same secret key is used for both the encryption of plaintext and the decryption of ciphertext. Imagine a secure lockbox: to lock the box, you use a specific key, and to open it, the exact same key is required. This shared secret is what gives symmetric key systems their unique characteristics and capabilities.
A Shared Secret for Data Protection
The defining characteristic of symmetric key cryptography is the single, shared secret key. This key must be known to both the sender and the receiver of the encrypted message and, crucially, must be kept absolutely secret from anyone else. If an unauthorized entity gains access to this key, they can decrypt all communications encrypted with it, completely compromising the security of the exchange. The strength of the encryption, therefore, is directly tied to the secrecy and randomness of the key itself. Modern symmetric keys typically range from 128 to 256 bits in length, offering a colossal number of possible combinations that make brute-force attacks computationally infeasible with current technology.
How Symmetric Encryption Works
The process of symmetric encryption involves taking a readable message, known as plaintext, and transforming it into an unreadable format, called ciphertext, using an encryption algorithm and the shared secret key. The encryption algorithm applies mathematical operations to the plaintext, guided by the specific values within the key, to scramble the data. Upon receiving the ciphertext, the intended recipient uses the exact same key and the corresponding decryption algorithm to reverse the process, restoring the original plaintext.
Several well-established symmetric key algorithms exist, each with its own nuances in how it performs encryption. The Advanced Encryption Standard (AES) is the most widely adopted and recommended symmetric encryption algorithm today, superseding its predecessor, the Data Encryption Standard (DES). AES operates on blocks of data (typically 128 bits) and employs a series of transformations, including substitution, permutation, and mixing operations, across multiple rounds, all parameterized by the secret key. Its robustness and efficiency have made it the de facto standard for securing everything from financial transactions to government communications and the data transmitted by cutting-edge autonomous systems.
Advantages and Disadvantages in Modern Tech
Symmetric key cryptography offers a compelling set of advantages, particularly in environments where high performance and efficient data handling are paramount. However, it also presents specific challenges that require careful consideration in its implementation across diverse technological applications.
Speed and Efficiency for High-Volume Data
One of the most significant benefits of symmetric key algorithms is their exceptional speed and computational efficiency. The mathematical operations involved in symmetric encryption and decryption are generally less complex than those used in asymmetric (public key) cryptography. This makes symmetric key systems ideal for encrypting large volumes of data quickly and for real-time applications where latency is a critical factor.
Consider the vast amounts of data generated by modern technology: high-resolution sensor feeds from drones, continuous streams of telemetry from autonomous vehicles, or the collective data from millions of Internet of Things (IoT) devices. Encrypting and decrypting this data in real-time demands algorithms that can process information with minimal overhead. Symmetric key cryptography excels in this regard, enabling secure communication and storage without significantly impeding system performance. This efficiency is crucial for maintaining the responsiveness and operational integrity of innovative systems, from AI-powered decision-making platforms to secure remote sensing operations.
The Key Distribution Challenge
Despite its efficiency, the primary drawback of symmetric key cryptography lies in the “key distribution problem.” For any two parties to communicate securely using a symmetric key, they must first securely agree upon and exchange that secret key. If the initial key exchange is compromised, the entire security of subsequent communications is undermined.
In a system with only a few participants, manual or out-of-band key exchange (e.g., physical delivery on a secure device) might be feasible. However, as the number of communicating entities grows, the problem scales dramatically. For instance, in an environment with ‘n’ participants, each needing to communicate securely with every other participant, ‘n * (n-1) / 2’ unique keys would be required. Managing, distributing, and securing this multitude of keys quickly becomes an insurmountable logistical and security challenge in large-scale deployments like interconnected smart cities, vast drone fleets, or global cloud computing infrastructures. This challenge often necessitates the use of asymmetric cryptography or secure key management systems to facilitate the initial secure exchange of symmetric keys.
Scale and Complexity Considerations
While symmetric key encryption is efficient, managing the keys themselves can introduce complexity, especially in distributed systems. Key rotation policies (changing keys periodically to limit exposure in case of compromise), secure key storage, and access control mechanisms for keys are all vital components of a robust security posture. In innovative tech environments with dynamic participants or ephemeral connections, these considerations become even more critical. For example, in a mesh network of autonomous drones, ensuring each new connection is securely established with a unique, shared symmetric key, and that old keys are safely retired, presents a significant architectural challenge. The inherent simplicity of the symmetric encryption operation is thus balanced by the complexity of its lifecycle management at scale.
Applications in Advanced Technologies
The attributes of symmetric key cryptography make it indispensable across a spectrum of advanced technologies, particularly where data integrity, privacy, and secure communication are non-negotiable requirements. Its role extends from the core of secure data storage to enabling trusted interactions within complex, interconnected systems.
Securing IoT and Autonomous Systems
The burgeoning world of the Internet of Things (IoT) and autonomous systems, including robotics and advanced drone platforms, relies heavily on symmetric key cryptography for its operational security. These systems often involve resource-constrained devices that collect, process, and transmit vast amounts of sensitive data—environmental readings, biometric information, location data, or operational commands. Symmetric encryption’s low computational overhead makes it ideal for these devices, which may have limited processing power and battery life.
For instance, sensor data from an agricultural drone conducting remote sensing, or telemetry from a delivery drone, must be encrypted in transit to prevent interception and manipulation. Commands sent to an autonomous vehicle for navigation or payload deployment also require robust encryption to ensure their authenticity and prevent unauthorized control. AES, with its efficiency, is frequently employed to secure the communication channels (e.g., TLS/SSL protocols) between IoT devices and cloud platforms, or between an autonomous drone and its ground control station, protecting both the privacy of the collected data and the integrity of critical operational instructions.
Protecting Data in Cloud Environments
Cloud computing has become the backbone for many modern technological innovations, providing scalable infrastructure for data storage, processing, and application hosting. Symmetric key cryptography plays a crucial role in securing data both at rest (stored on servers) and in transit (moving between clients and servers, or between different cloud services) within these environments.
When data is uploaded to a cloud service, it is typically encrypted using a symmetric key before being stored on disk. This “encryption at rest” ensures that even if an attacker gains unauthorized access to the underlying storage infrastructure, the data remains unreadable without the corresponding key. Similarly, data traveling between a user’s device and the cloud, or between different microservices within a cloud application, is usually secured using protocols like TLS (Transport Layer Security), which predominantly utilize symmetric key algorithms for the bulk of data encryption after an initial asymmetric key exchange. This dual application safeguards sensitive information—from proprietary AI models to customer data processed by innovative software solutions—ensuring its confidentiality and integrity throughout its lifecycle in the cloud.
Ensuring Secure Communication Channels
Beyond IoT and cloud, secure communication channels are fundamental to almost every aspect of modern tech and innovation. Whether it’s end-to-end encrypted messaging applications, virtual private networks (VPNs) enabling secure remote work, or the secure control links for critical infrastructure, symmetric key cryptography is the workhorse.
Protocols like TLS/SSL, which underpin secure web browsing (HTTPS), email (SMTPS), and many other network services, leverage a hybrid cryptographic approach. They begin with an asymmetric key exchange to securely establish a shared secret session key, which is then a symmetric key. Once this session key is established, all subsequent data transmission is encrypted and decrypted using this symmetric key. This hybrid approach capitalizes on the strengths of both cryptographic types: asymmetric cryptography for secure key exchange and authentication, and symmetric cryptography for fast and efficient bulk data encryption. This model is critical for safeguarding sensitive data exchanges in environments ranging from secure drone swarm coordination to real-time data analytics platforms.
Evolving Landscape and Future Perspectives
As technology advances and new threats emerge, the role and implementation of symmetric key cryptography continue to evolve. Its fundamental strengths ensure its continued relevance, even as researchers explore new paradigms and prepare for future computational challenges.
Integration with Hybrid Cryptography
The “key distribution problem” for symmetric keys is largely mitigated through the widespread adoption of hybrid cryptographic systems. As discussed, these systems combine the efficiency of symmetric cryptography for data encryption with the secure key exchange capabilities of asymmetric cryptography. This synergy is fundamental to almost all secure communications in modern networks and will remain a dominant paradigm. Innovators developing new secure communication protocols for autonomous vehicles, decentralized networks, or quantum-resistant communication links will continue to build upon this hybrid model, enhancing it with new key establishment techniques and authentication mechanisms.

Post-Quantum Cryptography and Symmetric Keys
The advent of quantum computing poses a significant long-term threat to current public-key cryptographic algorithms, which rely on the computational difficulty of certain mathematical problems that quantum computers could potentially solve efficiently. While quantum computers do not inherently break symmetric key algorithms in the same way, they could significantly reduce the effective key length. For instance, a 256-bit symmetric key might offer only 128 bits of security against a quantum adversary using Grover’s algorithm.
In response, the cryptographic community is actively developing “post-quantum cryptography” (PQC) – algorithms that are secure against both classical and quantum computers. For symmetric keys, this primarily means increasing key lengths (e.g., from 128-bit to 256-bit or higher for future-proofing) and ensuring the randomness and entropy of keys are impeccably maintained. Research is also exploring new symmetric primitives and modes of operation that might offer enhanced resistance to quantum attacks. Symmetric key algorithms, particularly AES, are considered more resistant to quantum attacks than their asymmetric counterparts, making them a crucial component in the transition to a post-quantum secure future, continuing to serve as the efficient workhorse for bulk data encryption.
In conclusion, symmetric key cryptography is far more than a historical footnote; it is a vital, living technology that underpins the security and functionality of virtually every advanced system and innovation today. Its efficiency, speed, and proven robustness make it indispensable for handling the ever-increasing volumes of data generated and transmitted by the cutting edge of technological progress. As we push the boundaries of AI, autonomy, and connectivity, symmetric key cryptography will remain a foundational element in building a secure and trustworthy digital future.
