Decoding “EXT” in Drone Network Architectures
In the rapidly evolving landscape of unmanned aerial systems (UAS), acronyms and specialized terminology often define the nuances of system design and operation. While “EXT” on a traditional phone number refers to an extension, within the realm of drone technology, its conceptual meaning frequently expands to encompass “External” or “Extended” functionalities, interfaces, or protocols critical to advanced operations. Understanding this interpretation is crucial for professionals designing, deploying, and managing complex drone systems, particularly in contexts involving integrated sensor payloads, communication links, and sophisticated ground control interactions.
External Modules and Peripheral Integration
When we consider the “EXT” in a drone context, one primary interpretation relates to external modules and peripheral integration. Modern drones are not standalone entities; they are highly adaptable platforms designed to carry a diverse array of external sensors, cameras, communication devices, and processing units. These “external extensions” significantly broaden a drone’s capabilities beyond its core flight functions. For instance, a drone might feature an “EXT” port designed for quick attachment of a high-resolution thermal camera for industrial inspection, a LiDAR scanner for topographic mapping, or an advanced multispectral sensor for agricultural analysis.
The concept here revolves around modularity and expandability. Drone manufacturers often provide standardized or proprietary “EXT” interfaces – both physical and logical – that allow third-party developers or end-users to integrate specialized hardware without requiring fundamental alterations to the drone’s core flight controller or propulsion system. These interfaces typically provide power, data transfer protocols (e.g., USB, Ethernet, CAN bus, serial ports), and sometimes even custom trigger signals. This level of external integration is pivotal for tasks demanding specific sensor data, enabling drones to transition from general-purpose aerial vehicles to specialized tools tailored for niche applications like precision agriculture, infrastructure inspection, or search and rescue operations. The robustness and interoperability of these “EXT” connections directly impact a drone’s versatility and its return on investment in professional settings.
Extended Data Protocols and Telemetry
Another significant interpretation of “EXT” within drone technology pertains to “Extended Data Protocols” and enhanced telemetry streams. While basic drones transmit essential flight data—altitude, speed, battery status—advanced applications demand a richer, more comprehensive exchange of information. “EXT” in this sense refers to the additional layers or specialized formats of data that extend beyond standard flight telemetry to include highly specific information from integrated external modules.
For example, a drone performing remote sensing might transmit not only its GPS coordinates but also real-time data streams from its externally mounted LiDAR sensor (point cloud data), thermal camera (temperature maps), or gas detector (chemical concentrations). These “extended” data protocols ensure that the ground control station (GCS) or remote operators receive a holistic view of the operational environment, enabling immediate decision-making and data verification. Such extensions often necessitate custom communication frameworks, encryption protocols, and data packaging methods to handle the increased bandwidth and complexity. They might operate over separate communication links or multiplexed channels alongside standard command and control signals. The reliability and low latency of these extended data protocols are paramount, especially in critical applications where immediate feedback from external sensors can prevent incidents, optimize data collection, or improve mission success rates. This sophisticated data exchange effectively “extends” the drone’s sensory capabilities directly to the operator, transforming raw sensor input into actionable intelligence.
Security Implications of External Access Points
The integration of “EXT” (external) modules and the use of “extended” protocols inevitably introduce significant security considerations. Any point of connection or data exchange in a drone system can represent a potential vulnerability if not adequately secured. External ports and communication links, by their very nature, are accessible points that could be exploited.
Consider a drone designed with a USB “EXT” port for data offload or module integration. If this port is not properly secured or authenticated, an unauthorized entity could potentially inject malicious firmware, extract sensitive mission data, or compromise the drone’s control systems. Similarly, “extended” data protocols, especially those transmitting high-value or sensitive information (e.g., surveillance footage, proprietary mapping data), must be encrypted and authenticated to prevent eavesdropping, data tampering, or spoofing attacks. Ensuring the integrity of the data stream from an external sensor to the GCS is as important as securing the command link to the drone itself. Manufacturers and operators must implement robust cybersecurity measures, including hardware-level authentication for external modules, strong encryption for all extended data protocols, secure boot processes, and regular security audits. The “EXT” functionality, while enhancing a drone’s utility, simultaneously expands its attack surface, necessitating a proactive and comprehensive approach to digital security to safeguard both the platform and its valuable data.
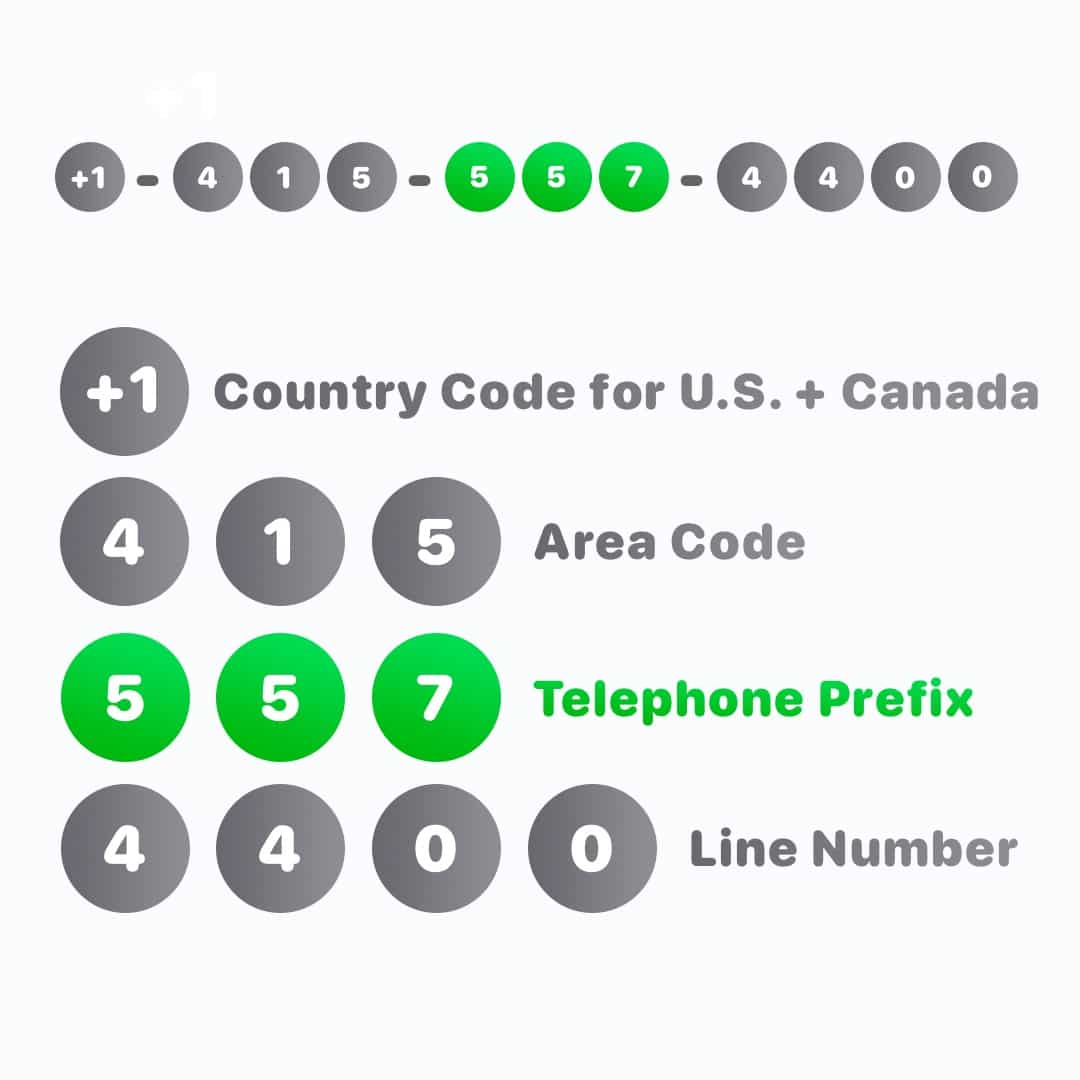
The “Phone Number” as a Unique Drone Identifier
In traditional telecommunications, a “phone number” uniquely identifies a communication endpoint. Transposing this concept to the drone world, it represents a unique digital identifier that enables specific addressing, communication, and management of individual drones within a larger fleet or network. This concept of a unique “address” or “identity” is fundamental for complex operations involving multiple UAVs, regulatory compliance, and robust data management.
Fleet Management and Individual Drone Addressing
In scenarios involving large-scale drone deployments, such as a swarm performing simultaneous mapping operations or a fleet delivering packages across a city, each drone requires a distinct “phone number” – a unique digital identifier – for effective fleet management. This identifier allows a central ground control system or an autonomous management platform to address, monitor, and command individual drones specifically. Without such unique addresses, discerning which drone is performing which task, or communicating specific instructions to a particular unit, would be impossible.
These identifiers are analogous to IP addresses or MAC addresses in computer networks but are often embedded within the drone’s firmware, communication protocols, and even physical markings. They enable the GCS to track each drone’s real-time position, telemetry, payload status, and mission progress. Furthermore, in the event of an anomaly or an emergency, the unique identifier facilitates pinpointing the affected unit, isolating it from the fleet, or dispatching recovery protocols. The ability to individually address and manage drones is crucial for orchestrating complex, coordinated missions, ensuring optimal resource allocation, and preventing interference or collisions between multiple aircraft operating in proximity. It forms the backbone of scalable and efficient drone operations.
Remote Piloting and Command Sequencing
The unique “phone number” of a drone is indispensable for remote piloting and sophisticated command sequencing. When a drone operates beyond visual line of sight (BVLOS) or as part of an autonomous mission, the only way to establish and maintain a secure control link is through its specific digital identity. This identifier acts as the primary target for command and control signals emanating from the ground control station.
Consider a scenario where an operator needs to update the flight path of a specific drone within a group, or manually intervene to take control during an unforeseen circumstance. The drone’s unique identifier ensures that these critical commands are routed precisely to the intended aircraft and not inadvertently to another. This is particularly vital in environments with high drone traffic, where erroneous command signals could lead to severe consequences. Beyond direct piloting, command sequencing for autonomous missions heavily relies on these identifiers. Pre-programmed tasks, waypoints, and payload operations are often associated with a drone’s unique ID, allowing the system to verify that the correct drone is executing the correct sequence of actions. The robust and unambiguous identification provided by a drone’s “phone number” is thus fundamental to safe, precise, and reliable remote piloting and the execution of complex automated missions.
Data Traceability and Regulatory Compliance
In an increasingly regulated airspace, the unique “phone number” or identifier of a drone plays a critical role in data traceability and ensuring regulatory compliance. Every flight operation, every piece of data collected, and every incident report can be meticulously linked back to a specific drone through its unique digital signature. This capability is paramount for accountability and auditing.
For regulatory bodies, the ability to identify individual drones is essential for enforcing airspace rules, investigating incidents, and tracking operational histories. For instance, if an airspace violation occurs, authorities can use the drone’s unique identifier, often broadcast via remote ID systems, to trace it back to its owner or operator. Similarly, for applications involving sensitive data (e.g., surveillance, critical infrastructure inspection), the data generated by a specific drone can be tagged with its unique ID, creating an immutable audit trail from collection to analysis. This ensures data integrity, verifies the source, and helps meet privacy regulations. The “phone number” of a drone, therefore, transcends a mere technical address; it becomes a linchpin for legal, ethical, and operational accountability, fostering trust and enabling the safe integration of drones into national airspaces and various industries.
Interoperability and Standardized “EXT” Interfaces
The growing complexity and widespread adoption of drone technology necessitate high levels of interoperability, particularly concerning “EXT” (external/extended) interfaces. For drones to fulfill their potential, they must seamlessly integrate with a myriad of ground control systems, third-party software applications, and diverse sensor ecosystems. Standardization of these “EXT” interfaces is key to fostering innovation, reducing development costs, and ensuring robust system performance across different manufacturers and applications.
Seamless Integration with Ground Control Systems
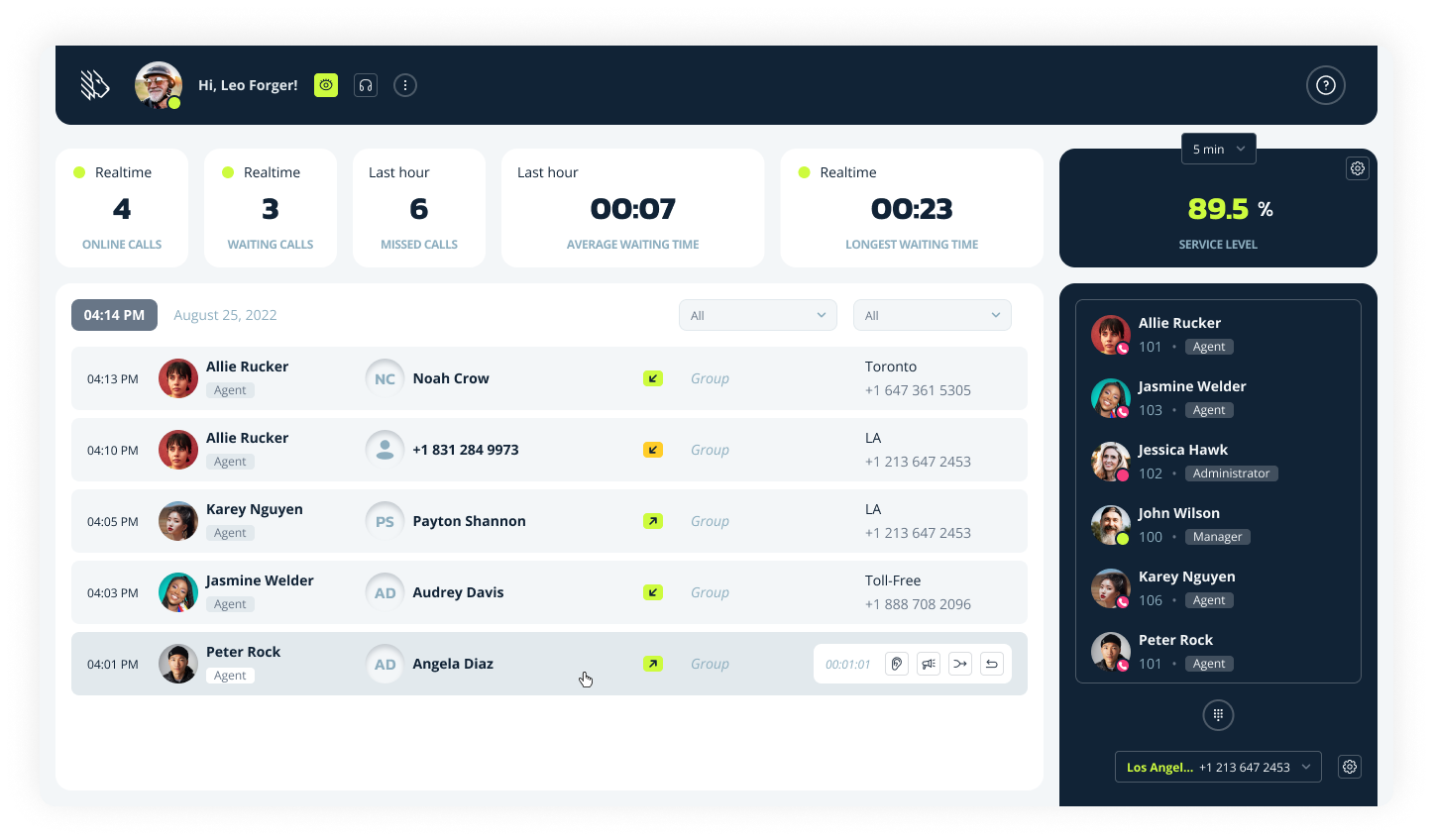
The “EXT” concept, referring to external data and command pathways, is crucial for seamless integration with Ground Control Systems (GCS). A modern GCS is far more than a remote control; it’s a sophisticated hub for mission planning, real-time monitoring, data visualization, and post-mission analysis. For a drone’s “extended” capabilities—such as advanced payload controls, custom telemetry streams from external sensors, or unique mission parameters—to be fully utilized, the GCS must be able to understand and interact with them.
Standardized “EXT” interfaces, whether they pertain to communication protocols (e.g., MAVLink, DroneCAN) or API specifications for accessing drone and payload functionalities, enable this seamless integration. Without such standards, every drone-GCS pairing would require bespoke software development, leading to fragmentation and inefficiency. With standardized interfaces, a GCS can universally command various drone models, process diverse sensor data, and display it in a consistent format. This allows operators to manage mixed fleets with a single system, significantly improving operational efficiency and reducing training overhead. Furthermore, it enables third-party developers to create innovative GCS features or analytics tools that can work across a wide range of drone platforms, accelerating the overall advancement of drone operations.
Future-Proofing for Evolving Drone Ecosystems
Standardized “EXT” interfaces and universal drone “phone number” identification schemes are vital for future-proofing the rapidly evolving drone ecosystem. Technology advancements are relentless, with new sensors, communication technologies, and autonomous capabilities emerging constantly. Without a framework that accommodates these changes, current drone systems risk rapid obsolescence.
The concept of standardized “EXT” ports and protocols allows new hardware modules or software features to be developed and integrated into existing drone platforms with minimal disruption. For example, if a new, more efficient communication module becomes available, a drone designed with a standardized “EXT” communication interface can be upgraded simply by swapping the module, rather than requiring a complete drone replacement. Similarly, a unified approach to drone identification (its “phone number”) ensures that future air traffic management systems (UTM) can effectively track and manage all drones, regardless of their manufacturer or age. This future-proofing approach protects investments in drone technology, encourages innovation by providing a stable integration platform, and ensures that the drone ecosystem can scale and adapt to new regulatory requirements and operational demands without constant, costly overhauls. It builds a foundation for a more interconnected and sustainable future for UAS.
Challenges and Future of Extended Drone Identification
The sophisticated “EXT” functionalities and unique “phone number” identifiers that enable advanced drone operations also present unique challenges. As the drone industry matures and moves towards ubiquitous integration into daily life, addressing these hurdles will be paramount for widespread adoption and safe, efficient operation.
Scalability for Massive Drone Deployments
One of the most significant challenges for “EXT” systems and drone “phone numbers” is scalability, particularly as we envision massive drone deployments. Current identification schemes and communication protocols, while effective for smaller fleets, may struggle to cope with thousands or even millions of drones operating concurrently in the same airspace or networked environment. A typical “phone number” system might eventually run out of unique identifiers, or the network architecture designed to manage individual “EXT” data streams might become overwhelmed.
Future solutions will require highly robust, hierarchical, and dynamic addressing schemes for unique drone identification. This could involve localized identifiers within specific operational zones that are then aggregated into global unique IDs, or dynamic assignment of “phone numbers” based on mission context. For “EXT” data, intelligent routing and prioritization will be essential to ensure that critical telemetry and payload data are transmitted reliably without overwhelming the network. Innovations in 5G and future wireless communication technologies, coupled with distributed ledger technologies for identifier management, will be crucial to ensure that these extended drone systems can scale effectively to meet the demands of truly widespread, complex drone operations.
Cybersecurity Threats to Unique Identifiers
The reliance on unique “phone number” identifiers for drones, while enabling precise control and accountability, simultaneously exposes these systems to advanced cybersecurity threats. A drone’s identifier, if compromised, could be used for malicious purposes, leading to catastrophic consequences. Threats could include spoofing, where an attacker impersonates a legitimate drone’s identifier to gain unauthorized access or issue false commands; tampering, where an identifier is altered to hide a drone’s true identity; or denial-of-service attacks targeting the systems managing these identifiers.
Protecting these unique “phone numbers” is paramount. Future solutions will require multi-layered security protocols, including hardware-level root-of-trust, strong cryptographic authentication of all identifiers, and continuous real-time monitoring for anomalous identification patterns. Immutable record-keeping through blockchain technology could offer a robust solution for managing and verifying drone identities, making them resistant to tampering. Furthermore, the secure management of “EXT” (external) access points that could potentially expose these identifiers to compromise will need constant vigilance. As drones become more integrated into critical infrastructure, the security of their unique identities will become as important as the physical security of the aircraft itself.

The Role of AI in Managing Complex “EXT” Systems
Artificial intelligence (AI) is poised to play a transformative role in managing the growing complexity of “EXT” systems and the vast number of unique drone “phone numbers.” Manually managing extensive fleets, diverse external payloads, and intricate data streams will quickly become unfeasible. AI offers the capability to automate, optimize, and secure these complex interactions.
For “EXT” data protocols, AI can be used to intelligently filter, prioritize, and analyze massive volumes of real-time sensor data, extracting critical insights and flagging anomalies that human operators might miss. It can dynamically reconfigure “EXT” communication links to maintain optimal bandwidth and latency under changing environmental conditions. Regarding unique drone “phone numbers” and fleet management, AI algorithms can optimize drone assignments, predict maintenance needs based on individual drone performance data, and autonomously route drones to avoid conflicts in congested airspace. AI-powered intrusion detection systems can continuously monitor drone identities and “EXT” communication for signs of cyber threats, responding automatically to mitigate risks. The future of extended drone operations, particularly at scale, will heavily rely on intelligent AI systems that can manage, secure, and optimize the intricate web of external interfaces and unique identifiers that define modern drone technology.
