The Foundation of Secure Drone Communication
In the rapidly evolving landscape of unmanned aerial vehicles (UAVs), commonly known as drones, the concept of a “network key” serves as a critical, albeit often unseen, pillar of operational security and data integrity. At its core, a network key is a piece of cryptographic information — a password, passphrase, or digital certificate — used to secure access to a network or to encrypt and decrypt data transmitted over that network. Within the realm of drone technology and innovation, its significance is profoundly amplified, touching every aspect from remote control links to sophisticated data processing in the cloud.
Defining the Digital Gatekeeper
A network key acts as a digital gatekeeper, authenticating legitimate users or devices and authorizing their access to a communication channel. Imagine it as a unique, secret code that allows your drone to communicate securely with its remote controller, a ground station, or even a cloud-based service for processing aerial data. Without the correct key, unauthorized entities are denied entry, preventing eavesdropping, data manipulation, or, most critically, the unauthorized control of the drone itself. This fundamental security mechanism is integral to maintaining privacy, ensuring operational reliability, and protecting valuable assets and sensitive information gathered by advanced drone systems.
Why Security is Paramount in Drone Tech
The innovative applications of drones—from precision agriculture and infrastructure inspection to search and rescue and autonomous delivery—demand robust security frameworks. Drones, by nature, operate wirelessly and often transmit sensitive data over open airwaves. This inherent vulnerability makes them targets for cyber threats. A compromised network key could lead to a myriad of catastrophic outcomes:
- Loss of Control: Malicious actors could hijack a drone, leading to crashes, property damage, or even intentional harm.
- Data Breach: Sensitive aerial imagery, LiDAR scans, or personal data could be intercepted and exposed.
- System Disruption: Jamming or spoofing attacks, facilitated by a compromised key, could disrupt critical missions.
- Reputational Damage and Financial Loss: For commercial operators, a security incident can lead to severe financial penalties, loss of client trust, and long-term reputational harm.
Therefore, understanding and implementing effective network key management is not merely a technical detail; it is a strategic imperative for anyone involved in drone technology and its diverse applications.
Diverse Applications of Network Keys Across Drone Ecosystems
The utility of network keys extends across various layers of drone operation, each demanding specific types of keys and robust management practices to ensure the integrity and security of the entire ecosystem.
Wi-Fi Passphrases: Local Connectivity and Data Management
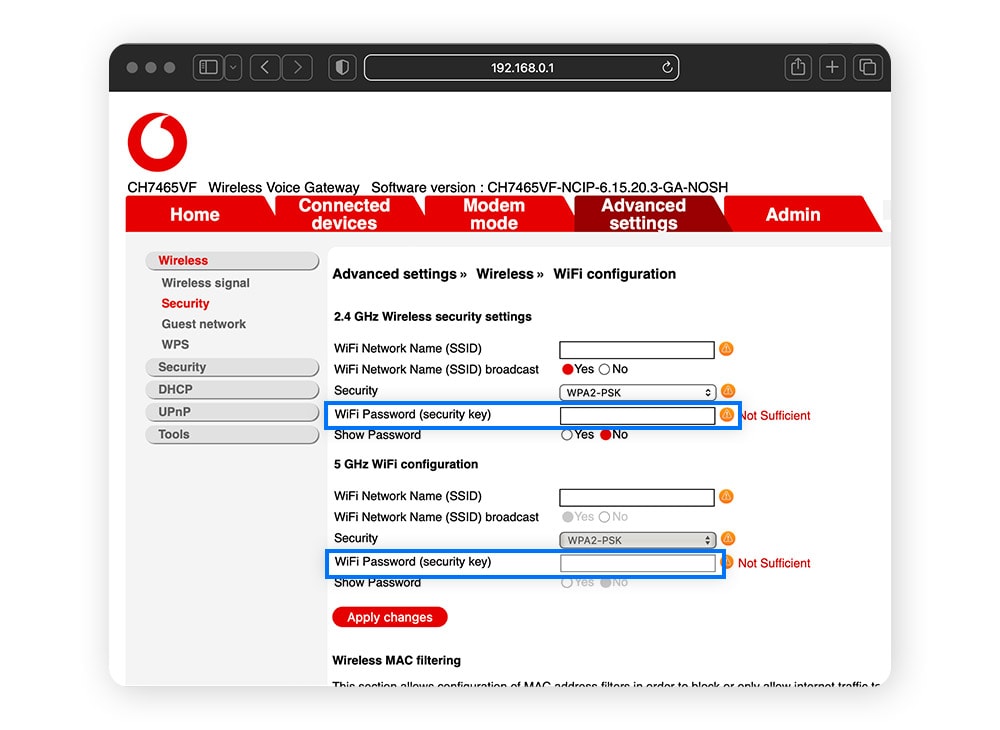
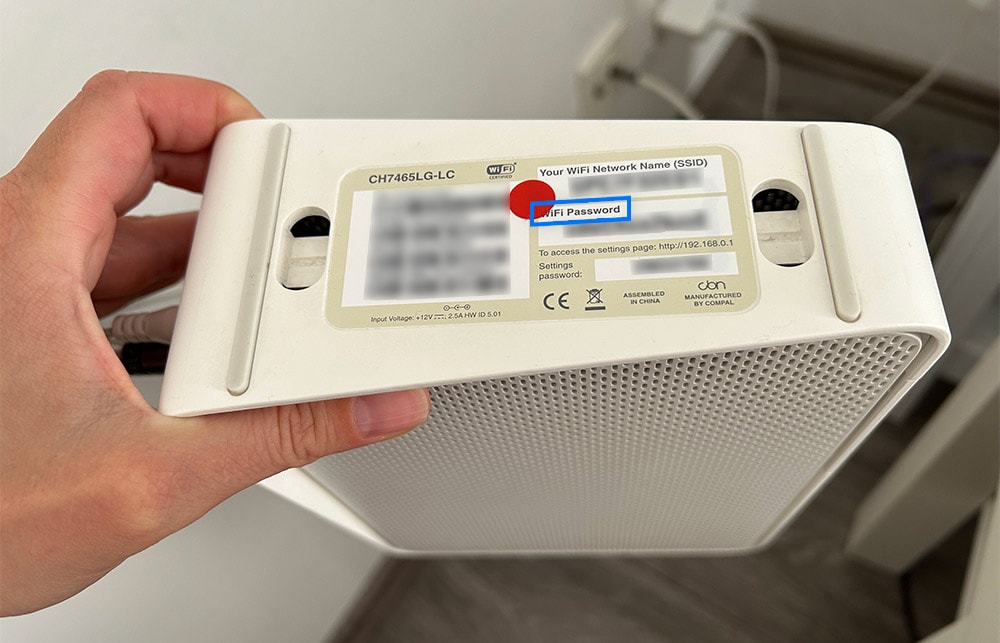
Many commercial and consumer drones utilize Wi-Fi for short-range communication, primarily for connecting to a smartphone or tablet for flight control, real-time video feed streaming, or downloading captured media. The Wi-Fi passphrase, often based on WPA2 or the newer WPA3 standard, serves as the network key for these connections. A strong Wi-Fi passphrase ensures that only authorized devices can connect to the drone’s ad-hoc network or to a local network that the drone might join for data offload or firmware updates. Neglecting this basic security by using default or weak passwords can open a door for unauthorized access, allowing someone within range to potentially intercept data or even interfere with drone controls. In enterprise drone operations, securing these local Wi-Fi links is crucial to protect proprietary data being transferred from the drone’s onboard storage to a local device for initial processing.
Command & Control (C2) Link Encryption: The Heartbeat of Flight Safety
Perhaps the most critical application of network keys in drone technology lies in securing the command and control (C2) link between the drone and its remote controller. Unlike Wi-Fi, this link often uses proprietary radio frequencies and communication protocols tailored for low-latency, high-reliability control. Encryption keys, frequently employing advanced encryption standards (AES), are embedded within these protocols to scramble the control signals and telemetry data. This encryption prevents unauthorized parties from intercepting control commands, sending malicious commands (spoofing), or taking over the drone mid-flight. For autonomous drone operations, especially those operating beyond visual line of sight (BVLOS), the integrity and confidentiality of the C2 link, secured by these robust encryption keys, are non-negotiable for safety and regulatory compliance. Any compromise of these keys could lead to complete loss of drone control, resulting in accidents, data loss, or even national security risks when dealing with sensitive missions.
VPN Keys and Certificates: Extending Secure Reach
As drones become more integrated into enterprise IT infrastructures, particularly for remote sensing, logistics, or surveillance, they often transmit data over longer distances to centralized cloud servers or data centers. In such scenarios, Virtual Private Networks (VPNs) are employed to create secure, encrypted tunnels over public internet connections. VPN keys and digital certificates are used to authenticate the drone or its associated ground station to the VPN server and to establish the secure tunnel. These keys ensure that all data—from sensor readings and live video streams to mission-critical telemetry—remains confidential and untampered with during transit across potentially untrusted networks. This is especially vital for critical infrastructure inspection, mapping projects involving sensitive locations, or military and public safety applications where data security is paramount.
API Keys and Authentication Tokens: Cloud Integration and Service Access
Modern drone ecosystems frequently leverage cloud-based services for data processing, analytics, mapping, and fleet management. Application Programming Interface (API) keys and authentication tokens are network keys used to secure these interactions. When a drone or its associated ground control software needs to upload data to a cloud mapping service, access a weather forecast API, or interact with a fleet management platform, an API key or token authenticates the request. These keys grant specific permissions to access certain services, ensuring that only authorized applications and devices can interact with the cloud infrastructure. Proper management of API keys—including regular rotation and strict access controls—is crucial to prevent unauthorized data access, service disruption, or the injection of malicious data into an enterprise’s drone workflow.
Safeguarding Missions: The Critical Role of Network Keys
The pervasive use of network keys across the drone ecosystem underscores their indispensable role in maintaining the security, integrity, and operational efficiency of UAV applications.
Ensuring Data Integrity and Confidentiality
Drones collect vast amounts of data—high-resolution imagery, thermal scans, LiDAR point clouds, multispectral data, and more. This data often contains sensitive information, be it personal identifiable information (PII) captured during surveillance, proprietary industrial secrets from inspection tasks, or critical infrastructure details. Network keys, through encryption, guarantee the confidentiality of this data, making it unreadable to unauthorized parties during transmission and storage. Furthermore, cryptographic techniques often bundled with key management ensure data integrity, meaning that the data has not been altered or tampered with since it was transmitted by the drone. For industries relying on precise and trustworthy aerial data, such as construction progress monitoring or environmental surveying, this assurance is invaluable.
Preventing Unauthorized Access and Drone Hijacking
The most immediate and apparent risk in drone operations is the potential for unauthorized access or, worse, outright hijacking. A strong C2 link secured by robust network keys acts as the primary defense against such threats. Without the correct encryption key, an attacker cannot decipher the drone’s commands or inject their own. This protection is vital not only for preventing accidental interference but also for thwarting deliberate malicious acts, ranging from recreational pranks to state-sponsored espionage or terrorism. In an increasingly complex airspace, ensuring that each drone adheres to its assigned mission and remains under the control of its legitimate operator is a fundamental safety and security requirement, directly underpinned by effective network key management.
Adhering to Regulatory and Compliance Standards
As drone operations become more sophisticated and integrated into various sectors, regulatory bodies worldwide are enacting stricter rules regarding data security and operational safety. For instance, in regions with robust data protection laws like GDPR, any drone collecting personal data must ensure its confidentiality and integrity. Similarly, for BVLOS operations or flights near critical infrastructure, stringent security protocols, including encrypted communication links, are often mandated. Network keys provide the foundational technology to meet these compliance requirements, demonstrating a commitment to secure operations and responsible data handling. Failing to implement adequate key management can lead to severe fines, operational restrictions, and loss of operating licenses.
Implementing Robust Key Management: Best Practices for Drone Operators
Effective management of network keys is not just about having them; it’s about employing best practices to ensure their strength, integrity, and proper lifecycle. This is crucial for maintaining the “Tech & Innovation” edge in drone operations.
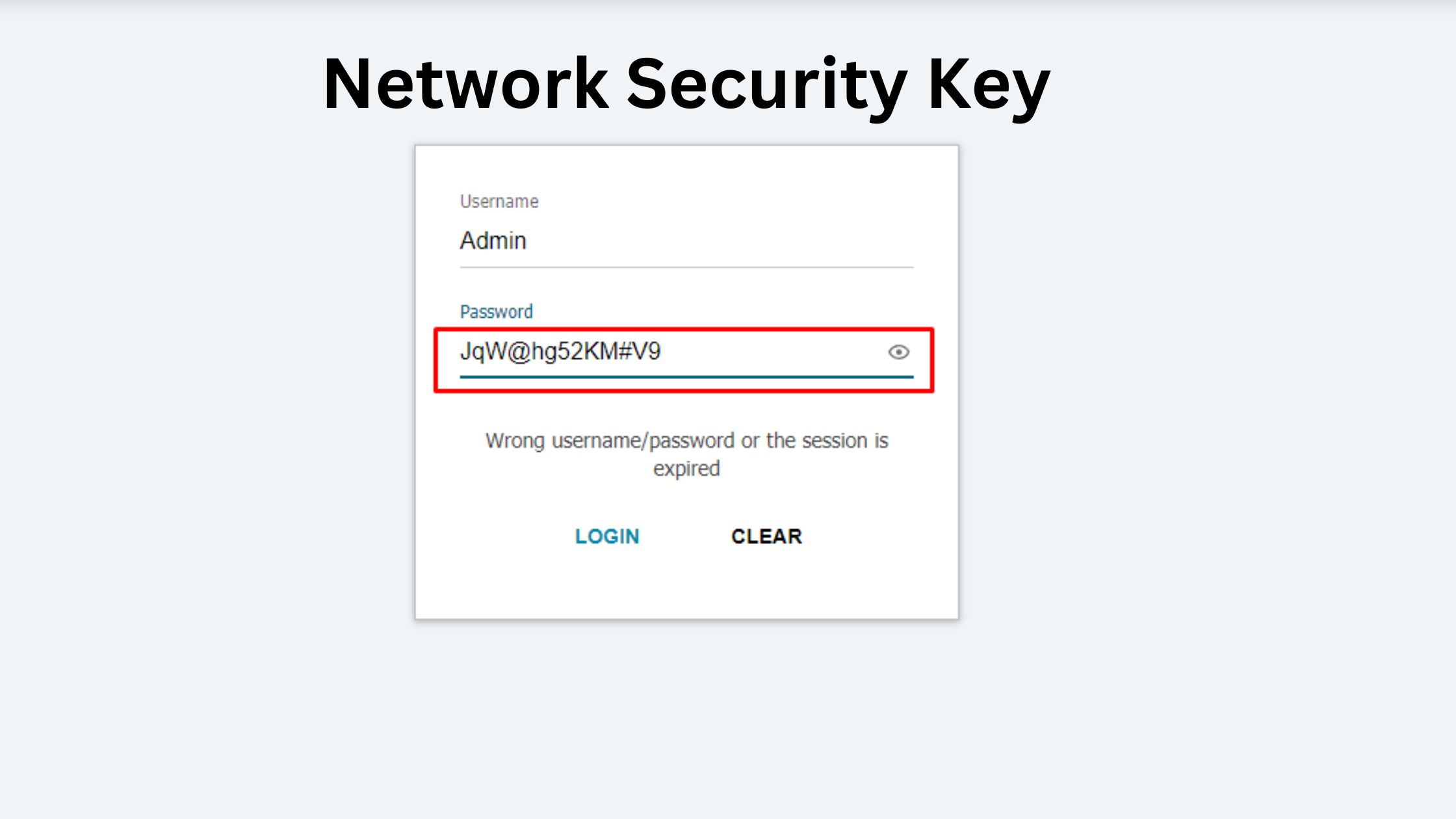
Cultivating Strong, Unique, and Dynamic Keys
The first rule of key management is to use strong, unique keys. This means avoiding default passwords or passphrases that are easy to guess or can be brute-forced. Keys should be complex, combining uppercase and lowercase letters, numbers, and special characters. For cryptographic keys used in C2 links or VPNs, these are typically system-generated and highly complex. Furthermore, implementing key rotation – periodically changing keys – is a critical practice. Even if a key is strong, its prolonged use increases its exposure to potential compromise. Regular rotation mitigates this risk by limiting the window of vulnerability.
Secure Storage and Lifecycle Management
Network keys must be stored securely. On a drone controller, this might mean encryption of the controller’s internal storage. For cloud-based API keys, using dedicated secret management services is paramount. Keys should never be hardcoded into applications or stored in plain text. A comprehensive key lifecycle management strategy includes secure generation, distribution, storage, rotation, and ultimately, secure revocation and destruction of keys when they are no longer needed. This ensures that compromised keys cannot be misused and that old, unused keys do not pose a lingering threat.
Embracing Multi-Factor Authentication and Least Privilege
Where applicable, multi-factor authentication (MFA) should be employed for accessing drone management platforms or critical ground control stations. This adds an extra layer of security beyond just a network key, requiring additional verification (e.g., a code from a mobile device). The principle of least privilege dictates that users and applications should only be granted access to the specific resources and data necessary to perform their tasks, and their associated keys should reflect these limited permissions. This minimizes the impact of a compromised key by restricting the damage an attacker can inflict.
Evolving Threats and the Future of Network Key Security in Drones
As drone technology advances, so too do the sophistication of potential threats. The future of network key security in drones will require continuous innovation to stay ahead of these challenges.
Advancements in Cryptography and Hardware Security
The looming threat of quantum computing, capable of breaking many current encryption standards, drives research into quantum-resistant cryptography. Future drones will likely incorporate these new algorithms to ensure long-term data security. Furthermore, the use of Hardware Security Modules (HSMs) directly on drones or in their controllers will become more prevalent. HSMs are dedicated physical devices designed to generate, store, and protect cryptographic keys, offering a much higher level of security than software-based solutions. Integrating HSMs can create a secure root of trust for all drone communications.
Decentralized and AI-Enhanced Security Frameworks
Blockchain technology, with its distributed ledger capabilities, holds potential for decentralized key management and identity verification in drone fleets, creating immutable records of key usage and authentication. This could enhance transparency and traceability in complex drone operations. Concurrently, artificial intelligence (AI) and machine learning (ML) are being leveraged for anomaly detection in drone communication patterns. AI systems can analyze vast amounts of data to identify unusual behavior that might indicate a key compromise, a spoofing attempt, or unauthorized access, enabling proactive threat response. These innovations will collectively contribute to more resilient and intelligent security frameworks for the next generation of drone technology, ensuring that network keys remain an unyielding fortress against evolving cyber threats.
