In an increasingly digitized world, the seemingly simple question, “What is my verification code?” echoes across countless platforms, applications, and services daily. Far from being a mere nuisance, the verification code represents a fundamental pillar of modern digital security, a micro-transaction of trust that underpins our online interactions. It’s a critical component within the vast landscape of Tech & Innovation, safeguarding personal data, financial assets, and digital identities against an ever-evolving array of threats. Understanding its nature, mechanisms, and future trajectory is essential for anyone navigating the digital realm, from casual users to sophisticated tech developers.
At its core, a verification code is a short, temporary string of characters—often numerical—sent to a user through an out-of-band communication channel, such as SMS, email, or a dedicated authenticator app. Its purpose is singular and profound: to verify the user’s identity during a login, transaction, or critical account change, thereby adding an essential layer of security beyond traditional passwords. This concept, known as multi-factor authentication (MFA), moves beyond “something you know” (a password) to include “something you have” (your phone or email access) or “something you are” (biometrics). As technology advances and cyber threats become more sophisticated, the innovation in how these codes are generated, delivered, and utilized continues to be a frontier in digital security.
The Ubiquitous Guardian: Understanding Verification Codes in the Digital Age
The proliferation of verification codes across virtually every online service—from banking and social media to cloud storage and e-commerce—underscores their critical role in establishing and maintaining digital trust. They act as a real-time, dynamic gatekeeper, ensuring that the person attempting to access an account is indeed its rightful owner, even if their primary password has been compromised. This omnipresence is a direct result of continuous innovation in security protocols, striving for a balance between robust protection and user convenience.
The Core Purpose: Security and Identity Assurance
The primary driver behind the widespread adoption of verification codes is the inherent vulnerability of single-factor authentication (SFA), which relies solely on passwords. Passwords can be guessed, stolen through phishing, brute-forced, or exposed in data breaches. A verification code, typically valid for a very short period (e.g., 60 seconds), dramatically reduces the window of opportunity for an attacker. Even if a malicious actor gains access to a user’s password, they would still need access to the user’s registered phone or email account to complete the login, making unauthorized access significantly harder. This innovative approach to identity assurance transforms a static defense into a dynamic challenge, adapting to the immediate context of the login attempt.
Different Forms: OTP, SMS, Email, App-based
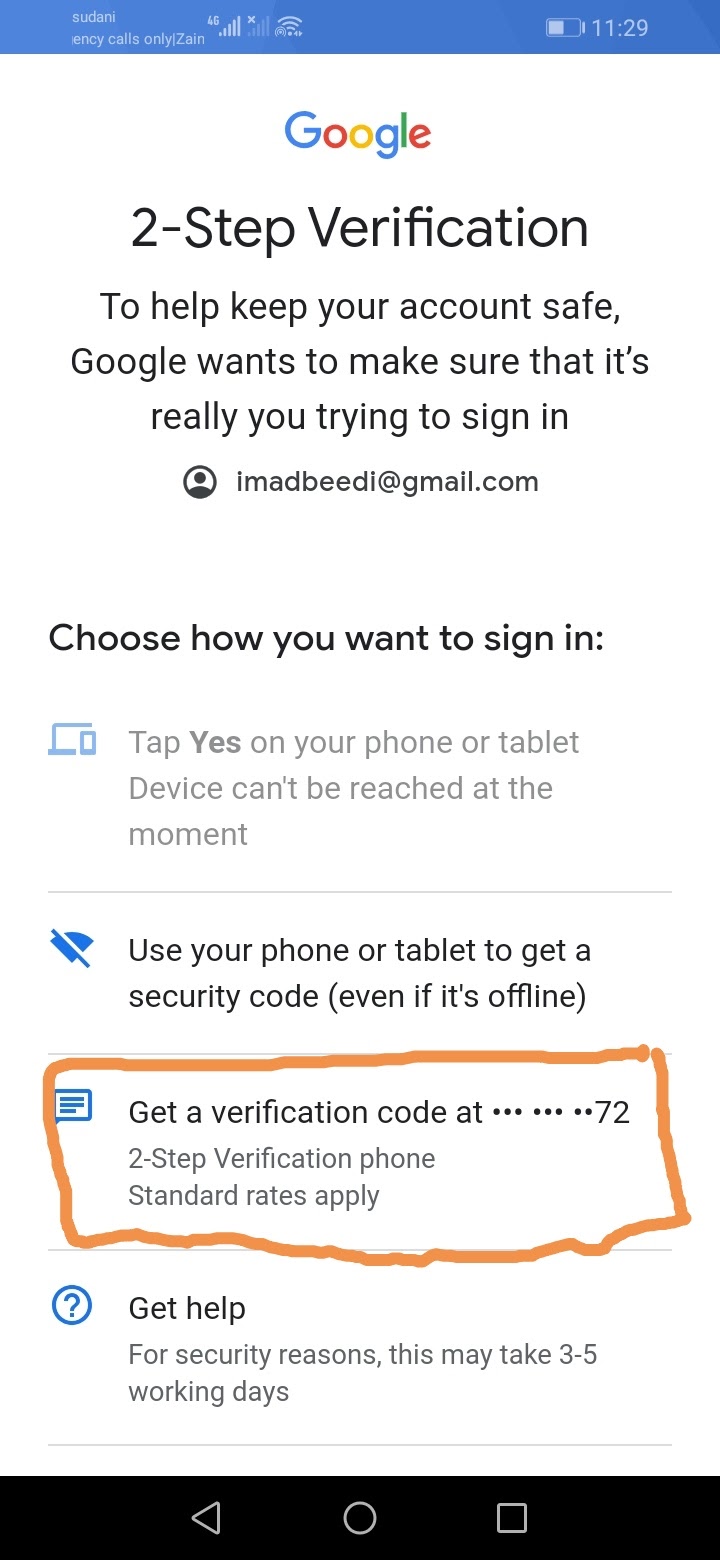
Verification codes manifest in several forms, each with distinct advantages and security implications.
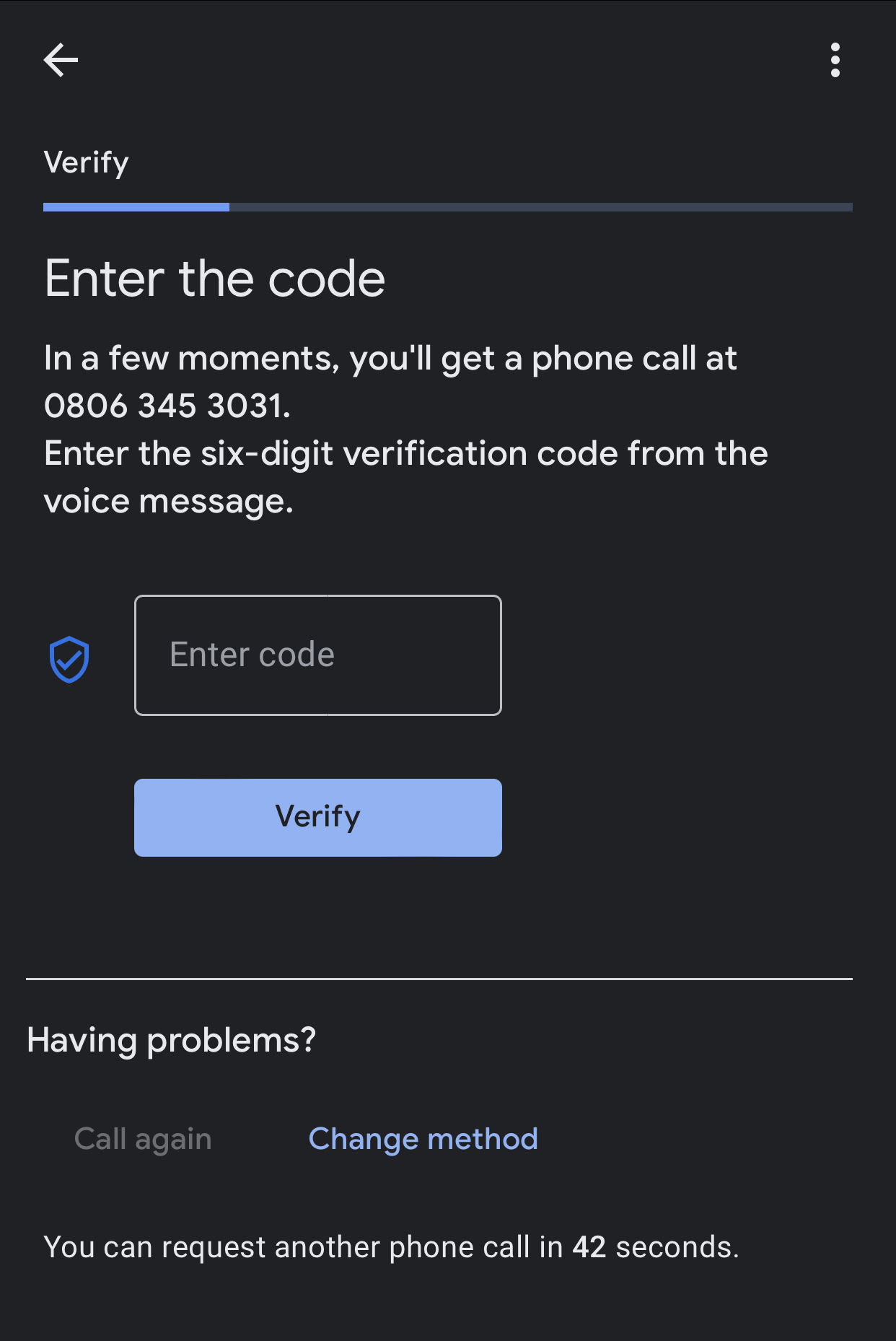
- One-Time Passwords (OTPs) via SMS: This is perhaps the most common form. A numerical code is sent via text message to the user’s registered mobile phone. While widely accessible and convenient, SMS OTPs face vulnerabilities like SIM-swapping attacks, where attackers trick carriers into porting a user’s phone number to their own SIM card.
- Email-based Codes: Similar to SMS, a code is sent to the user’s registered email address. This method is convenient but susceptible if the email account itself is compromised, making it a weaker second factor unless the email account is separately secured with MFA.
- Authenticator App-based Codes (TOTP/HOTP): Applications like Google Authenticator or Authy generate time-based (TOTP) or HMAC-based (HOTP) one-time passwords directly on the user’s device. These codes are generated algorithmically and do not require network connectivity to be received, making them more resilient to phishing and SIM-swapping attacks. This method represents a significant technological leap in security for its independence from telecom infrastructure.
- Push Notifications: Some systems send a push notification to a trusted device, asking the user to approve or deny a login attempt with a simple tap. This offers a highly convenient and secure method, leveraging the device’s inherent security features.
Each innovation in delivery method aims to enhance security while minimizing friction for the legitimate user, a constant balancing act in tech development.
The Psychology of Trust: Why We Rely on Them
Beyond the technical aspects, verification codes play a crucial psychological role in building user trust. The act of receiving a code and entering it creates a tangible connection to the security process, reassuring users that their accounts are actively being protected. It transforms an abstract concept of “security” into a concrete action. This immediate feedback loop fosters a sense of control and confidence, encouraging users to engage more fully and responsibly with their digital identities. The consistent experience across diverse platforms also reinforces a universal understanding of security best practices, a testament to effective tech innovation and standardization.
The Technological Underpinnings: How Verification Systems Work
The simplicity of entering a six-digit code belies the sophisticated technological infrastructure operating behind the scenes. These systems involve complex cryptographic algorithms, secure communication channels, and robust backend services, all working in concert to generate, transmit, and validate these temporary credentials efficiently and securely. The innovation here lies in creating systems that are both highly secure and scalable to millions of users, often under immense pressure from concurrent requests.
Cryptographic Principles and Random Number Generation
At the heart of any secure verification code system lies strong cryptography and genuinely random number generation. When a user requests a code, the system doesn’t just pull a random number out of thin air. Instead, it uses cryptographic techniques to generate a unique, unpredictable, and non-reusable code. For app-based authenticators (TOTP), a shared secret key is established between the authenticator app and the server during setup. Both then use this key, combined with the current time (for TOTP), to algorithmically generate the same code simultaneously. This deterministic yet unpredictable generation, without any network transmission for the code itself, is a hallmark of robust security innovation. For SMS/email codes, a cryptographically secure pseudo-random number generator (CSPRNG) is used to create the random string, which is then securely stored in association with the user’s session and expiration time.
Backend Infrastructure and Delivery Mechanisms
The backend infrastructure supporting verification codes must be robust and resilient. When a code is requested, the system performs several steps:
- Identity Verification: Confirms the requesting user’s identity (e.g., via username/password).
- Code Generation: Generates a unique, time-sensitive code.
- Code Storage: Temporarily stores the code, associated with the user and an expiration timestamp.
- Delivery Channel Selection: Determines the preferred method (SMS, email, push notification, etc.).
- Secure Transmission: Sends the code via an encrypted channel. For SMS, this involves gateways; for email, secure SMTP; for push, platform-specific secure APIs.
- Validation: Upon user entry, the system retrieves the stored code, checks for validity, expiration, and potential multiple attempts.
Innovations in this infrastructure focus on minimizing latency, ensuring delivery reliability, and implementing robust fraud detection mechanisms to prevent abuse, such as excessive code requests or brute-force attempts.
User Experience vs. Security Trade-offs
A constant challenge in tech innovation is balancing stringent security requirements with an intuitive and seamless user experience. Overly complex authentication processes can deter users or lead them to bypass security features. Verification codes, while adding a step, are generally perceived as a manageable inconvenience. However, issues like delayed SMS delivery, lost phone access, or complex recovery procedures can degrade the user experience. Tech companies continuously innovate to streamline these processes, offering multiple recovery options, clear instructions, and intelligent fallbacks, all while maintaining high security standards. This continuous refinement is a testament to the dynamic nature of innovation in digital identity.
Evolution and Innovation: Beyond the Basic Code
The journey of verification codes is far from over. As cyber threats evolve, so too must the defenses. The tech industry is constantly pushing boundaries, exploring new paradigms that promise even greater security, convenience, and resilience against future attack vectors. This includes moving beyond simple numeric codes to more advanced multi-factor, biometric, and even decentralized identity solutions.
Multi-Factor Authentication (MFA) and Adaptive Security
MFA itself is an innovation that has become a standard. However, the future lies in adaptive security, where the level of authentication required dynamically adjusts based on context. For example, if a user logs in from an unfamiliar location or device, or at an unusual time, the system might trigger an additional verification step, like a code. If the login is from a recognized device and location, it might allow access with just a password or even leverage passwordless authentication. This intelligent, risk-based approach, often powered by AI and machine learning, significantly enhances security without burdening users unnecessarily. Such systems analyze behavioral patterns, device fingerprints, and network telemetry to make real-time risk assessments.
Biometrics and Behavioral Authentication
Beyond “something you have,” biometrics (“something you are”) offer a compelling evolution. Fingerprint scans, facial recognition, and iris scans provide highly secure and convenient authentication. These methods, integrated into devices, eliminate the need for remembering or typing codes. However, even biometrics have their limitations, such as the impossibility of changing a compromised fingerprint.
Behavioral biometrics, a cutting-edge field, takes this further by analyzing how a user interacts with their device—typing speed, mouse movements, swipe patterns, even gait. These subtle, continuous streams of data can uniquely identify a user without explicit action, offering a “passwordless” and “codeless” authentication that runs in the background. This passive, continuous authentication represents a significant leap in security innovation.
Blockchain and Decentralized Identity Solutions
Another transformative innovation on the horizon is the use of blockchain technology for decentralized identity. Instead of relying on centralized services to store and verify identity attributes, users could own and control their digital identities on a blockchain. Verification codes, in this paradigm, might evolve into cryptographically signed credentials or attestations issued by trusted authorities and presented by the user without revealing underlying personal data to every service. This “self-sovereign identity” model promises enhanced privacy, security, and user control, fundamentally changing how digital identities are managed and verified, moving away from centralized vulnerability points.
The Future of Digital Identity: Seamless and Secure Interactions
The ultimate goal of tech innovation in digital identity is to achieve a future where online interactions are both effortlessly seamless and impeccably secure. The “what is my verification code” query, while still relevant, will likely transform as more sophisticated and integrated authentication methods become standard. The focus is shifting towards invisible, continuous verification that protects users without disrupting their experience.
AI and Machine Learning in Anomaly Detection
Artificial intelligence and machine learning are pivotal to this future. AI algorithms can analyze vast datasets of user behavior, network patterns, and threat intelligence to detect anomalies in real-time. If a login attempt deviates significantly from a user’s typical behavior, AI can automatically trigger higher authentication hurdles—like demanding a verification code or stepping up to biometric authentication—even before the user suspects an issue. This proactive, intelligent defense moves beyond static rules, making security a dynamic and adaptive process, a true testament to modern tech innovation.
Passwordless Authentication and FIDO Standards
The industry is rapidly moving towards a passwordless future, where the need for traditional passwords and, by extension, many forms of explicit verification codes, diminishes. Standards like FIDO (Fast Identity Online) are leading this charge. FIDO uses public-key cryptography to authenticate users, allowing them to log in with a biometric (fingerprint, face scan) or a device PIN instead of a password. The cryptographic keys are stored securely on the user’s device and never leave it, making phishing attacks largely ineffective. This innovation streamlines the login process while dramatically enhancing security, offering a more robust alternative to typical verification codes.
The Promise of Quantum-Resistant Cryptography
Looking further ahead, the advent of quantum computing poses a potential threat to many current cryptographic schemes, including those underlying some verification systems. Researchers and innovators are actively developing quantum-resistant (or post-quantum) cryptography—new algorithms designed to withstand attacks from future quantum computers. Integrating these new cryptographic primitives into identity and authentication systems will be a critical future challenge for tech and innovation, ensuring that digital verification remains secure against even the most advanced computational threats.
In conclusion, “what is my verification code” is a question that opens a window into the dynamic and ever-evolving world of Tech & Innovation in digital security. From its simple origins as a second factor for authentication to its integration into complex adaptive security systems, biometrics, and decentralized identities, the verification code reflects a continuous commitment to protecting our digital lives. As technology progresses, we can expect these mechanisms to become even more intelligent, seamless, and resilient, securing our online interactions in ways we are only just beginning to imagine.
